When using Locations within a data loss prevention (DLP) rule, especially when targeting OneDrive, the default behavior is to list the main site where all the user information is being stored. However, we don’t have an easy option to define per-user basis.
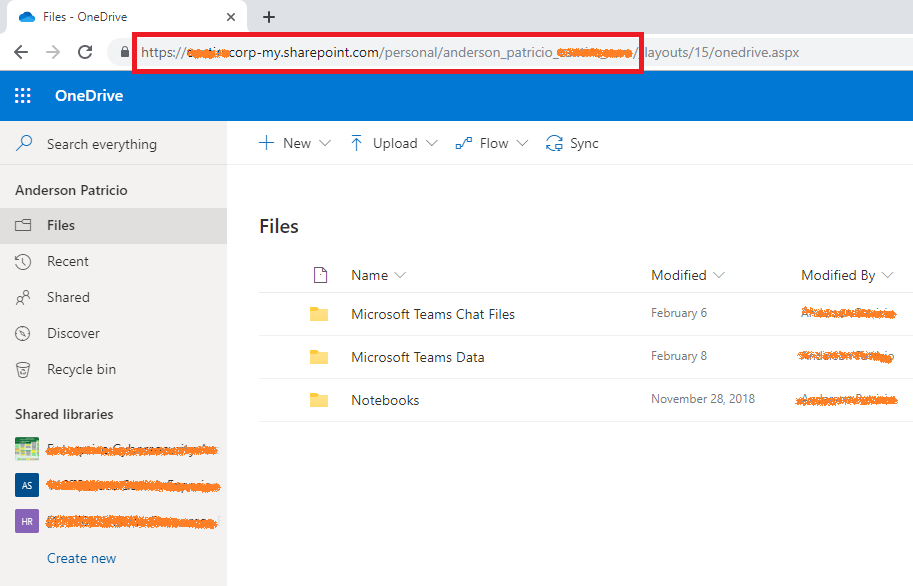
There is a workaround for this scenario. It is not the prettiest one around, but it could be useful if you have a small number of users who are required to receive a specific data loss prevention policy. The first step is to identify the URL being used by OneDrive for the user that we want to add to the policy. The easy way is to log on the Office 365 portal, and then click on OneDrive from the list of available applications.

When the portal opens, copy the URL, make sure to remove the suffix _layouts/15/onedrive.aspx.
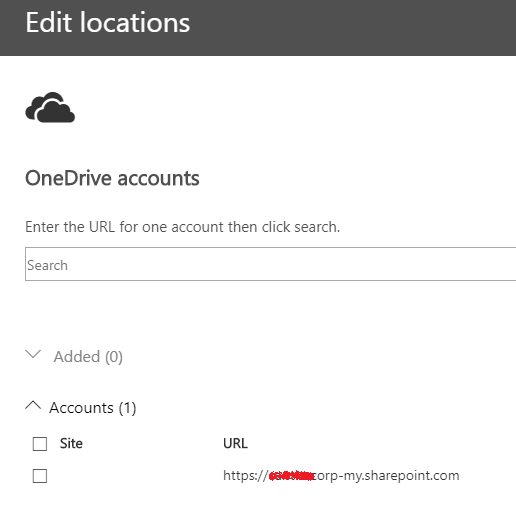
Open the DLP rule that you want to define which user will define which users can receive the information, click on Choose Accounts, and type in the address that we retrieved in the previous step.

The result should be similar to the image below. Add any additional user to the list, and save the rule.

This workaround can be used for a small subset of users due the manual process involved. We can use PowerShell to automate the extraction of the URLs and use it to create/update DLP rules, but still a lot of work has to be done to automate the process.
Featured image: Shutterstock



