Many small and mid-sized businesses are under the impression that because of the size of their company and relatively low profile, they are immune to attacks from cybercriminals. However, this type of mindset is absolutely incorrect. In fact, more than 60 percent of small businesses were hit by a cyberattack last year. The reason why cyberattackers concentrate more on small businesses rather than larger ones is because it’s easier to siphon off their personal data. This personal data is then used for identity theft or stealing credit card information. Of course, larger enterprises usually provide greater amounts of data for theft, but small businesses are a prime target. Criminals have an easier time breaching the network and getting what they want through automated attacks. SMBs also don’t often have the resources necessary to implement proper security. Thankfully, there are ways for small and medium-sized businesses to avoid falling prey to cyberattacks. It all comes down to identifying and plugging the cloud security gaps mentioned below:
Cloud security gaps: Lack of a firewall

A firewall is the primary line of defense in the event of a cyberattack. It is recommended that every SMB establish a proper firewall to isolate their precious data from cybercriminals. Apart from the regular external firewall, companies must also implement internal firewalls for additional protection. If that’s not all, employees who regularly work from home should make it a point to use a firewall while connecting via their home networks too for ensuring compliance.
Undocumented cybersecurity policies
Although the majority of small and mid-sized businesses operate on the basis of intuitional knowledge and word of mouth, cybersecurity is one area where it is absolutely necessary to document all the protocols. Employees in these companies must have the necessary online training, information, and checklists to protect their online businesses. Keep your cybersecurity policies updated at all times and use detailed toolkits to determine and document all the cybersecurity policies being implemented in the company.
Absence of a clear plan for mobile
A lot of small and mid-sized businesses have started following the “bring your own device” trend, which allows employees to use their personal devices for work purposes. But companies should remember to document their BYOD policies that focus on security measures. Thanks to the growing penetration of smart wearables, like fitness trackers and smart watches with wireless capabilities, it is a no-brainer to include such devices in the existing policy. Small business must also make use of automatic security updates for employees and implement a strict password policy on every mobile gadget.
Lack of training among employees
Companies make an active effort to educate all internal users. The staff often wears multiple hats in an SMB, making it necessary for all employees connecting to the network to be trained regarding the security policies of the company network. As the policies continue to evolve, the cybercriminals continue to become smarter as well. This makes regular protocol updates a necessity. In order to hold the employees accountable, each employee needs to sign a document mentioning that they will comply with the company policies.
Non-enforcement of safe and secure password practices

This is something that every company, whether they are big or small, needs to rectify immediately. Yes, it is true that employees find it quite irritating to change passwords. But a large chunk of data breaches occur because of stolen, lost, or weak passwords. What’s even more worrisome is that a majority of SMBs with clearly outlined password policies fail to actively enforce them. In the modern BYOD world, it is necessary that every employee device accessing the network remain protected via a password. Employees should use passwords consisting of lowercase and uppercase letter, symbols, and numbers. Moreover, they need to change passwords every 60 to 90 days.
Infrequent backups of company data
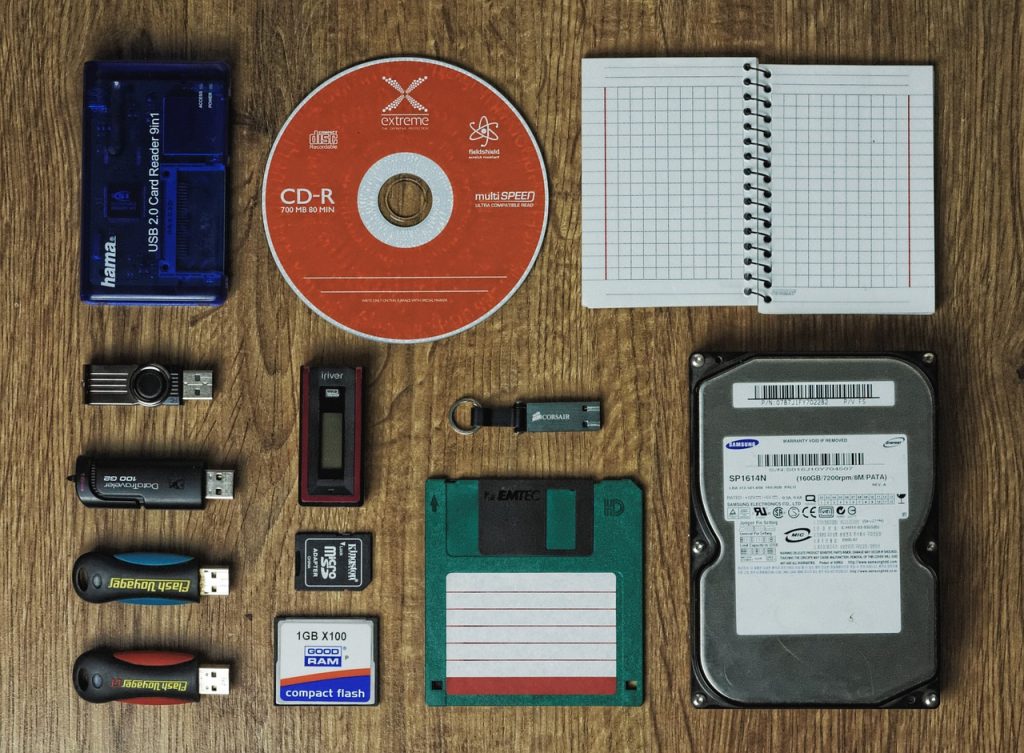
Companies should try to avoid as many cyberattacks as possible. But despite their best efforts there is always the possibility that they might experience a breach. That’s why it is necessary to back up all electronic spreadsheets, financial files, human resources files, databases, word processing documents, and payable or accounts receivables files. On top of that, ensure that all the backed-up data gets stored on the cloud. The backup data should be stored in a location that is separate in case of a natural disaster. To make sure your data backup is up to date, check your backup regularly. And having backups is not enough. Make sure you know how to restore them.
No anti-malware software installed on systems
Small and medium-sized businesses often assume that their employees know better than to open phishing emails. But there is always the possibility that an unsuspecting employee might open a phishing email and accidentally launch an attack. Now, most phishing attacks involve installing codes on the computer of the employee as soon as they click on the problem link. For that reason, it is important to use potent anti-malware software on every device as well as the whole network. As phishing attacks tend to target certain employee roles, position-specific strategies should be outlined to prevent any mishap.
Lack of multifactor identification
No matter how well your company is prepared for a cyberattack, employees can make one security mistake and compromise all the system data. However, the use of multifactor authentication settings on most of the email products and major networks adds an extra precaution to the proceedings. Plus, the whole process is fairly simple. Ideally, employees should use their mobile phone numbers as a second level of authentication as it is quite unlikely that a cybercriminal will have both their password and PIN.
Closing cloud security gaps: It’s an endless struggle
Security is evolving constantly and SMBs must do their best to ward off cybercriminals who are becoming more and more advanced with each passing day. To safeguard their valuable data, it is necessary for employees to take the onus and make cybersecurity a major priority. Most importantly, companies need to stay atop the latest trends for the latest prevention technology and attacks and make sure all cloud security gaps are closed.
Images: Pixabay



