Product Homepage: click here
For an Office 365 Health Check: click here
For a Demo: click here

Last month I had a chance to look at CoreAdmin from CoreView. As I wrote that review, I realized there was much more to the CoreView suite than I could cover within the confines of a single review. That being the case, I wanted to go back and look at another CoreView product, CoreSecurity
CoreSecurity is designed to help you figure out whether or not your Office 365 environment is secure, and your users are in full compliance with the policies that you have established. As you are no doubt aware, email is by far the most commonly exploited point of entry through which malicious software enters an organization, so it makes sense to put a solution in place that can help you keep Exchange Online and the rest of the Office 365 platform secure.
Auditing
Auditing is one of CoreSecurity’s core functions. CoreSecurity’s auditing functions were built around two different Microsoft APIs. This includes the Office 365 management API used to collect Office user activity and another API used to collect information about the Office 365 login process.
Although there might not be anything unique about creating Microsoft audit log reports, CoreView compiles the logging data in a way that is different from what I have seen anyone else do. When an event occurs, CoreSecurity seems to be using the logging data to perform an Azure AD query to augment the log entry with as much additional data as possible. This allows Azure AD attributes such as Department and Country to be associated with each log entry.
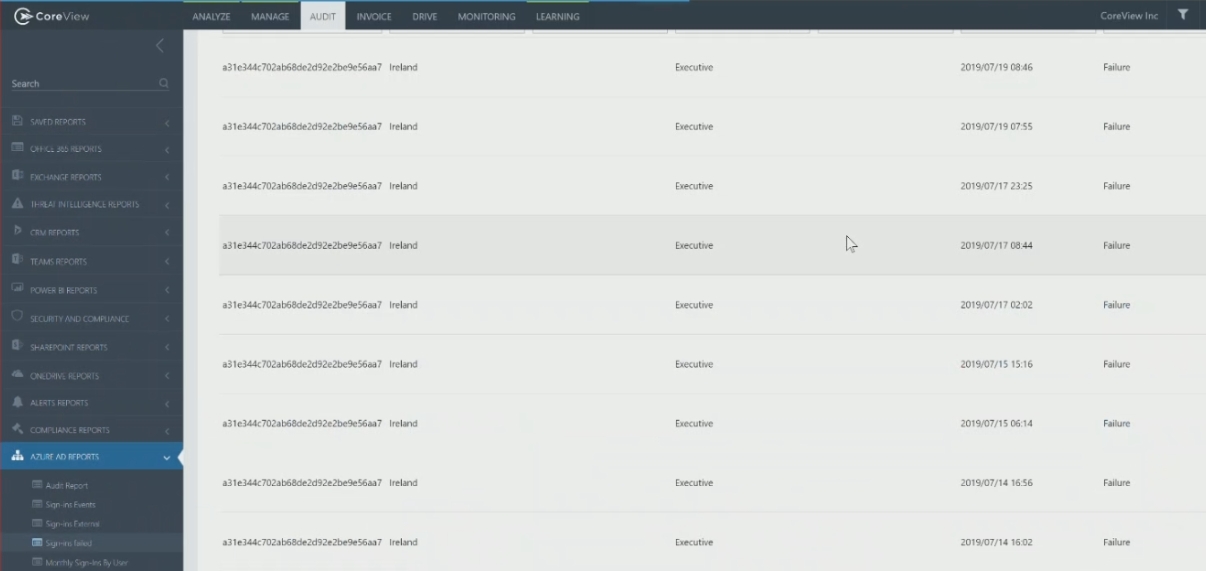
The reason why this is so important is because it allows IT pros to create reports that go well beyond what is natively possible in Office 365. The extra Azure AD data makes it possible for example, to view failed login attempts on a department by department basis. This makes it easy to determine, for instance, if someone outside the organization is targeting the executive management team’s accounts. You can see an example of this in the screenshot below. Similarly, it would be theoretically possible to see if any users are logging in from countries other than the one in which they reside (which would indicate that the user’s account has been compromised).
It is also worth noting that CoreSecurity retains logging data longer than Microsoft does. By default, Microsoft retains standard Office 365 logging data for 90 days and retains sign-in data for 30 days. In contrast, CoreSecurity retains this data for twelve months, and it is possible to retain logging data indefinitely.
Given the sheer volume of logging data that CoreSecurity creates and retains, I was initially a little concerned that it would be cumbersome to sift through the logging data in search of a particular event or event type. What I found, however, is that CoreSecurity provides numerous prebuilt reports that make it easy to locate the auditing data that is likely to be of the most interest to the organization. These reports are grouped into categories such as Exchange, SharePoint, and Power BI. There are several reports provided within each category. The Exchange Reports category, for example, includes reports on admin mailbox activities, non-owner mailbox activities, and mailbox rights change — just to name a few. You can see some of the available Exchange Online related reports in the next screenshot.

As helpful as these reports are, the reports are not the sole mechanism for auditing logging data. CoreSecurity provides a wide variety of filters that make it easy to perform a custom search.
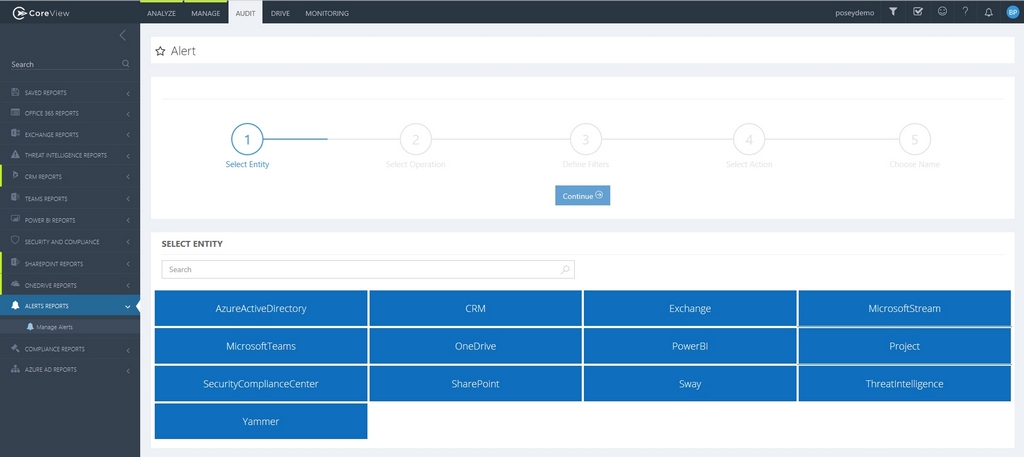
One of the most compelling features in CoreSecurity’s Auditing section is its alerting mechanism. Like most of the other alerting mechanisms I have seen in other security products, the CoreSecurity Alert feature is based around trigger events and actions. The thing that makes this Alert engine different from others is that it can be configured with extreme granularity. In the Exchange section alone, there are over a thousand different types of event triggers that can be defined. Even so, CoreSecurity’s intuitive GUI interface makes it easy to navigate the alert creation mechanism. You can see the Alert interface in the next screen capture and some of the available filters for Exchange in the screen capture right below it.

Analyze
The other major part of CoreSecurity is its analytical capabilities. Among other things, the product’s Analyze tab contains a Compliance Dashboard, which you can see in the next figure. CoreSecurity allows you to create a series of checks that define what it means to be compliant. For example, you might check for impossible travel to atypical locations, mailboxes that have forwarding enabled, or perhaps sign-ins from infected devices. The Compliance Dashboard shows you at a glance whether or not everyone is compliant with a particular check. If the software determines that not everyone is compliant with a particular item, then the item is flagged with a red X. You can then click on the item to see exactly which user is not compliant, and why. If, for example, a user was found to be forwarding all of their email to someone outside of the organization, the report would show which user was forwarding their messages, and who they were forwarding them to.
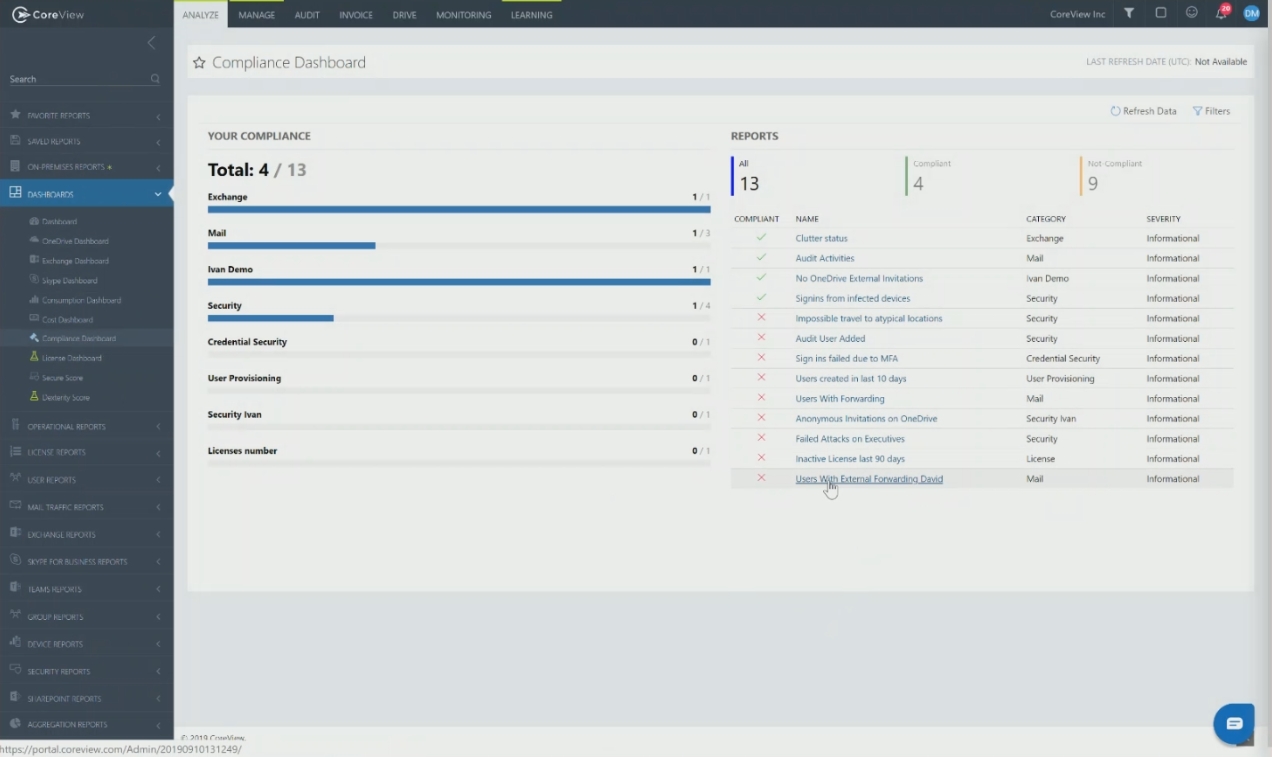
One of the things that I particularly liked about the Compliance Dashboard is that while CoreSecurity does allow you to manually generate compliance reports, you can also run reports on a scheduled basis. The thing that is really nice about these scheduled reports is that you can configure CoreSecurity to only send you a report if someone is out of compliance. This keeps your mailbox from being flooded with reports when everything is normal. CoreSecurity only emails you when there is a condition that you need to be aware of.
The verdict
It has become customary for me to conclude my reviews by giving the product a score ranging between zero and 5 stars, with five stars being the best. With that said, I decided to give CoreSecurity a score of 4.9, which is a Gold Star review.
Microsoft Office 365 is a complex environment, with numerous configurable security settings but, unfortunately, many of Microsoft’s default security settings are inadequate. Most of the Office 365 breaches that I have personally heard about were the direct result of security settings that were simply too lax. I think that CoreSecurity does an excellent job of helping organizations understand where potential vulnerabilities exist within their Office 365 configurations.
I was also impressed that the software doesn’t just point out areas in which security could be improved, it actually shows you which users are out of compliance, and what the user has done to result in their noncompliant state.
The thing that impressed me most about CoreSecurity, though, was its extreme granularity. CoreSecurity is a GUI-based product, yet it provides an ability to create custom filters with a level of granularity that would be tough to achieve even through PowerShell.
Rating: 4.9/5


