Up until several years ago, I used to practice what I liked to call “security through obscurity.” The idea behind this philosophy was that hackers, script kiddies, and other cybercriminals tend to target things that are well-known and well-documented. If, for example, cybercriminals were going create a piece of malware that attacks an operating system, they would no doubt choose an operating system that is widely used so as to maximize the effectiveness of their malware. As such, I had the idea that I could improve the security of my own environment by using hardware and software that were well outside the norm.
Since it would not be in my best interest to publicly disclose the details of my internal security, I will give you an example from way back when. When wireless networking gained mainstream popularity, 802.11B quickly became the standard of choice for both businesses and for residential use. That being the case, I avoided using 802.11B and opted to use 802.11A instead. 802.11A performed better than 802.11B (54 megabits instead of 11 megabits), and it operated on a different frequency (5GHz instead of 2.4GHz). In spite of these advantages, 802.11A never caught on. 802.11B components were far less expensive, and therefore became the WiFi flavor of choice. More importantly, using 802.11A gave me a security advantage because most of the wireless exploits of the time were specifically designed to target 802.11B networks.
Is security through obscurity a defense against cybercriminals?
One of the other ways that I have heard of people practicing security through obscurity is by utilizing really old technology. I recently had a conversation with someone about the IT infrastructure used by a chain of large retail stores. I was shocked to learn that the retailer uses an operating system that is about 20 years old. The person that I had spoken to told me that the OS has a much smaller footprint than today’s operating systems, and is therefore much easier to harden.
Whether or not a 20-year-old operating system can be adequately hardened to protect against today’s threats is debatable, but it does raise an interesting question. Can an organization achieve security through obscurity by using legacy tech?
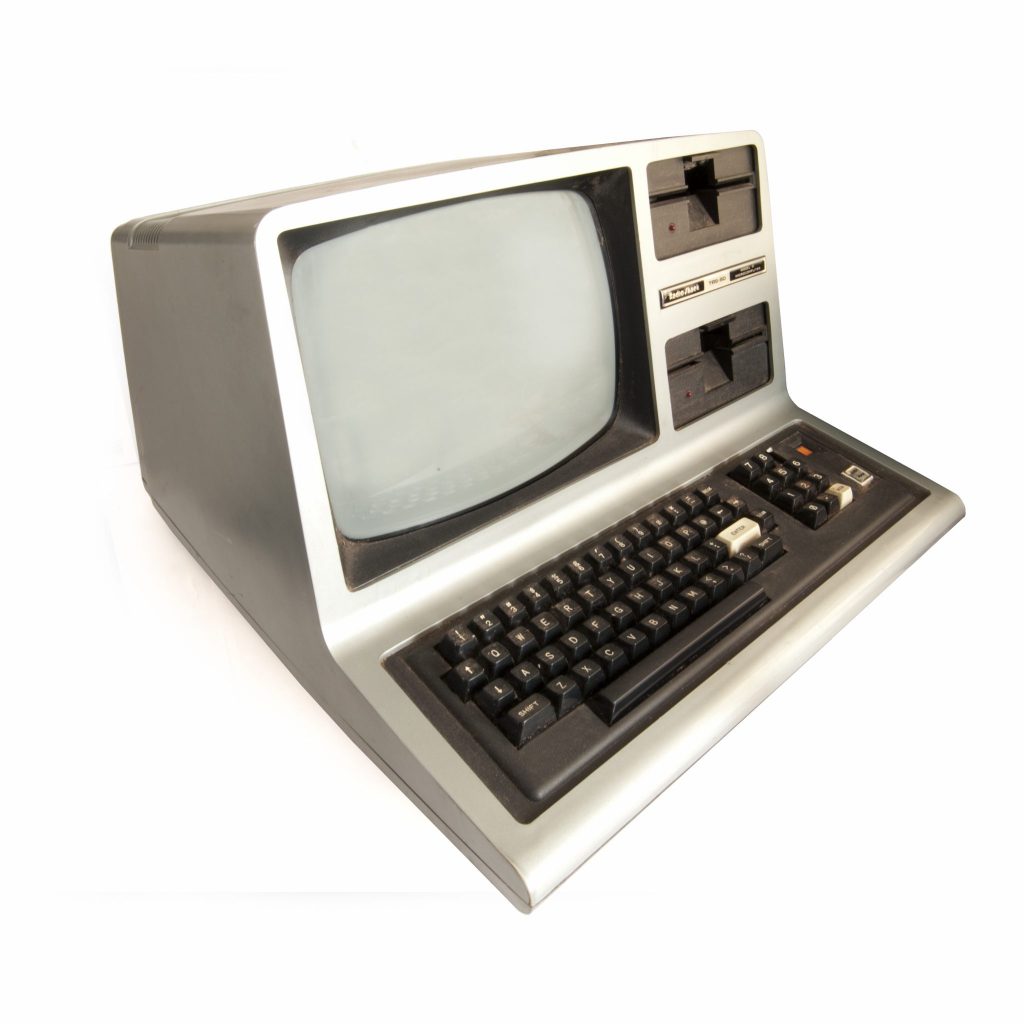
In some cases, I honestly believe that ancient technology could provide security against cybercriminals that is far better than anything that is being sold today. For the sake of illustration, let’s pretend that I was going to start some sort of business and that rather than buying a bunch of PCs and Macs, I chose instead to scour yard sales looking for old Radio Shack Color Computers from the 1980s. The Color Computer was arguably the most underrated computer of its day, and I have no doubt that in a few days’ time I could use one to code an application for use by a small business. So with that in mind, how secure do you think that application would be?
There is no way that the application would be able to leverage all of the security safeguards that have become so commonplace today. At the same time, however, I am betting that most hackers are not expecting to encounter an application running on extinct, 8-bit hardware from 30 years ago. To the best of my knowledge, none of the attacks that are commonly used today would be effective against such a system, because its microprocessor would not know how to interpret the instructions.
Now admittedly, that was kind of an extreme example. If I were starting a new business, I wouldn’t base it on 30-year-old hardware, nor would I recommend that you use a Radio Shack Color Computer in production. Even so, it’s hard to deny the idea that the use of such hardware would probably at least slow down a hacker simply because the use of such a system would be so far outside of anything that a hacker might realistically expect to encounter.
Legacy tech we still use
But what about legacy technology that actually is still being used in production? Although a case can be made that an old, obscure, or completely unexpected piece of hardware might actually improve security in certain situations, such an outcome is definitely not guaranteed. In fact, hackers have recently begun targeting legacy technologies.
The idea that a hacker might look to exploit some aging piece of hardware that is practically extinct is the exact opposite of what I said earlier about hackers targeting whatever happens to be popular at the moment. Even so, hackers are doing it, and there are at least two reasons why.
First, there is no rule book that says that hackers have to operate in a certain way. Cybercriminals are going to do whatever it takes to reach the desired result. Although certain generalizations can be made with regard to the way that hackers operate, hackers are by definition not bound by any rules that limit the techniques that they use.
Another reason why cybercriminals are increasingly targeting aging tech is because modern security mechanisms are becoming increasingly sophisticated, so in at least some circumstances it is easier to reevaluate an old device for previously undiscovered vulnerabilities than to try to penetrate modern defenses. One especially eye-opening example of this is the fax machine.
A few weeks ago, Check Point Software Technologies discovered a vulnerability in HP Officejet Pro All-in-One machines that could allow an attacker to gain a foothold on a network by simply sending a fax. Before I tell you how the exploit works, I want to quickly mention that HP has released a fix that you can download at HP.com.

So with that said, the hacker begins the attack by creating a document containing what equates to machine-readable malware and then faxes the document to the victim. The machine receives the inbound transmission and copies the document’s contents to the machine’s internal memory. At that point, the all in one machine treats the document contents as executable code. The code can then use them all in one device’s network connection to gain access to the network. This technique has been proven to be especially effective for spreading ransomware or spyware. You can read the full press release here.
Personally, I find it to be frightening, but not surprising that a fax machine can be exploited in this way. There is a lot of talk these days about the vulnerability of IoT devices, but I am guessing that most of us have at least some legacy tech on our networks that predates the IoT revolution. This might include anything from digital copy machines to old MP3 servers.
Every connected device is a potential problem
The newly discovered fax exploit illustrates the importance of taking security seriously for any device that is connected to a network, regardless of the device’s age or function. Even seemingly benign devices could potentially be compromised by cybercriminals with devastating results. As such, I recommend applying any available firmware updates to your devices and unplugging any devices that are no longer in use.
To guard against these types of exploits, it is important to keep all network endpoints up to date with any available security patches, regardless of the device type. It is also a good idea to disconnect any device that is no longer being used. That is your best defense against cybercriminals.
Featured image: Shutterstock



