If there’s one security takeaway from 2017, it’s that ransomware has become the biggest headache keeping cybersecurity personnel awake at night. (We saw a terrible virus shut down the system in “Transformers” via Frenzy’s wicked ways, but fortunately, that was fiction!) Ransomware doesn’t magically appear on your computer or network. So how does it get there? Once you learn how ransomware spreads, you have taken the first step to safeguarding your system.
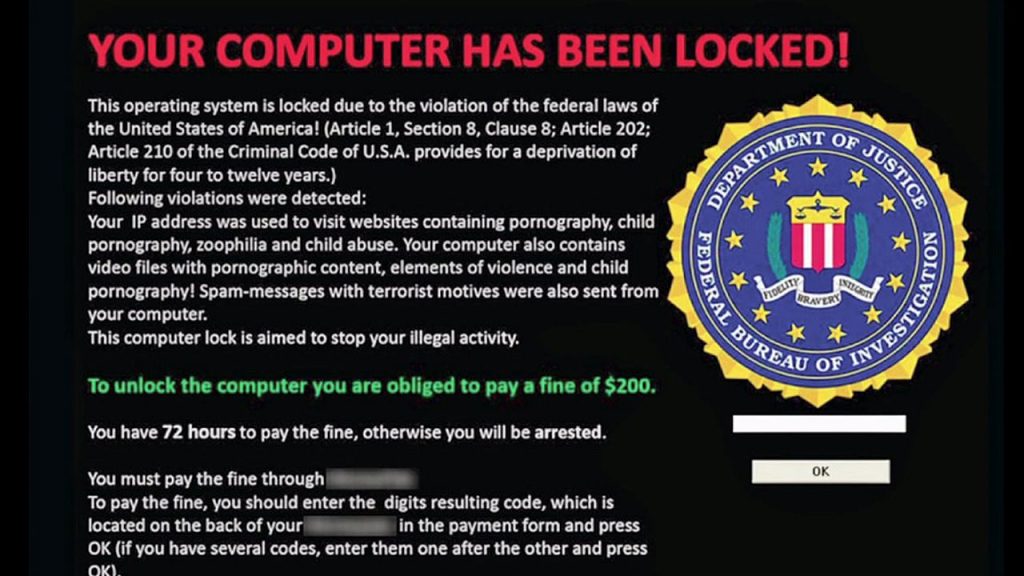
There are several false pretexts on which such ransomware files are pushed at you via the Internet. For instance, you might see a popup message while browsing telling you to click a button that will install an antivirus necessary for system security. Or you might see a similar popup telling you to install a driver file to make the computer work properly. Most of us have become savvy to these blatant attempts to spread ransomware — but a surprisingly large number still fall for it.
If you click on these bogus popups, a ransomware program will be installed that encrypts the data on your computer system and shows you a message to make a ransom payment to the perpetrators to have your data decrypted. In most cases, the payment is sought to be done using cryptocurrencies, so that nobody can track the actual account information or identity of the team spreading ransomware.
Techniques used for ransomware spreads
Before we delve deeper into the mechanisms and media used by ransomware attackers to target individuals, let’s know a bit about the advanced methodologies they adopt to keep their location and identity safe.
- Perpetrators of ransomware use Tor protocol to conceal their identity and location.
- Another technique used by them goes by the name of fast flux; it’s a Domain Name System method used by bots to conceal malware and phishing attempts.
- Domain shadowing, where attackers plug a malicious website within a genuine website, and redirect unsuspecting users to a website that releases malware to your PC.
- Fake sites masquerading as genuine ones.
- Attackers keep on using new IP addresses and moving to new locations to hide their identities.
- Domain generation algorithm that sends new domain addresses to the attackers after pinging Domain Name Servers.
- They use dynamic tactics to keep on defeating the safeguards put in place by cybersecurity personnel.
Email: Biggest gateway for ransomware
While the bogus popups we spoke about before are becoming less effective, email-based attacks continue to flourish and are behind most new ransomware spreads. It’s estimated that almost 60 percent of ransomware spreads via emails. These emails contain infected files, typically as attachments, and are worded to encourage the user to download the file and execute it.

It could be an enticing image, a Microsoft Word file from somebody posing as an employee of the firm, or a ZIP folder of the software you thought IT wants you to install for securing your computer. Cisco Systems’ 2017 Annual Cybersecurity Report revealed how almost 65 percent of email traffic is made up of spam messages.
In 2016, almost 8 percent to 10 percent of spam messages were seen as malicious. In hard numbers, that’s more than 1 billion emails. Whereas email clients are being bolstered to flag potential ransomware-laden emails as spam, attackers are depending on pure blitzkrieg tactics to perpetrate their iniquitous designs.
A major contributor to the continuation of email as the primary medium of spreading ransomware is the fact that attackers use social engineering tactics to increase their hit rates. Social engineering involves the careful planning of malicious communication by contextualizing the message, salutations, sender address, and tone to inspire trust in the receiver, leading to the desired action (double-clicking on that cursed .exe file).
Malvertising: The next biggest problem for the web user
Next to email-based ransomware attacks are attempts to infect computers by luring Internet users into clicking on popups and concealed web ads that ultimately lead to ransomware installations. This is how malvertising works:
- Attackers purchase legitimate advertisement slots on web platforms.
- They link these advertisements to exploit servers, which further redirect to a gate server.
- When a user clicks on the legit ad, they are taken to the exploit and gate server as well.
- This reveals vital information about the user’s operating system, software versions, plugin status in the browser, and other browser details.
- Attackers then use this information to understand the highest potential malware they can push to the victim’s system.
- The information also becomes a source of information to enable attackers to create highly contextualized emails with ransomware infected files as attachments.
Here’s shocking stat — in 2015, Google removed 780 million bad ads. Any guesses on the number for 2016? It’s more than twice – a whopping 1.7 billion suspicious ads. Web-based advertisement platforms need to up their game by building safeguards to make sure that slots are only sold to genuine advertisers; until then, malvertising continues to be a pain in the backside, for users, IT personnel, and pretty much everyone else.
Ransomware as a Service
It’s enough to give goosebumps to every Internet user on the globe to know that the best computer programmers and Internet wizards are looking to sell their expertise to cybercriminals to run ransomware campaigns, in return for 10 percent to 20 percent commissions on the loots. Sophisticated exploitation kits like Nuclear, Angler, and Neutrino are available to be bought by cybercrime groups. The basic idea here is to let computer and Internet experts work on the technology while experienced (and often novice) cybercriminals go about targeting organizations with the ransomware tools.
WannaCry: A case study
WannaCry ransomware was, arguably, the biggest shake of the Internet-powered world after MyDoom worm circa 2004. A Malwarebytes analysis on available packet captures information from a ShadowBrokers dump (go ahead, read about it https://blog.malwarebytes.com/cybercrime/2017/04/shadowbrokers-releases-more-stolen-information/), and binary files suggests that WannaCry worm spreads via an operation that finds vulnerable public SMB ports, using an NSA-leaked exploit called EternalBlue, and then another NSA-alleged exploit called DoublePulsar to invade networks, to persistently attack terminals, and begin unauthorized installations of the ransomware.
This puts into perspective how several layers, channels, and exploits can be made to work in tandem to wreak havoc via ransomware spreads.
It’s up to you
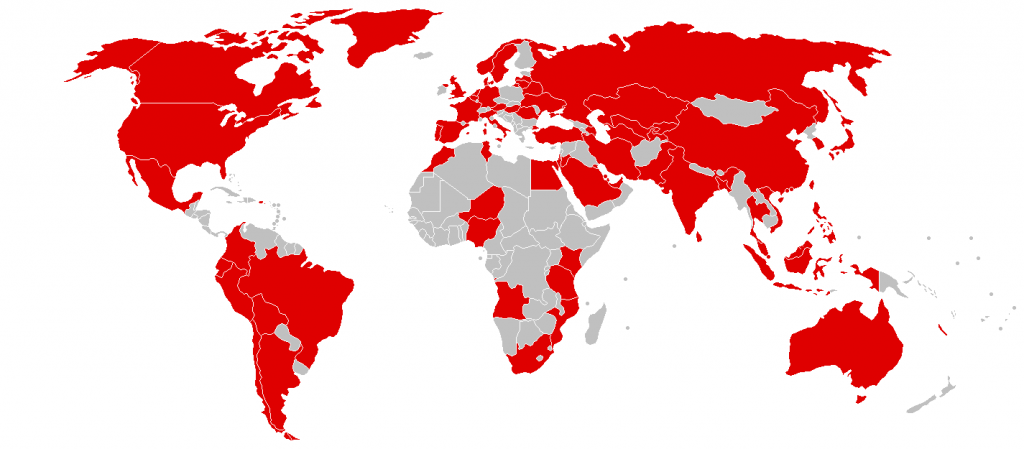
WannaCry ransomware disrupted businesses and government organizations in more than 150 countries. This is just one example of the tremendous disruptive potential of ransomware attacks. Knowing how ransomware spreads can help you to take the right steps to secure your personal and business computers. Always patch your applications for latest releases, never open any email you’re even slightly suspicious of, and install anti-ransomware applications that warn you of potentially dangerous websites. And yes, don’t click that bogus popup.
Photo Credit: Shutterstock




OK… I am a Systems Admin with 250 PCs to watch over. I have seen 2 cases of this ransomware. In the first one, we recovered most of the files we needed from usb drives. In the other we recovered from shadow copies. Here is what I learned at that time. Once the virus has installed itself, it needs to contact a server to get the key to encrypt the files. If it can’t do this it can’t do any harm. Many if not most of these servers are outside the US. If your company does not do business outside the US you need to block all traffic out of the country. WatchGuard has a service that will allow you to do this. It will not stop all possible attacks but it will reduce the chance of loosing your files. It also keeps up with the known IPs associated with ransomware and has a service to block those as well. While this may not help home users, it does offer a solution for business users.
Thanks for the feedback Harry. Fascinating.
All countries should have tougher penalties for this type of behavior.
I hope your week is going well.