In May, security researchers warned of a ransomware entitled “Jaff.” It was transmitted to potential victims via the Necurs botnet, which was also responsible for Locky and Dridex ransomware infections. Jaff’s attack method occurs by spam emails that contain a Word macro hidden inside a PDF file, that if opened, will unleash the ransomware and lock your machine’s files. The hackers behind Jaff demanded 0.5 to 2 bitcoin to release the locked files.
Now the tables have turned on the black hats behind Jaff. According to a statement by Kaspersky Lab researchers, there is a flaw in Jaff’s code that has allowed for a creation of a decryption tool. The statement reads:
“We have found a vulnerability in Jaff’s code for all the variants to date. Thanks to this, it is now possible to recover users’ files (encrypted with the .jaff, .wlu, or .sVn extensions) for free”
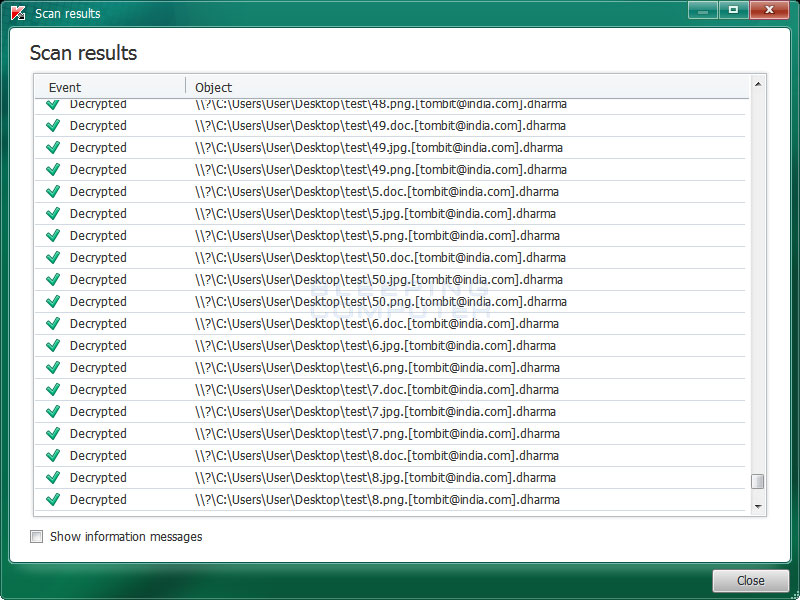
The Jaff decryption tool has been added to Kaspersky’s RakhniDecryptor, which already has an extensive list of ransomware that it is effective against. Installation of RakhniDecryptor is relatively simple, as it requires you to extract the tool from a downloaded .zip file. Once open, you are prompted to scan files that are encrypted. The tool then gets to work, which is a rather laborious task, but the end result is the elimination of all encrypted code locking your files. Bleeping Computer has a visual walkthrough of how to use RakhniDecryptor that I recommend if you need to be shown a more step-by-step process.
The major countries most affected by Jaff include China, India, Russia, Egypt, and Germany, but the Necurs botnet was wide-reaching and there are likely to be cases in far more countries than these. As such, you should stay vigilant and watch out for emails that contain suspicious PDF files (which may very well contain Jaff). If you do find yourself infected, however, understand that you do not have to pay the ransom and should instead utilize this tool as soon as possible.
Photo credit: Flickr / Christiaan Colen



