So, you’re working from home because of COVID-19 and you’re using Remote Desktop to connect to your Windows 10 office computer via Remote Desktop Protocol (RDP). You accidentally (or perhaps intentionally) select Shutdown when you click the Start button in your RDP session, and as a result, your office computer shuts down.
Now what? How do you get your office computer up and running when no one is in the office who can press the power button on your computer to boot it up again? And more importantly, is there any way you can prevent this kind of thing from happening if you’re the IT person in charge of managing employees’ computers at your company?
Using Group Policy
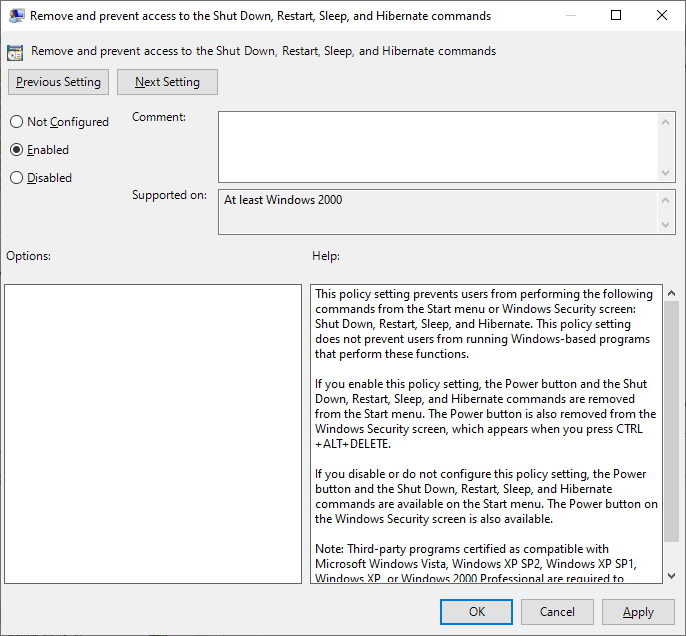
It’s tricky. One approach often used is to enable the following Group Policy setting:
This setting can be found under:
User Configuration \ Administrative Templates \ Start Menu and Taskbar
What it does is prevent users from selecting Shutdown, Restart, Sleep, and Hibernate from either the Start menu or the Windows Security screen. You could enable this policy in the GPO that’s linked to the OU where the user accounts of remote workers are found.
Note that this may not prevent users from shutting down their remote computers using other means, such as by invoking the shutdown command at a command prompt. But it does remove the most obvious way for a user to unthinkingly shut down their office PC when they finish doing their work for the day.
Editing the Registry
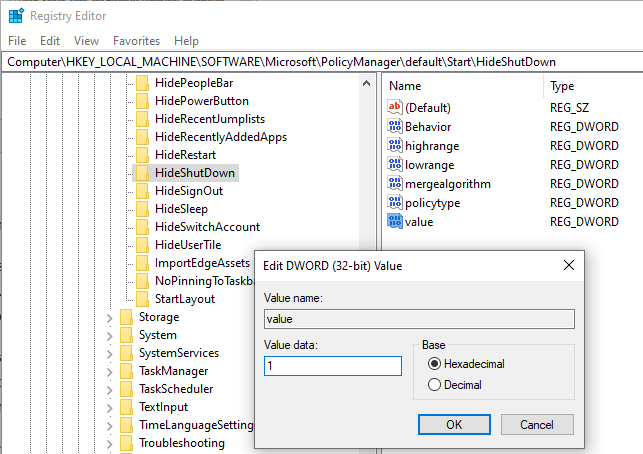
What if you want to want to hide the shutdown option on the Start menu but leave all the other options present like Restart, Sleep, Hibernate, and also the Disconnection option for an RDP session? It turns out you can do this by editing a registry setting, but the setting you need to use will depend on the version of Windows 10 your PC is running. Specifically, on Windows 10 v.1803 or earlier set the following registry value equal to 1:
HKLM\SOFTWARE\Microsoft\PolicyManager\current\device\Start\HideShutdown
But on Windows 10 v.1809 or later set this registry value equal to 1:
HKLM\SOFTWARE\Microsoft\PolicyManager\default\Start\HideShutDown\value
Here is what it looks like on Windows 10 v.1909:
In a managed environment you can, of course, use Group Policy Preferences (GPP) to deploy Registry settings like this to users’ computers.
Removing shutdown privileges
What if you really want to prevent users from shutting down their computers? I mean not just hide the most obvious ways of doing this from them but actually removing their shutdown privileges from them?
Group Policy allows you to do this by modifying the user rights on the computers targeted by the GPO you’re editing. The particular setting involved can be found under the following path in the Group Policy Editor:
Computer Configuration \ Windows Settings \ Security Settings \ Local Policies \ User Rights Assignment\ Shut Down the System
By default, user accounts that are members of the local administrators, backup operators, and users groups have the right to shut down the computer. The easiest way to prevent the user from shutting down his machine is to simply remove the users group from the list above. But before you use this “extreme” approach see the section titled Beware of collateral damage later in this article.
Other approaches to remote desktop access
Making it hard for users to shut down their office PCs over a remote desktop connection is sometimes more trouble than it’s worth as we’ll see shortly. Because of this, some administrators avoid trying to implement such solutions and instead accept the inevitable that some employee PCs will end up being turned off at the end of the workday — and then try to implement an approach for automatically getting them booted up again before morning arrives. One of the most commonly attempted methods for doing this is to use Wake On Lan (WOL), a networking technology supported by many network adapters that allow the computer to be remotely turned on when it’s sleeping or hibernating or in some cases fully powered down. WOL works by allowing a “magic packet” (a specially crafted Ethernet packet) to boot the motherboard causing the operating system to launch.
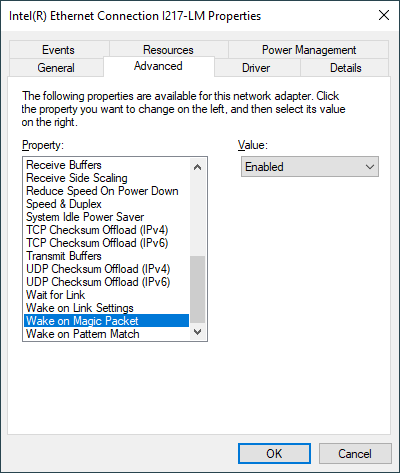
Implementing WOL can be tricky. First, it requires that you have enabled WOL functionality in the system BIOS of the computer, so your system’s motherboard has to support this functionality. Second, it requires modifying the settings of the machine’s network adapter. To do this you open Device Manager, expand the Network Adapters node, and right-click on your Ethernet adapter to select Properties. Now, on the Advanced tab make sure Wake on Magic Packet is Enabled like this:
Next switch to the Power Management tab and make sure that the setting “Only allow a magic packet to wake the computer” is enabled:
Now that you’ve enabled WOL on the machine you need some program that can send a magic packet to it when you want to boot it when the machine has been turned off. The systems management software your company is using probably already has this functionality; otherwise, there are lots of programs around you can choose from, many of them free. TeamViewer is one of these tools and is often used in helpdesk environments. One thing to keep in mind: It’s called Wake On Lan for a reason. Some routers will block the Magic Packet if it comes from outside the network — for example, sending it via the Internet.
Another approach is if your PCs have Intel processors that support the Intel Active Management Technology (AMT) of the Intel vPro platform which allows you to remotely control PCs even when they crash or are turned off.
Banning remote desktop access: Beware of collateral damage
Whatever you do, be sure you first know about any difficulties or problems that may arise when you implement a solution that makes it difficult or impossible for remote users to shut down their office computers via RDP. The biggest consideration here is how this may affect helpdesk support for these remote workers. For example, sometimes a user working from home and using Remote Desktop to access their office computer will encounter a problem of some sort with their office computer. The user phones the helpdesk and the support technician walks the user through some troubleshooting steps. The user follows these steps but the problem isn’t resolved, so the support technician takes things to the next level and tells the user to try performing that age-old fix of rebooting their office computer. “How can I do that? IT has taken away that menu option from my machine.” Heads are scratched as the support call drags on and the user falls behind in their work assignment.
Just another day in the trenches of IT.
Featured image: Shutterstock