Product Page: click here
Free Trial: click here
Introduction
Cayosoft Inc. is a global software vendor that develops products to help organizations manage and protect their Microsoft infrastructure, as well as adopting a modern cloud infrastructure.
Two of its main products are Cayosoft Administrator, a powerful and complete management solution for Active Directory (AD) on-premises, in Azure, and/or hybrid, and Cayosoft Guardian, which we will cover in this review (v1.2.2, released on May 19, 2020). Guardian is a new product from Cayosoft that aims at protecting and recovering Active Directory data, be that on-premises, Azure, or hybrid. It monitors all directory changes so that administrators can quickly see, understand, and rollback mistakes or malicious changes across their directory. When rollback is needed, Guardian provides an automated recovery plan that does not involve incomplete or time-consuming backup files.
Why would we need Guardian?
Most AD, Exchange, or Azure/Office 365 administrators have faced at least one case where they had to restore one or more objects such as a user account or a group for example. This can be an easy task, or it can easily be a nightmare for several reasons. Let us consider the following:
- Microsoft will not restore your directory data. If you have to restore something, you have to know how to it yourself (if it is even possible).
- The AD Recycle Bin only protects against deletions. But what about those cases where an admin makes a change by accident? It is not as bad if it is one or two objects and we know which ones and what changes were made, but what if it is hundreds of objects? What if the Recycle Bin feature is not even enabled?
- Not all object types are protected. For example, Azure AD Recycle Bin was primarily designed to protect user objects. It will also protect Office 365 groups (aka unified groups), but it does not offer any protection for distribution or security groups! If one of these gets deleted, that is the end of it.
- What happens if an attacker, or rogue administrator, disables the Office 365 unified log and makes changes? How will other admins know what was changed and roll back those changes?
- Organizations can make use of a Security Information and Event Management (SIEM) solution to centralize and secure all audit logs, but these don’t make rolling back changes much easier.
Key features
Guardian has several key features that distinguish it from the competition:
- It continuously monitors the directory and records any changes made in the on-premises and Azure AD;
- It makes it extremely easy to find a particular change and roll it back immediately, while other tools typically rely on backup files. Additionally, it proactively identifies and alerts critical changes, plus users can create additional alerts;
- It goes beyond Microsoft’s Recycle Bin. Guardian allows admins to restore what native tools cannot, such as groups, changes to an object’s attributes, Office 365 licenses, hard-deleted objects, and more;
- It provides a single solution for any scenario, on-premises, cloud, or hybrid, by centralizing and continuously recording all directory changes;
- Quick recovery. The key to minimize outages and reduce end-user downtime is the ability to roll back the change(s) that caused the outage in the first place, and Guardian provides immediate rollback without wasting time searching dozens of backup or log files;
- It supports multi-tenant and multi-forest environments. After all, not every organization runs a single tenant/forest, so Guardian makes it easy to protect multiple environments from a single console.
Requirements and installation
The requirements for Guardian are simple. In terms of hardware, we need a physical or virtual server, or a pre-built Azure VM, with a 2GHz or higher Intel-compatible dual/quad-core CPU, at least 8GB of RAM (32GB or more recommended for environments with over 100k users), and at least 180GB of storage.
In regards to software, Guardian runs on Windows 10 or Windows Server 2016 and above. Additionally, we need Google Chrome, Mozilla Firefox, or Microsoft Edge based on Chromium. As its database, Guardian uses Microsoft SQL Local DB engine (included), with support for SQL Server coming soon.
Installing Guardian could not be simpler:
- Download the software and run it with the administrator account you want Guardian to run as;
- Accept the license agreement and click Install:

- The installation process will then start:

- After a short while, Guardian is installed:

We are not able to specify the account that Guardian should run as, or where it should be installed, but this is on the roadmap and should be available in Q2-Q3 2020.
Guardian’s sign-in experience is integrated with Azure AD, meaning we can use our on-premises AD account or our Azure AD account to sign-in. Azure AD security features, like Multi-Factor Authentication and Conditional Access Policies, are enforced when we authenticate.
 Once logged in, we are taken to Guardian’s Dashboard (more on the interface later):
Once logged in, we are taken to Guardian’s Dashboard (more on the interface later):

Configuration
Before we have a look at the interface, let us first connect Guardian to our on-premises AD and Azure AD so that we have some data to look at.
To start with, we will connect Guardian to our Azure AD / Office 365 tenant, and later to our on-premises AD. To add our tenant:
- Click Add tenant under the Azure AD / Office 365 section in the Dashboard:

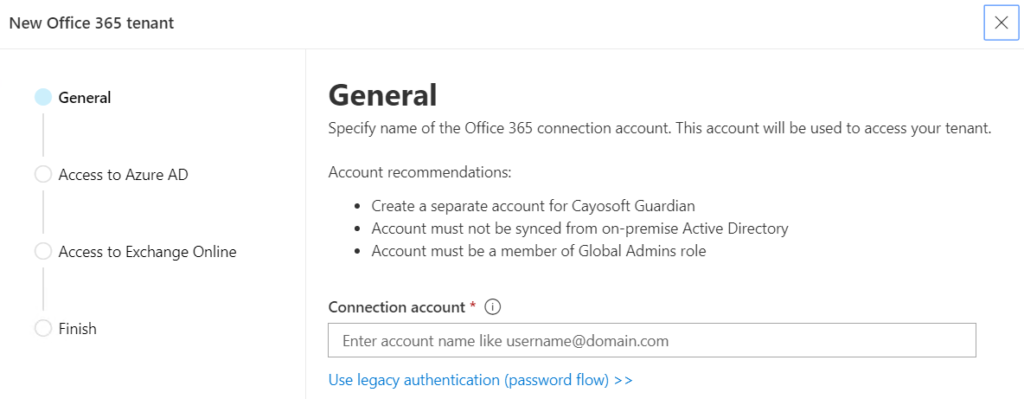
- In the New Office 365 tenant wizard, we specify the Office 365 account to connect to Azure. This account needs to be cloud-only (i.e., not synchronized from the on-premises AD), and assigned the Azure AD Global Admin role:
- The following screen is where we give the service account the required access to Azure AD:

- The permissions are all listed before we accept them:

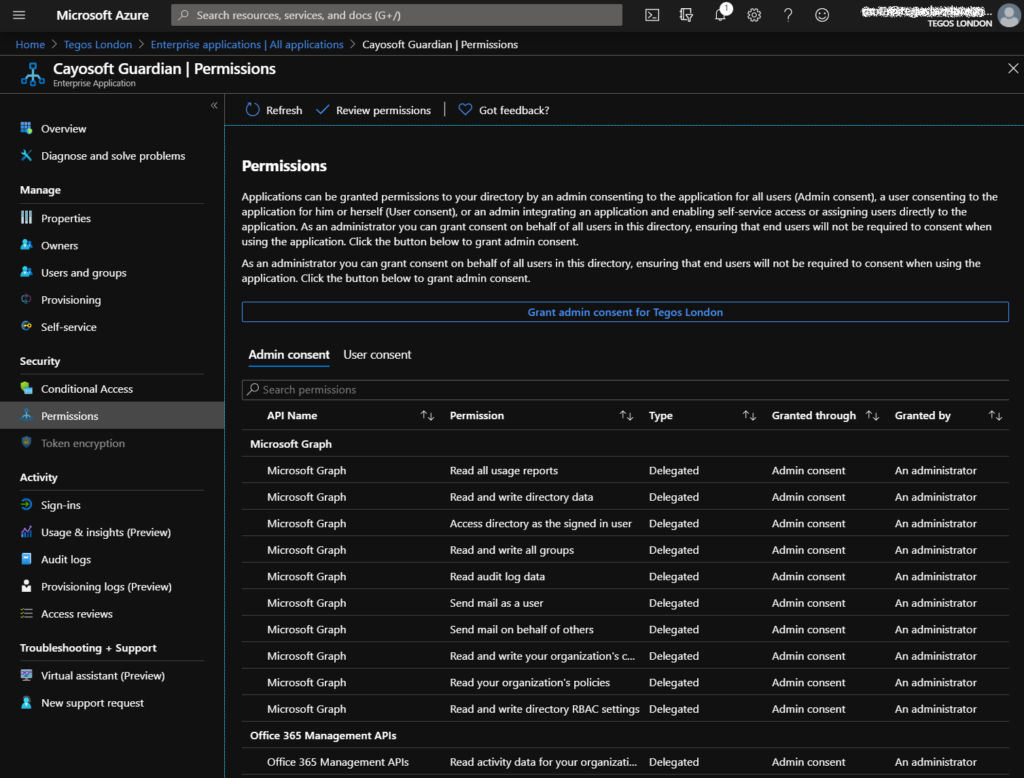
- These are also detailed in the Azure portal under Enterprise Applications:
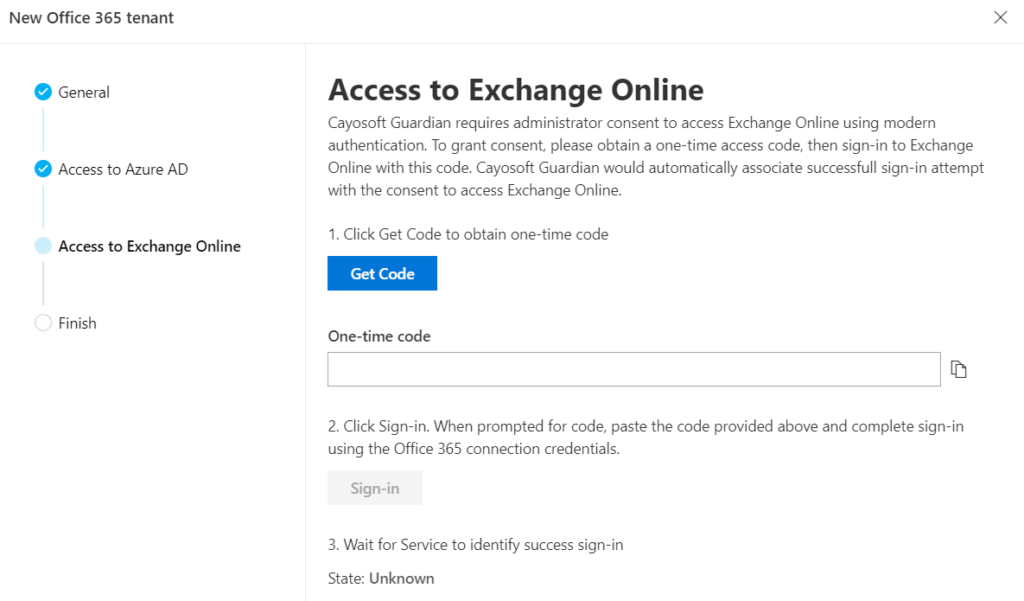
- Next, we grant Guardian access to Microsoft Exchange REST API through a one-time code (it is good to see it using this new method of accessing Exchange Online):
- And we are done!
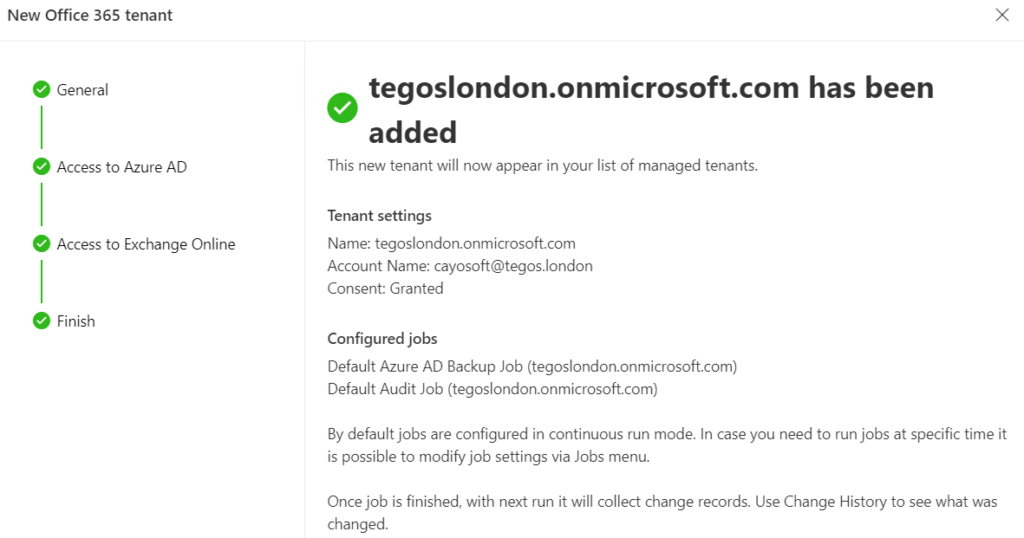
Adding our Azure/Office 365 tenant immediately enables change monitoring for continuous protection against unwanted changes, as we will see later. Now, our tenant will appear in the list of managed tenants under the Azure AD / Office 365 section:

Since this is a hybrid environment, let’s add the on-premises AD as well:
- Click on Add domain in Active Directory on-premise section in the Dashboard:

- We then specify the AD service account we want to use (it must be a member of the Domain Admins group) and click Next.

- The final step is to enable, or not, auditing which allows recording the initiator of certain changes in AD:

- Once more, we get the confirmation screen once everything has been configured:
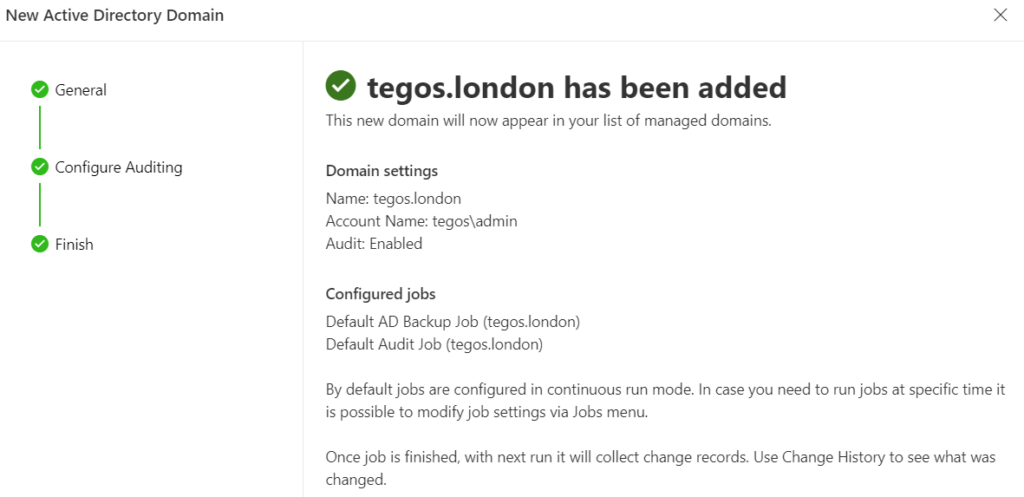
- Our AD domain will now appear in the list of managed domains under the Active Directory on-premises section:

Note: In hybrid or cloud-based environments, Cayosoft Guardian discovers if Azure AD Connect is installed in the domain being added, and connects to it to run sync cycles when needed.
The final settings we will be configuring are related to notifications. Guardian uses notification channels that allow it to alert admins of any important changes, like those to key security groups for example. These notifications can be sent through Teams into a specific channel, or by email. This means that the service account we use to connect to our tenant needs a Teams and/or Exchange Online license.
To configure the Teams Connector, we:
- Navigate to Connectors under Alerting;
- Select Microsoft Teams Connector and click Properties;
- All we need to configure is the team name under Default Team, and the channel we want the alert to be sent to:
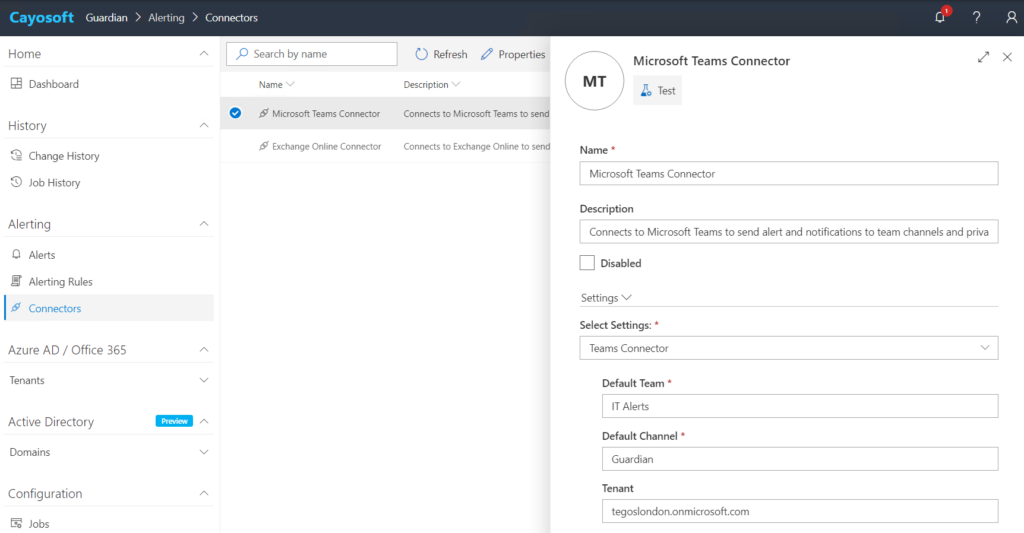
- Finally, we click Save and then Test to make sure it is working. If it is, we will receive a test alert in Teams:

Configuring the Exchange Online Connector is as easy. We configure the sender, which is the email address of the service account, and the recipient of the alerts:

If we now navigate to the Alerting Rules section, we can see all the alerts that can trigger these notifications:

For example, there is an alert for when someone is added to an on-premises highly privileged group such as Domain Admins or Enterprise Admins. We can customize each alert, including the alert message:

We can even customize the filter used to trigger the alert, or create our own alerts but it is not straightforward. Cayosoft plans to add some additional out-of-the-box alerts and a wizard in either v1.3 or v1.4 later this year. Alternatively, if a customer needs a specific alert, they can request it and Cayosoft will send them the query/filter. Great service!
We can also create additional notification channels that are used by different rules. This allows admins to safely test new channels and alert rules, or send different alerts to different recipients.
Interface
Straightaway, we can see that Guardian has a very modern and clean interface:

The main Dashboard gives us an overview of the status of Guardian and the changes in our environment. The Protected Objects diagram shows us how many objects are being monitored and protected, and Recent Changes shows the number of changes performed recently:

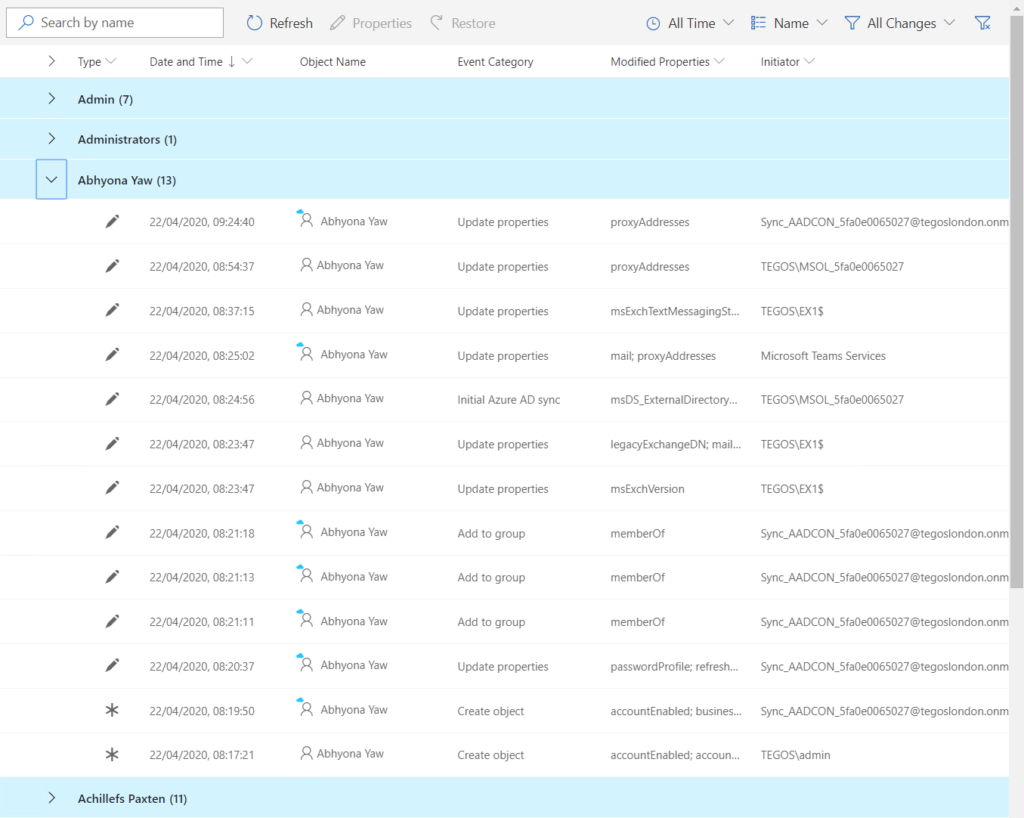
Change history is one of the main sections of Guardian as it is used to view and restore object changes:

All the changes in the configured environments are listed with the most recent on top. Details include the modified object, what property was changed, by whom, and more. Quick search allows us to easily search and find changes.
The Properties button shows additional information such as any alerts the change might have raised, or the old and new values for the changed property:

The Restore button does what it says, it reverts the selected change history record. But we will explore this in more detail in the next section.
To make easier to see all the changes that happened to a given object, it is possible to group all changes by Name or even by Change Type:
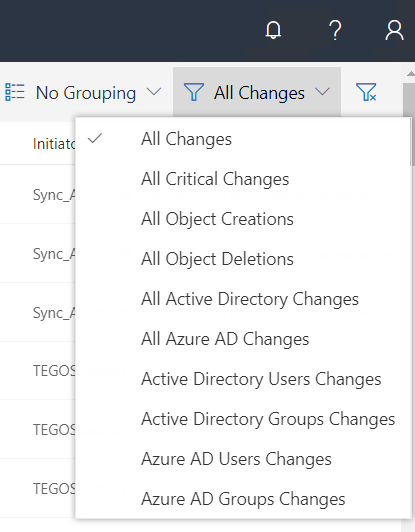
We can also use Filters to get a subset of data for easier viewing and analysis:
Under the Azure AD / Office 365 and Active Directory sections we can explore our cloud and on-premises directories. For example, under Groups we see a list of all our groups present in Azure AD:

Under Users, all the cloud and synchronized user accounts in Azure AD. This is extremely useful as it also allows us to see all the changes done to a particular user account, and revert any or all of those changes:

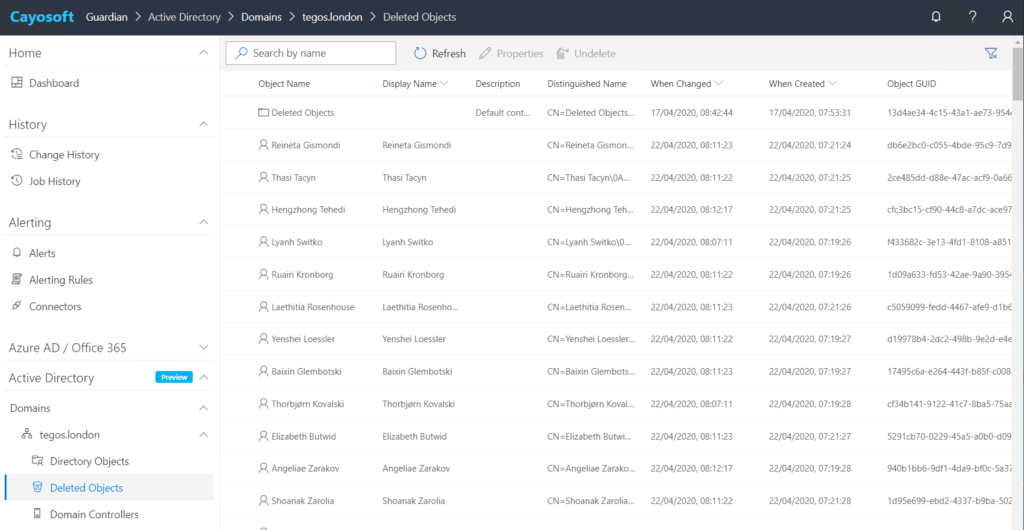
Active Directory has a similar structure. For example, we can use the Deleted Objects section to list all the objects that have been deleted from the directory, any changes made to them prior to deletion, and revert any of those changes or recover the object itself:
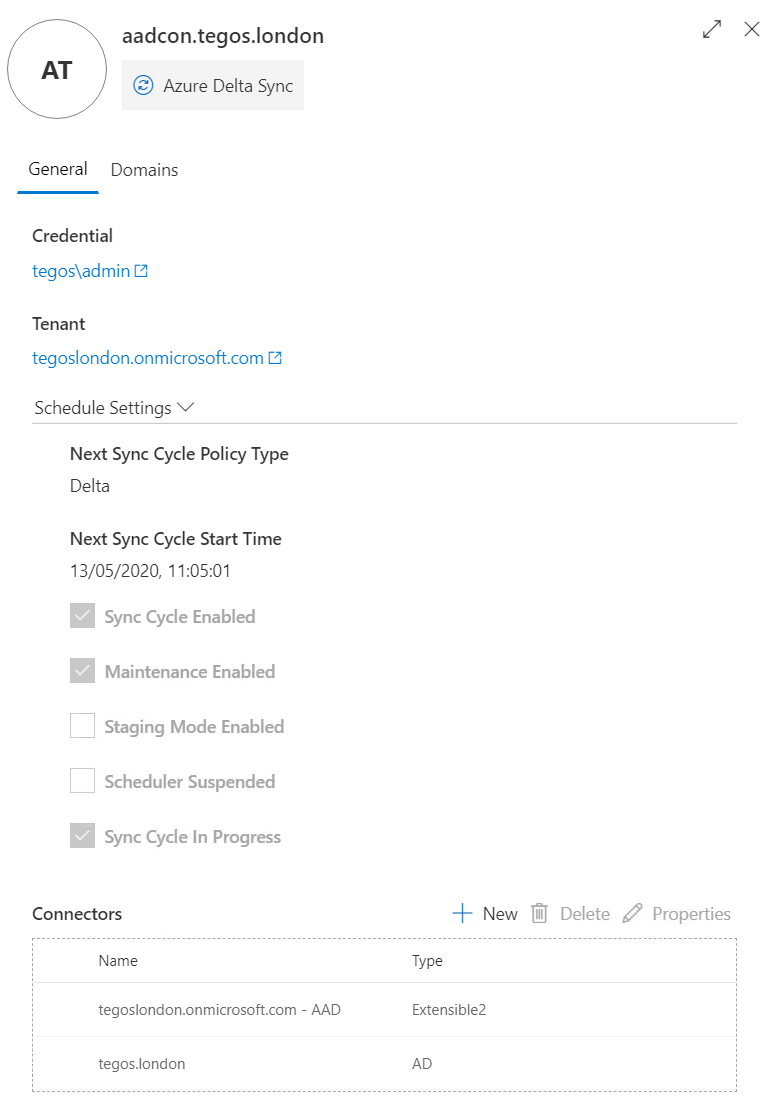
Another feature of Guardian that I like is that it lists our Azure AD Connect server(s), and it even allows us to trigger a delta synchronization without us having to log in to the server or use PowerShell:

It also shows if a sync is currently in progress, when the next sync is expected to happen, and some of the main features we have enabled or disabled in Azure AD Connect:
Detecting and reverting changes
Restoring objects to a previous state is pretty much the bread and butter of Guardian. Maybe a change was made to an on-premises or cloud object that had unforeseen consequences, or maybe it was done by accident or by a malicious admin or attacker. No matter the reason, every admin will eventually need to rollback a change made to a directory object. And this is where Guardian shines.
To be able to revert a change, Guardian uses Jobs, which are automatically created when we add a tenant or domain and allow Guardian to record any changes made to that directory:

By default, jobs are configured in continuous run mode but can be configured to run at specific times. Additionally, we can split the actions of each job into several different jobs. However, given that Guardian has no noticeable performance impact on the directory servers, I don’t see why we would need to do this.

So now that we know Guardian is protecting our directory, let’s try to cause some damage. First, I am going to add a user to the Domain Admins group using the native Active Directory Users and Computers console:

Almost instantly, we receive a notification in Teams informing us that a user was added to this group:
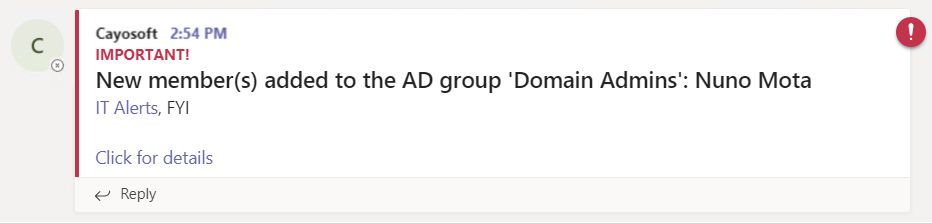
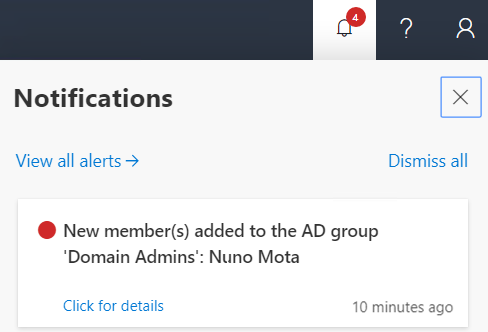
The same notification is also present in Guardian’s console:
If we click on Click for details either on the Teams or on the Guardian console notification, we are taken straight into the details of the change, where we can see what was changed (the member property of the group in this case):

To revert the change, all we need to do is click on Restore (we are notified that hybrid restores are still a preview feature):

Guardian creates a new job to revert the change which completes almost immediately:

If we navigate to Change History, we can see both the original change made (the red circle means it raised an alert), as well as the new change to revert it:
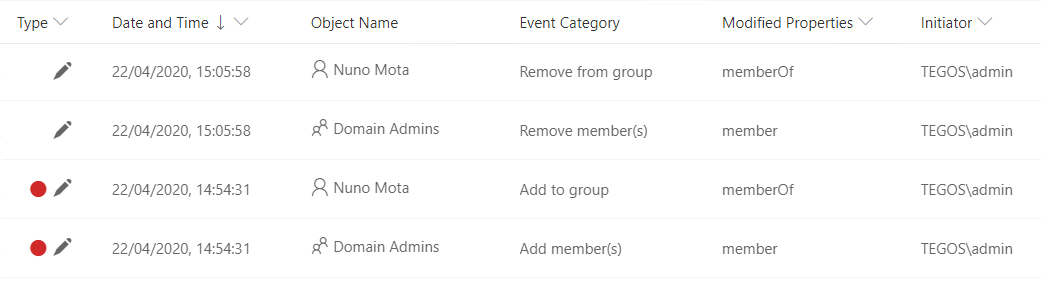
Restoring Distribution Groups (DG) is a great example as there is currently no way of restoring a deleted DG in Office 365… When deleted, an Exchange Online DG is not moved to the Azure AD Recycle Bin and thus cannot be recovered using native tools. Guardian fixes this problem by quickly recreating the group object, converting it to a DG using Exchange Online, and then restoring the group’s membership. Let’s try deleting the following cloud-only DG and see if we can restore it in its entirety:

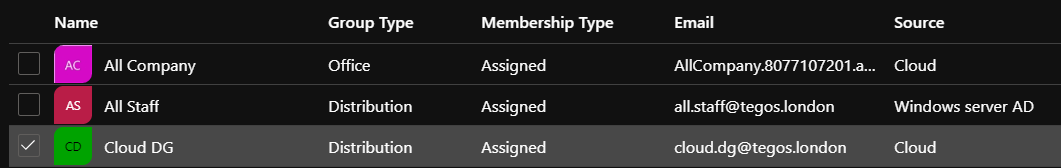
Once I delete this group, we can see that it does not show up in the Azure AD Recycle Bin:
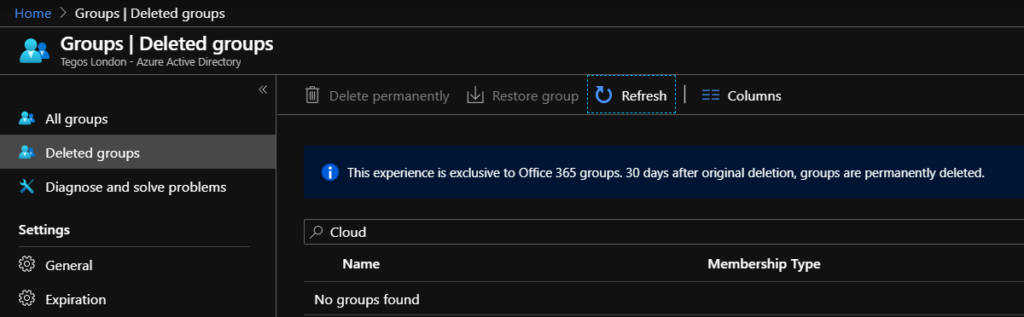
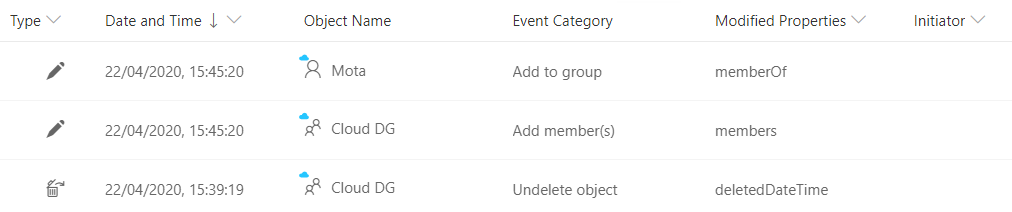
Guardian detects the deletion, as well as all the membership changes that come with the deletion:

As before, all we need to do is select the Delete object change, click on Restore, and wait for the Job completed successfully notification to appear in the Notifications area:
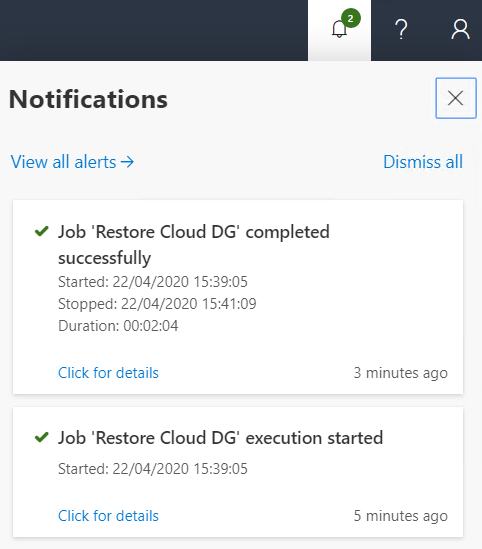
Once the restore is complete, we can see the new change records added to the list: Undelete object as well as Add member(s):
The group is now back in Azure AD with all its members!

Another important feature of Guardian is the ability to revert changes in bulk. Imagine an HR system updates a property wrongly for several users or a scrupulous admin or attacker that creates a mail forwarding on everyone’s mailbox. In these cases, we can easily roll back all the changes in one go. We start by searching for the changes we want to roll back (we can search or group these together). We then select the changes we want to roll back either individually or all of them at the same time and click Restore:

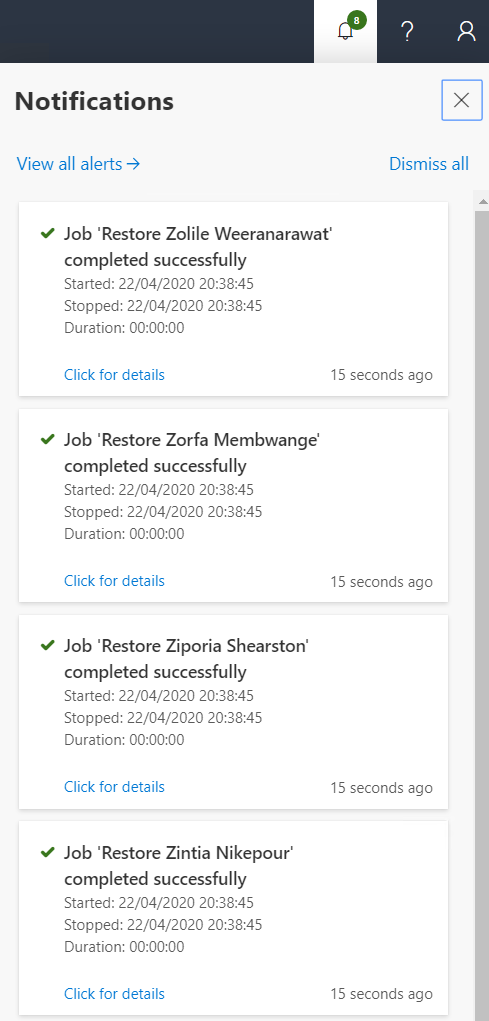
Within a few seconds, we get a Job ‘Restore <user>’ execution started followed by a Job ‘Restore <user>’ completed successfully notification in the Notifications area:
When the restore is complete, we see the new change records added to the list:

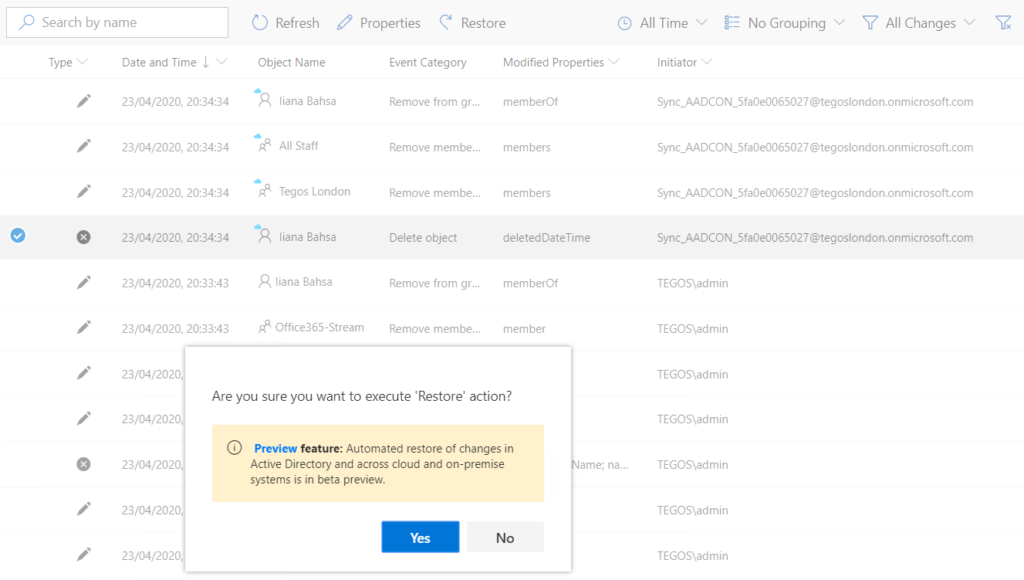
Let us look at another scenario. User Iiana Bahsa has had her account deleted from an on-premises directory by someone or something. The account is synced to Azure AD, so in the Change History we see her on-prem account being deleted followed by her cloud account (notice the blue cloud icon):

The admin doesn’t know if s/he needs to restore the AD account, the cloud account, or both. Typically, we would restore the on-prem account and then let Azure AD Connect sync it to the cloud with all its properties. However, while rushing to get the issue fixed as soon as possible, the admin restores the cloud account instead (and the cloud account alone):
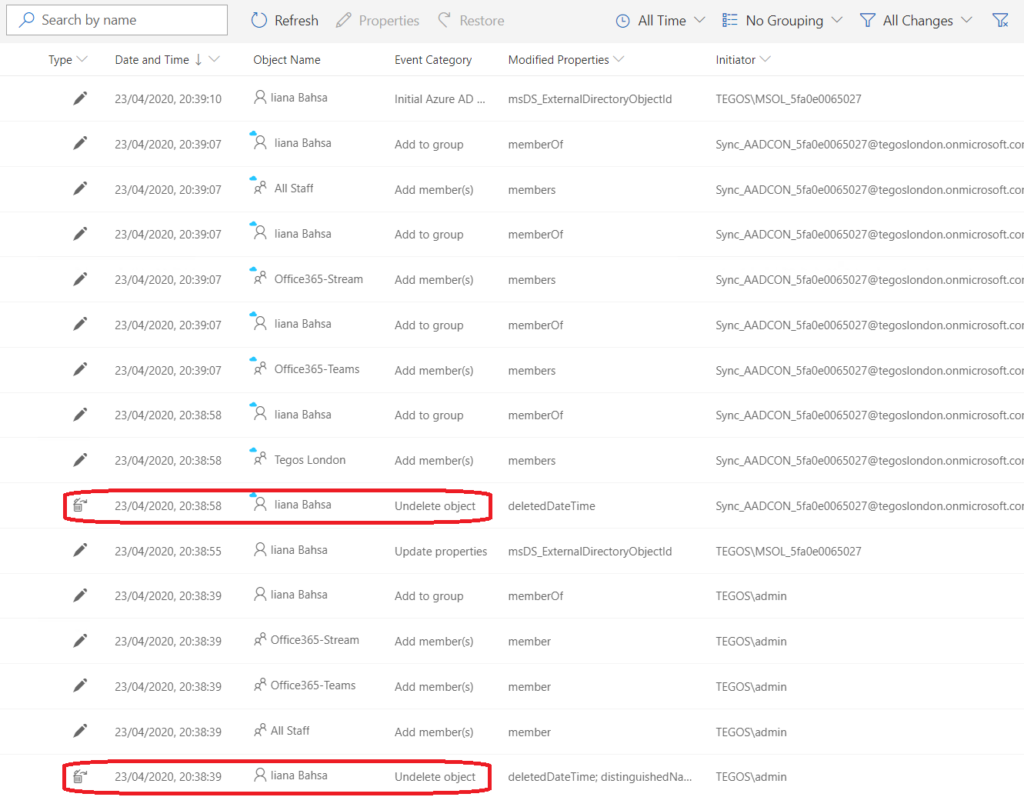
After a short while, Guardian starts a restoration workflow. If the account is in the Recycle Bin it gets restored, and all the properties checked and restored (like group membership). If the object was hard deleted, it gets fully reconstructed. Another great thing about Guardian is that we don’t need to know if the user has an on-prem account, cloud-only account, or hybrid. Guardian takes care of all of that for us! After an automatic delta sync with Azure AD Connect, all is back with just one click. Below, we can see that everything was automatically restored, such as both accounts, groups membership, and so on:
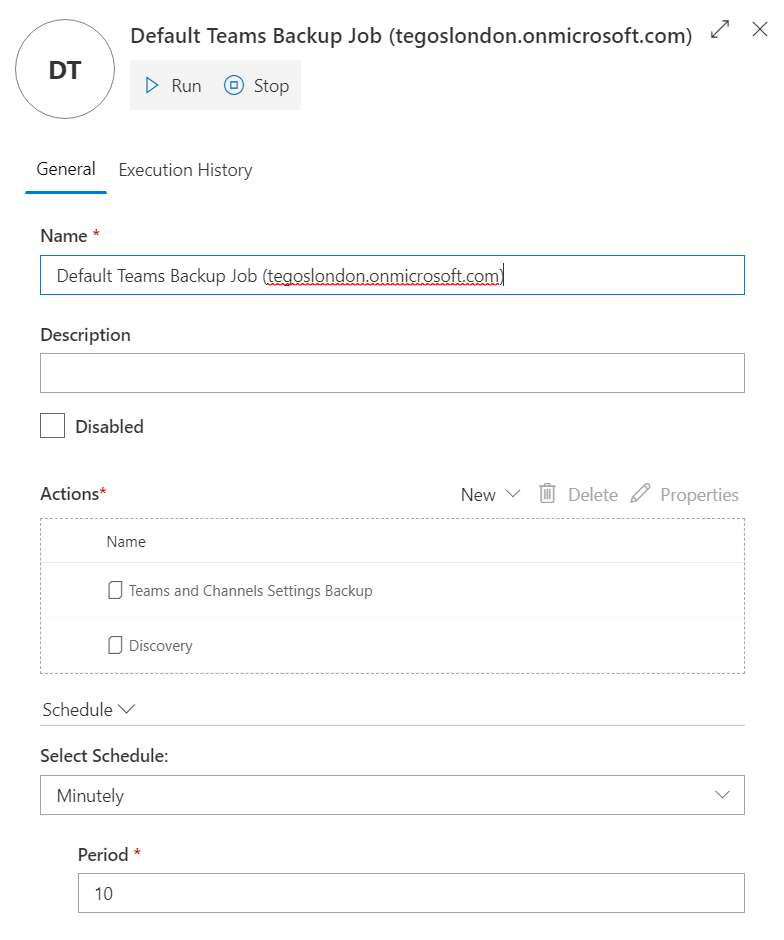
Another great feature of Guardian is that it also monitors Teams changes through the Default Teams Backup Job that runs every 10 minutes by default:
Let us take the following team as an example:

In the Change History window, we can see Teams operations being monitored such as the creation of the team itself, creation of channels, and the addition of owners for example:

Re-adding a user back to a team is as easy as before. We simply select the operation we want to rollback and click Restore:

The user is then added back to the team:

There is also an alert created by default that alerts admins of any Guest changes made to a team. For example, if we enable the Allow guests to delete channels option:

We are alerted to the fact:

Under Change History, we can see exactly what was changed (under Modified Properties), as well as who performed the change and on which team (both under General):

Certain actions cannot be rolled back, such as the deletion of channels for example, since Microsoft does not provide an API for that:

Other actions such as those performed on Exchange or on Exchange attributes in AD also get logged. However, Guardian is not a backup solution for user content like user files, mailbox, posts, and such, so do not expect to be able to recover a mailbox deleted ages ago just because you see the deletion action in the Change History.

The verdict
Guardian clearly delivers on its promises. Its continuing monitoring and protection of on-premises and/or Azure Active Directories guarantees that most changes can be rolled back swiftly and at the touch of a button, without administrators having to go through numerous logs or resort to backup scripts or files. The fact that it is extremely easy to install and configure makes its deployment painless and hassle-free. All in all, an awesome tool that I would not have any problems in recommending to anyone responsible for managing Active Directory!

Rating 4.6/5



