One of my favorite podcasts is Darknet Diaries by Jack Rhysider. He offers some real insight into the importance of securing your network. In a two-part episode, he starts its coverage talking to a tight-knit group of friends that enjoy hacking Xbox devices and ends the series with their tragic end. What was most interesting to me in that series was a group of kids were able to purchase Xbox dev kits (real, working Xbox machines with developer tools baked in) from a liquidator. Worse, Microsoft (presumably) dumped them there and seemingly never requested they be destroyed. These kids would purchase the discarded devices to not only try out an unreleased game box but also hack into Microsoft and pretty much every major game developer’s network to play unreleased games or even download source code.
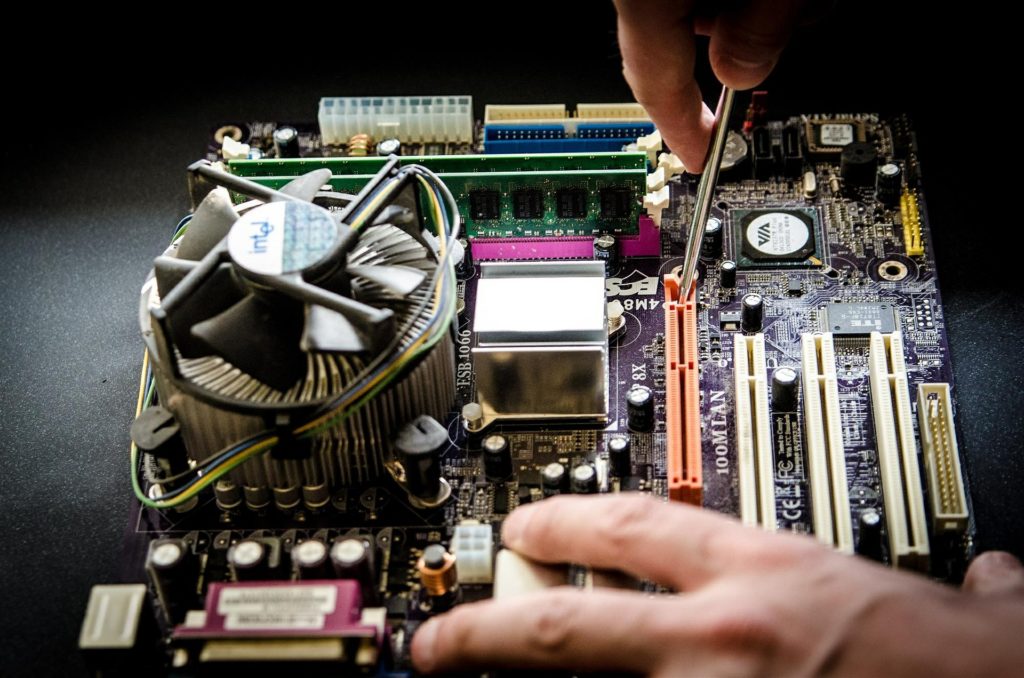
The podcast taught me that even if you plan to liquidate your assets, it is critical organizations have a chain of custody for every device and ensure the proper destruction where it is needed.
In today’s T-Suite Podcast, I talk to Richard Greene, managing partner of Liquid Technology. We talk about how IT organizations should properly manage their liquidation projects and how to properly dispose of materials and destroy company data. We also talk about the industry best practices any liquidation facility should follow, along with some interesting stories along the way, including one dealing with the now-defunct Theranos.
You can reach Richard and his team at Liquid Technology.
Special thanks to Jennifer Handshew for introducing me to Richard.
