Sponsored by Netsparker
Discovering that your website or web application has a vulnerability is just the beginning of a very complex process. The primary goal of this process is to make sure that this vulnerability disappears. This may seem simple, but when you consider that you may have to oversee thousands of such processes on a regular basis, you need the right tools to make it possible and easy. This is why you need a good vulnerability management solution.
The same principles that apply to web vulnerabilities also apply to network security vulnerabilities and other types of common vulnerabilities. Both the vulnerability management process and the functionality of vulnerability management tools may be subdivided into three closely related subjects: vulnerability scanning, vulnerability assessment, and the overall vulnerability management.
What is a vulnerability scanner?
The term vulnerability scanner may apply to very different classes of software. By default, the term scanner suggests that the software takes something as input, scans it, and gives you the result — nothing else. There are solutions on the market that are designed just to do that. However, a professional, business-class vulnerability scanner must provide much more than just an engine for vulnerability scanning. It must also help you evaluate the impact of those vulnerabilities and help you fix them.
To understand the processes that are related to vulnerabilities, you may compare them to processes that are related to servicing a car. Finding a vulnerability during a vulnerability scan is like observing that a check engine icon lights up on your car dashboard. You know that something is wrong, you may even know the name of the condition and the location, but that tells you nothing about what needs to be done next. This is where assessment and management come in.
What is a vulnerability assessment?
Vulnerability assessment is like going to a service station and having someone attach a remote sensor to your car computer. The car service expert will read the details of the error and understand exactly what is wrong. Then, they use their knowledge and experience to tell you, whether you can still drive your car for a while or whether it needs immediate servicing. That car service expert is the key element of the assessment and the remote sensor is the tool that they use. And the tool is just as important because, without it, the car service expert would spend hours looking through the engine manually.
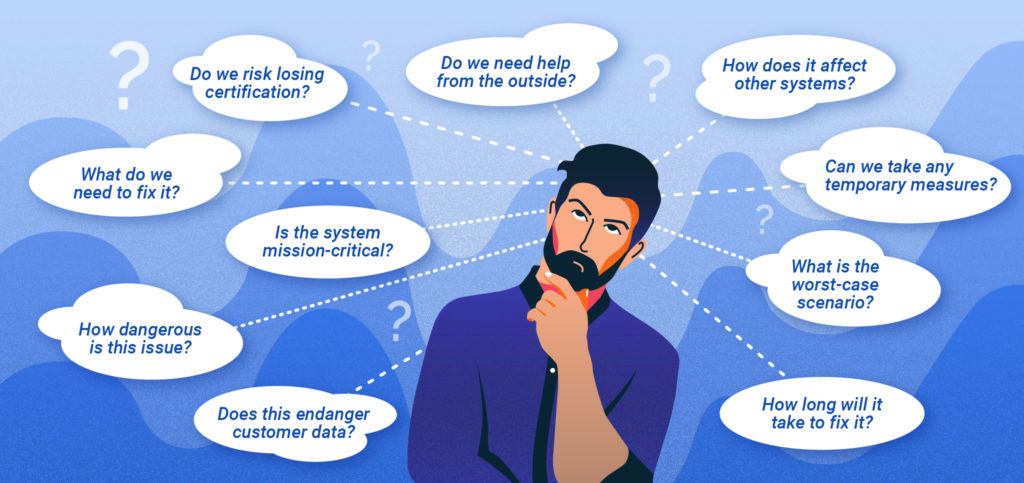
The situation is similar when it comes to information security. The tool itself is necessary because it provides information about security vulnerabilities and may greatly automate the process. A security expert would spend hours on penetration testing with tools like Metasploit if they did not have vulnerability scanning and assessment software. However, the expert is still needed. They are able to evaluate the impact of the vulnerability on the assets, pinpoint critical assets, assess potential consequences, and more. Then, as part of risk management, they can assign priorities to vulnerabilities to help effectively manage resources.
What is vulnerability management?
Vulnerability management, on the other hand, is like being in charge of managing a fleet of cars for a large company. You cannot just leave them in one service station and hope for the best. You must monitor when they are to be repaired and react to delays if necessary, verify the costs against the budget, choose the right service stations for each job, and more. In general, you need full visibility from the moment that the check engine icon lights up to the moment when your employee is back in the driver’s seat. And you need that visibility possibly for thousands of cars.
A software vulnerability management process takes similar factors under consideration. For every vulnerability that is first found and then assessed, you need to monitor it until it is completely fixed and proven to be fixed. This may take multiple steps and require different actions for different kinds of software. In the case of third-party software, this might involve communication with the vendor, prompting for an update, installing the update, and then verifying it. In the case of in-house software, this might involve choosing the right developer team, monitoring the QA process, and knowing when the fixed version is available in the staging environment and in production. A large organization might need to do all this for hundreds or thousands of different assets.
It is also worth noting that security vulnerabilities have a tendency to reappear after some time. If they do, it makes sense to be able to link this fact to earlier appearances. This saves a lot of time and resources when trying to fix a vulnerability. If you use a good vulnerability management system, you can use previous knowledge to very quickly get rid of such reoccurring issues.
Website vulnerability assessment and management process
To select the best software to support your security services and your web vulnerability management program, you need to make sure that the selected solution provides the right functionality in all three key areas: web vulnerability scanning, web vulnerability assessment, and web vulnerability management. Luckily, leading-edge market offerings in this class usually provide all of the required functionality.
Web vulnerability scanning
When you select the best web vulnerability scanner, you should consider the following important factors:
- How thorough is the scanner? How effective is it for known vulnerabilities and for new vulnerabilities? For example, a signature-based scanner will not be able to find zero-day vulnerabilities at all.
- How accurate is the scanner? If a scanner reports a lot of false positives, you will waste resources trying to find problems that don’t exist.
- Will the scanner support all your technologies? If a scanner works only with selected technologies (which is often the case with static application security testing), you may need several tools for one job.
Web vulnerability assessment
When you look for vulnerability assessment functions, you should consider the following important factors:
- Can the software automate part of the assessment process? For example, can it evaluate the potential impact of a security issue and propose priorities right after the scan is complete?
- How flexible is the software when it comes to assigning priorities and grouping? With a large number of assets, grouping capabilities are of key importance.
- How extensive are the reporting capabilities of the software? Will it be able to provide reports that are useful for security risk management, assessing the security posture, developing new security policies, security programs, security controls, and more?
Web vulnerability management
The key factors to consider when choosing vulnerability management tools include:
- Does the tool support the full lifecycle of a vulnerability: from its discovery till the confirmation that it is completely fixed?
- Does the tool integrate with systems that can help with vulnerability management and web asset management, for example, issue trackers or continuous integration software?
- Can the tool discover reappearing vulnerabilities to help mitigate them on the basis of already known vulnerability data?
The human factor
No matter how good the vulnerability management tool is in terms of its functionality, it still remains a tool for the security team. Penetration testers and managers must be comfortable with it and must like to use it. The tool must be both powerful and easy to use. It must also form a part of a comprehensive vulnerability management policy.
Meeting all these requirements together is not an easy task. One of the leading tools on the market that does it is Netsparker. Of course, the ease of use category is very subjective but since this product provides a fully functional demo, you can check how much you like it.



