If you would like to read the other parts in this article series please go to:
- Reverse Engineering Malware (Part 1)
- Reverse Engineering Malware (Part 2)
- Reverse Engineering Malware (Part 4)
- Reverse Engineering Malware (Part 5)
Over the course of parts one and two in this series on reverse engineering, we laid out the groundwork for our upcoming analysis. In this third part we will now get to the sexy stuff, actual malware analysis.
Reverse engineering and you, Part III
Well in part two we ended with my asking you if your piece of downloaded malware was represented with a winzip or winrar icon. Why would I ask this question? Do any of you remember reading the article series I wrote a while back called “The student, the Teacher, and Optix Pro“. That article series dealt with someone who used a trojan to compromise his teacher’s computer. Part of the process in building the trojan server dealt with whether or not you wanted to disguise the trojan with an icon such as a winzip one. Rather clever isn’t it? While this may not fool everyone, it certainly does fool a lot of computer users who are not as security savvy as us. That is also fine, as not everyone can be a security expert. I mention this simply for the reason that we cannot look down our collective noses at those who are not computer literate. We all have different skill sets, and must remember that. No one likes an elitist!
Is it fake or real?
Well much as I alluded to above, I am not in the least bit convinced that my piece of malware is actually a winzipped file. Were I to simply double-click on it to uncompress it then I may very well be installing malware on my system. That or it could genuinely be a compressed piece of malware. Can any of you think of a way to unequivocally prove one way or the other whether or not this is a genuine winzipped file? Well I can. What we need to do is open up the piece of malware seen below, that I downloaded earlier, with a Hex editor.
Figure 1
So as you can see the malware is indeed represented by a winzip icon. It does not show up as the classical winzip icon as I have winrar installed on my VMware image. Before we open up the file in a hex editor it is important to note something. File formats such as a winzip, winrar, or even a PE format one, all have a specific byte signature that can be recognized at the byte level. This is easily viewable via a hex editor which is why we need to open the piece of malware in one. This will allow us to look for specific byte sequences in the file itself. That in turn will tell us if the piece of malware seen in the screenshot above is a genuine winzipped file or not. You need not worry either about executing the malware when opening it up in a hex editor as you are simply viewing its contents, you are not invoking it.
Of bits and bytes
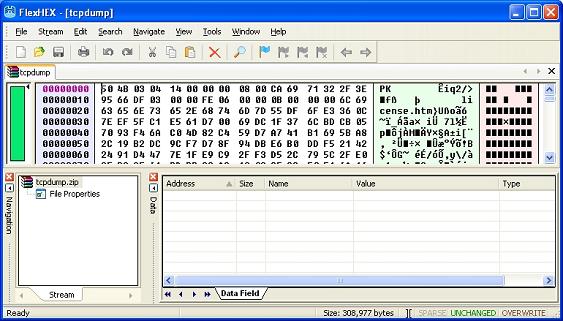
We can see in the screenshot below that I have opened up the malware file in my hex editor of choice. Of note in the screenshot are the characters “MZ”, or as represented in hex by the characters “4D 5A”. The characters “MZ” represent the opening sequence of bytes found in a PE header format. In other words the “MZ” tells us that this file is an executable one, and not a compressed winzipped file format. Shocking! Just shocking! Do these malware authors have no honor? Heheh. Well as we all know they most certainly don’t. Trying to make an executable look like a winzipped file is mildly clever, as double-clicking on it to decompress it would actually invoke the malware.
Figure 2
Well this begs the question of just what a winzipped file format looks like at the byte level. A good question indeed and one we should look at, for if nothing else then to positively prove the difference between them. Just like the PE format has an opening byte sequence of “MZ” the winzip file format will have an opening byte signature of “PK”. On that note let’s take a look at a legitimate winzipped file format.
Figure 3
Just to make believers out of you, we can see in the screenshot above that there is indeed the “PK”, or as represented by the two bytes “50 4B”. Now we have established our baseline and proven that the malware file is of course an executable one, and most certainly not a winzip compressed one. I should mention here that when looking at hex it is important to note that one ASCII character will be represented by two alpha-numeric ones as viewed in a hex editor. To clarify further, the byte “50” represents the ASCII character “P”, and the byte “4B” represents the ASCII character “K”. This is a very important detail, and really is also carried over to the world of packet analysis as well. Though in packet analysis we often have metrics represented by one bit, and not a whole byte. That bit of nitpicking I shall reserve for future articles on packet analysis.
File formats and their importance
You were likely hoping that we would now get into reverse engineering hot and heavy. Well we will soon enough, but all in good time as it were. It is also important to go over information that is very much germane to our analysis. Information such as the above noted file formats for winzip and that of the PE header. When doing reverse engineering it is at times required that you verify what file format a specific file is in. To do that, as we have done here, you need to understand how to do it. That would include opening the file in a hex editor as we have done, and furthermore, having a copy of the file format specification in hand.
The Portable Executable (PE) format is one that is native to Microsoft Windows. This format specification is, I can honestly say, quite fascinating to read. To help grow and hone your knowledge of computer security you often must increase the complexity of the subject matter you study. I would greatly encourage you to take the time to properly look at and assimilate just what the PE format is, what it means, and what can be pulled out of it. Studying this file format will also help you cement just how a program residing in physical memory ie: your hard drive, actually gets mapped into memory ie: RAM. Hmmmmm, this might make for a rather interesting article actually.
Wrapup
In this article we took a look at the piece of malware that I downloaded. It was represented by the winzip icon, but I had my doubts as to it actually being in that file format. Being suspicious by nature I then cracked it open with a hex editor and confirmed that it was indeed not winzip compressed, but rather in an executable format aka PE format. Further to that we also covered key information on what various file formats have in terms of unique byte sequences. This feature helped us definitively identify what type of file we actually had. In the next parts we shall cover what type of malware packing was used, and also how to unpack it. Once that is done, our analysis will begin in earnest. Though as you will see, the analysis part of it is relatively quick seeing as we are only doing basic reverse engineering. See you in a bit.
If you would like to read the other parts in this article series please go to: