Introduction
There is an ongoing need and desire to utilize the security logs that are generated on Windows servers and desktops. The security logs can be used to help troubleshoot, track data access, log user access, and even for forensics. The long time issue with the Windows security logs (and all logs for that matter) is that the logs are stored on the computer where the action occurs. This causes a significant issue for even the smallest companies, as logs on hundreds of computers can be hard to access, manage, and organize. However, there are some tools, techniques, and options that allow every administrator, security professional, and auditor to gather information from one or many Windows computers remotely and efficiently.
Event Viewer
The new Event Viewer that was first delivered with Windows Vista and Server 2008 has some new features that you might want to consider when looking to remotely access security logs. The new features can help you find key security events and even filter through thousands of events in an efficient manner. The structure and help that come with the new Event Viewer are very useful, but other features such as filtering, custom views, and associating a task to an event provide even more control over sifting through events.
Filters
Each log within Event Viewer has an option to be filtered. The filter will allow you to narrow down what is being shown in the log, so you can clearly see only the events that you need to see. Some logs can become very large and cumbersome, not to mention the inclusion of events that are important for someone, but not for you and the task you are trying to complete.
To configure a filter, simply click on the log that you want to filter, and then select the Filter Current Log option on the right pane. The Filter Current Log dialog box will appear, as shown in Figure 1, and you then configure what you want to see. There is not much else to it, as the filtering options are clear and easy.
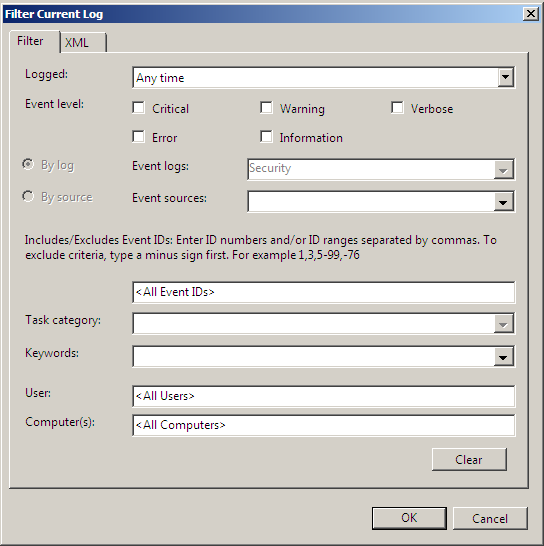
Figure 1: Filtering options within Event Viewer for each log.
Custom Views
The addition of custom views within Event Viewer really makes the manipulation and “mining” of specific events easy. It also allows for easier viewing of events to look for trends and potential combination of events to track down intruders or to troubleshoot issues.
The key with custom views, in my opinion, is that you can leverage ANY log, even logs from other computers. As long as the log is on the computer that you are creating the custom view on, you can add any event to the custom view. For example, consider the situation where you are having an issue with replication between your domain controllers. It seems as if some domain controllers have all of the correct information, others have some of the information, and others don’t have any updates. In this scenario, you can create a custom view from different logs on a single computer. You can take the entire Active Directory log, or just specific event IDs from the Active Directory (or any other log).
Note:
We will discuss later in this article how to get these additional logs onto a single computer for use in a custom view.
For more information on how to setup custom views go here.
Tasks
Within the new Event Viewer you can associate a scheduled task to an event or an event ID. The options are fantastic for anyone that needs to be notified when certain activities occur on one or more systems. The tasks can be created directly in the Event Viewer by using the “Attach a task to this log” option on the right pane or by clicking an event and then selecting the “Attach task to this event” option on the right pane. Either will start a Wizard which will walk you through the options for the task. You can also launch the Task Scheduler, which has a new option for setting up tasks associated with events.
For more information on setting up tasks within Event Viewer for events and logs, go here.
EventComb
EventComb is a tool created and released by Microsoft. The tool has been available for some time, the issue is that it was not highly publicized and certainly not easy to obtain. However, the power of EventComb is rather impressive, depending on what you need to gather for events. You can see all of the options available within the EventComb interface from Figure 2.
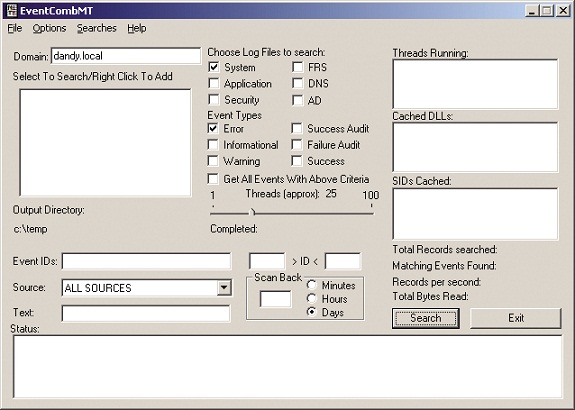
Figure 2: EventComb allows for granular control over gathering events from remote computers.
To obtain EventComb, you can download it from here.
A few tips when running EventComb is that it will generate a local file per computer that you scan. It will not create a single file, but you can take the files generated and import them into Excel and perform searches on all files and events with one search. Being able to control and find events in this manner makes finding issues and problems much easier.
Subscriptions and Event Forwarding
One of the most powerful solutions to gathering events remotely is a newer technology that is built directly into Event Viewer. The technology requires that you have the correct operating systems in the mix, but I am sure that most of you reading this have what you need already. At a minimum, Table 1 illustrates what you need to configure subscriptions and forwarding.
|
Configure Subscription and Collect Events in Central Log |
Can Forward Events to Central Log |
|
|
Windows 2000 |
No |
No |
|
Windows XP |
No |
Yes |
|
Windows Server 2003 |
No |
Yes |
|
Windows Vista |
Yes |
Yes |
|
Windows Server 2008 |
Yes |
Yes |
|
Windows 7 |
Yes |
Yes |
|
Windows Server 2008 R2 |
Yes |
Yes |
Table 1: Subscriptions and Event Forwarding Requirements.
In order to get subscriptions and event forwarding configured to collect what you want, you will need to configure each computer in the process to understand that it will be collecting events and/or forwarding events. This is easily done with a few commands on each computer, which is detailed in this article:
The subscriptions are configured on the computer that will be collecting the events. Each subscription defines which computer(s) will be notified to forward events and which event(s) will be forwarded.
Once events are collected in a central log, the event can then be parsed using filtering, searching, or custom views.
Summary
Being able to capture and view events remotely from some or all of your computers on the network is essential for security and troubleshooting. With so many solutions at your disposal, you will need to test and verify which solution works best for you. The Event Viewer itself has some solutions which can be helpful, especially if you leverage the event log forwarding and subscription solution that is now available and free from Microsoft. With Event Viewer now supporting advanced search, filter, and view options, you can parse through logs and events quickly. EventComb is another solution that makes remote event log entry parsing much easier.




