Editor’s note: In response to the coronavirus crisis gripping the world, TechGenix is republishing a selection of recent articles, tutorials, and product reviews that contain relevant information for IT pros as their jobs change dramatically. In this excellent tutorial, originally published June 27, 2018, we walk you through the steps on leveraging Azure MFA to ensure that remote users connecting to the network via VPN are who they say they are.
In a time when more and more focus is being placed on network security, more and more businesses are looking toward multifactor authentication to ensure that the people logging into their networks are who they say they are. With the growing number of remote users accessing networks remotely via VPNs, it makes sense that more and more businesses are turning to multifactor authentication solutions, such as Azure MFA, to protect their networks over those VPN connections.
While there are many multifactor authentication options available, one of the simpler solutions to deploy is based on Azure Active Directory. In this article, I’ll talk a little bit about an Azure-backed MFA solution for VPN access, how it works, and how to add it to an existing VPN solution.
The typical VPN solution
In most environments, the typical VPN solution features a firewall/VPN device such as a Cisco ASA or maybe something like a FortiGate device, along with a domain-joined Network Policy Server. The VPN device is configured as a client in the Network Policy Server and access to VPN is controlled via group membership in AD.
In the above scenario, things typically look like this:
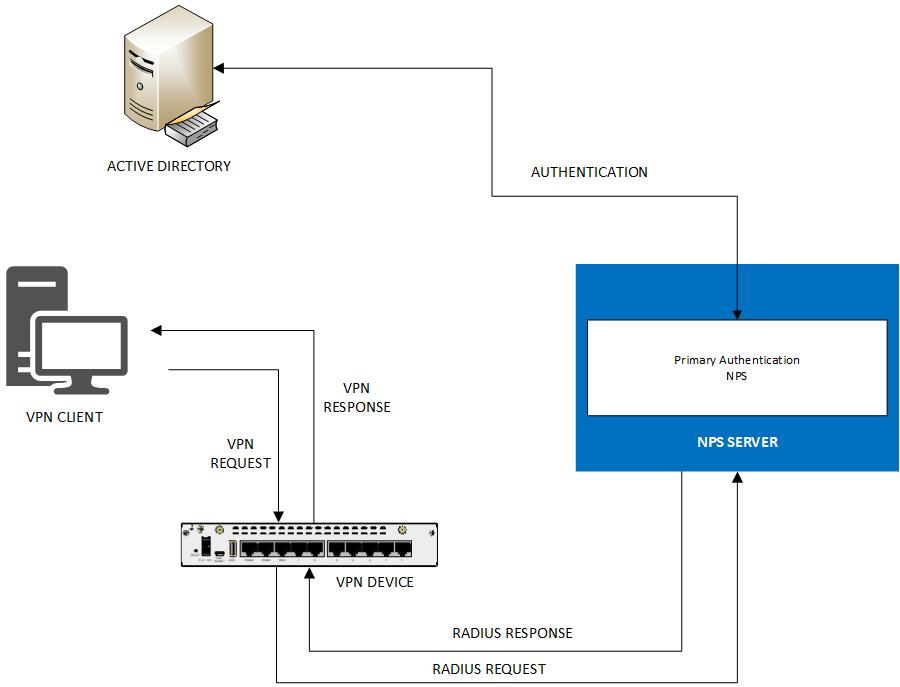
While the typical VPN solution described above works, the inherent flaw is that if someone loses a laptop or gives up a password to a phishing attack, it’s quite easy for an intruder to get access to the network via VPN.
Enter multifactor authentication
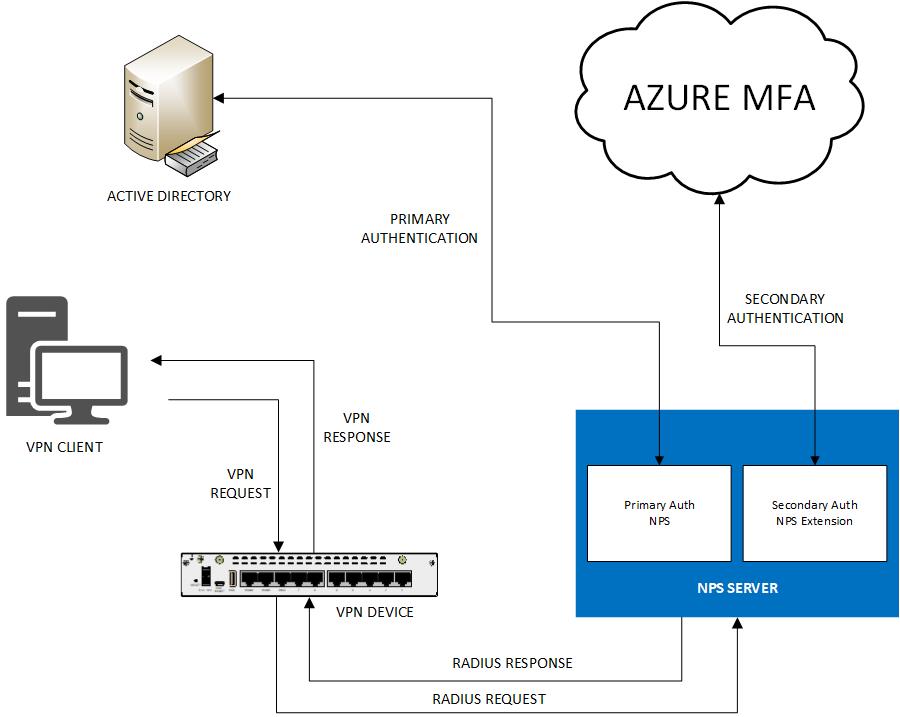
Deploying a VPN solution that leverages Azure MFA provides an added layer of security and helps ensure that remote users connecting to the network via VPN are who they say they are. By leveraging Azure Active Directory and the NPS Extension (both available from Microsoft), an organization can very easily deploy or upgrade an existing VPN solution to one that offers MFA protection.
The Azure MFA VPN solution
An Azure-backed MFA VPN solution requires a few additional components in addition to the typical VPN device and NPS server. Those additional components include:
- Azure Tenant
- Premium Azure AD Subscription
- NPS Extension
- Azure AD Connect
In an Azure MFA VPN solution, the secondary MFA authentication for VPN users is performed against Azure AD accounts that have been synced to Azure AD in the Azure Tenant via Azure AD Connect. The premium Azure AD Subscription is necessary as it provides the required licensing to enable MFA in Azure AD. The NPS Extension is a piece of software that is installed on the on-premises NPS server. This software securely communicates with Azure AD and facilitates the secondary authentication when someone attempts to connect to the VPN.
A typical Azure MFA VPN solution looks something like this:
Preparing for an Azure MFA VPN
Before deploying a multifactor VPN solution based on Azure AD MFA, you must first provision an Azure tenant and an Azure AD subscription within the tenant. The Azure AD subscription must be at least Premium P1. The free version of Azure Active Directory that comes with a deployment of Office 365 / Exchange Online does not support multifactor authentication for VPN.
Provisioning an Azure tenant is as easy as clicking this link. Once the Azure tenant is provisioned, you can sign up for an Azure AD Premium P1 subscription right from your Azure portal.
With an Azure tenant and Azure AD subscription in place, you should deploy Azure AD Connect in your on-prem Active Directory environment so that the on-prem Active Directory user accounts can be synced to Azure Active Directory. This is necessary because the MFA preferences will be set on the Azure AD accounts that are synced from on-prem. Additionally, the NPS Extension that you will eventually install on the existing NPS server will communicate directly with the Azure AD subscription to validate MFA status and credentials.
Once the Azure tenant is in place and the on-prem users are being synced to Azure Active Directory, you can enable MFA for your users that will be using the VPN by following the steps below:
- Browse to the Azure Portal and login
- Click on “Azure Active Directory” in the left pane
- Click “Users”
- Click “Multi-Factor Authentication”
From there, select the users for whom you wish to enable MFA and click “Enable.” This will enable MFA for the selected users.
MFA enrollment for users
After enabling MFA for your Azure AD users, and before they begin using the VPN, the users who will be using the MFA VPN must enroll in Azure MFA and set up their MFA preferences by following the instructions below:
- Sign in here
- Follow the prompts to set up a verification method
With the Azure AD users configured for MFA and enrolled, the existing VPN solution can be upgraded to leverage the Azure-backed MFA features that are now available.
How to deploy an Azure MFA VPN solution
This article assumes that you have a working VPN solution already in place and are leveraging an NPS server. With an NPS server already in place, you just need to make a few changes to make it work with Azure-backed MFA. The first change is the installation of the NPS Extension on the NPS server. The second change is the creation and installation of a certificate on the NPS server so that it can securely communicate with the Azure AD subscription/directory.
Installing the NPS Extension
The NPS extension allows the NPS server to perform secondary MFA authentication against Azure AD. The extension can be downloaded here. Installation of the NPS extension is painless and consists of just a handful of “Next” prompts, followed by a “Done” prompt.

There are no configuration options to choose when installing the extension as all it is doing is essentially adding some DLL libraries to the NPS server.
Securing communication between NPS and Azure AD
Once the NPS extension is installed on the NPS server, a certificate must be generated to allow secure communication between the NPS server and the Azure Active Directory. This certificate is created and installed by running the “AzureMfsNpsExtnConfigSetup.ps1” PowerShell command, found in the “c:\Program Files\Microsoft\AzureMfa\Config” directory on the NPS server where the NPS Extension is installed.
To create the certificate, the PowerShell command requires the directory GUID of the Azure AD.
Procuring the Azure AD GUID is easy enough. Simply follow the steps below:
- Browse to the Azure Portal and log in
- Click on “Azure Active Directory” in the Left Pane
- Click “Properties”
Copy the value from the Directory ID field that you see and save it off to a text file somewhere.

After obtaining the Azure AD GUID, create the certificate and establish connectivity to the Azure AD by following the instructions below:
- Run Windows PowerShell as an administrator
- Change to the “C:\Program Files\Microsoft\AzureMfa\Config” directory
- Run the AzureMfaNpsExtnConfigSetup.ps1 script (be sure to preface command with .\)
- Sign in to Azure AD as an administrator when prompted
- Provide your Azure AD Directory ID that you saved earlier
The process above creates a self-signed certificate on the NPS server and secures communications between the NPS server and the Azure AD. It associates the public key of the certificate to the service principal on Azure AD and stores the certificate in the local machine store on the NPS server. The network user is granted access to the certificate’s private key.
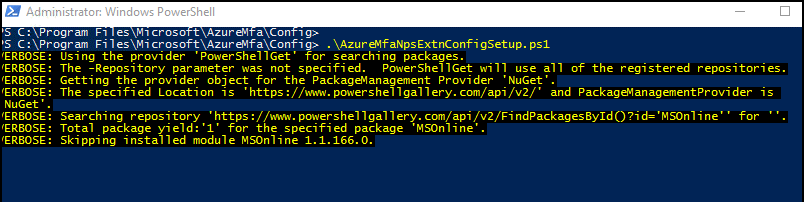
After all of this is completed, the NPS service is automatically restarted.
A word about authentication
Although your existing VPN/NPS solution may already be configured, you need to determine which encryption protocols you need to use to support Azure-backed MFA — because not all encryption protocols support all MFA verification methods.
For example, PAP supports phone calls, one-way text messages, mobile app notification, and mobile app verification code, whereas CHAPV2 and EAP support phone calls and mobile app notification only.
Two key factors affect which authentication methods are available with an NPS extension deployment:
- password encryption algorithm used between the VPN and the NPS server
- input methods that the VPN client application supports
For example, if your VPN client software doesn’t offer a field that allows the user to type in a verification code from a text or mobile app, you aren’t going to be able to use one-way text messaging as a secondary verification method. As such, you could use PAP, CHAPV2, and EAP encryption protocols. Alternatively, if your VPN client does make a field available to enter a code from a text or mobile app into (and that is the secondary authentication method that you want to use), you would need to use PAP, since CHAPV2 and EAP only support phone call and mobile app notifications.
With that said, before you deploy the NPS extension, consider your existing environment and how these factors impact your configuration.
Deploying the solution
By default, once the NPS Extension is deployed, users who have not been enabled for MFA in Azure AD will be denied access to the VPN. As such, you may find it useful to allow non-MFA-enabled users to still connect to the VPN until you are ready to go to production.

To allow non-MFA-enabled users to access VPN, open the Registry Editor on the NPS server and set the “REQUIRE_USER_MATCH” value in the “HKLM\SOFTWARE\Microsoft\AzureMfa” registry key to “FALSE” while you are testing. If it doesn’t already exist, create it. Otherwise, users who are not enabled for MFA will be blocked from connecting to VPN. You can set the value to “TRUE” when you are ready to move the solution into production.
Test your new Azure-backed MFA VPN by attempting to login to the VPN with a user account that has been synced to Azure Active Directory and who has had MFA enabled. Ensure that your test user receives the expected secondary authentication prompt (phone call, text message, app notification, etc.). If your test user does not successfully authenticate, confirm that the authentication settings that you have configured in the NPS server policies support your preferred MFA verification method.
After confirming that your test user can log in to the VPN, you can set the “REQUIRE_USER_MATCH” value to “TRUE” to enforce MFA authentication for the VPN.
Pulling it all together
You can add Azure MFA authentication to your existing VPN solution to further secure your network by leveraging the multifactor authentication functionality available in Azure Active Directory. Doing so requires you to provision an Azure tenant and an Azure Active Directory P1+ subscription. With those provisioned, sync your on-prem users to Azure AD with Azure AD Connect. Once your on-prem users are synced to Azure AD, you can enable MFA for them in Azure Active Directory.
After your users are synced to Azure AD and have been enrolled in MFA, install the NPS Extension on your NPS server and create and install the self-signed cert using the PowerShell script that the NPS Extension creates. With the certificate installed, establish secure connectivity between the NPS server and Azure AD so that the NPS Extension can leverage the MFA offered by Azure AD.
The overall effort to complete this process is less than one hour. Isn’t the security of your network worth an hour of your time?




Hi – Windows 10 VPN does not allow you to enter in a code from TEXT or App Codes. and the VPN connection fails.
Do you know how to get this working?
Thanks
Jess
same thing here, anyone that have a good solution for this?
Nice Article.
How can you make Azure to display a pop up message for users during the mobile app and phone call verification?
Hi Great article. I got this mostly working in that I got hte popup approval, but its too quick before the VPN client fails the login. I am using Fortinet appliances so perhaps its an issue there somewhere in the config. The popup on the app is more a setting to be configured when the user enrolls into Azure MFA
Can you install the NPS addin on the VPN server, where NPS is already installed by default?
If MFA is enable via conditional access how can we exclude/bypass a group from MFA.
I have same question as Bilal. Looking to deploy and trying to review Helpdesk support scenerios