While corporate logos definitely have their place, we can all probably think of a few companies that take their branding to the extreme by plastering their logo onto anything and everything they possibly can. In all honesty, I always thought of the Microsoft 365 branding feature as being little more than a concession to corporate customers who felt the need to paste their logo onto the Microsoft 365 sign-in screen. More recently, however, I have realized that this type of branding actually has some practical uses.
Branding Microsoft 365: Two good reasons
I can think of two main reasons (beyond corporate vanity) why an organization might want to brand the Microsoft 365 sign-on screen.
The first reason is that branding Microsoft 365 can actually help to improve your security. Seriously. Think of all of the phishing emails that your users receive every single day. Granted, most organizations go to great lengths to thwart such attacks, but some phishing messages will inevitably slip through the cracks. Additionally, some of these attacks are far more convincing than they once were. As such, there is a relatively high probability that a user will eventually click on a link within a phishing message.
Many phishing messages are designed to target Microsoft 365 users. Often, clicking on a link within such a message will take users to a fake sign-in screen designed to steal the user’s credentials. If the user knows that the authentic sign-in screen contains the company logo, then the odds of a non-targeted phishing attack succeeding in getting a user to enter their credentials go way down.
The other reason why branding a Microsoft 365 account might be helpful is that it can remind users which account they are signing into. Many users have both personal and corporate Microsoft 365 accounts. Branding an account might help to prevent user confusion. If you can stop users from entering the wrong set of credentials, you may be able to help prevent account lockouts.
How to brand Microsoft 365
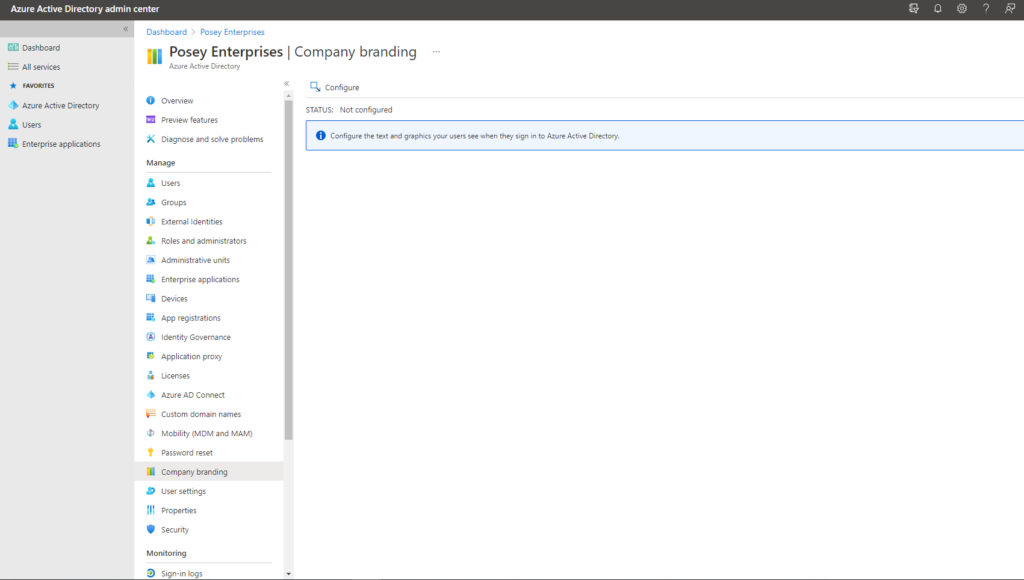
To add your branding to Microsoft 365, begin by signing using an account with global administrator permissions. Once you have logged in, open the Azure Active Directory Admin Center. Next, select the Azure Active Directory tab and then click on Company Branding, as shown in the figure below.
Click on the Configure link shown in the figure. This will cause the Azure Active Directory Admin Center to open the Configure Company Branding page, as shown below.
Upload your banner image
The first option on this page allows you to upload a background image. This background image will be used on the Microsoft 365 sign-in page. You can use any image that you want as a background as long as it is less than 3,000KB in size and has a resolution of 1920 x 1080. The image will also need to be in PNG, JPG, or JPEG format.
The second option found on this page allows you to upload your logo. The logo that you provide will be displayed on the Azure AD sign-in screen. It also gets displayed within the Access Panel service. Like the background image, the banner logo must be a specific size. Specifically, the banner logo must have a resolution of 280 x 60 and the file size must be 10KB or less. The PNG, JPG, and JPEG file formats are supported.
Just beneath the Banner Logo option, you will find an option to provide a username hint. This is where you can remind users of the structure of their username. For example, you could say something like, “your username is your first name followed by @contoso.onmicrosoft.com.” However, I don’t recommend providing a username hint unless you require multifactor authentication. That’s because it becomes easier for bad actors to gain access to your environment if they know how your usernames are structured.
The next option to appear on this page is the sign-on text. Sign-in text can be used for a variety of purposes, such as providing technical support contact information or perhaps a “terms of use” disclaimer. When deciding how to use this text, there are two things to keep in mind. First, the text you enter can be seen by the public, so you will want to avoid including any sensitive information. Second, you are limited to using a total of 1,024 characters, so you won’t be able to include overly lengthy text.
The next option allows you to enter a background color for the sign-in page. The background color is only used if the background image fails to load. If you enter a background color, it will need to be entered as an RGB color code in hexadecimal format.
Just beneath the background color option, you will find options for uploading a square logo image and a square logo image for use with the dark theme. As strange as it might sound, these images will represent user accounts. If you decide to upload square logo images, they will need to be at a resolution of 240 x 240 and less than 50KB in size. Microsoft recommends that you use a PNG image, but JPG and JPEG are also supported.
Finally, this screen lets you control whether or not the option to remain signed in should be displayed. I recommend setting this option to Yes because it will make your users’ lives easier.
Branding your Microsoft 365: Is it for you?
Branding Microsoft 365 isn’t for everyone. However, by going ahead and branding Microsoft 365, you can give it that personal touch while also helping keep your users a little bit safer.
Featured image: Shutterstock




