2021 has been quite a rollercoaster ride for many of us in the IT profession. The SolarWinds hack discovered in late 2020 turned out to be a really big deal. In 2021, organized cybercriminals used many different attack vectors to also highlight common defects across all commercial sectors. 2021 was a call to action for every business to prepare for the worst. 2022 is also offering us now the possibility of a commercially available Intel quantum processor attacking us soon! All networks, large and small, are at risk with so many different exploits possible as hackers, threats, and exploits continue to grow.
In this article, we’re going to briefly review how bad the cybersecurity situation got for us last year. You’ll then get some advice on how we should prepare for 2022. We’ll look at key aspects of cybersecurity with a particular interest in keeping your data safe and how we can use technology, innovation, and policy to keep your business going in uncertain times.
Let’s first delve straight into some of the main cybersecurity breaches that occurred last year and their impact within the IT community!
Top 5 Cybersecurity Breaches in 2021
How bad did things get for us last year? Pretty bad indeed, if you look at the calendar.
January: Microsoft Exchange Hack
A Chinese hacking group called Hafnium exploited four zero-day vulnerabilities in Microsoft Exchange. Businesses complained about not being able to access their mail which had mail admins scrambling. Microsoft quickly published some workarounds followed by patches to address the problem.
April: Apple Supplier Ransomware Attack
A Russian ransomware gang called REvil breached the defenses of a company belonging to Apple’s supply chain. The attackers demanded $50 million in extortion money or they would leak confidential Apple data they said they had stolen. REvil has been responsible for some high-profile ransomware attacks. The Russian Federal Security Bureau (FSB) says they’ve now dismantled REvil, but this still needs independent confirmation.
June: Gas Pipeline Cyber Attack
A criminal gang calling themselves DarkSide caused a fuel supply crisis on the East Coast of the US when they hacked the control network of Colonial Pipeline. It took more than a week for the company to resume normal operations after the attack. It’s believed that the DarkSide gang resides in Eastern Europe and seems to be a private criminal organization; not a state-sponsored group. More and more of these cyber-gangs are coming into existence and exploiting connected enterprise solutions through the weakness of Operations Technology (OT).
Here you’ll get a nugget of useful technical banter for your lunchtime chit-chats. OT systems were originally designed to be ‘air-gapped’ with no consideration of how its coding worked in relation to security. Real-time AI-driven OT risk mitigation software now exists that can analyze OT operations. Yet, it only alerts users of weaknesses in changes to manufacturing or enterprise operations – no OT firewall currently exists!

July: Kaseya Ransomware Attack
Software developed by Kaseya Limited that’s used by managed service providers (MSP) was discovered to have been compromised. This enabled the attacker to deliver malicious payloads to businesses serviced by MSPs that employ Kaseya’s software. Cooperation between the US Department of Justice and authorities in Poland and Ukraine led to several arrests later in the year.
December: Critical Vulnerability Discovered in Log4j
If all this and more wasn’t enough, a discovery of a zero-day vulnerability in the Log4j library for Apache also occurred. That’s serious because myriads of web applications and software packages utilize this library and event monitoring logs. This is why, unless they’re patched, the potential that this vulnerability could bring down (est. 67%) the internet will be there!
The above attacks are a reminder of how bad last year was for cybersecurity. Unfortunately, evolving trends in cyber attacks point towards even worse attacks on the horizon with events predicted to increase in a nearly exponential manner!
Ransomware Threats are Evolving
“Cybercriminals and ransomware are evolving,” says Mihir Shah, the CEO of StorCentric. He also stated attackers are now targeting managed service providers (MSPs) directly. This lets them target multiple organizations in one fell swoop. So, what’s behind this shift?
Influencing Factors
Part of the problem is simple economies of scale and better accessibility to technology. Cybercriminal gangs become larger and more sophisticated due to their increasing number and their ability to network! As such, it makes more sense to launch attacks that target bigger companies and groups of companies for better rewards.
Some of you may be throwing your coffee at the screen at the mention of cryptocurrencies and blockchains helping cybercriminals to get paid and stash their ill-gotten gains! To reduce the tsunami of a coffee split, this nefarious usage was a fraction of a percent of all crypto-assets even during the Silk Road days!
The COVID-19 pandemic has also played its part, cultivating an explosion of remote workers, jobless, and too much time on an individual’s hands! Physical isolation has acted as a Petri dish to cultivate new vulnerabilities, cybercriminals, and criminal organizations.
Selling Extortion
Remember the script-kiddies of the past? Today, a growing trend of criminal organizations offer Ransomware as a Service (RaaS). In other words, selling pre-packaged ransomware tools to individual malicious actors and cybergangs. “RaaS is a huge business,” says JG Heithcock, the General Manager of Retrospect, and mentioned such attacks continue to grow at an alarming pace.
Targeting Backups
What cybercriminals are targeting recently has also been evolving based on exploits. Cybercriminals are now attacking backups first. Once backups are compromised, they go after production data. This means that many enterprises are feeling a false sense of security. A false sense of security can be worse than having no security or inadequate security. So, what can be done to combat these cyberthreats?
Cyber Insurance is Essential
Patching each vulnerability can be difficult to impossible for automated or integrated business solutions. This is especially true for enterprises that leverage IT, OT, and IoT integration. Mixed technology made by the lowest bidder with code that isn’t security orientated is often spliced together to provide a business solution. At no point is hacking, phishing, or malware effectively considered; even for the largest enterprises!
Cyber insurance is a way of mitigating the outcome of such attacks. SMEs are starting to onboard once they understand that within the next 10 years, cybercriminals will target each and every commercial company! Cyber insurance is essential because we just don’t know what new kinds of attacks may be coming in the future, their frequency or the extent of losses incurred.
Cyber insurance is important in this evolving threat landscape, but it’s not a complete solution. For one thing, you may often be confused and frustrated over what such insurance covers and doesn’t cover. You might also worry about liability scaling out of hand with clients and supply chains potentially being disrupted by a failure your company caused. Like a car pileup at an intersection, this can mean mass litigations to cover losses between multiple parties!
If you insure your business against cyber attacks and take every possible precaution to prevent and recover from an attack, it’s still not enough. You also need to make sure you can fully recover from such an attack. That may mean rethinking your current backup and recovery strategies to better safeguard your corporate data. It also includes how to cover the loss of trust and business from dissatisfied clients that may have lost business themselves or had their data leaked.
Data Protection is Paramount
Data is the lifeblood of a business. This is why it’s paramount to protect it. Cybercriminals know about its value, so they target it with ransomware and other attacks. That makes implementing effective data protection a key strategy to maintain the success of your business.
Tried and Tested Protection
A good data protection strategy doesn’t mean you have to start all over from scratch again. Organizations can best implement data protection through a combination of both established methodologies and innovative technologies.
The 3-2-1 Backup Rule
One tried-and-true methodology that plays well even in today’s hostile online environment is the familiar 3-2-1 Backup Rule. This is where you keep three copies of data saved on at least two media types, with an additional copy stored offsite. Many cyberthreats utilize injection attacks that require the system to be powered on to work. This simple backup process could save the day!

That said, while the 3-2-1 Rule remains a golden rule for data protection, organizations should look for more in 2022.
Beyond the 3-2-1 Strategy
The 3-2-1 backup rule continues to be the golden rule of complete data protection, but it has some challenges in the modern age. One challenge is financial losses due to downtime. Gone are the days of a few gigabytes of data stored on a few CDs, now you need to consider if backups are run out of hours. Even SMEs are having to deal with larger file and storage sizes thanks to the adoption of smarter technology that leverages the latest and greatest hardware performances available to it.
When your system goes down or encounters malware, the last thing an Administrator should do is run around. You shouldn’t be looking around for out-of-date data that could have become corrupt over time. Parity and logic checking along with transfer times could mean a business isn’t only down for days or even weeks, but also has lost all the progress made between the backup timestamp and the system down event. This could, and in some cases has bankrupted previously viable going concerns.
Profits also remain the name of the game, so organizations will seek a proven solution that makes this easy and affordable to implement. The ideal backup solution may enable a backup script to a local destination and a backup transfer script to an offsite target. Using a transfer script to copy backups to a second location enables the administrator to perform the operation offline; without the need to use the original source.
On the matter of cloud technologies, the options for implementing 3-2-1 workflows have expanded considerably. Below are a few different options you may consider.
Option 1: The Disk and Cloud Combo
The first possibility is disk and cloud solutions. Many businesses use this common backup strategy of combining local disks and cloud storage locations. An onsite backup on a local disk allows the fastest data recovery time possible due to better bandwidth. A remote backup on a cloud storage location insulates the organization’s data from malware and other data losses.
Option 2: The NAS and Cloud Combo
Using a network-attached storage (NAS) and cloud combination is another option. NAS devices are an affordable on-site storage solution. Using a NAS ensures a large dedicated storage pool and high bandwidth is possible. Transferring those backups to the cloud as an offline process is useful. It allows administrators to avoid ‘double-dipping’ the original source multiple times and slowing down the production system.
Option 3: The Disk and Tape Combo
Disk remains the most common and cost-effective backup storage media. The administrator can quickly back up their environment with a local disk. Backups are also onsite and available for fast restorations. You can also use a security deposit box or a third-party storage locker to keep the data safe. At present, a big debate on the security of cloud or offsite data storage exists. Countless recent data leaks have propagated an opinion that while outsourcing is great, it may not be so good for business data.
Extreme Circumstances Need Extreme Measures
Going beyond the 3-2-1 backup rule will provide organizations with extra reassurance that their data is safe. To protect digital transformation initiatives, organizations can choose to add a second remote storage location, called a 3-2-2 strategy. Alternatively, a NAS, tape, or cloud solution called a 3-3-2 strategy may be used for redundancy.
Innovative Data Management & Recovery Capabilities
Many companies these days are effectively 100% digital, from their deliverables to their intellectual property. As data sizes are continually growing with file formats and data complexity, innovative data management is a necessity.
Data management systems (DMS) are based around a ‘single source of truth’ premise. All software used by a business and respective databases is merged into one single database that serves the organization. Data variables between software solutions vary along with access rights for users or roles. To control data I/O between, a ‘gatekeeper’ manages each software and the database. Each software variable during implementation is associated with a database variable. This ensures the business or user of an eCommerce site never needs to enter duplicate data. Less data duplication means less space used, and faster data recovery. The security of a DMS also helps protect the system from attacks that aren’t designed to bypass a DMS system.

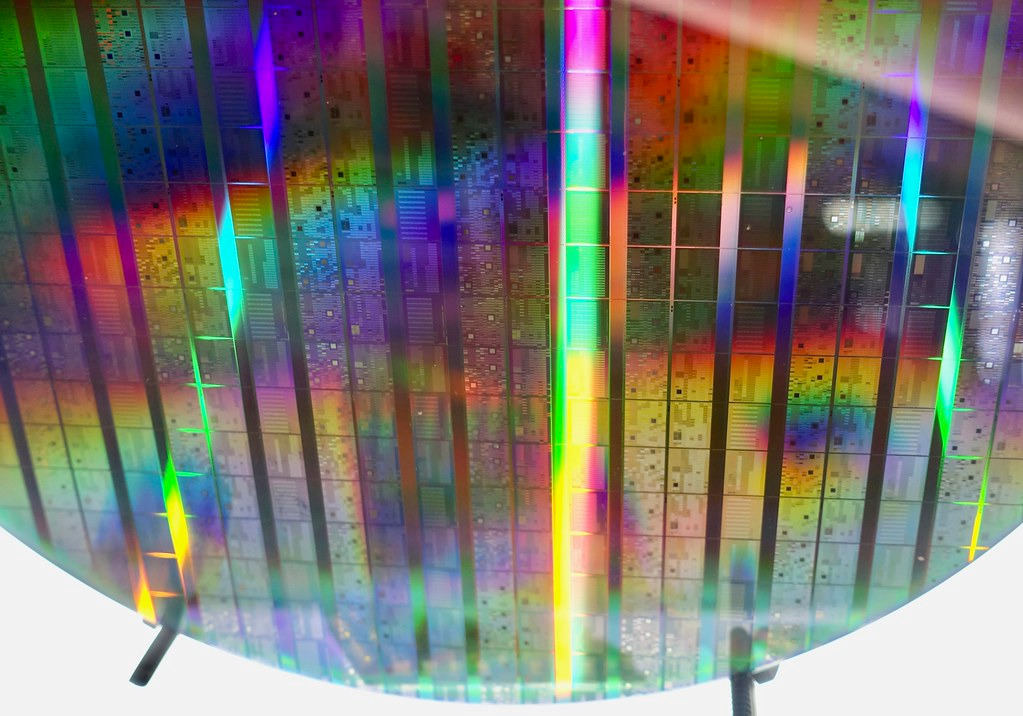
Innovative technology contributes to data management with the advent of the non-volatile memory (NVM) protocol and NVMe SSD storage solutions. The protocol is now the latest de-facto standard that has taken decades to develop and has the likes of Intel and Facebook not developing a better solution! Storage now can be partitioned and managed all from one software. AI is also used to handle this management and recovery processes to help predict and maximize performance and end user productivity. Better yet, thanks to the NVM protocol data going to and from each SSD through its interface, it doesn’t need converting between data formats. This facilitates everything related to data management.
This enables the usage of not only ‘hot-switching’ or ‘fall-over’ recovery methods, but also these can be automated through the AI directly or system managed by an app. This also enables third parties to manage smaller businesses better without the risk of downtime.
Final Thoughts
The digital world is on fire and not in a good way. A new cyberthreat appears in the news nearly every week. 2022 showed no company was infallible with Microsoft Exchange being hacked, Apple’s supply-chain being compromised, and a gas pipeline being exploited. If you think you’re a low-profile target and you don’t care, we also saw a Log4j exploit that could potentially take down around 67% of the entire internet!
Each software your company uses will have at least one vulnerability in some form or another. Plugging the gaps in any enterprise appears to be almost impossible with hacking zero-day exploits posing a major challenge. IT, OT, and IoT integration to make businesses leaner has not helped the matter with the erosion of traditional air-gaps.
The bottom line for a business is the bottom line, so you may wish to investigate Cyber insurance. This will likely form only part of the solution for your business. Implementing a 3-2-1 backup strategy that is then further complemented with the latest NVM protocol-supported storage hardware won’t only help speed up backup and restore processes, but enables AI to help manage the restoration process.
Whatever new cyber threats might be just over the horizon in the coming year, we’d better start getting prepared to deal with them. The time to begin thinking about how to better secure your network, systems, and data is now; not when the system has already been exploited.
You’ve been given some keep principles used for both traditional and modern data management techniques for your consideration. Keeping to traditional techniques is the bread and butter of any administrator, but you need to keep an eye on modern and innovative tools to keep you one step ahead.
FAQs
Are cybersecurity attacks a credible concern to a business?
Some ransomware attacks led to 6 months of disruption for multiple Hospitals in France last year; no sector is safe or sacred. Cyberthreats can bankrupt a company due to loss of earnings. If a business has 10 people costing on average $400 a day each, then it’ll lose $4000 per day plus the overheads of the business. Orders won’t get fulfilled and business loans aren’t paid on time. For larger businesses in the engineering sector, downtime can equate to millions of dollars in losses each hour!
What is cyber insurance?
Cyber Insurance can help reduce the financial impact of a cyber attack by cybercriminals. The challenge is that while it may help ease financial burdens, it fails to help recoup lost clients after data leaks or failed order fulfillment. Digital assets like the businesses accounts may also have been destroyed in the attack. This could make the business inoperable beyond repair. If intellectual property has also been stolen and sold in an attack, the businesses moat may be compromised and lead to bankruptcy.
What is the 3-2-1 backup rule?
The 3-2-1 backup rule helps administrators to remember to have a triplicate data backup, two onsite on different media and one stored offsite. The idea is if the site is destroyed, critical business data like businesses ledger would be available somewhere for recovery.
How can I protect my data in 2022?
Use multiple storage locations and media to protect data. Ensure your backup systems are automated and that you regularly check a system can be restored from it. Many administrators make silly mistakes with some overlooking this over many years – even in large multinationals!
How has innovation helped improve cybersecurity?
You can both streamline your enterprise’s data to reduce its data footprint and expedite recovery through the utilization of a data management system. These can also add an additional security layer to data entering the centralized database. Most exploits don’t cater for this setup at present which could help.
You could also implement NVMe SSD data storage, expediting data transfer speeds while being able to manage all data management tasks from one application. If the system falls over, these systems can switch to another data source automatically through the AI integration. You can also distribute data over many storage locations obfuscating big data that may be associated with a businesses intellectual property.
Did quantum computers expose cybersecurity vulnerabilities?
Quantum computers are starting to become a concern on the horizon making it possible to brute force passwords in seconds and potentially destroy blockchains developed within some businesses. The latest Intel quantum processor may be the beginning of the end.
How did remote working impact cybersecurity?
Thanks to COVID-19, remote working, unemployment, and the need to keep paying bills has acted as a Petri dish cultivating cybercrime. Cybercriminals are now more organized than ever due to social networking platforms, Tor, and assisted in their crimes by businesses trying to integrate IT, OT, and IoT to improve profitability in a globally competitive marketplace.
Resources
TechGenix’s Website
For more cybersecurity and technology news, check TechGenix’s Tech News here!
TechGenix Tutorials
Check out our tutorials on all tech tasks here.
TechGenix Microsoft Backup
Learn how to add a storage account in Microsoft 365 and sync to the cloud using our handy tutorial.
TechGenix Exchange Server Backup
Learn how to backup an exchange server in this handy tutorial.
TechGenix Webinars
Check out TechGenix webinars to learn more about the exciting world of tech!



