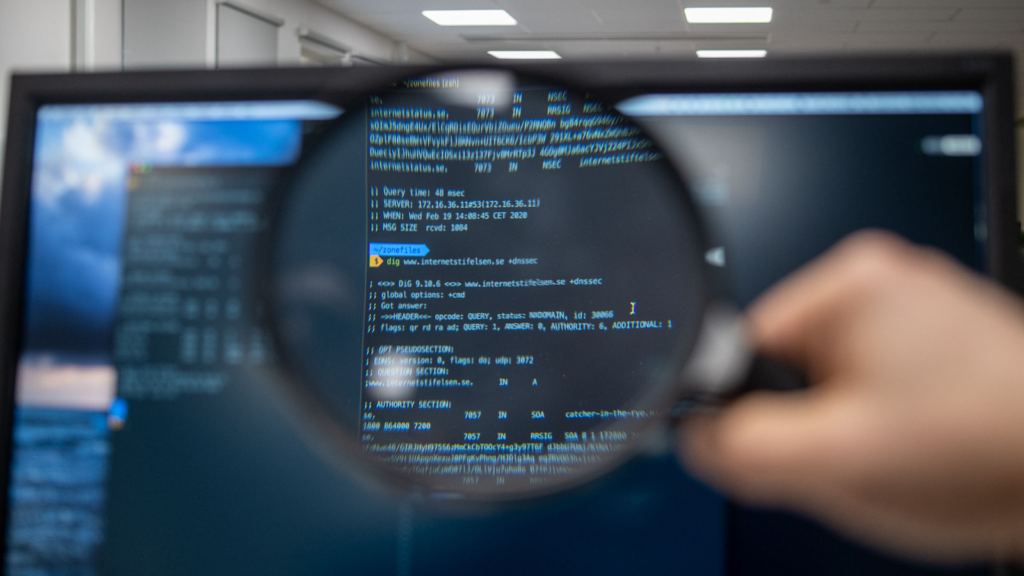
Directory Naming Service (DNS) helps resolve a site address from a common name using a list hosted on a server. When you type in a website address in human form, you need the internet protocol (IP) address. This is to send queries to the site and then download content to your browser. DNS hijacking intercepts your request and redirects you to a nefarious site or initiates a redirect download. Then, you can go to the site you originally wanted. But the malware download will have started.
In this article, I’ll discuss what DNS hijacking is and how you can protect yourself from it. First, let’s find out exactly how DNS hijacking works.
What Is DNS Hijacking?
Most companies don’t actively maintain their domain name system and trust the system once it’s set up. All bad actor attacks work on misplaced trust in a resource or process. When you enter a human-readable name for an address, the DNS gets queried and returns a new IP address. If this IP has been “resolved” before, most browsers will often cache it.
DNS hijacking is where bad actors incorrectly resolve the DNS address and provide you with the IP address of their website instead. For example, you type a website into Google. In this case, the DNS server should match the address you see with the IP address on its website. If bad actors change this IP, your browser may get a different IP.
This can be for a few nefarious purposes including collecting user data. You often find internet service providers (ISPs) do this to monitor traffic and collect data. Likewise, the National Security Agency (NSA) uses a similar process to force onion users through a specific server path. This is to identify “anonymous” users and monitor data. Users may also fall for an automated download containing some form of malware payload. This also includes adverts from the attacker in website banners. You’ll find 4 main DNS hijacking attacks that I’ll discuss below.
4 DNS Hijacking Attacks
When talking about DNS hijacking attacks, you’ll need to learn about 4 main ones:
1. Router DNS Hijack
A router is a network device designed to route traffic, making it a way for attackers to conduct a DNS hijack. Most routers come with pre-set credentials that many people forget to change. Router DNS hijacking is one of the easiest ways to conduct a DNS hijack attack. Cybercriminals can use various onsite or remote attacks to gain access to the router without too much technical knowledge. Most attacks utilize common penetration testing tools available with Kali Linux or downloaded from third-party vendors.
2. Man-in-the-Middle DNS Hijacking
This attack is also known as DNS Spoofing. It targets traffic between your network and website. First, cybercriminals add their router between you and your router. Cybercriminals can then implement DNS hijacking by intercepting the packet data and changing the header IP address between the source and destination. As the header of data packets are often unencrypted, the implementation of this process is easy. Most VPN encryption will be vulnerable without end-point protection. If you fear this attack, check out 1.1.1.1 Cloudflare technology.
3. Local DNS Hijacking
Cybercriminals can add a trojan to the cloak computer to implement local DNS hijacking. Trojan malware often appears as legitimate software and is useful for creating persistent website redirects. Cybercriminals use these to change advertising banners when installed and allowed to run on your system. The drawback of this attack is that most attacks become known quickly. Firewall malware lists will always include these trojans. To bypass this injection, attacks can only be useful while the user’s machine is powered on. Alternatively, attackers periodically change their malware code to bypass security lists.
4. Rogue DNS Server

This is where attackers hijack the DNS server. They alter the lists you can use if a public server propagates changes to the rest of the internet. This is one of the most difficult DNS hijacking attacks to implement successfully. That’s because these types of servers have high security. Attackers will need to find a weakness to gain DNS server access. They’ll also need to implement an attack before the exploit is found and patched. The benefit of this attack is the number of users that cybercriminals could exploit.
Now, let’s look at the issues DNS hijacking can cause.
How Do Cybercriminals Use DNS Hijacking?
Cybercriminals use DNS hijacking to take you to a fake site to steal credentials. Alternatively, this redirect can automate downloads from the attackers’ site or sell you items from advertising added to the site’s banners. If the fake site is a close approximation of the real one, attackers may be relying on this to gain trust. You may accidentally accept a prompt that helps download malware. Alternatively, applications installed on a genuine website can undergo modifications to add spyware, adware, or a different type of install-based malware. In this case, you will likely need to agree to run the software.
Next, let’s discuss how you can protect your business from DNS hijacking!
Protecting Your Business from DNS Hijacking
To protect yourself and your business, you have 3 main classes of measures:
1. Server DNS Hijacking Mitigation
Router DNS attacks require device reconfiguration for the attack to work. To stop this, you can:
- Install firewalls around your DNS resolution system
- Change the default credentials for the router
- Restrict access to the router
- Enable a multi-factor authentication process to reduce the possibility of unauthorized personnel accessing the system
- Use timeouts on server connections to reduce further risk of brute force attacks to gain access
To do the latter, you can use third-party solutions or implement it directly from devices and servers.
2. Education to Avoid End User Security Threats
You’ll have to follow certain measures to mitigate end-user threats. These measures are:
- Get users to change their passwords regularly and patch anti-viruses. This is because bad actors often wait to implement an attack with credentials.
- Get users to use VPNs to reduce exposure of data to cybercriminals. In most DNS hijacking attacks, cybercriminals are after user credentials. So, taking adequate operations security (OPSEC) precautions can help reduce risk to your business.
Note: If you want to hide DNS queries through encryption, check out 1.1.1.1 Cloudflare solutions or use VPNs with end-point protection.
3. Measures for Website Managers
DNS hijacking requires the bad actor to have access to your firm’s DNS solutions. That’s why you need to:
- Restrict access to the DNS hardware or software solution to only core members of your team. This will stop bad actors within your company from implementing DNS hijacking for the fear of being found out.
- Use monitoring tools and locks to ensure access to DNS systems doesn’t occur.
- Use security cameras to oversee physical systems and login and monitoring software for core systems.
- Set up multi-factor authentication for platforms and secure parts of the company.
- Implement a buddy system where someone shadows a lead.
Justify this as internal training to help retain staff and note that you may not use this system all the time
Final Thoughts
DNS hijacking targets changing the DNS resolver to send a user to a fake website. Cybercriminals can implement DNS hijacking in many forms and for a variety of reasons. They use this attack to implement another attack or exploit the user through trust engineering. To protect against DNS hijacking, you need to inspect several attack surfaces, which are part of your operations security measures.
If you want to know more about DNS hijacking and servers, check out the FAQ and Resources section below!
FAQ
What is DNS hijacking?
The Directory Naming Service (DNS) resolves a website address to the internet protocol (IP) address needed to send queries to the site. DNS hijacking intercepts your request. It then redirects you to a nefarious site or initiates a download-based attack. This includes installing spyware or adware or starting an injection-based attack with the user trusting the content.
How can you protect your business from DNS hijacking?
To protect your business from DNS hijacking, you must secure your router or DNS resolver with a firewall. You’ll also need to isolate your router physically. Ensure only a few members of the IT team have access to the DNS. In addition, you’ll need to get remote users to use VPNs to reduce access by bad actors to credentials.
Do I have to worry about Rogue DNS servers?
Bad actors can set up their DNS servers to redirect many users to their web addresses. That said, it’s uncommon since they need to find and use an effective exploit with a useful attack. You can patch exploits quickly, so this is a major problem for attackers. Rogue DNS servers are rare.
Can I reduce DNS hijacking attacks by training my users?
Training your end users about different attacks is one of the best ways to protect them. DNS hijacking often is only part of a bigger attack. Train users about how cybercriminals install malware along with spyware and adware. This may help them question what they see in their browser.
What type of firewall can help stop DNS hijacking?
DNS hijacking requires the bad actor to get to the router or your DNS solution to modify the resolver records. To stop this from occurring, you can either change the passwords that came with the hardware or use a firewall. You also need later-generation firewalls that can filter IP addresses, users, and regions. These firewalls should also be service-based.
Resources
TechGenix: Article on Malware
Discover what types of malware your cybersecurity may face.
TechGenix: Article on Operations Security
Learn what you need to make the security of your operations robust.
TechGenix: Article on Firewalls as a Service
Get more information on how to use Firewalls as a service (FWaaS) to protect your users.
TechGenix: Article on AI Poisoning Cyberattacks
Learn how AI poisoning could be a new threat to businesses.
TechGenix: Article on Cybersecurity Strategy
Discover how to create an excellent cybersecurity strategy.



