One of the best new security features to be released with Windows Server 2016 was the Host Guardian service. This is the service that provides the attestation and key protection services that are required for Hyper-V to be able to run shielded virtual machines.
Shielded virtual machines solve what may be Hyper-V’s biggest security problem – portability. When you create a Hyper-V virtual machine, what you are really creating is a few files that take the place of physical hardware. There’s a virtual hard disk file, and some files that store the virtual machine’s hardware configuration. You may also have files for virtual machine snapshots. The reason why this is a problem is because the virtual machine’s entire contents are written to a single virtual hard disk (although you can attach additional virtual hard disks to the VM).
Preventing ‘going rogue’
By default, Hyper-V uses dynamically expanding virtual hard disk files. This means that even though the default virtual hard disk size is 127GB, the virtual hard disk is initially only a few MB in size. The file grows as data is written to the virtual hard disk. Hence, a fully provisioned VM may realistically only consume 20GB to 30GB of physical storage space (although VMs can be much larger). A rogue administrator could easily copy such a file to a USB flash drive, slip the drive into his pocket, and walk out the door with a full copy of a virtual machine. The rest of the administrative staff is unlikely to realize that the incident ever even happened.
When the rogue administrator gets home, they can use the VM copy to boot and run the VM on their own system. Even something as simple as a Windows 10 laptop could run a Hyper-V virtual machine. If the rogue administrator doesn’t know the virtual machine’s password, or if they are missing infrastructure components such as a domain controller, then that isn’t a problem. The rogue admin can simply mount the virtual hard disk and browse its contents at will, without ever having to enter a password.
Shielded virtual machines solve this problem by encrypting virtual machine files in a way that prevents a virtual machine from being run on an unauthorized system. The encryption also protects against mounting a copy of the virtual hard disk on an unauthorized machine.
Configure a guarded host with the Host Guardian service
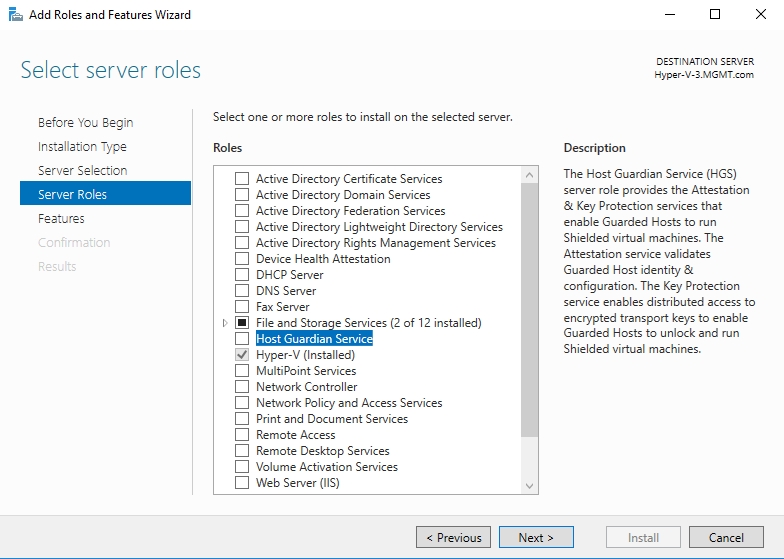
To use virtual machine shielding, the Hyper-V host must be configured to act as a guarded host. You can accomplish this by opening the Server Manager and selecting the Host Guardian service from the list of available roles, as shown below.
Using Server Manager to enable the Host Guardian service is fine, but if you manage your network using System Center, then you will be happy to know that you can use System Center Virtual Machine Manager to enable the Host Guardian service.
To enable the Host Guardian service through Virtual Machine Manager, open the Virtual Machine Manager Console, go to the Settings workspace, and then click on the Host Guardian Service Settings option. This will cause VMM to display the Host Guardian service Settings screen shown below.
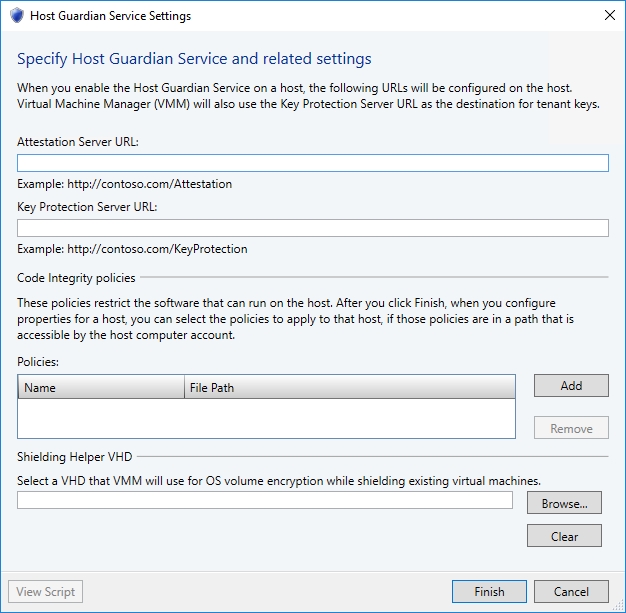
As you can see in the figure, you will need to begin by providing a pair of URLs to be used by the Attestation Server and by the Key Protection Server. The dialog box gives examples of what those URLs should look like. The dialog box also contains options for providing a code integrity policy and for specifying a virtual hard disk to be used during the encryption process. You don’t have to worry about setting those options right now.
Unfortunately, when it comes to enabling the Host Guardian service on existing Hyper-V hosts, VMM makes you enable each host individually, as opposed to performing a bulk operation. To enable the Host Guardian service on an existing host, go to the console’s VMs and Services workspace, expand the All Hosts container, and then select the Hyper-V host that you want to manage.
Maintenance mode
Before you can enable the Host Guardian service, you will need to put the host into maintenance mode. To do so, right click on the host and choose the Start Maintenance Mode command from the shortcut menu. With the host now in maintenance mode, right click on the host once again, and choose the Properties command from the shortcut menu. This will cause the console to display the host’s properties sheet.
The next step in the process is to select the properties sheet’s Host Guardian service tab. Enabling the Host Guardian service is as simple as selecting the Enable the Host Guardian Service checkbox and clicking OK. Even so, there are a couple of important things that you need to know.
First, VMM checks to see if the Host Guardian URLs have been configured. If you have not properly configured the URLs, then you will see a warning message like the one shown in the figure below.
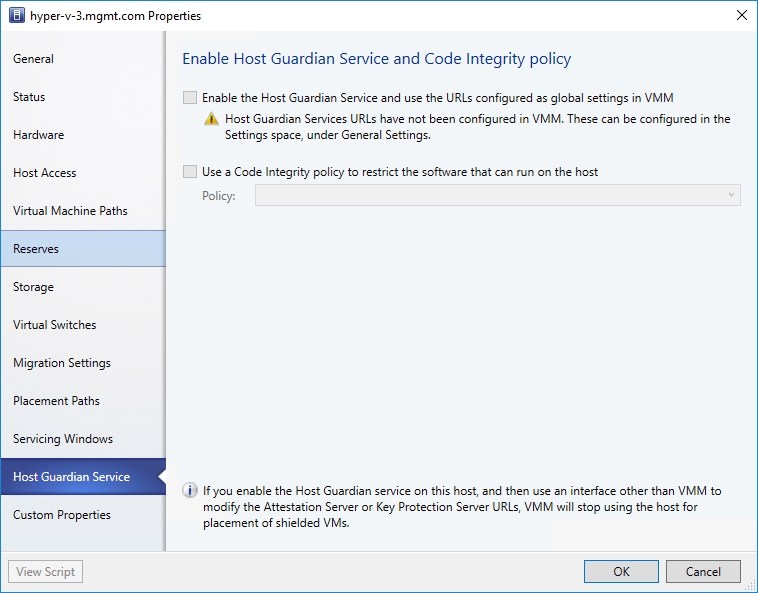
The second thing to be aware of is that once you enable the Host Guardian service, then you will need to manage it using only VMM. If you make a modification to the Attestation Server or the Key Protection Server URLs from outside of VMM, then VMM will stop allowing shielded VMs to be placed on the host.
As you can see, using VMM to enable the Host Guardian service on a Hyper-V host is a fairly straightforward process. Just be sure to take the host back out of maintenance mode when you are done. Once the Host Guardian service is enabled, then you can go back and configure the previously mentioned Shielding Helper virtual hard disk, and any necessary code integrity policies.
It is worth noting that adding a code integrity policy to VMM through the interface shown in the second screen capture does not cause the host to use that policy. Once a code integrity policy has been created, you will need to go back to the host properties sheet and select the code integrity policy that you want the host to use.
Photo credit: Freerange Stock




Hi Brien
Thanks for the good article. I have one question left, is it ok to put the HGS role on the same physical host that u use as Hyper-V Hosts? Could it give problems?
Kind regards,
Tomas