Network security has now achieved an unprecedented level of visibility in today’s corporations. Company CEO’s now realize that to run an efficient business you need to have your digital assets secure. Note that I don’t say most organizations run their security practices well, but rather that they at least have them now. Network security much like system administration is a difficult job, and it does not help if both are assigned to one or two people. Commercial vendors have designed a lot of solutions to help networks stay secure, be they software or hardware based, or a combination of both.
The tools offered to today’s network security practitioners are not only varied in application, but also in their ability to give you one crucial element in your daily battle against malicious hackers. That being the ability to give you meaningful output. What good is a firewall, IDS, IPS, or whatever else if the output is not only cryptic, but also unusable? I have had experience with a wide variety of vendor solutions and have found no real easy way of tying them together in a meaningful way. You would be surprised at the amount of logging that is going on in your organization today if you really thought about it.
Hackers and residue = CSI style fun
To give our event log and monitoring consolidation some context let’s go through how a hacker could compromise your network, and see if they leave any “residue”. What I mean by residue is that, were there any tracks that they left as they went about trying to break into your network. Did they for example get logged by one of your routers ACL’s (access control list) as soon as they crossed your edge router. Did the firewall you have behind your router log anything of interest about this attacker? What about the IDS that you have plugged into the span port of your main switch have to say? The list goes on depending on your network layout and need for security.
Well with the above paragraph in place, let’s trace out a typical attack that one might see in today’s corporate network environment. Our dubious hacker scans your network block and settles on a specific IP for further scrutiny. Now that he has a specific IP in mind they decide to “light up” your network by scanning for a specific series of ports. This could include all of the usual victims;
TCP Port 21 FTP
TCP Port 22 SSH
TCP Port 25 SMTP
TCP/UDP Port 53 DNS
TCP Port 80
UDP Port 161
TCP Port 443 SSL
Also seen from the hackers point of view.
Figure 1
With the above list of services ticked off in their favorite port scanner, likely nmap, the malicious hacker probes your network. Depending on your network defenses, this scan initiated by the hacker should have been logged. It may not stand out all that much on its own, but it should have been logged nonetheless. What if the hacker decides to do what is called a “low and slow” scan? What is “low and slow” you ask? Well a “low and slow” scan is where the hacker probes your network with only a couple of packets a day over the course of a week or weeks. The one advantage to doing such a scan is that the hacker is far less likely to stand out in your logs. That is unless you are doing event log monitoring and consolidation. More on that later on though.
What about my other devices output?
There is not only the firewall and router to look at in terms of logged events. One of the best ones to view is that of the intrusion detection system. This is especially true if you have taken the time to properly adjust, over time, the device itself. All intrusion detection systems are prone to false positives just like any system. What you can do over time though is disable alerts for services you do not have, and also fine tune the ones that you must have turned on. Also you would be wise to write yourself some egress filters as well. That way, while you may not catch a hacker on the way in, you very well might on their activities such as having a reverse command shell sent to them.
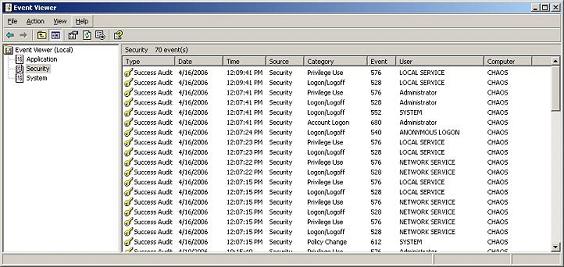
Further to security devices are the logging capabilities of your network administration control devices such as your PDC, BDC, or Active Directory controller for example. These systems will log a fair amount of interesting data themselves. This is a fact that pretty much almost every system administrator can attest to. Much like raw data such as packets are to me, is the information provided to the sys admin via the event viewer as seen below equally important.
Figure 2
You are able to keep a fairly close eye on the goings on of your internal network through the use of the event viewer as seen above. The information shown above can then be further correlated with the output of other devices as mentioned in the paragraphs above. That way you are presented with a far fuller picture of what is happening on your network. What would be nice though is to have a means of integrating all of these various outputs into one central console.
Consolidation
Over the course of the article so far we have seen that there is a tremendous amount of output generated by various devices on your network. The problem is that it is fairly difficult, to darn near impossible, to have them all in one spot at once. I have seen various offerings from vendors who will correlate some of your networks security devices in a nice GUI driven environment. Having the ability to quickly and easily see what is happening is a key factor in helping you secure your network assets.
Should you be able to tie together all of this output so that you would be able to track hackers as they attempt to penetrate your network. You would also be able to detect those “low and slow” scans that I mentioned earlier. While such a stealthy scan may not stand in one day’s traffic, it would stand out when aggregated over a month’s traffic. One key theme that we keep seeing here is the need to have the output logs of all these network security devices in one place ideally. Much like a ships Captain gets all the information from those around him, you in turn would be fed all of the information from the outlying devices.
Wrapup
There is little doubt that having quick and ready access to logs from your security devices is of key importance. This is even more true when you have all of that information in one place. You would then be able to make some informed decisions based on analysis as it pertains to your network. Often times, when information is taken without context, it is difficult to leverage. On the other hand when you can correlate it with information, you are able to see it for what is it; a gold mine of data logged by your security devices. My advice to you is to do your best to amalgamate all of the logs into one central repository. It will pay off quite handsomely for you I am sure. On that note I will end the article, and as always welcome your feedback. Till next time!