In these difficult times, the use of technology and remote connectivity is crucial. I have seen an increasing number of requests between companies and partners to allow remote access to perform activities in Azure subscriptions. In this article, we are going to cover the required steps to allow an external user to authenticate and access your Azure resources. We are going to cover what the cloud administrator can use to track and understand the usage and permissions given to any external account.
Here’s the scenario: We will start with a single Azure subscription for which we need help from a vendor to connect and perform some assessment, or to help us in any shape or form. The process to allow an external user to authenticate and access your subscription is done through Azure Active Directory when we create a guest user. We can use any email address that the vendor may have, as long as they have a Microsoft account assigned to that email address.
If there is no Microsoft account associated with the account before the invite, the association can be created easily before or after by accessing your account.
Creating access for a vendor
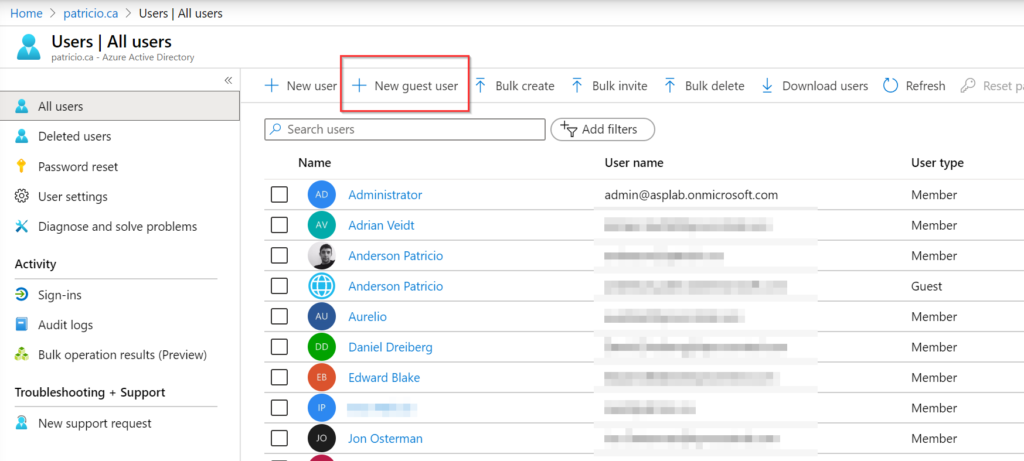
The process to create the external user to access your Azure resources is this: Click on Azure Active Directory, then click on All Users. A list of all users will be listed on the right side, click on New guest user, as depicted in the image below.
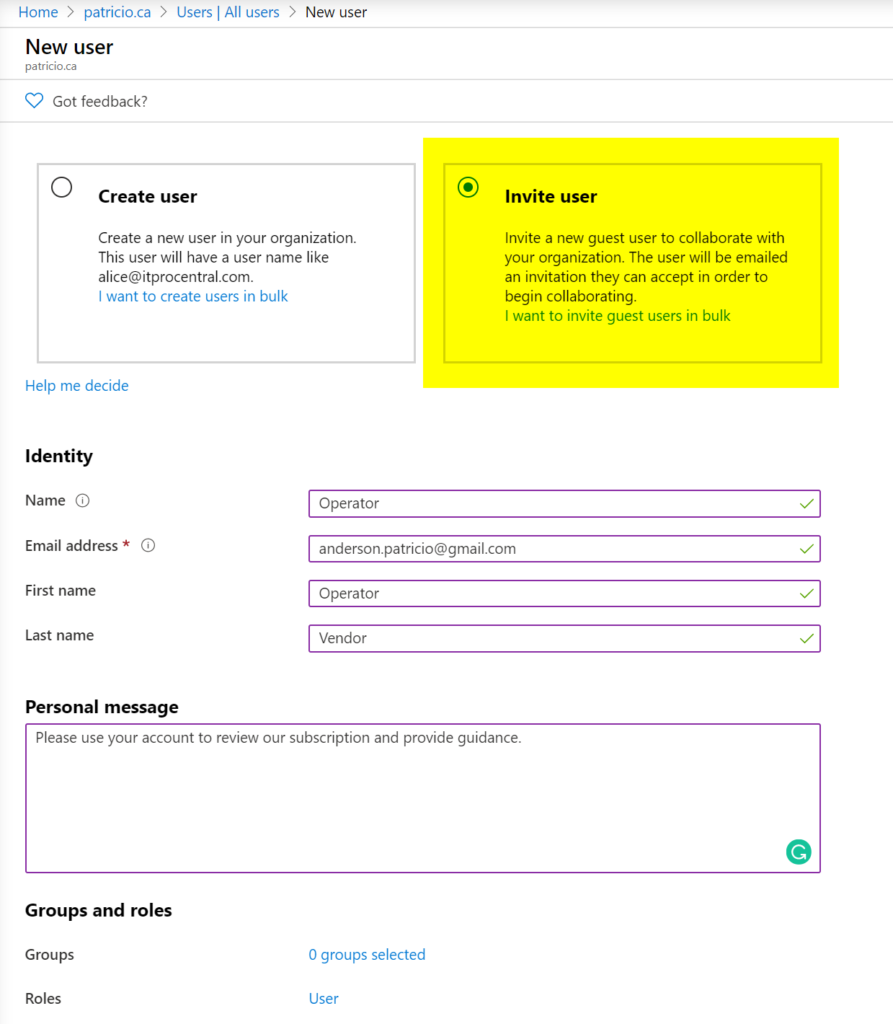
In the New user blade, select Invite user, fill out the Identity information for the given user, and we can even add some additional information to the invited user. To complete the process, click on Invite.
The vendor will receive an email with the invitation (similar to the images depicted below). To complete the process, click on Get started and authenticate using your Microsoft account credentials associated with the email.
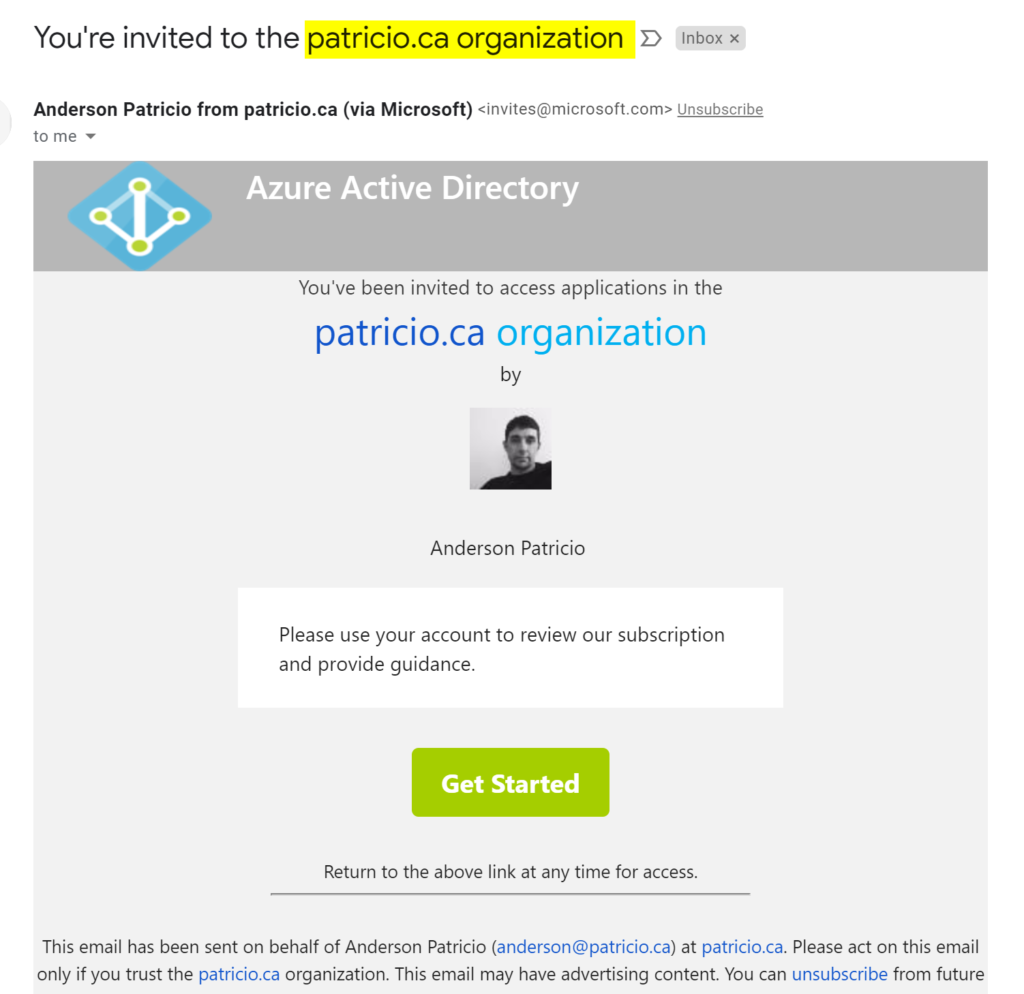
In some cases, you may not end up in the Azure Portal after authentication but in the Microsoft Apps site. Since you are authenticated, you can simply type in https://portal.azure.com.

Assigning permission to a resource group
In the previous section, we covered the basics to create a guest user and the process that this external user has to follow to authenticate in Microsoft Azure.
We are going to switch gears and go over the process to assign the RBAC (role-based access control) to the given user and see how it plays out in real life.
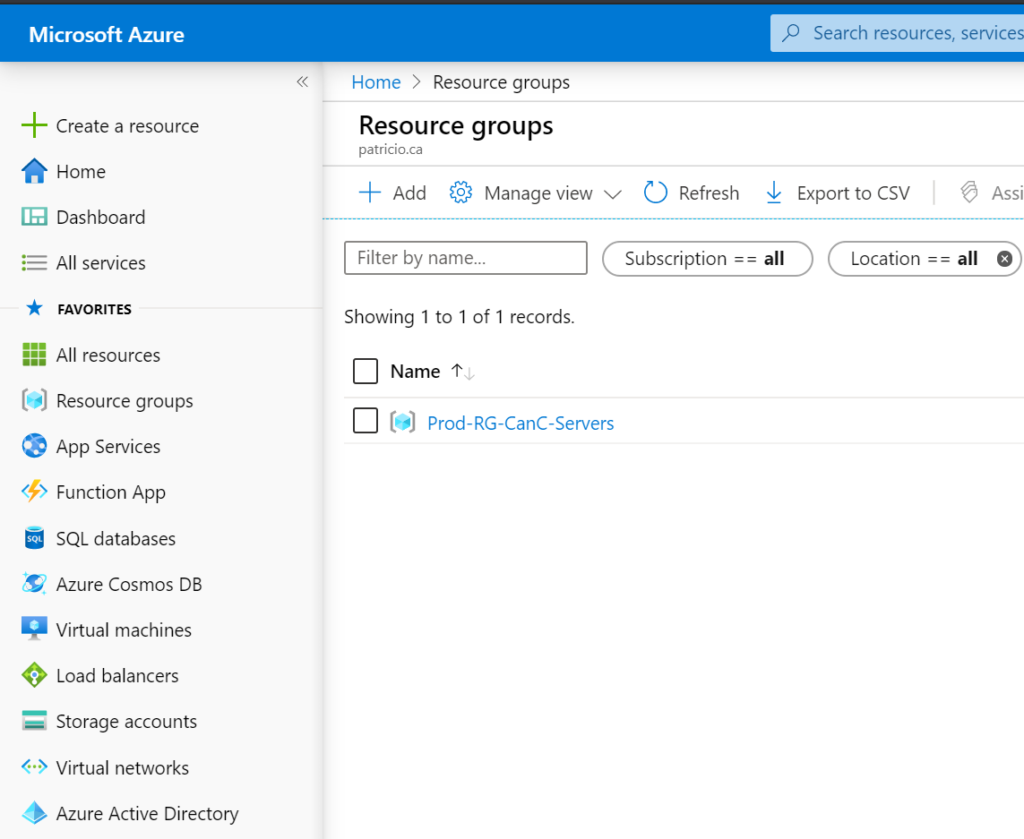
We can either assign administrative roles, which will give access to Azure Active Directory and some services shared at the tenant level (Office 365, security, and so forth), or assign specific permissions within a subscription. In the example below, we are going to assign permission to a particular resource group called Prod-RG-CanC-Servers.
Click on the desired resource group (Item 1), click on Access control (IAM) (Item 2), click on + Add (Item 3). In the new blade on the right side, select the role Reader and select the guest account that we have just created and click on Save.
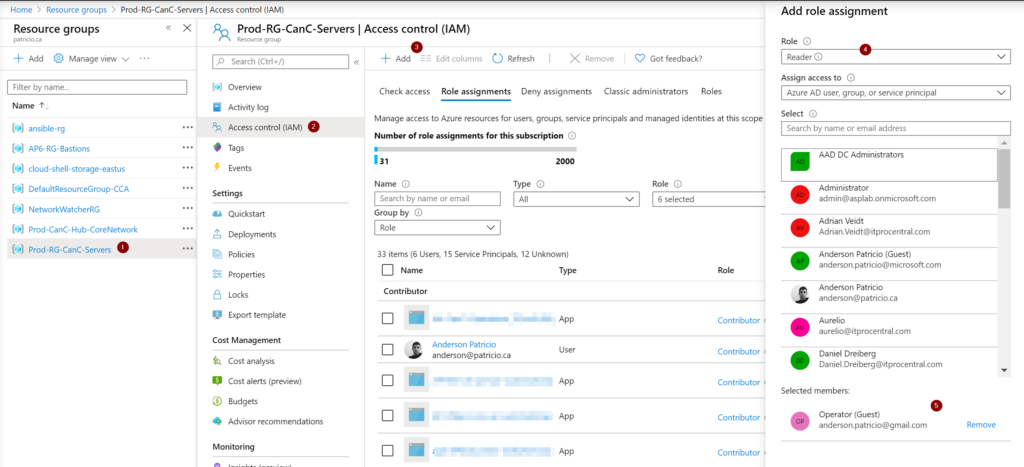
The results of the permissions that we have just introduced can be seen when the guest user tries to access the Azure portal. As we can see, the guest user will see only the resource group that we allow them to have access to. In our article, we are giving read access, which means the guest user will be able to check all settings of that given resource group. However, they won’t be able to do changes on the resources, start a VM, or even check Azure AD information.
Managing guest user access
So far, we created an account for an external entity in our Azure Active Directory, and we assigned permissions based on our business requirements.
The cloud administrator must be aware of the options available to track and understand how the guest user is accessing the environment.
The first view that provides some information is the Profile item of the user’s properties. To get there, click on Azure Active Directory, click on All Users, and click on the desired user from the list. The result should be like the image depicted below.
On the right side, we can see the number of sign-ins (Item 1) of the specific account, and that indicates the activity of the user. We can also check if the invitation that was sent was accepted (Item 2), and the other evidence is the Source (Item 3). If it is Microsoft account, we know that this account is using that method to authenticate.

If we want more detailed information and historical data, we can always click on Sign-ins item. A list of all attempts of that account to access the resources will be displayed, including the status, IP address, and location. We can export that data (up to 250k records) to a CSV or JSON file. Another feature is the ability to narrow down the results by adding and changing existing filters.

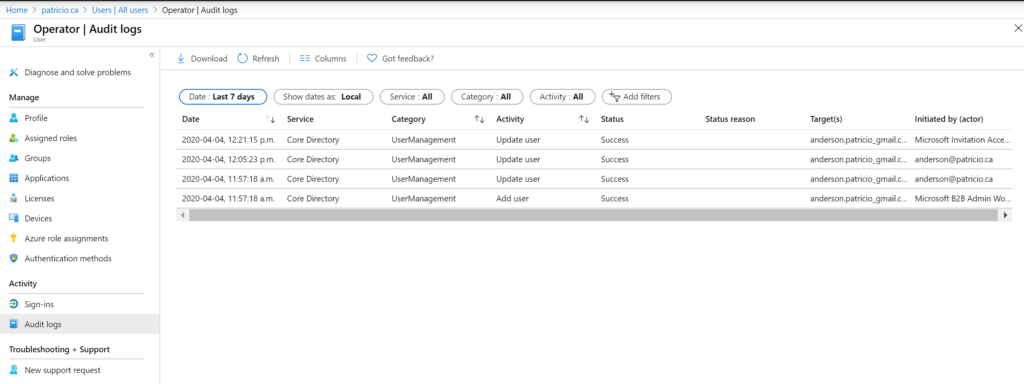
If we want to get more information about changes at the guest account level, we can use the Audit logs item. All changes from the Azure Active Directory perspective in that given account will be logged.
Another useful resource is the ability to check in a single glance all permissions of any given user in your Azure subscription. We can get this view by clicking on Azure role assignments. A list of all roles, resources, and resource types will be listed.
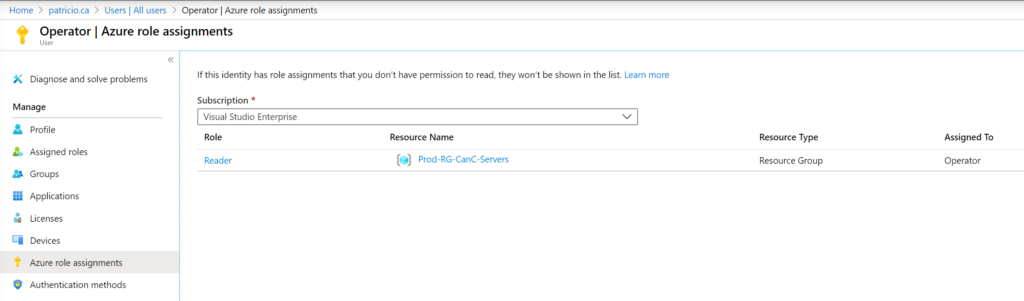
We can check the administrative roles at the tenant level using the assigned roles item as well.
External access to Azure: Only give enough permissions
We covered all the necessary steps to allow an external guest user to authenticate and perform activities on your Azure subscription, and most importantly, how the administrator can track the use of that credential.
Make sure that you only give enough permission to complete the task, and remove the access when it is no longer required as a security best practice. We don’t need to delete the guest account, just block the ability to sign-in.
Another point worth mentioning is that all changes performed in Microsoft Azure are logged, and we can track any possible changes from a guest user as well as regular users. A simple and easy way to access that information is using the Monitor feature and then click on Activity log.
Featured image: Shutterstock




Hi, great article. What if I need to provide this user RDP access to a VM in the resource group via JiT? what additional permissions are required?