Most people don’t realize that their Office 365 subscription is tied into Azure. Stop and think for a second. What is handling your authentication when you log into Office 365? Since this is an article about Azure, you would be wise to have guessed Azure Active Directory. So yes, if you have an Office 365 subscription then you have Azure Active Directory. If you’d like to understand what your options are for integrating Azure AD into your on-premises AD, use this support article from Microsoft. Depending on your level of Office 365 subscription, you get a corresponding level of Azure Active Directory. Azure AD is divided into Free, Basic, Premium 1, and Premium 2 levels. Most people have either Free or Premium. For details of what each level provides, use this support article from Microsoft.
The first thing that you need to realize is that Azure AD is not exactly like your on-premises AD. The domain controller model doesn’t apply here because you can’t scale that big enough for Azure. So open your mind and get ready for a new authentication experience that Microsoft happened to also name Active Directory.
Activate your Azure AD benefit
Although your Azure AD exists the minute you sign up for Office 365, your ability to manage it is not available until you activate it. Follow along in this article through that process. Note that although it asks for a credit card as authentication material, it does not charge that card as long as you don’t level up beyond what you’ve purchased with your Office 365 subscription.
Self-service change password portal
Since everyone gets a self-service password portal, you should start with your configuration here. The self-service portal will allow your users to go to a website and change their password. Since we all know that users are really good at ignoring that popup that says your password will expire in 14, 13, 12, 11, etc. days, having this portal setup will save you some time. After it is set up, just point them here.
To set it up, go the Azure AD in the Azure portal. On the Overview page you’ll find a link to the Password Self-Service configuration page. The first thing that you’ll do is enable it, either for everyone or just a group.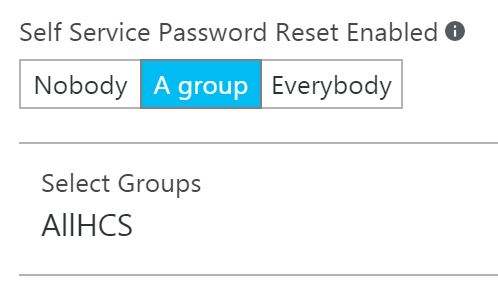
Next, you’ll choose the authentication methods by which users are going to verify that they own the account.
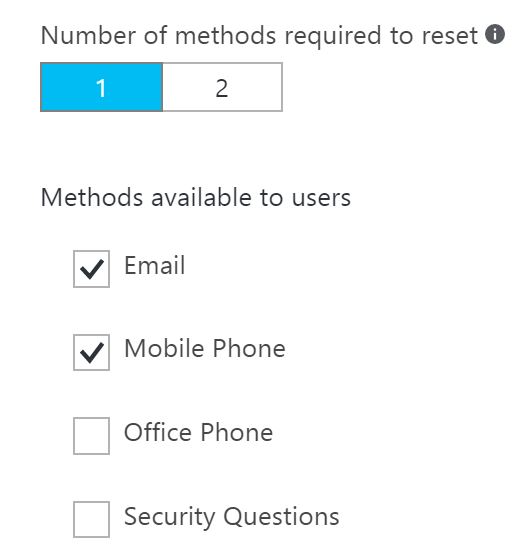
Now for a couple of nice features that you don’t get with on-premises AD. You have the option of enabling some monitoring that will let the user and the admin know when a user’s password has been reset. And you can also enter a URL or email for the users to go to if they need help changing their password.

Reports
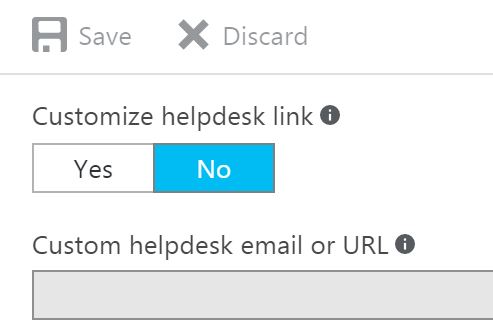
Even at the most basic level, everyone gets some reporting capabilities. I use the Premium 1 level that comes with the EMS package, and about 50 reports are preconfigured for me to use. At the most basic level you get three reports. Now that you have your Azure AD connected to your Office 365 subscription, you will access your AD reports from within the Office 365 portal. To find them go to Reports, Security and Compliance, and Select Azure AD Reports. A new window will open.

Here you’ll see the full report list that you have access to. They are categorized into Licensing, Anomalous Activity, Activity logs (general auditing), Integrated Applications reports, Right Management usage, and External Access grants. Drill down and you’ll find more items within the list. These reports will give you information about weird stuff going on with your users. Microsoft likes to show this one off in just about every presentation they make. It does have a high coolness factor because knowing that someone is logged in from two impossibly geographic places is pretty useful knowledge.
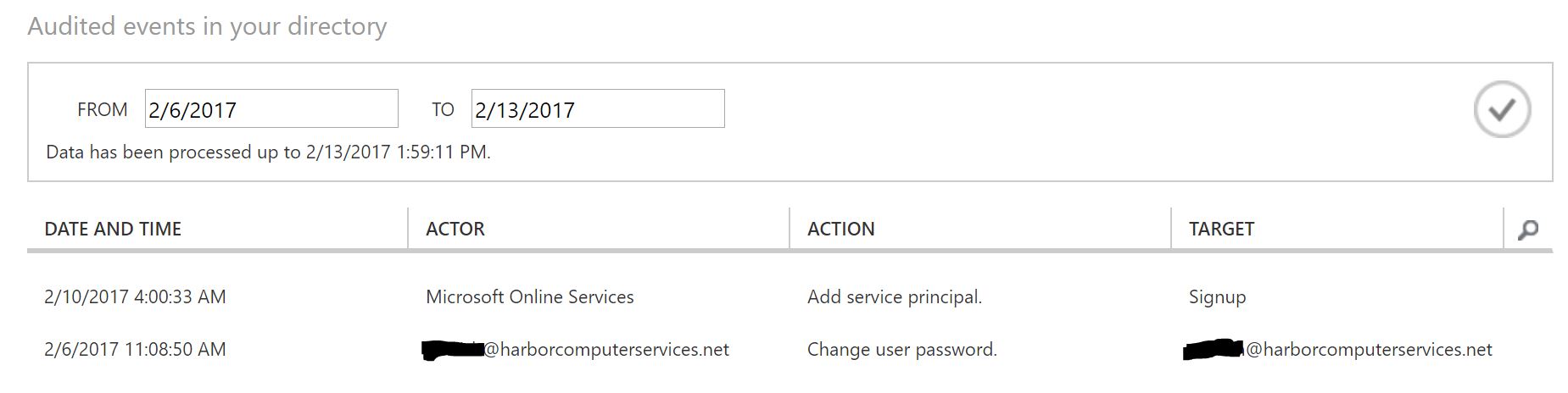
I like to look at the general audit report as well. It gives me a quick overview of what’s been going on with Azure AD and Office 365. Below, I see that a new user signed up and that a user changed his password. Nothing odd there so I’m happy.
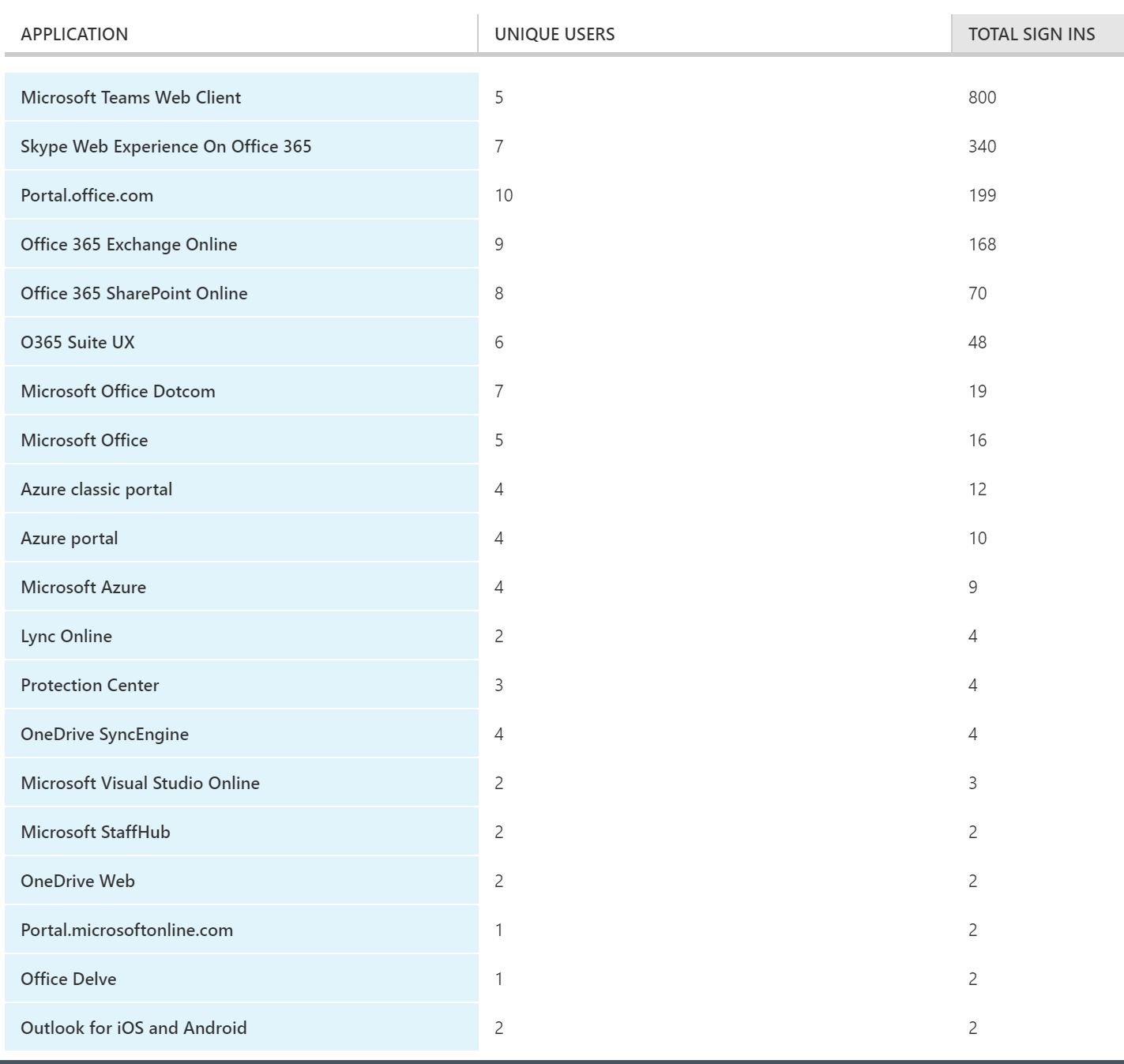
Another example of an interesting cloud report that is hard to come by with traditional on-premises application is a usage report. As IT comes closer into the inner circle of departmental and C-level management, one of the questions to answer is whether your users are actually using the applications that you’ve purchased for them. The usage report lets you know. From there, it’s up to you to determine the WHY behind the data.
Next, you might want to consider customizing the login pages and branding your portals or using Rights Management, which comes with most of Office 365 subscriptions. But the features that we’ve covered at least should have you exploring your Azure AD benefits that you probably didn’t even realize you had.
What’s next?
We’re definitely getting there! Hopefully, by now you’ve got several things going on in Azure and some fine-tuned configurations are coming together. Ideally, the wheels in your brain are spinning and ideas for how you can put this into production are popping up.
I’m going to write one more getting started article for this series, and it will cover monitoring, alerting, and a little security. Azure has recently released a large number of options with some great new sub-portals to help IT administrators keep tabs on what’s going on with their growing Azure infrastructure. We’ll take a look at those and some of the automated tools that will make your job a bit easier.



