
Does Terraform ring a bell? I’m sure it does as it’s one of the most used Infrastructure as a Code (IaaC) tools in the industry right now! Haven’t heard of it? How about HashiCorp tools? HashiCorp is a software development company that creates tools for DevOps processes and cloud computing. Stick around as I take you through all the cloud tools HashiCorp offers.
In this article, I’ll be covering 4 HashiCorp tools and their respective functions. I’ll also show you how they can improve your DevOps tech stack. Shall we?
4 HashiCorp Tools And Their Functions
1. Terraform
Starting off with Terraform, this tool has become an extremely popular tool for building out IaaC, due to the fact that it serves more than 100 cloud providers. In other words, if your provider has an API, then it should work with Terraform.
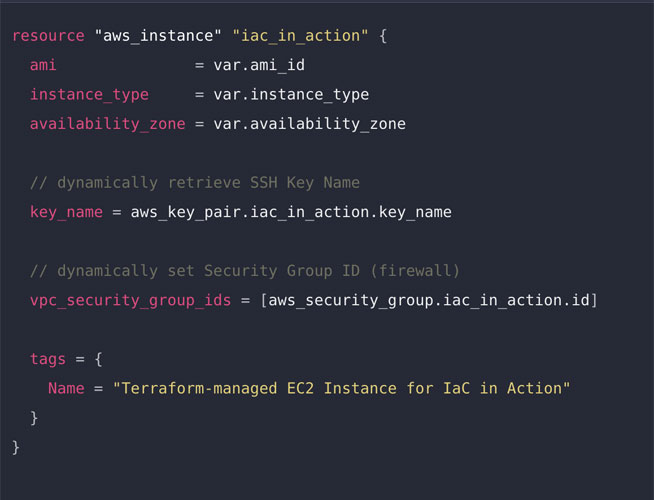
Terraform is an imperative language that is very helpful to you and your team. Being an imperative language takes a lot of the hard work out of the equation. In case you didn’t know, an imperative language will take what’s written and do all the steps required to get that infrastructure in the state that you tell it to be in. If you request to create one linux vm, it will do all the work on the provider (AWS, Azure) side to do that.
Now, let’s take a look at what Terraform can actually do for you!
Maintain State
Terraform is unique because it has a state and that state can be kept in a cloud or on a server. That means it has a single source of truth and many engineers can work with the same state. The state will be updated once you have made your changes and run the “terraform apply” command. The state will then update and pass the changes to the provider which will, in turn, make the requested changes to the infrastructure.
Reuse Code with Modules
Additionally, Terraform offers you a great way to package and reuse common code in the form of modules. Terraform modules are similar to functions or methods in scripting or programming languages. They present a typical interface for creating resources by providing inputs and returning outputs. By creating modules, it’s easy to duplicate resources or share the modules with other teams in your organization.
In short, Terraform has a lot of great features that make it one of the best of HashiCorp tools. It’s one of the highest-rated IaaC tools in the industry right now because it’s easy to use and provides a lot of added efficiency to your DevOps workloads.
Moving along, let’s dive into Vault, what it is, and what it does.
2. Vault
Question: Where do you store your secrets? Simple answer: In a vault. Vault was designed to protect sensitive information in low-trust environments. It can act as encryption, and it can also manage secrets and offer identity-based access. Vault is able to store all your access tokens, passwords, certificates, encryption keys, and other secrets. This can be done using the Vault UI, the terminal, or the API.
Now that you have an idea of what Vault is, let’s touch on some of its functions!

Secret Management Made Easy
Vault’s main specialty is to store secrets. It can also store any type of secret you want with access tokens, API keys, usernames, and passwords. You can easily control access to these secrets. Need to rotate keys? That’s not a problem. That can sometimes be an arduous task, but Vault makes it easy. Did an employee leave and you need to revoke access right away? Done. Vault gives you complete control over your secrets and who has access to them.
Encryption As A Service (EaaS)
Vault offers encryption as a service (EaaS), by encrypting data in transit with TLS and at rest, using AES 256-bit CBC encryption. This protects sensitive data from unauthorized access when it’s traveling across your network. It also shields in when it’s in storage on the cloud or on-prem data centers.
If you have centralized key management, it’s easy to update and roll out new keys across distributed infrastructure.
Identity-Based Access Controls Who Can Use it
Vault manages identity for both humans and machines. For human users, identity is managed with role-based access control (RBAC). RBAC allows you to grant or restrict access based on the user’s role, and this RBAC works based on the current secret RBAC that the current user is using.
For machines, it’s a different process: they connect with a different secret or point it to a different server. Vault helps create temporary access tokens that can be revoked immediately if you find some suspicious activity or an actual network breach. You can also generate on-demand secrets that are assigned and revoked immediately after the job is done.
All in all, Vault is a great tool for managing and storing secrets, as well as using RBAC for systems and users, and last but not least using encryption in transit with TLS and in storage with AES 256-bit CBC encryption. To bring things all together, let’s take some time to review Consul, HashiCorp’s service mesh.
3. Consul
Consul is the third of HashiCorp tools we’ll be looking at, and it’s a service mesh that allows DevOps engineers to check the health of applications, store keys, connect databases and provide service discovery all out of the box. Essentially, Consul is a neat application providing several services!
Health Check Made Easy
The consul agent daemon runs a health check against all connected servers and provides updates on the dashboard. No configuration is necessary. This is a very helpful way to keep track of your servers’ performance. Furthermore, with the round-robin DNS combined with the health check, you can get rid of internal load balancers when using Consul.
Key Storage That Is Not Confusing
Consul includes a basic key storage, but if you’re using Vault in conjunction with Consul, then you don’t need Consul’s key store as Vault is the obvious winner. However, if you aren’t using Vault, then Consul has your key storage covered.
Database Connections Made Quick
You can define multiple data centers, where each data center has its own key/value (KV) datastore. This is a powerful way to store your non-prod KVs separately from your prod KV store.
Service Discovery As Simple As Turning Consul On
Last but not least is the built-in service discovery which works immediately with the Consul Daemon. The Daemon runs and pings all the services it finds and brings them in under the Consul dashboard.
To sum up, Consul is a great service mesh tool designed to reduce the number of other applications you’d have to otherwise use to replace it. Consul works really well together with AWS and Docker, so if you have those two in your tech stack, you might want to consider using Consul alongside them.
Now, let’s quickly touch on Packer and what it does before we wrap up.
4. Packer
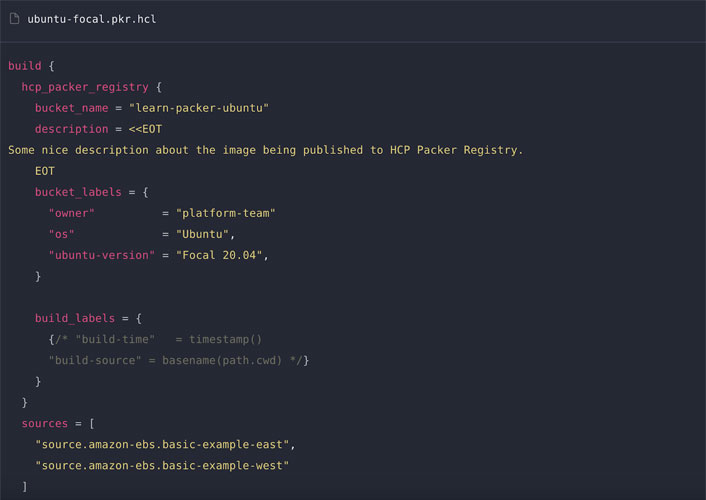
Packer automates the creation of any form of machine image. This brings a game- changing advantage to the table because, normally, the creation of machine images is a tedious task that eats up a lot of your time. Packer allows you to launch and deploy machine images in seconds because they’re already pre-installed and ready to go. Packer also offers you a super-fast setup time, and multi-provider portability, meaning you can use all the major cloud providers such as AWS, Azure and Google Cloud.
The Bottom Line
In this article, I talked about 4 HashiCorp tools that can really add value to your tech stack. First, I showed you Terraform’s IaaC, the company’s most popular tool due to its single source of truth state, modules, and code reusability. These features make it a sure fire winner in the IaaC market. We also talked about Vault, an excellent tool for managing secrets and restricting/granting access to systems. What’s more, I explained Consul’s 4-in-1 service mesh that allows engineers to monitor systems and connect databases with many cloud providers. Finally, I showed you how Packer solves the time problem of building and deploying machines images. Overall, HashiCorp tools are easy to work with, highly integrative and well-maintained. They’re a great asset to your organization.
FAQ
Do HashiCorp tools work with all cloud providers?
HashiCorp works with over 100 providers including the main cloud providers such as AWS, Azure, and Google Cloud. So you, generally, shouldn’t have a problem integrating with a cloud provider.
How can I use Terraform output as input for the Azure ARM template?
You can define the output of Terraform yourself and then just create resources for them in order to store them in the key vault/storage/tables. That’s the great thing about Terraform, as you can call your outputs whatever you want!
Why is Packer an important HashiCorp tool?
Packer helps keep development, staging, and production environments as similar as possible. Packer can be used to generate images for multiple platforms at the same time and they can be generated at the click of a button taking out a lot of the work that had to go into building machine images.
How good is Vault’s encryption service?
Vault follows in accordance with industry standards and uses TLS when moving data on a network and AES 256-bit CBC encryption when data is being stored. That means the encryption and security levels are very high. In turn, that makes Vault a very powerful HashiCorp tool.
How secure is Consul’s key store encryption if not using Vault?
Consul lets you use Gossip encryption or TLS. Again, Consul is following industry standards for security and encryption. This HashiCorp tool is very secure, and you can use it with Docker and AWS.
Resources
TechGenix: Article on The Skills that every DevOps Engineer needs in 2022
Learn about all the skills you should know about in 2022 here.
TechGenix: Article on an Expanded Open Source Collaboration Announced by Google and HashiCorp
Find out about what Google and HashiCorp are collaborating on here.
TechGenix: Article on Terraform 101–A Beginner’s Guide for Arm Template Lovers
Learn how to get started using Terraform here.
TechGenix: Article on The Most Important Launches from AWS, Azure, and Google Cloud in 2022
Learn about all the major launches coming from the big cloud providers in 2022 here.
TechGenix: Article on Using Storage Accounts in your Automation Accounts in Azure
Learn more about using your storage accounts in Azure here.



