
Source: Comodo Cybersecurity
Cybercriminals constantly develop new methods of attacking your company. After all, they want to steal your valuable data and disrupt your operations for financial gain. These criminals typically use viruses as a common attack strategy. Moreover, these viruses are becoming more sophisticated as time passes. So, how can you defend against them? Heuristic analysis is the answer!
Interested in learning more about it? Well, you’re in luck! In this article, I’ll go over what heuristic analysis is, its benefits, and how it works. Then, I’ll go over some problems you might face when applying it. Lastly, I’ll cover how you can run an effective heuristic analysis. With that said, let’s begin!
What Is Heuristic Analysis?
The term “heuristic” refers to a problem-solving approach that uses a calculated guess based on previous experiences. Let’s say you repeatedly observe that it rains when the sky gets cloudy. On the next cloudy day, you might “guess” that it’ll rain based on your previous observations.
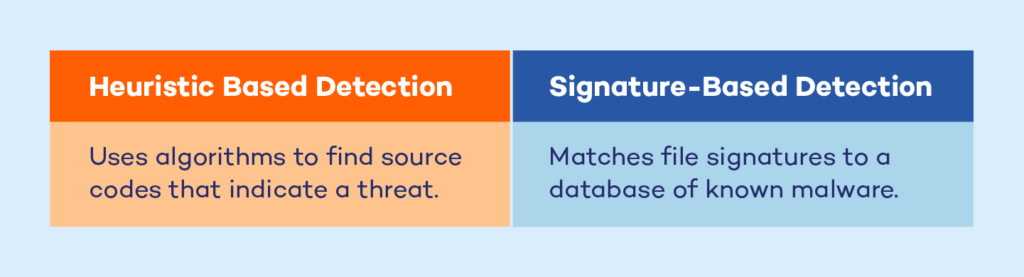
In cybersecurity, heuristic analysis is a method used to detect malware. Essentially, it does this by analyzing the program’s source code for suspicious behavior. Overall, it’s an automated and rapid malware detection method that increases security teams’ efficiency.
Traditionally, security teams discovered malware through a method known as signature detection. This method compares a program’s code against a database of known viruses. However, given the evolving cyber threat landscape, the method is tedious and inefficient.
Heuristic analysis is an improvement upon signature detection. Using it, you can detect previously unknown or upgraded viruses. In turn, this allows your security team to stay on top of any threat.
Source: Panda Security Mediacenter
Now that you understand what it is, let’s look at some of its benefits!
3 Benefits of Heuristic Analysis
Heuristic analysis is a crucial strategy for malware detection. Here are some of its benefits:
1. Polymorphic Virus Detection
Polymorphic viruses are highly intrusive viruses that constantly morph to evade detection. Specifically, they periodically alter their source code to avoid signature detection. Programs that incorporate heuristic analysis can detect these viruses.
2. Zero-Day Threat Detection
A zero-day threat is a previously unknown attack or threat. Essentially, a cyberattacker would scan your software or IT system for vulnerabilities. They then create a virus to exploit those vulnerabilities. Before anyone realizes, you’re in trouble. Heuristic analysis can protect you from zero-day attacks. To clarify, you can use it to detect and isolate any attack before it inflicts heavy damage.
3. Improved Accuracy
Heuristic analysis can accurately detect normal system program behavior. As a result, this limits the number of false positive malware categorizations. In turn, your team will only receive an alert when an actual virus pops up.

Source: Hasan Albari On Pexels
So far, you’ve learned what heuristic analysis is and how important it is. But how does it work exactly? The next section has the answer!
How Does Heuristic Analysis Work?
Antimalware solutions employ two methods for heuristic analysis: static and dynamic heuristic analysis. Let’s look at each one in more detail.
Static Heuristic Analysis
In static heuristic analysis, an antimalware solution reverse engineers, or decompiles, a program’s source code. The solution then tests the source code and matches it with previously known viruses in the heuristic database. If a predefined portion of the source code matches with the database, the solution immediately flags the program as a potential threat.
Dynamic Heuristic Analysis
In dynamic heuristic analysis, an antimalware solution isolates a suspicious program and allows it to run in a controlled virtual environment known as a sandbox. The solution then analyzes the program’s behavior within this sandbox. Specifically, it analyzes each command, looking for suspicious activity such as self-replication or file deletion. After doing this, the solution categorizes the program as safe or dangerous.

Source: Public Domain Pictures On Pixabay
A good antimalware solution typically combines these methods to detect malicious programs more efficiently. However, heuristic analysis is still subject to some problems.
Potential Problems with Heuristic Analysis
As mentioned earlier, heuristic analysis enables security teams to quickly catch new or modified malicious programs. It does this without relying on an updated signature database. However, it isn’t always correct, as it’s prone to two types of errors: false positives and false negatives.
False Positives
False positive issues emerge when an antimalware solution falsely identifies a program as malicious. While these issues are rare, they can still occur. They often arise in static heuristic analysis, where the analysis might match a portion of a genuine program’s source code with a malicious program. Therefore, security teams must carefully fine-tune the static heuristic analysis process to avoid these errors.
False Negatives
False negatives occur when an antimalware solution fails to identify a malicious program. This problem typically arises in a dynamic heuristic analysis. This could be the case if you encountered a malicious program with algorithms that delayed its actions. To clarify, if this program made its way into your system, it wouldn’t take any actions immediately. This makes it look harmless in your sandbox. As a result, your antimalware solution might flag the program as safe, allowing it to pass through.
So how can you use heuristic analysis to circumvent these pitfalls? Find out in the next section!
How to Run an Effective Heuristic Analysis
To make the detection process more effective, your company should get an antimalware solution incorporating various techniques. Ideally, you should look for a solution that offers the following:
- Multiple detection methods, such as signature-based detection, static heuristic analysis, and dynamic heuristic analysis
- Fine-tuning capabilities so that security professionals can test the program’s tuning and set the appropriate value for each detection method
In the case of fine-tuning, you can decide which method you prioritize for virus detection. You can set a percentage value or weightage to the methods you prefer. For example, you can set signature-based detection to 95%, static analysis to 50%, and dynamic analysis to 75%. The solution will use all three analysis methods when analyzing an unknown program. Each method will then return a score based on whether the method thinks a program is a threat or not. However, the calculation of these scores depends on your initial input percentage. In this example, if static analysis says that a program is a virus, it’ll only have 50% weightage
Overall, having the right antimalware solution will lead to an effective analysis. I think it’s about time we wrapped up now, don’t you think?
Final Words
To conclude, heuristic analysis is invaluable to modern-day cybersecurity efforts. In a rapidly-evolving landscape, this technique helps you to catch existing, ever-changing, and new viruses rapidly and effectively. It can swiftly detect and stop new and old viruses before they cause heavy damage. The technique also offers several benefits, including zero-day threat detection and improved accuracy.
However, it doesn’t come without its problems. The technique is prone to occasional false positives and false negatives. As a result, you must use multiple heuristic methods and fine-tune analysis to suit your requirements.
Do you have more questions about heuristic analysis? Check out the FAQ and Resources sections below!
FAQ
What is the difference between a heuristic virus and a heuristic analysis?
The term “heuristic virus” is an alternative name for the malware known as Heur.Invader. This virus can change your device’s security settings, disable antivirus software, and even install additional malicious software on your computer. Meanwhile, heuristic analysis is a malware detection method based on analyzing a program’s source code behavior. In essence, you can use it to detect a heuristic virus.
What is a heuristic antivirus?
A heuristic antivirus is a software tool that works on the principles of heuristic analysis. This software can identify unknown malware and provide defense against newly-discovered malware. Heuristic antivirus programs employ a variety of scanning methods to achieve these goals. These methods include file analysis, file emulation, and genetic signature identification.
What is the most common heuristic cybersecurity tool?
You can choose from several different tools available in the market today. However, the most accessible one for companies is Fortinet’s FortiGate next-generation firewall (NGFW). This solution employs heuristic analysis to detect malicious activity and eliminate the source program from your system. Furthermore, it uses machine learning (ML) algorithms to identify unusual behavior, which can protect you from zero-day attacks.
What is heuristic software testing?
Heuristic software testing is the testing of software based on past data about probabilities. These focused test methods frequently provide a more thorough study of potential bug locations. Additionally, developers use a variety of heuristics when testing software to help them make decisions and identify issues. Heuristics can also provide helpful suggestions when a tester isn’t sure how to begin the testing process.
What is the difference between the terms “heuristic” and “algorithmic”?
The term “heuristic” refers to a method of problem-solving that leads to a solution through intuition and educated guesses. On the other hand, the term “algorithmic” refers to a detailed collection of instructions used to tackle a problem.
Resources
TechGenix: Newsletters
Subscribe to our newsletters for more quality content.
TechGenix: Article on Apple Macbooks and Viruses
Learn if your Apple Macbook can get a virus.
TechGenix: Article on Types of Malware
Discover the different types of malware and how you can defend against them.
TechGenix: Article on Cyber Threat Hunting
Read more about cyber threat hunting and how you can benefit from it.
TechGenix: Article on Cybersecurity Strategies
Find out how to develop the right cybersecurity strategy for your organization.
TechGenix: Article on the Top Cybercrime Cases in 2022
Check out the top 5 cybercrime cases in 2022.



