The work-from-home culture that saw a big uptick during the pandemic has fueled the growth of remote desktop, productivity, and collaboration tools. According to TrustRadius, the remote desktop traffic increased by 16X during the pandemic, with March to April 2020 alone seeing a 1,587% increase per week. Even as businesses open, this trend is likely to stay relevant, and this is why we will be looking at ways to enhance security while accessing remote systems. Remote Desktop Protocol (RDP) is Microsoft’s proprietary protocol that comes with a graphical user interface. It enables you to connect to and access other devices remotely through the Internet.
This RDP forms the basis for building virtualized solutions and, through them, offers flexibility, extensibility, and cost-value to your organization and customers.
Some of the benefits of using RDP are:
- Enables you to add processing power or capability to existing devices without costly upgrades.
- Deliver applications on different devices including thin clients.
- Ensures data safety and security.
- Reduces configuration time for new devices.
Due to these immense benefits, RDP is widely used and is a part of the Windows operating system.
Let’s briefly see how Windows supports remote desktops.

Working of remote desktop
Windows operating systems come with a built-in Microsoft Remote Desktop, a client application that allows you to connect and access resources and files on remote computers using the Internet.
How does it work?
When you start a remote desktop session, the client (your computer) sends a signal to the host computer via the listening port 3389 requesting permission to connect. In turn, the host asks for login credentials, checks it against its list of preconfigured remote desktop users, and accordingly gives permission.
After you log in, the listening port sends your keyboard strokes and mouse movements to the host computer and gathers and displays the data from the host to your computer. It almost feels like you’re sitting in front of the remote computer and working on it! And all this is because of the back-and-forth communications through the listening port.
However, note that a host allows only one remote connection at a time, and if someone tries to use the host computer or connect to it from another device, the remote connection is lost.
From the above discussion, it’s clear that listening ports are a critical part of remote desktop working.
In some ways, the criticality of listening ports is also a vulnerability as hackers can take over the listening port to connect to remote computers.
Why change the RDP port number?

Microsoft uses the standard port 3389 for all remote connections — and this is no secret. Many times, hackers use the 3389 listening port to connect to remote systems and use a system of automated password guessing to gain access to it. Such attacks are called brute force and password spraying attacks like the one just uncovered by Microsoft.
Undoubtedly, this is a major security vulnerability that can put your remote system at risk.
To overcome this vulnerability, many administrators choose to change the RDP port number from 3389 to any other free port, making it more difficult for hackers to identify the listening port.
Besides protection from hackers, administrators also change the RDP port number to work around firewalls.
For security reasons, some systems’ firewalls are configured to block incoming and outgoing messages to and from port 3389, respectively. This practice is more to prevent hackers from logging in through the port than to cut off remote access.
Again, the workaround for this is to change the port number.
How to change the remote desktop port number on Windows 10
Now that you know why you should change the remote desktop port number, let’s see how you can change it on Windows 10.
There are two ways to change this port number — using Windows registry and PowerShell.
While one is not necessarily better than the other, it’s more of a personal preference. If you know PowerShell and prefer to get things done through codes, that’s your best bet.
Using Windows Registry
Here is a step-by-step guide on how you can change the port number using the Windows Registry.
- Click Windows + R to open the Run dialog box. Type Regedit to open the registry editor.
- Navigate to HKEY_LOCAL_MACHINE\System\CurrentControlSet\Control\Terminal Server\WinStations\RDP-Tcp.
- Look for Port Number.
- Click Edit > Modify.
- Enter the new port number and click OK.
- Close the registry.
- Restart your computer.
- Check if you can connect to the remote computer.
If your remote system is using a firewall, make sure to configure it to allow connections to the new port number.
Using PowerShell
If you’re comfortable using PowerShell commands, this is the easier way to do it.
Use the script below to check the current port being used:
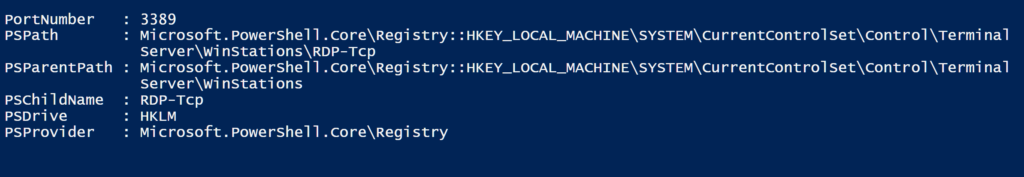
Get-ItemProperty -Path 'HKLM:\SYSTEM\CurrentControlSet\Control\Terminal Server\WinStations\RDP-Tcp' -name "PortNumber"
The screenshot below shows you what the result will look like.
Now, use this PowerShell command to change the port to 3320:
$portvalue = 3320 Set-ItemProperty -Path 'HKLM:\SYSTEM\CurrentControlSet\Control\Terminal Server\WinStations\RDP-Tcp' -name "PortNumber" -Value $portvalue New-NetFirewallRule -DisplayName 'RDPPORTLatest-TCP-In' -Profile 'Public' -Direction Inbound -Action Allow -Protocol TCP -LocalPort $portvalue New-NetFirewallRule -DisplayName 'RDPPORTLatest-UDP-In' -Profile 'Public' -Direction Inbound -Action Allow -Protocol UDP -LocalPort $portvalue
You can choose either of the two methods to change the remote desktop port number on Windows 10.
Besides these two methods, some third-party tools will allow you to change the port number using a simple user interface, and all the complex changes will happen in the background.
A good reason to change the port number
To recap, RDP helps to connect to devices remotely, and all conversations between the two devices happen through listening ports. Specifically, port 3389 is used by default for remote connections.
But hackers can use brute force attacks to connect to remote devices through the default port, so many administrators and security experts prefer to change the port number to make it difficult for hackers to take over remote devices. Sometimes, the change is necessary to work around firewalls as well.
There are two ways to change the port number — using Windows registry and PowerShell code.
So, which of these do you prefer? Have you changed the remote desktop port in any other way? Please share your experience with our readers.
Featured image: Shutterstock



