
You want full control over your cybersecurity, but may find it difficult to investigate and conduct the correct response. One reason is that you may not know when an intrusion is happening. Luckily, you’re not alone and you have systems to help. Many companies use an intrusion detection system (IDS) in this case. If you’re unsure what an IDS is or have no idea how it works, look no further.
In this article, I’ll explain what an IDS is, what it does, how it works, how it detects intrusions, and what benefits it offers. You’ll gain all the information you need to make an informed decision about using IDS in your business.
Let’s get the ball rolling by first defining what an intrusion is.
What Is an Intrusion?
In cybersecurity, an intrusion occurs when an unauthorized entity manages to enter your network or host. That entity can be a threat actor deliberately infiltrating a system with harmful intentions. For example, it might be a malicious hacker doing network reconnaissance or a DDoS attack. It can also be a non-malicious but unauthorized entity that entered the system unintentionally.
An IDS helps prevent both undesirable cases. The system alerts security staff, who can, in turn, take preventive action. That said, before any prevention can take place, the IDS must be able to detect the intrusion.
IDS solutions detect intrusions through one or more detection methods, which we’ll review shortly. First, let’s learn what an IDS is.
What Is an IDS?
An intrusion detection system is a security-oriented appliance or software application. Its main purpose is to detect intrusions, log event data, and send alerts. You can configure an IDS to store the data locally, send it to a logging server, or forward it to a SIEM.
Once your IT administrator or security staff receive the alerts, they can analyze the data and correlate events to determine if a threat exists.
When you purchase an IDS solution, you’ll find it has several components. Let’s go over them one by one.
4 Typical IDS Components
Generally, IDS solutions come with one or more sensors or agents, management servers, database servers, and a console.
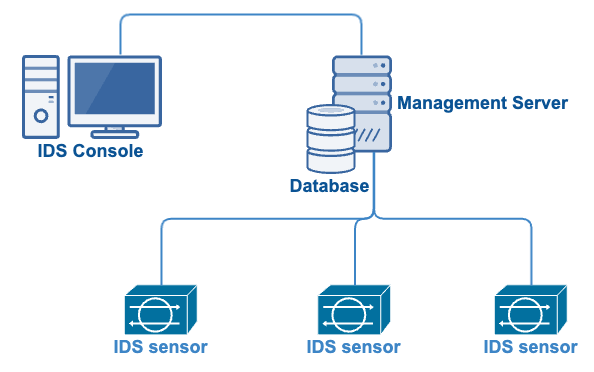
1. IDS Sensor or Agent
An IDS sensor or agent is the part of your IDS you’d deploy on a network or host to monitor their activity. Sensors monitor wired or wireless networks. Agents, on the other hand, monitor endpoints or hosts. Depending on the number of hosts or portions of your network you want to monitor, you may have to deploy one or more sensors or agents.
2. Management Server
An IDS management server is responsible for collecting data from sensors and agents. The management server can also correlate and analyze this data. You’ll find that some IDS solutions have one or more management servers, while others don’t have any at all. Large deployments—such as those in large enterprise networks—usually have multiple management servers. Smaller deployments—such as those in small businesses—usually don’t have management servers.
3. Database Server
An IDS database server is where you’ll store the event data your IDS sensors and agents record. Some IDS tools store data in an embedded database, while others use an external database like MySQL, Oracle, or MS SQL.
4. IDS Console
The IDS console is where you’ll perform administrative or management tasks. How you use your IDS console depends on the vendor’s design. You may use it to configure sensors/agents and/or conduct monitoring and analysis. Basically, some IDS consoles can configure sensors/agents and conduct monitoring and analysis, while others are only capable of configuring sensors/agents.
Now that you know the IDS’s components, let’s learn how the IDS detects intrusions.
How Does an IDS Detect Intrusions?
Older IDS solutions usually relied on a single intrusion detection method—pattern-based detection. Today, IDS solutions combine multiple methods to increase their chances of detecting threats and reducing false positives.
What is pattern-based detection, and what are the other common detection methods? Let’s go over them one by one.
Pattern or Signature-Based Intrusion Detection
Pattern or signature-based intrusion detection looks for network traffic or file patterns and compares them with similar threat-related patterns in their database. For example, this kind of IDS might flag a “root” username in a telnet attempt or a “free games” subject in an email. The method is similar to malware detection in traditional antivirus software—the IDS generates an alert once it finds a match (potential threat).
Anomaly-Based Intrusion Detection
Anomaly-based intrusion detection usually employs machine learning (ML) technology to create a baseline to signify safe or normal network traffic or files. Baseline behaviors for various elements like users, hosts, networks, etc., are initially collected over a period of time. Once that period elapses and the IDS detects a deviation from normal behavior, it interprets the anomaly as a potential threat. In this case, the IDS sends an alert.
Policy-Based Detection
In policy-based detection, the IDS compares traffic or files against pre-configured security policies, much like a firewall. For example, you might have a policy that restricts unencrypted protocols like FTP and HTTP. Someone from your IT/security team may draw up these policies. You may also find your IDS vendor has built them into the system when you purchase it. Once the IDS finds that certain traffic violates the policy, it generates an alert.
An IDS has to capture network or host activity before it can carry out the intrusion detection methods outlined above. Let me explain how an IDS does that.
How Does an IDS Work?
An IDS monitors inbound and/or outbound traffic and detects intrusions through any of the 3 detection methods I mentioned earlier. Once it detects an intrusion, the IDS sends a corresponding alert to your IT administrator or security staff.
Remember that all the IDS does is detect an intrusion, log the event, and send a corresponding alert. It doesn’t act on a threat even if it detects one. It’s up to your IT admin or security staff to confirm the presence of the threat and act on it.
It might help you visualize how an IDS works if I showed you where it monitors traffic. Normally, an IDS, or more specifically, an IDS sensor, is deployed in the following manner:
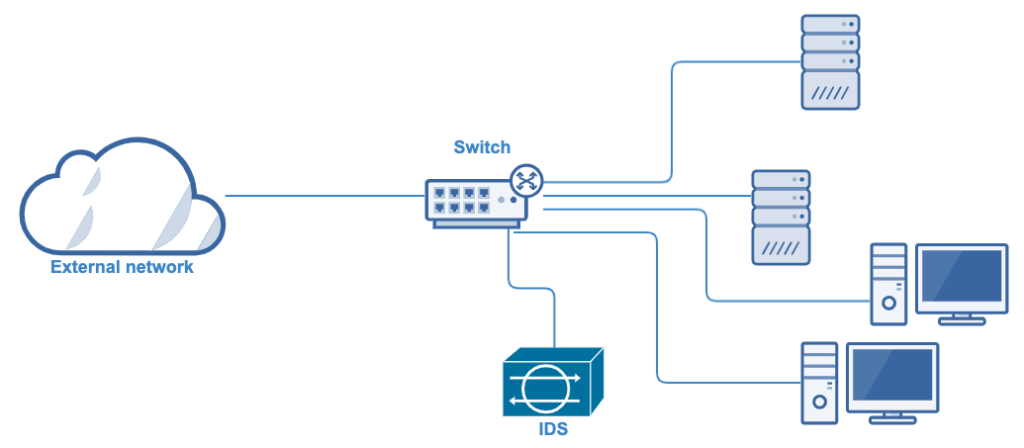
The deployment you see above is an out-of-band or passive mode deployment. You can implement this deployment by connecting the IDS to a spanning port of a switch. A spanning port is a feature in certain switches that copies packets and directs them to a target interface. Here’s an overview of the processes involved.
- Packets coming from the external network arrive at the switch.
- The spanning port of the switch copies the packets and then directs the duplicate packets to the IDS. The rest of the packets move on to their respective destinations.
- As soon as the IDS receives the duplicate packets, it applies its intrusion detection methods to them.
The diagram above only applies to a network-based intrusion detection system (NIDS), arguably the most common IDS type. I’ll talk more about NIDS and other IDS types later. In the meantime, let’s discuss the benefits of using an IDS.
3 Benefits of an IDS
You can use an IDS to detect several threats and alert your security staff, who can take appropriate action. You can gain several other benefits as well. Here are 3 of them.
1. Detects DDoS Attacks
Distributed Denial of Service (DDoS) attacks can incapacitate your network or crash your servers. This attack can cause considerable downtime and prevent users from accessing your services. An IDS can identify a DDoS attack by conducting network behavior analysis and notifying your security staff. Your security staff can then reconfigure your firewall and block packets involved in the attack.
2. Helps Meet Regulatory Compliance Requirements
Some data privacy/protection laws and regulations explicitly or implicitly recommend using IDS/IPS. PCI DSS, for example, requires the use of intrusion detection techniques to detect network intrusions. If you implement an intrusion detection system, you’d be in compliance with such requirements.
3. Detects Network Reconnaissance
Network reconnaissance is the act of running tests against a network to discover potential vulnerabilities. It usually precedes most hacking attempts, as it lets the cybercriminal understand the “lay of the land”. You can employ an IDS as part of a layered defense to identify potential network reconnaissance activities. You’d also have a threat analyst investigate IDS log data indicating such activities. That way, you can catch a hacking attempt before it escalates.
With these benefits in mind, let’s briefly talk about the types of IDS you can use to achieve those benefits.
4 Main Types of Intrusion Detection Systems
You can use 4 main types of IDS. Each IDS type will require slightly different deployment and inspects different data. It’s important you distinguish one from the other so you know what the best fit for your business is.
1. Network-based Intrusion Detection System (NIDS)
You’d deploy NIDS sensors out-of-band (passive mode). They inspect wired network traffic and flag suspicious activity. As most firms use wired networks, this is the most likely IDS type you’ll need before pursuing other options.
2. Wireless Intrusion Detection System (WIDS)
WIDS sensors can be deployed in a variety of options depending on their design. WIDS sensors can be fixed in a strategic location in your facility or installed on mobile devices (laptops, phones, or other specialized mobile devices). You can also build them into a wireless Access Point (AP) or wireless switch. A WIDS inspects suspicious wireless network activity. This is ideal for Bring Your Own Device (BYOD) environments that involve several non-IT-managed mobile devices or for any wireless network
3. Host-based Intrusion Detection System (HIDS)
You’d install HIDS agents on endpoint devices or hosts, like PCs or servers. They inspect application-generated log files, changes to the registry, and system processes. Use this IDS type to detect suspicious activity at your endpoint devices. I recommend you use it after you’ve deployed a NIDS but still require monitoring at your endpoints. You can also use a HIDS if you want additional protection for business-critical hosts.
4. Network Behavior Analysis (NBA) IDS
NBA IDS sensors have an inline deployment. They inspect network packets and flow information that routers and other network devices generate. Most NIDS solutions are susceptible to attacks that involve large volumes of traffic like a DDoS attack. NBA IDS solutions are more suited to mitigate these types of attacks.
| IDS Type | Deployment | What it inspects | Use Case |
| NIDS | Out-of-band (passive mode) | Wired network traffic | Detect suspicious activity in your wired network |
| WIDS | Design dependent: Fixed in strategic locations in your facility Installed on mobile devices Built into a wireless Access Point (AP) Built into a wireless switch | Wireless network traffic | Detect suspicious activity in your wireless network (ideal for BYOD environments) |
| HIDS | Installed on endpoint devices or hosts, like PCs or servers | Application-generated log files Changes to the registry System processes | Detect suspicious activity at your endpoint devices |
| NBA IDS | Deployed inline | Network packets Network flow information generated by routers and other network devices | Mitigate attacks that involve large volumes of traffic like a DDoS |
Final Thoughts
An intrusion detection system is a tool that detects intrusions, logs event data, and sends alerts to IT and security staff. The system uses multiple methods, including pattern or signature-based, anomaly-based, and policy-based detection.
An IDS benefits your business by detecting DDoS attacks and network reconnaissance and helps you to meet regulatory and compliance requirements. NIDS, WIDS, HIDS, and NBA IDS are the 4 main types of intrusion detection systems that have specific use cases and intrusion detection methods.
Have more questions about IDS? Check out the FAQ and Resources sections below.
FAQ
What is the difference between an IDS and an IPS?
An intrusion detection system (IDS) only detects intrusions and then sends alerts. On the other hand, an intrusion prevention system (IPS) detects intrusions and automatically acts on them. For a more detailed discussion, check out this IDS vs IPS article.
What is a DDoS attack?
A Distributed Denial of Service (DDoS) attack aims to incapacitate the target’s network. The attack overwhelms a network’s resources to slow or even shut down the network. When that happens, you can’t access the network’s services. Many intrusion detection systems can identify a DDoS attack and alert security staff, who, in turn, can act on the problem.
Is there another way of deploying an IDS sensor out-of-band?
Yes. Another out-of-band (a.k.a. passive deployment) option is to use a network tap. A network tap is a direct connection between the IDS and the physical network, e.g., fiber optic cable. Similar to spanning ports, a network tap will allow you to view a copy of the network traffic transmitted over the media being tapped.
Can you deploy an IDS inline?
Inline is a deployment option where you place the network device in question along the line of traffic. You usually use this option if you need the device to do something to the traffic. For example, a firewall is placed inline because it has to block unwanted traffic. Advanced IDS solutions that have IPS capabilities can be placed inline because they block packets once they detect an intrusion.
What is Machine Learning?
Machine Learning (ML) is a branch of computer science that uses data and algorithms to mimic how humans learn. Advanced intrusion detection and prevention systems also use ML-based techniques. The techniques detect intrusions by finding anomalies in network traffic or host-based activities.
Resources
TechGenix: Article on WAN Optimization
Discover WAN optimization for SMBs in this introductory guide.
TechGenix: Article on Session Initiation Protocol (SIP)
Delve into the various elements, features, and processes of the SIP protocol.
TechGenix: Article on IPsec
Acquire a deeper understanding of IPsec.
TechGenix: Article on Remote Network Access
Get acquainted with remote network access in this definitive guide.
TechGenix: Guide on Choosing a Small Business Firewall
Master the art of choosing a small business firewall



