In a previous article, we went through the process of creating an Azure Policy to control which Azure Resources could be deployed in a subscription. While the process can be repeated, and several policies can be added, there is a different method that helps organizations when several policies must be created.
It is called initiatives, and basically, it combines several policies in a single unity and it makes easier to manage it. By grouping every Azure Policy that is related in a single initiative simplifies administration and troubleshooting processes.
Creating the first initiative with Azure Policy
In this article, we are going to start creating an initiative to support some of the business requirements, as follows:
- The current cloud solution will use datacenter in East U.S.
- Storage Accounts must be LRS (Standard or Premium).
- VMs being provisioned must be using only two types.
- OMS must be configured on any new VM being provisioned without additional requirements from the operations team.
- As part of the security policy, the company does not want public IP addresses being assigned to resources.
Let’s get started. Logged in the Azure Portal, search for Subscription or click on it on the left side (if available). In the new blade click on the desired subscription (in case you have more than one), and on the main page click on Policies located under Settings section.
Click on Definitions and click on New Initiative. In the new page, the first step (item 1, below) is to select the location where the Azure Policy/initiative will be stored, which is the subscription. Then define a name for the new initiative (item 2), configure the category (item 3), and finally, we can select which definitions we can add to this current initiative.
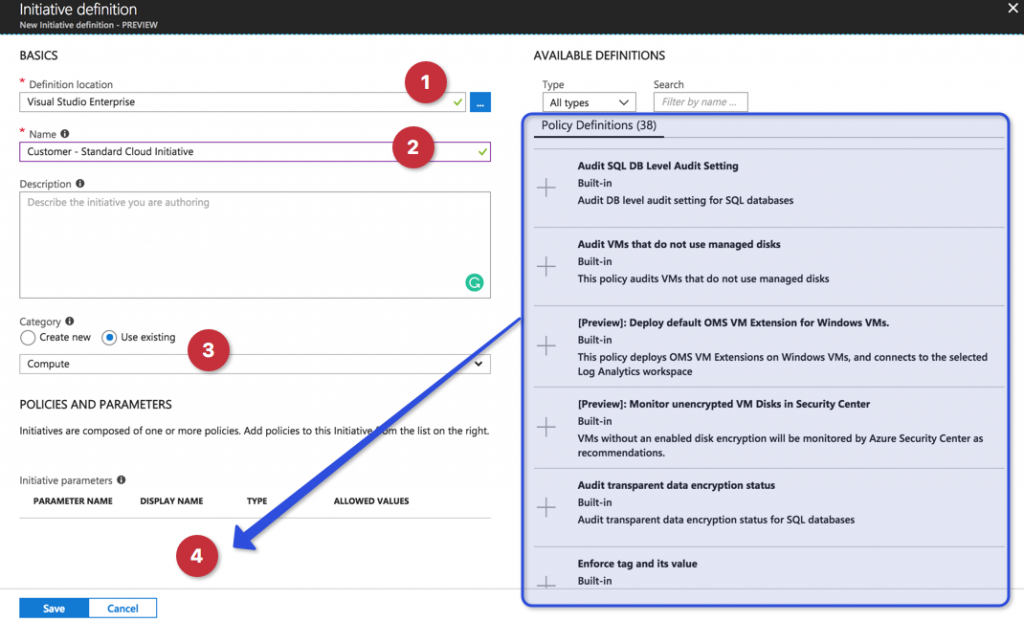
To add an available definition, we have two possible methods: the fastest one is hitting the + button or clicking on the Policy Definition, which will bring a new blade on the right side. In the new blade, we can read a summary of the policy, but we can also check the JSON definitions that are the definition by itself. We can use that code and make changes to create our own definitions. To add the current definition, just hit + Add button.
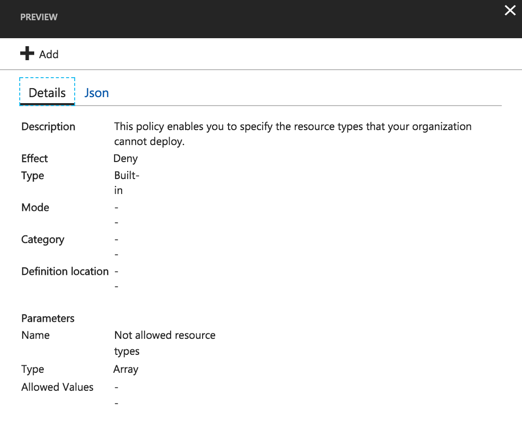
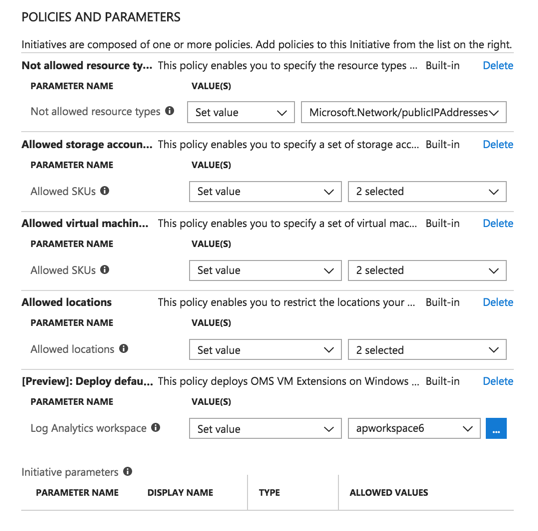
Based on the business requirements we will be adding the following Policy definitions and configure these values:
| Azure Policy Definition | Configured Values |
| Not allowed resource type | Microsoft.Network/publicIPAddresses |
| Allowed storage account SKUs | Premium_LRS Standard_LRS |
| Allowed virtual machine | Standard_D1 Standard_D4 |
| Allowed locations | East U.S. East U.S. 2 |
| [Preview]: Deploy default OMS VM extension for Windows VMs | Apworkspace6 (the current workspace) |
The result of adding each definition can be seen in Policies and Parameters. Using initiatives, we have some advanced options such parameters, where depending on the information that we are trying to use may be really useful. In the current situation, it does not make a lot of sense because we need to select the desired values from a pre-populated list (such as regions, type of VMs, storage, and so forth). After completing all changes, click on Save.
Assigning the new initiative
After saving the definitions we need to assign them to a subscription. Click on Definitions (item 1, below), from the list of existent definitions. Select the one that we have just created (item 2. We can see the number of policies being used in that definition by looking at the Policies column). Click on Assign (item 03).
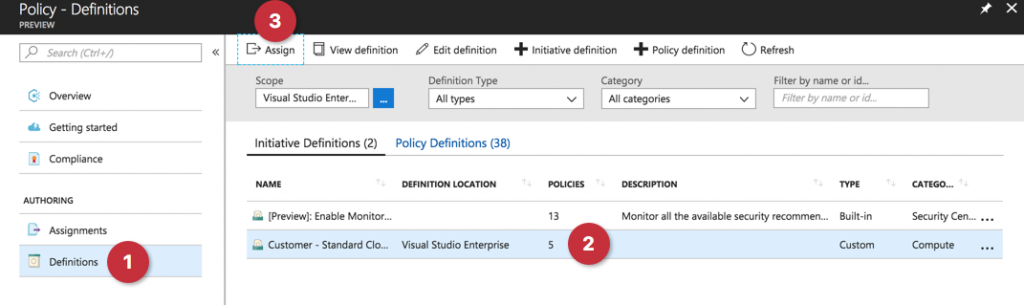
In the new blade, all the information will come filled out. The only definition is the Exclusions where an administrator can select a Resource Group or a specific resource within a Resource Group to be excluded from the current initiative. Click on Assign — it may take up to 30 minutes for the initiative/policies to take place.

Testing the new definition
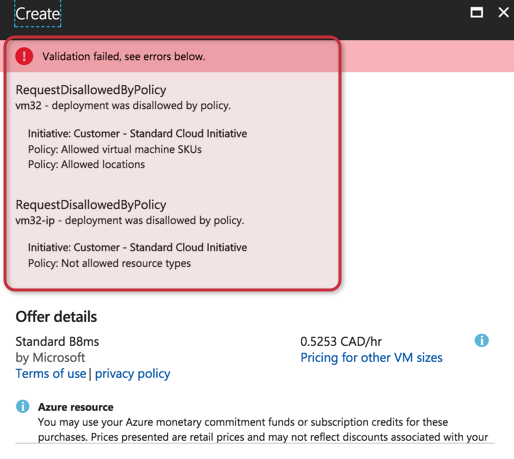
When creating a new VM using a disallowed SKU and location the following error is displayed, informing us which policies within the initiative are the ones blocking the provision of the process.
To evaluate which policy is blocking the deployment, read the error in its entirety. We can see Allowed virtual machine SKUs, which is around the VM type; Allowed Locations, which is related to the region on which the VM was configured to be provided; and last but not least the vm32-ip – deployment was disallowed by policy. If we pay attention, that is related to the public IP, because it has the VM name (in this case vm32) and -ip, which is the default name for new public IP on any new given VM.
Checking initiatives compliance
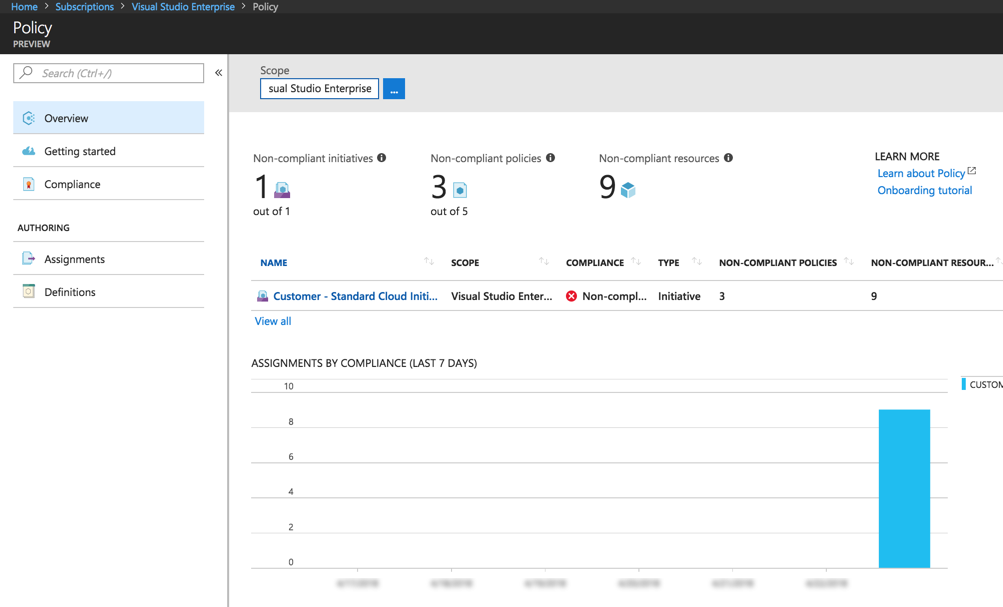
After enabling the initiatives and performing the initial tests, we can go back to the Azure Policy and click on the Overview item. In this page we will have the numbers of noncompliant initiatives, policies, and resources; a list of the current policies and initiatives will be shown as well, and a graph with the assignment by compliance in the last seven days. We can also define the Scope to get more information about policies and initiatives.
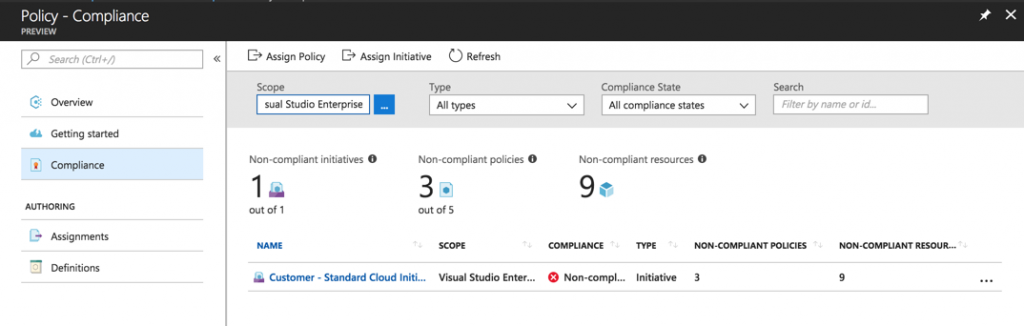
We have a similar view in the Compliance area — the only difference is that we can define a query using scope, type, compliance state and even search for a specific string. As you can see, the initiative that we created has a noncompliant status. Click on it to get more information.
In this page, we can get most of the information about the initiative in a single glance, and that is the most important place when managing initiatives.
At the top, we have View Definition, where we can list all policies currently in use by the initiative and their effect type, which is important when troubleshooting, and from that page, we can actually edit the current initiative and add and remove policies. In Edit Assignment, we can configure the assignment of the initiative (at this point it is more to define an exclusion than anything else).
We will have some information about the initiative and we can configure scopes to update the numbers being displayed below.
We are going to have visual indicators about the compliance state and the number of noncompliant policies, resources, and the events in the last seven days (useful information here because it will generate the numbers for audit, append, deny and deploy).
We have three important tabs: Policies, which will show all the policies, their effect type, the compliance status, and the number of noncompliant resources; non-compliant resources will list all resources that are not compliant with the current initiative; and Events, which will have a list of all events by the user who initiated the action, and it counts the number of each action (deny, audit, append, deploy, and last event).
 Work smarter
Work smarter
As you can see, using Azure Policy Services to create initiatives will make your work life easier. By grouping every related Azure Policy into a single initiative, administration is simplified and troubleshooting any problems that arise should take up less of your valuable time.



