On Friday, October 21, 2016, I celebrated a significant milestone, and like many millions of people before me, planned to upload my software application to GitHub. Sadly, that was not to be, as the GitHub website would not load in the browser. Following a quick Google search, I learned history was in the making as a massive DDoS attack that took down (or at least affected) Twitter, Amazon, and numerous other popular sites. Who was behind the attack is a topic for another day, but here is what we do know: so-called IoT (Internet of Things) devices were the vehicle for enabling these attacks.
What is IoT?

IoT is shorthand for Internet of Things. IoT is a broad term to describe network-connected devices. These devices can be nearly anything, such as security cameras, home thermostats, light bulbs, and much more.
Have you seen one of those commercials where a beautiful person yawns and says (to no one in particular) “I’m ready for bed” and suddenly the lights dim, the curtains close, the temperature goes down, and the security camera turns on? Another typical example is someone sitting on the beach realizing the lights are on at the house. The newly tanned individual puts down a fruity cocktail, picks up a phone, taps a few icons, and poof! Thousands of miles away, the house lights go off.
The way this technology works is through so-called smarthome devices that can directly interact with your network, or even over the Internet. Some of these devices can even work on their own. For example, a security camera can start streaming video if it senses a threat or your DVR can record your favorite show whether you are home or not. Collectively, we call all these smart devices — and innovations that come with them — IoT.
IoT – a $19 Trillion market

According to Cisco, a leading networking equipment and software provider, the market for IoT is around $19 trillion. As I write this, IoT devices at home are just now coming into fashion. That said, IoT is already the norm in the enterprise. IoT is already enormous in business, government, and healthcare. Street lights, manufacturing plants, and indeed, entire buildings, are already using IoT.
A lightbulb with an operating system?
For your lightbulb to dim on command or your thermostat to inform you the house is getting too cold, it needs to communicate over a network. That means even a simple network-connected lightbulb needs an operating system. The operating system can send information to you such as I’m on! You can send it information, such as dim to 50%.
If you have a smart TV, a wireless router, a cable modem, a gaming system, or a home streaming device to binge on Netflix, they are all devices with operating systems. Unlike a computer, these operating systems do not need a massive hard drive, a monitor, and a mouse to work, but they are still operating systems with a lot of capabilities.
I doubt your lightbulb can do much (but just wait–that should change soon!), but your TV, DVR and security cameras already certainly could be hijacked for evil purposes.
Operating systems and malware

Chances are, you or someone you know, was infected with a virus. In the computer industry, we have all sorts of terms that describe viruses, such as trojans, worms, spyware, and others. Very often, the technical industry will refer to malware as a generic term that could mean any type of virus.
Malware can do anything from just be a pain in the neck to doing severe damage like infecting your network, remove necessary files, or allow someone to spy on you through your computer’s camera. That is probably why Mark Zuckerberg’s was met with a lot of unintended press when people saw a picture of his computer with the camera and audio port covered with tape.
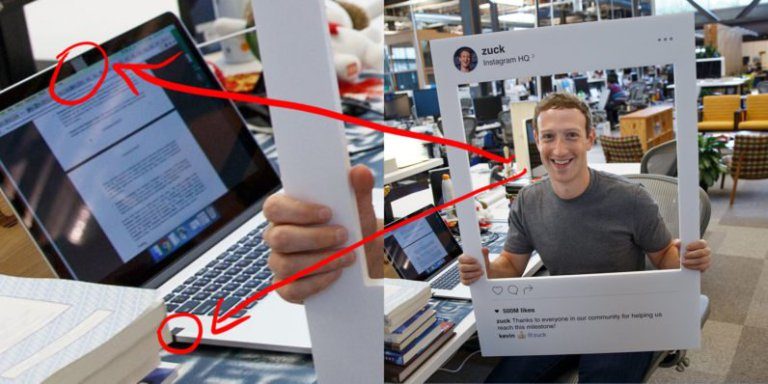
Mark Zuckerberg knows malware could watch or listen to him without his knowing, so those features get taped up.
Malware can certainly wreak havoc on your personal computer, but there are people out there who want nothing more to use all sorts of methods to attack computers. So-called black hat hackers or bad governments create malware because they can make money or get revenge (or more, but that’s a topic for another day).
DDoS (denial of service): A zombie apocalypse
I am not a security expert, so let me explain what I know in layperson terms. Also, I will explain it using zombies.

You are peacefully curled up in a warm blanket watching a cute Pixar movie.
That is how a network should run. Everything is fine, data is safe, and no one is panicking.
Suddenly, there is a rapping at your door. Tentatively, you peek around a curtain and see a zombie making a half-hearted attempt to get into your home. No problem, you have a heavy door, so the zombie will just keep scratching for awhile and go away.
That is the beginnings of a denial of service attack (DDoS). Just like your door, network equipment is designed to take on these types of attacks and should keep out the amateurs.
Bang, bang, bang! Another peak through the curtain and there are dozens, maybe hundreds of zombies wildly throwing their bodies at the door in rapid succession. You hear cracking sounds and watch in horror as the screws come loose in the top latch.
Your security systems are designed to take a beating, but sometimes they are hit so hard, cracks begin to form as the DDoS attack overwhelms.
Crash! The door falls. The zombies are in. You rush to the back of the house, run into the bedroom, throw your bed, your dresser, your lamp, everything, at that door to keep the zombies from getting in.
Just because the hackers knocked down the front door does not necessarily mean they can walk through the threshold. Hackers may be doing this to distract you from their real purpose, to hold your network hostage, or do any number of other things.
About the October 21 DDoS attack
We do not know all the details of the DDoS attack that occurred on October 21, but we do know a few important things. First, the DDoS attack was targeting a company called Dyn, a DNS provider that runs a core part of the Internet. Dyn company operates a service used by a vast majority of the internet called DynDNS.
The Internet creates a unique number for every website (domain). We call those numbers IP addresses. For example, Microsoft has an IP address of 131.107.0.89. What DynDNS does is allow you as a consumer to type microsoft.com into your browser and DynDNS translates that back to 131.107.0.89 for you, rendering the page and ensuring you’re reaching the appropriate address.
As you can imagine, black hat hackers (or evil governments) may want to try and shut down DynDNS. Maybe the plan is to hack Dyn’s network, or maybe the plan is to hack companies like Twitter and Amazon that were affected. Maybe they want to blackmail Dyn, or maybe they thought it would be fun. As of this writing, no one knows why the hackers did what they did, but you can see why attacking Dyn could be very rewarding to nefarious hackers.
How IoT made the attack easy (well, easier)
As you can imagine, a company like Dyn manages mass amounts of traffic every second, so if you want to do some real damage, you can’t just throw a few hundred zombies at their front door. You need a lot of zombies, and they need to bang at the doors really, really fast and for long periods of time.
Rather than employ massive amounts of people to keep attacking DynDNS, the hackers used a piece of Malware called the Mirai botnet. One of the powerful features of Mirai is that it can find IoT devices sitting out there on the Internet, connect to the operating system within, and use it to start attacking another computer.
A huge portion of the Internet was taken down for hours because a bunch of little Internet-connected devices were hacked, turned into zombies sent to attack the DynDNS system. Most security experts agree the bulk of these IoT devices were DVRs and security cameras. Don’t worry; your lightbulb probably wasn’t involved. (But in the future, your HVAC system might be.)
We do not know what the attacker’s intentions were and if they accomplished what they set out to do, but we do know there is a massive unpatched security hole in the IoT space.
You might be wondering how on earth Mirai could even hack the operating systems of these IoT devices. The fact is, most of these IoT devices ship with default usernames and passwords. The end customer may never even know that exists and many of these devices never ask you to change them. Mirai has a database of devices, and when it finds them, it simply logs in with the default username and password and then has control.
A call to action
Back in the day, Microsoft shipped Windows without the need for a password. Later, they secured the product with things like passwords, but [dirty secret], you could just hold down the shift key to bypass all the security. This lack of security and a massive uptick in malware led to a lot of consumers and big enterprise customers to force Microsoft to do better. Bill Gates famously recognized the need for all Microsoft products to be secure by default, announcing the Trustworthy Computing initiative.
The IoT industry sells a vast array of devices in hospitals, homes, manufacturing plants, and secure locations, but there is no one overarching trustworthy computing initiative for devices in the IoT space. That means manufacturers get to decide what the term secure means to them. More and more, we are going to trust IoT devices with our lives (self-driving cars, anyone?) and we need to make sure they are secure.
Until then, do the world a favor. If you have any IoT devices you simply plugged in and forgot about, make sure to create a new password.
Mark Zuckerberg image courtesy facebook.com and solucioneselectronicasrl.com.
All other images courtesy pixabay.com and Shutterstock.



