Image source: Created using Canva
Appearing in 25% of all attacks encountered by respondents of the 2022 VMware Global Incident Response Threat Report, we can no longer ignore the issue of lateral movement. Unless you understand exactly what it is and what it’s all about, this malicious tactic can undermine your network’s security.
I’m here to help you out. In this article, you’ll learn what lateral movement is, the types of attacks that use it, its stages, and more. As always, let’s start with a definition.
What Is Lateral Movement?
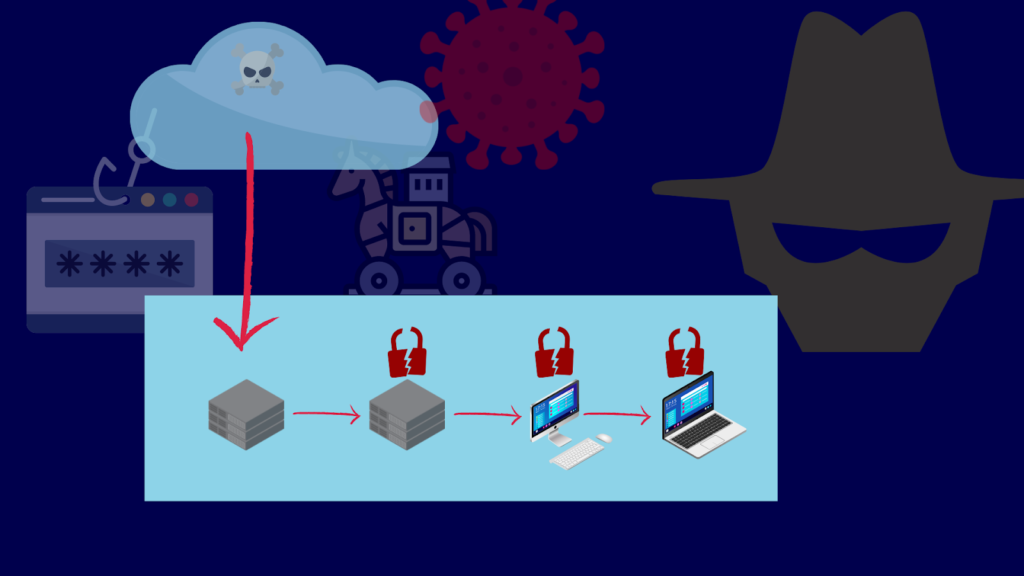
Lateral movement is a tactic that many threat actors use after gaining initial access to your company. To clarify, it involves navigating across your company’s network and breaking into your endpoints like servers, PCs, and others. Threat actors resort to this tactic if the initial compromise isn’t the main objective. Additionally, they can use it if they want to open up alternative entry points in case you somehow managed to uncover the initial compromise.
Highly sophisticated attacks that take days or even months to complete usually involve lateral movement. Lateral movement, a.k.a. east-west movement, often goes undetected and unimpeded. Why is that? Well, in the past, people thought most threats originated from outside the company. Employees and other internal entities in the company cause east-west traffic, so it’s natural for people not to raise suspicions.
This is also why you configure most of your security controls, like your firewall and IDS/IPS, to focus more on north-south traffic, not east-west traffic.
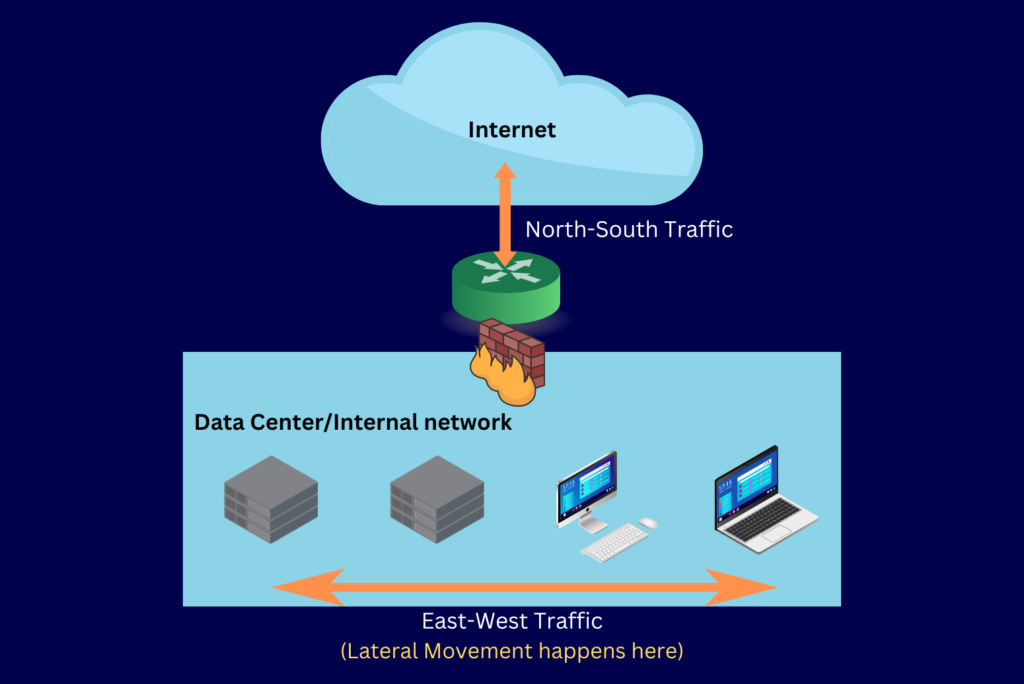
Image source: Created using Canva
Today, however, we know that lateral movement is one of the key tactics employed in modern cyberattacks. Now, before continuing further, it’s important to highlight one technique that cyberattackers use when employing lateral movement called “Living off the Land”.
Living off the Land (LotL)
Although some attackers deploy malware to aid lateral movement, most prefer to “live off the land”. In essence, Living off the Land (LotL) is an evasion technique involving system utilities and tools readily available in a compromised endpoint. Let’s say, for example, the compromised system is a Windows host. The attacker may use PowerShell, regsvr32.exe, WMI, and other binaries found in a typical Windows installation.
This strategy aims to be as stealthy as possible. This is because known malware can trigger signature-based antivirus solutions. Using built-in system tools, an attacker can run a query or access another endpoint without raising the alarm.
As a result, many security solutions and analysts will dismiss those actions as part of normal operations.
Now, let’s examine what attacks use lateral movement to their advantage.
Types of Cyberattacks That Use Lateral Movement
Any cyberattack that benefits from having a great number of compromised systems uses lateral movement. Here are some cyberattacks that employ this tactic.
Ransomware Attacks
Ransomware is malware that encrypts files and displays a note demanding a ransom payment. To increase their chances of getting paid, ransomware operators try to infect as many IT assets as possible. Additionally, some ransomware types attack backups. Cyberattackers design ransomware variants to move laterally and self-propagate to capture multiple assets.
Advanced Persistent Threats (APTs)
APTs are highly sophisticated attacks often backed by nation-states. Designed to conduct extensive espionage, data theft, or sabotage, they’re nasty, to say the least. For this reason, APT operators want to keep the attack hidden for as long as possible. A typical attack can remain undetected for weeks or even months. Throughout the attack, APT operators will conduct a substantial amount of lateral movement and break into multiple systems.
Botnet Infections
Botnets are networks of zombified devices like servers, PCs, and Internet of Things (IoT) devices. In essence, once infected with botnet malware, these devices will be at the beck and call of the botnet operators. Cyberattackers can design botnets to, for instance, carry out DDoS attacks. A botnet’s strength is highly dependent on its size. As such, botnet operators try to trap as many devices in a network as possible. Lateral movement helps in achieving that goal.
To gain a deeper understanding of lateral movement, it might help to know how threat actors go about it. Let’s now discuss the 3 most common stages involved in employing this tactic.
3 Common Stages of Lateral Movement
Lateral movement occurs after the initial compromise, which a cyberattacker achieves through phishing attacks, malware infections, and other methods. After the initial compromise, an attacker will perform an east-west movement in 3 main stages. Let’s look at each stage in more detail.
1. Reconnaissance
Before anything else, your attacker will want to get the lay of the land. In this stage, your attacker’s objective is to learn more about your company, hosts, network, security tools, etc. As a result, the information they gather will help your attacker strategize for subsequent stages. For instance, your attacker can choose the most suitable method for stealing login credentials by knowing your weaknesses.
2. Credential Theft and Privilege Escalation
At this juncture, the objective of your attacker will be to obtain valid login credentials like usernames and passwords. Your attacker will target accounts with higher privileges than the account it currently has. They can achieve this through several methods, including Pass-the-Hash attacks, Man-in-the-Middle (MITM) attacks, and social engineering. Some attackers also use tools specially designed for stealing passwords from keystrokes and memory, like keyloggers and Mimikatz.
3. Lateral Movement and Gaining Access
Once your attacker obtains login credentials for an endpoint other than the one it’s currently logged into, it can move on to that endpoint. It’s at this stage that your attacker will start to move laterally. Upon gaining access to that next endpoint, your attacker will go through the same set of processes and stages. They will keep repeating these actions until they breach their main target endpoint and achieve their ultimate objective.
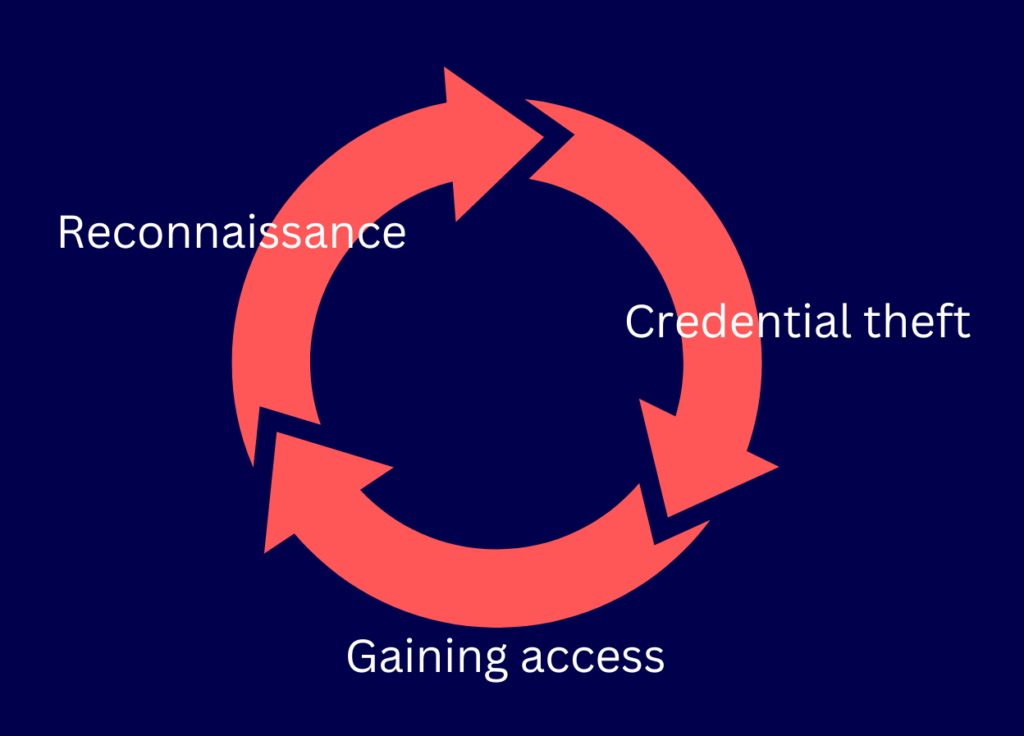
Image source: Created using Canva
Alright, so we know that lateral movement is stealthy. How can you detect it? Let’s find out.
Best Practices for Detecting Lateral Movement
Lateral movement often manages to evade detection for two reasons. The first reason is that organizations can simply lack security controls for east-west traffic. Secondly, lateral movement often involves stolen legitimate accounts.
That said, you can use some best practices to help you detect this deadly tactic.
Update Antivirus/Antimalware Software
If a known malware carries out lateral movement, you should be able to detect this movement using robust antimalware tools. However, you’ll need to update these tools regularly. One reason is that you don’t want these tools to get compromised. Another reason is that some antimalware use malware signatures for detection.
Every time an antimalware vendor discovers a new malware, the vendor creates a signature for it. Thus, if you want to be sure your antivirus software can detect the latest network-hopping malware, patch regularly!
Deploy Solutions That Use Behavioral Analytics
As you know, lateral movement often involves stealing credentials associated with legitimate accounts. Some of those accounts even have administrative privileges. As such, lateral movement is hard to detect. Most security tools can’t even distinguish malicious intent that passes off as routinary action conducted by a legitimate account.
That said, a malicious action can still exhibit subtle yet suspicious behavior. This behavior can trigger tools equipped with behavior analytics. If you deploy a User and Entity Behavior Analytics (UEBA) solution, you can have a leg up against threats that carry out an east-west movement.
Detection is good, but prevention is better. Fortunately for you, I’ll now discuss the best practices for preventing lateral movement.
Best Practices for Preventing Lateral Movement
You can prevent lateral movement in several ways. However, keep in mind that no single best practice can completely prevent lateral movement. As always, it’s best to take a multi-layered defense strategy and apply multiple best practices for optimal results.
Implement Patch Management
Aside from using stolen credentials, many threat actors perform an east-west movement by exploiting a system’s known vulnerabilities. Cyberattackers usually share these vulnerabilities in hacking forums on the dark web. That said, software updates usually include security patches that fix known vulnerabilities.
So if you patch regularly, you can counter threat actors that move laterally through vulnerability exploits. However, remember that knowing or finding each vulnerability is not easy. You’ll need to employ more advanced tactics like penetration testing for the more obscure ones.
Perform Penetration Testing or Hire an Ethical Hacker to Do It for You
Some vulnerabilities are only evident to people who think like an attacker. Since you’re likely not a hacker, hiring ethical hackers to perform penetration testing is one option. Essentially, this is a tactic that cybersecurity professionals employ, which involves the same techniques used by threat actors.
Penetration tests can help you discover vulnerabilities undetectable by regular vulnerability scanners and other security tools. You can then fix those vulnerabilities and render them ineffective for lateral movement.
Institute Zero Trust Security
As mentioned earlier, the misperception that threats mainly originate from outside the network is why you often see an unequal application of security controls. Consequently, east-west traffic controls are usually much more lenient than north-south traffic controls. However, you can correct this inequality by adopting zero trust security.
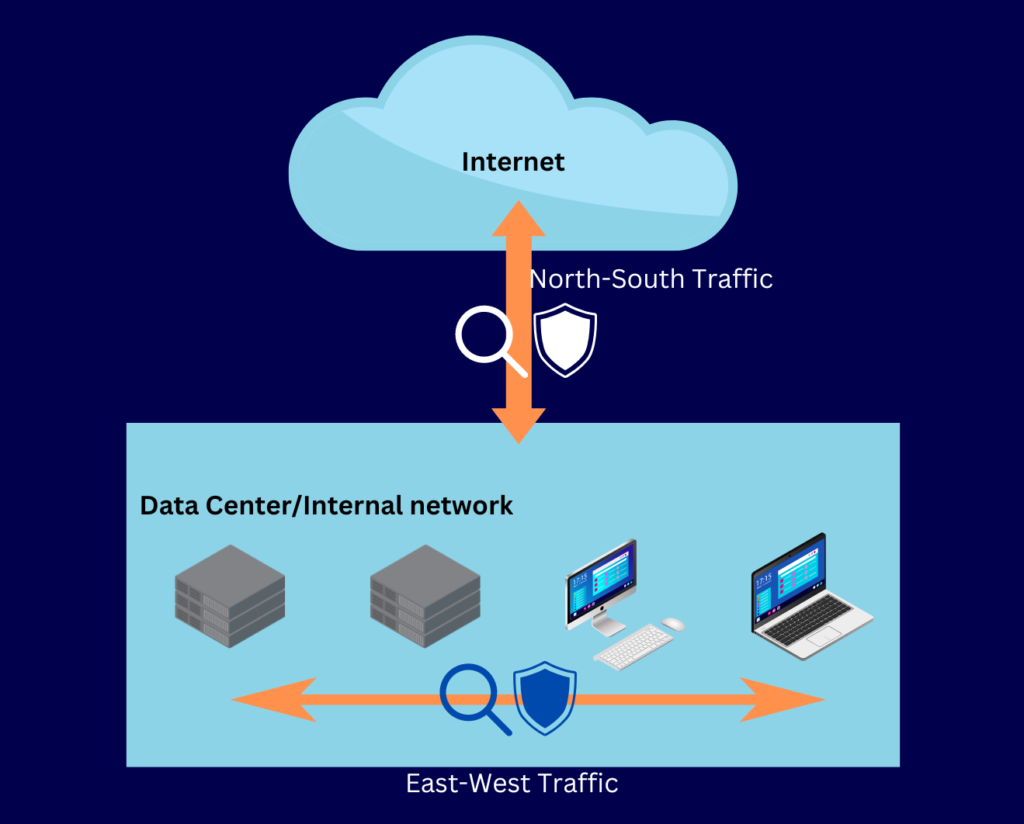
Image source: Created using Canva
Zero trust security is a cybersecurity philosophy that considers all users, devices, and other entities untrustworthy by default. This means that north-south and east-west traffic should receive the same restrictions. Moreover, zero trust incorporates several stringent security best practices, including the principle of least privilege, strong authentication, and others. Adopting this philosophy will make it difficult for threat actors to move across the network and carry out privilege escalation.
Establish Endpoint Security
It’s not enough to monitor and secure east-west traffic. We know that lateral movement also involves compromising endpoints like servers, PCs, laptops, switches, IoT devices, etc. For this reason, it’s important to establish endpoint security as well.
Endpoint security is the practice of securing endpoints through a combination of threat prevention, detection, and response mechanisms. The most basic form of endpoint security is using an antivirus. You can employ an EDR, MDR, or XDR solution for even better protection. Essentially, these solutions offer comprehensive detection and response capabilities for endpoints and, in the case of MDRs and XDRs, other IT assets.
Apply Network Segmentation
A network where all endpoints can freely communicate with one another is the perfect environment for lateral movement. As long as the attacker has all the right privileges, hopping from one endpoint to another should be fairly easy. The question is—do all your endpoints need to communicate with one another?
If not, you should apply network segmentation. Network segmentation is the practice of splitting up your network into segments. For example, you can create segments for each business unit. Another strategy is to isolate critical IT assets from non-critical systems. Your goal is to contain east-west movement to the affected segment in the event of an attack on the system.
Alright. Time to wrap things up.
Final Words
Most sophisticated cyberattacks like ransomware and APTs involve lateral movement. In essence, it’s a tactic that allows threat actors to navigate deep into your network, capture as many endpoints as possible, and establish alternative entry points. It consists of 3 main stages: reconnaissance, credential theft, and gaining access.
To improve your ability to detect lateral movement, you must update your antimalware and deploy behavior analytics solutions. Moreover, you can prevent lateral movement by implementing patch management, performing penetration tests, instituting zero trust, establishing endpoint security, and applying network segmentation.
Do you have more questions about lateral movement? Check out the FAQ and Resources sections below!
FAQ
What type of solution should I look for if I want to detect lateral movement through behavior analytics?
User and Entity Behavior Analytics (UEBA) is the class of security solutions specializing in detecting threats using behavior analytics. Some solutions specialize in UEBA, while others, like IDS/IPS and SIEM solutions, have this capability built-in.
How do I mitigate the risk of lateral movement in a data center?
You can apply several security controls in a data center that can help prevent lateral movement. Basically, you can deploy firewalls, IDS/IPS solutions, multi-factor authentication, and antimalware solutions, to name a few. Our article on data center security has a more detailed discussion on the subject.
What are my other options against MITM attacks aside from HTTPS, SFTP, and FTPS?
You can use a virtual private network (VPN). In essence, a VPN encrypts your connections, which include HTTPS, SFTP, FTPS, and other encrypted protocols. Moreover, a VPN protects applications that don’t use encrypted network protocols which is a big advantage. Refer to this article on Internet Protocol Security (IPsec) VPN which offers a great description of this.
What is a DDoS attack?
A Distributed Denial-of-Service (DDoS) attack overwhelms a network’s resources to slow or even shut it down. Once this attack overwhelms the network, users can no longer access its services. Many IPS solutions can identify a DDoS attack and block traffic associated with the attack.
Can firewalls help secure IoT devices?
Yes. You have certain types of firewalls that can address security issues involving IoT devices. Specifically, certain next-generation firewalls (NGFWs) have built-in features that enable IT admins to build firewall rules based on IoT traffic.
Resources
TechGenix: Guide on Choosing a Small Business Firewall
Learn how to choose a small business firewall.
TechGenix: Article on DNS Hijacking
Find out how to protect yourself from DNS hijacking.
TechGenix: Article on Proxy Servers
Discover what proxy servers are and their role in cybersecurity.
TechGenix: Article on Firewall Best Practices
Use these firewall best practices to bolster your data center’s defenses.
TechGenix: Introductory Guide to Cloud Network Security
Learn more about the basic concepts of cloud network security.



