
Source: Unsplash
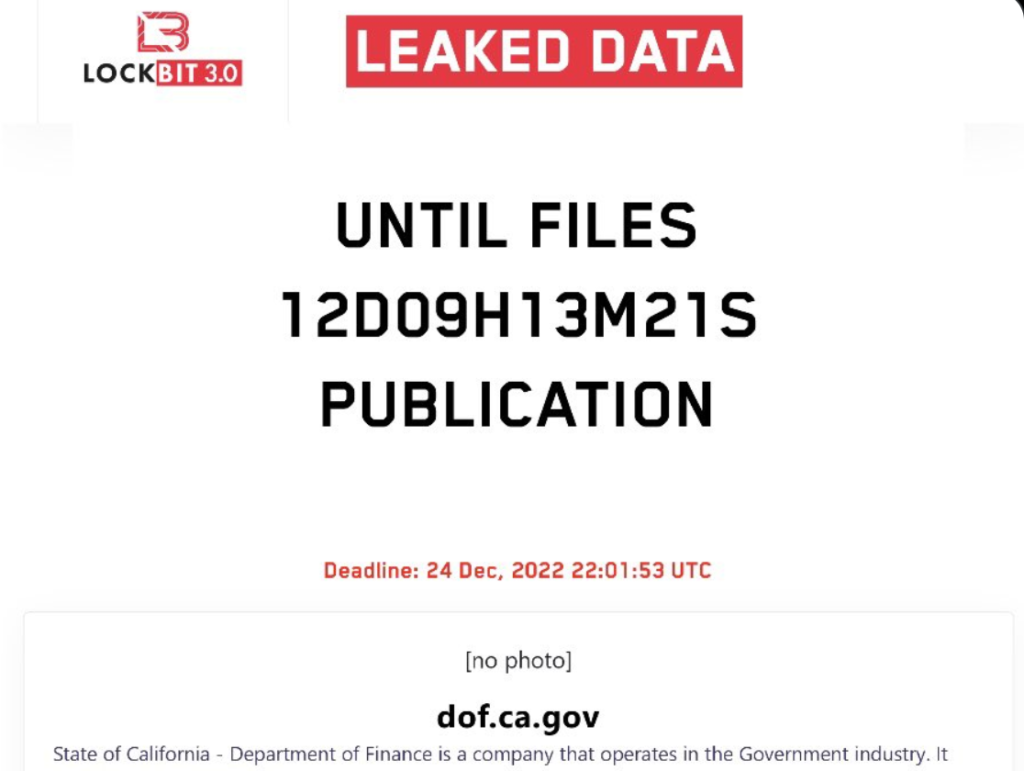
LockBit has claimed to have stolen 76 gigabytes worth of confidential data, including financial and IT records, certifications, and legal documents, in an attack on California’s Department of Finance. While officials aren’t divulging much information, the LockBit group gave the department until December 24 to meet its demands. Or else, it threatened to leak the department’s stolen information on the darknet.
LockBit is both a cybercrime group and a ransomware technology. LockBit’s ransomware is available to anybody who wants to purchase the technology and launch their attacks. A black-hat technology with support on darknet forums, it also has a bug bounty program. LockBit 3.0, also known as LockBit Black, is its most recent ransomware edition.
LockBit Holds Data for Ransom
Source: Twitter
California Governor’s Office of Emergency Services (CAL-OES)—one of the departments investigating the matter—did confirm “no state funds have been compromised,” but refrained from commenting further due to the ongoing investigation. The department further claims to have proactively identified the threat.
LockBit posted several screenshots of old budgetary documents, contracts, and file directories on darknet forums. These files are anything but earth-shattering data and certainly not worth the millions of dollars the group is demanding.
State departments haven’t been LockBit’s only targets so far. In August 2021, LockBit ransomware compromised both Accenture and Gigabyte. More recently, it claimed to have breached Continental AG. Between 2021 and 2022, the European Union Agency for Cybersecurity (ENISA) identified LockBit as one of the most prolific active ransomware groups out there. It has also recently exploited Windows Defender to launch Cobalt Strikes against its targets.
How the LockBit Ransomware Works
Source: Unsplash
The LockBit ransomware penetrates networks and encrypts computers, holding the data within for ransom. LockBit targets widely available protocols, such as Server Message Block (SMB) and Windows PowerShell, and encrypts Windows domains with Active Directory Group Policy.
Groups using LockBit gain remote access to servers by compromising user credentials, possibly through phishing. Once they establish a foothold, it’s a matter of hours before they compromise the entire network by identifying mission-critical systems like NAS devices, backup servers, and domain controllers.
To aid its affiliates, LockBit provides a main control panel for creating ransomware variants, managing victims, and posting blogs. Moreover, it compiles statistics, so attackers can build upon that data and customize their tactics.
LockBit ransomware attacks were originally known as “.abcd Virus”. The group has affiliations with Maze, RagnarLocker, and SunCrypt. Moreover, it’s an extension of the LockerGoga and MegaCortex malware families.
Protection against Dangerous Ransomware
Source: Pexels
Globally, extortions account for only 20% of the total damages due to ransomware. The rest of the damage occurs due to productivity losses, cleanup costs, and negative PR. To protect against ransomware and the damages they cause, businesses need to:
- Use passkeys instead of passwords wherever possible
- Activate multi-factor authentication for all applications
- Automatically scan and patch vulnerabilities
- Limit user permissions and delete inactive accounts
- Ensure system configurations follow all security procedures
- Have system-wide backups in case of file encryption or deletion by ransomware
- Use a powerful network protection tool with email filtering, scanning, and antivirus capabilities
- Maintain a complete enterprise-level cybersecurity solution
These techniques will protect companies against ransomware, like LockBit, and malware toolkits, actively searching for network vulnerabilities. Businesses with proactive cybersecurity policies can prevent such attacks.
Moreover, state authorities need to do their part as well. Californian authorities may have acted proactively in identifying the threat, but they need to go further and arrest the ringleaders. Earlier this month, a Russian-Canadian was arrested in relation to the global LockBit ransomware operation and will soon be extradited to the US.
LockBit 3.0 — Far Deadlier than Predecessors
LockBit has evolved since 2019. The latest version, LockBit 3.0, which arrived in June 2022, is much harder to defend against because it requires a password to scan each instance. It’s impenetrable to analysis, as it uses kernel-level Windows functions.
A LockBit attack goes something like this:
- LockBit 3.0 infects a victim’s device, encrypts files, and appends the extension, HLjkNskOq
- A command-line argument key (“-pass”) carries out the encryption
- LockBit 3.0 creates various threads to perform multiple tasks simultaneously (increasing encryption speed)
- LockBit 3.0 deletes certain services to make encryption and exfiltration easier
- An API harbors service control manager database access
- Desktop wallpaper changes (alerting victims to the attack)
Despite its sophistication, companies can avoid the threat LockBit and other actors similar to it pose by implementing two-factor authentication (2FA) and password-protecting RDP connections. Since cybercriminals seek easy targets with vulnerabilities, a proactive approach to network security is the only real way to stay safe.



