If you missed the other parts in this article series please go to
- A Microsoft PKI Quick Guide – Part 1: Planning
- A Microsoft PKI Quick Guide – Part 2: Design
- A Microsoft PKI Quick Guide – Part 3: Installation
We have now gotten to our last article in our Microsoft PKI quick guide series. In the previous articles we gave you a quick overview on how to prepare, plan and design your Microsoft PKI. We also got a bit more technical, and showed you how to install a PKI based on Microsoft Certificate Services in Windows Server 2003. In this final article, we’ll give you a quick overview on how to maintain and troubleshoot your PKI using some basic, but very valuable tools.
The toolbox
One of the things that will be of great value to you and your PKI, is a toolbox containing the right tools. This will help you maintain a stable PKI and help you solve problems quickly and painlessly. However this is not an easy task, since there aren’t too many tools available, therefore we’ll just have to make the best of what we have. Here are your options for your Microsoft PKI toolbox (in no particular order):
- Certificate Services (certsrv.msc) – This MMC contains the primary functions you’ll need to configure and maintain your PKI.
- Certificate Templates (certtmpl.msc) – This MMC is used to maintain and secure certificate templates.
- Certificate Manager (certmgr.msc) – This MMC is used to control the certificates that are installed on a computer or the current user.
- Certutil.exe – A command line based certificate utility that does the same as the Certificate Services MMC plus a whole lot more.
- Event Viewer (Eventvwr.msc) – The Event Viewer MMC is not a typo. This tool is very important when troubleshooting your PKI, as you will soon learn.
- Enterprise PKI tools (PKIview.msc) – An MMC based PKI health tool, that you should make your best new friend.
- Capimon.exe – Allows an administrator to monitor a security application’s CryptoAPI calls and its results.
All of these tools all contribute to a well functioning PKI, but they can also reveal some very important information that will help you troubleshoot your PKI. And the best way to troubleshoot your PKI is by using a structured process. Here’s one approach:
- Always start your troubleshooting by checking the event logs. This may seem obvious, but almost all PKI related errors will be logged to the event logs. Even though you can display the error messages from the various programs such as the Certificate Services MMC, the event log is by far the easiest way to read and debug PKI related errors.
- Use the PKIview.msc tools to get a quick overview of the health of your PKI. PKIview.msc will normally reveal some of the most common errors including a missing or outdated CRL or an expired CA certificate. If everything seems ok from this tool, you can move on and concentrate on specific certificate related issues, such as security settings on certificate templates, etc.
- If the error still isn’t obvious or difficult to troubleshoot in the previous steps, then seek help from our resource list at the end of this article, or look for solutions via support.microsoft.com, newsgroups or forums.
Another thing that can be of great help is to have a checklist to follow after installation and during maintenance. Here’s one example to get you started:
- How is the availability of your PKI and your root certificates?
- Is the CRL available?
- Are the issued certificates working properly?
- Are the infrastructure components or applications that rely on certificates from your PKI working properly?
- How is the performance on systems that use certificates from your PKI?
- Are there any error messages related to certificates installed on a computer?
Let’s move on and take a quick look at a few of the utilities from our toolbox and how they can actually make life easier with respect to your PKI.
Certificate Services and Certificates Templates MMC Snap-in
The Certificate Services MMC Snap-in (certsrv.msc) is your primary PKI administrative console. You should try to spend some time with this MMC Snap-in and get familiar with the tool, since it gives you a deeper insight into the world of a Microsoft based PKI. With this snap-in, you’ll get a better understanding of what AIA, CDP, V2 certificate templates, etc., means and how they relate to some of the areas we covered in the previous PKI articles. The built-in help is also of great value, and even contains a small best-practice section (like many of the other built-in Windows Server 2003 help files). Most of the problems with a Microsoft based PKI are usually related to permission problems when a certificate is being issued or the availability of the CRL. So let’s look at a couple of examples where this tool can be of great help during troubleshooting of your PKI.
One of the most common errors you’ll see with respect to a PKI is an outdated or inaccessible CRL. The quick way is to publish the CRL from the Certificate Services MMC, but this can also be scripted from the command line as you’ll soon learn.
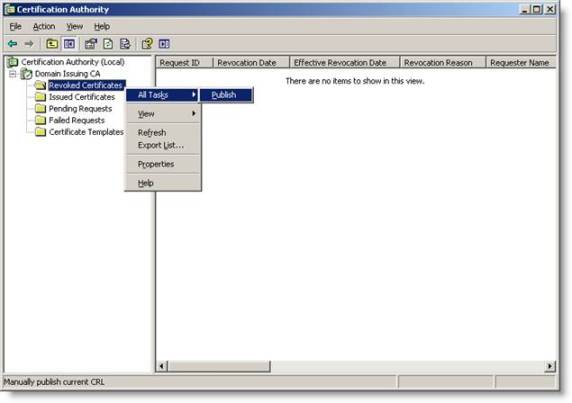
Figure 1: Publishing the CRL
You should make it a habit to occasionally check if a certificate has been issued or not, by checking the “Failed Requests” submenu on the left pane of the MMC console. From this menu you’ll be able to investigate why there was an error associated with a failed attempt to issue a certificate. Often this error will be difficult to read from the “Failed Request” section. The good part is that the same error will be added to the application log. And since it’s easier to copy an event log entry from Event Viewer than the Certificate Services MMC, this should be the preferred method to check for any PKI related errors, unless you of course you use some kind of delegated administration and customize your MMCs.
Another common error is incorrect security settings on certificate templates. You can the modify the security of certificate templates from the Certificate Services MMC by either right-clicking Certificate Templates and select Manage or start a new MMC where you add the Certificate Templates (certtmpl.msc) snap-in. Either way, from the Certificate Templates MMC, you select the properties of the certificate template you want to use. You then click the Security tab and make sure that the correct security group is allowed to receive a certificate, by enabling “Read” and “Enroll” permissions for that group.

Figure 2: Check if a certificate template has the correct security settings
PKIview.msc
One of the most valuable troubleshooting tools for your Microsoft PKI is PKIview.msc which is available in the Windows Server 2003 Resource Kit. With this tool, you can check the status of your PKI. When you start the graphical tool, you’ll see various indicators that will give you the updated health status of your PKI. A green checkmark indicates that everything is alright with your PKI. However a yellow warning sign indicates that a certificate or Certificate Revocation List (CRL) is close to expiration. If you see red errors, then it would normally indicate that CRL or Authority Information Access (AIA) locations cannot be reached. Red errors may also indicate that a CA is not trusted. If this is the case, then right click the error and click “Copy URL”. Paste the URL into a web browser, if it’s an HTTP location that can’t be reached, or use a tool like adsiedit.msc from Windows Support Tools to check whether the published CDP location actually contains the revocation or trusts list in error.
This tool is capable of much more, and at a minimum, you should run this tool once a week, to ensure the health of your PKI. The details in the errors will quickly indicate where exactly the error is, however it will not give you the exact solution. Here you still need to do some detective work, using some of the other tools mentioned in the toolbox list earlier in this article or Google for the event shown in PKIview.msc.
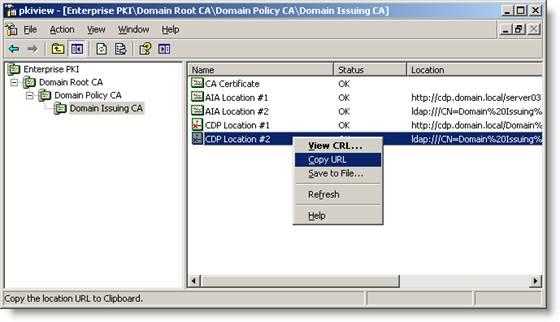
Figure 3: PKIview.msc is a great troubleshooting tool
Certutil.exe
The master of all Microsoft PKI tools is without any doubt Certutil.exe. This powerful command-line utility supersedes the resource kit tool from Windows 2000 called Dsstore.exe. There are several advantages using Certutil.exe. First of all, it’s easily scriptable and is capable of much more, both with respect to configuration, documentation and troubleshooting, compared to all the other tools in our PKI toolbox. Another advantage not mentioned very often, is that it can run many of the data-gathering features as a regular user. This is actually a great feature for troubleshooting certificate problems, without compromising the security of your PKI. The reason why troubleshooting your PKI with Certutil.exe will not compromise the security of your PKI is because many of the core configuration options aren’t available unless you have the necessary permissions.
Another advantage of Certutil.exe is the built-in change-management feature (sort of). Many of the Certificates Services settings are stored in Windows registry under:
“My Computer\HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\CertSvc”
Whenever you make changes to your PKI using the “certutil -setreg” parameter, the utility will display the old setting first followed by the new setting afterwards.
We’re not going to walk through all the different features and options for Certutil.exe, since there are too many. However enter “Certutil -?” to get a complete overview. A little hint is that the Windows Server 2003 version of Certutil.exe can be ported to Windows Vista, Windows XP and Windows 2000. All you need to do is to copy Certutil.exe, Certcli.dll and Certadm.dll to a location on your Windows Vista, XP or Windows 2000 machine. There’s no need to register any DLL file, etc. Just run the command line utility from that location.
Conclusion
This may seem obvious and in many ways it is, but by using a structured troubleshooting process, you’ll be able to quickly locate and pinpoint exactly where your PKI is misbehaving. We’ve tried to give you a quick overview and summarize the tools and utilities you have at your service and we have documented a few examples on how you can use some of the tools. But there are many other options available, depending on how you mix and match the tools. The samples shown in this article are suggestions that merely serve as inspiration. In the external resources list below, you’ll find links to valuable whitepapers that will cover a lot more troubleshooting options. With all the resources mentioned in this article, you’ll be well on your way to keep you PKI healthy and running.
External resources
This article series is done with the help from a lot of great resources. All the excellent Microsoft PKI articles are collected in one place which you can find on the Microsoft PKI Web Portal
http://www.microsoft.com/pki
Want to see how Microsoft does PKI, then check out the IT Showcase -Deploying PKI Inside Microsoft
http://www.microsoft.com/technet/itsolutions/msit/security/deppkiin.mspx
And this is a great book – Microsoft Windows Server 2003 PKI and Certificate Security
http://www.microsoft.com/mspress/books/6745.asp
If you missed the other parts in this article series please go to



