
Your Wi-Fi password, also known as your network security key, does more than just allow authorized users access to your Wi-Fi. It also plays a role in encrypting data. I bet you didn’t know that. You probably also didn’t know you can get your Wi-Fi password from connected endpoint devices. Don’t worry if you’ve forgotten it!
In this article, you’ll learn about all the security functions of your network security key. I’ll also show you where to find that key on connected Windows, Mac, Android, and iOS devices.
What Is a Network Security Key?
A network security key is simply what most people call a Wi-Fi password or passphrase. It’s what you enter on your device when you connect to a wireless router or access point (AP). Network security keys help admins restrict access to your Wi-Fi network to authorized users only.
Some wireless router/AP manufacturers use the labels ‘WEP key’, ‘WPA key’, or ‘WPA2 key’ on their devices. These are all references to the network security key. I’ll talk about WEP, WPA, and WPA2 in more detail later. I’ll also be using these terms interchangeably throughout this article. In the meantime, let’s talk about what a network security key does.
What Does a Network Security Key Do?
A network security key has 2 major functions, both of which enforce Wi-Fi security.
1. Helps Provide Access Control to the Wireless Network
A network security key provides access control, to ensure the user has authorization to join your Wi-Fi network. If the password a user submits doesn’t match the correct value, it could mean the user doesn’t have access privileges. For this reason, that user’s device won’t connect. This will also help you cut the risk of unauthorized users gaining access to your wireless network.
2. Helps Facilitate Data-in-Motion Encryption
The second function of a network security key has to do with data-in-motion encryption. The network security key generates the cryptographic keys for encrypting/decrypting data exchanges between the client device and the wireless router/AP. This data exchange encryption can mitigate the risk of man-in-the-middle attacks. Simply put, it can protect the data you send and receive over the wireless network from eavesdroppers. How you use the network security key depends on the wireless network security protocol, i.e., WEP, WPA, WPA2. Let’s discuss those now.
Different Types of Network Security Keys
Network security keys come in different types. I’ll show you what each of them does, so you can learn the differences.
WEP Key
A WEP key is the network security key used in Wired Equivalent Privacy (WEP). This protocol was most common in the ‘90s and has now become obsolete. It may consist of either a set of ASCII or a set of hexadecimal characters. The number of characters you use will depend on the key length chosen (e.g., 64-bit, 128–bit). You can use the table below for reference. Note that longer keys provide stronger security.
| Key length | Number of ASCII characters | Number of hexadecimal characters |
| 64-bit | 5 | 10 |
| 128-bit | 13 | 26 |
| 152-bit | 16 | 32 |
The characters you enter convert into bits. Then, they concatenate with a 24-bit initialization vector (IV). That way, they form the actual encryption/decryption key. This key possesses the 64, 128, or 152 key lengths, not your WEP key. The concatenation happens in the background; you don’t need to perform it yourself.
The main purpose of the IV is to remove repetitive patterns in the encrypted data. Repetitive patterns are undesirable from a security standpoint because they allow attackers to deduce the original, unencrypted data, a.k.a. the cleartext.
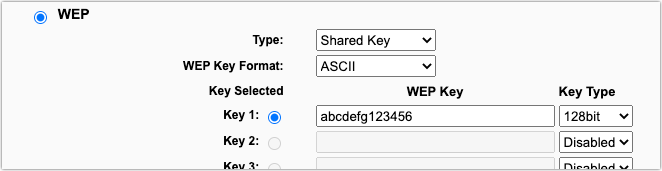
In WEP, the network security key (a.k.a. the WEP key) encrypts the packets sent over the wireless connection. Despite the presence of the IV, cryptanalysts have demonstrated how easy it is to recover the encryption key. Once recovered, it’s quite trivial to obtain the encrypted data.
Because it’s easy to crack, WEP is now replaced by WPA and WPA2. Although many wireless routers/APs still support WEP, you shouldn’t be using it anymore. Hackers can easily crack it and intercept sensitive data you send over the network.
WPA/WPA2/WPA3 Key
A WPA key, on the other hand, is the type of network security used in the Wi-Fi Protected Access (WPA) protocol. By design, this protocol addresses the inherent vulnerabilities of the WEP protocol. This protocol currently has three versions: WPA, WPA2, and WPA3.
Each higher version is also more secure than the previous ones. Although WPA3 is the most secure, WPA and WPA2 are still the most widely supported versions. Of course, of the two, I recommend WPA2, being the higher version.
As with WEP, WPA may also consist of either a set of ASCII or a set of hexadecimal characters. If you use ASCII, you can enter between 8 and 63 characters. On the other hand, if you use hexadecimal characters, you can enter between 8 and 64 characters.
Unlike WEP, the network security key (a.k.a. the WPA/WPA2/WPA3 key in this case) isn’t used directly in encryption. Rather, it’s combined with several other values to generate the actual key. The combination gets carried out through a per-packet key mixing function. That creates a new key for every packet transmitted. This also makes it much more difficult to recover, because it’s different throughout (unlike the WEP encryption key).
How to Find a Network Security Key
Sometimes, you want to connect a device to your Wi-Fi network, but you forgot the network security key. Don’t lose hope! I’ll show you different retrieval methods for different devices.
On a Router
If you didn’t bother to change the factory default network security key on your wireless router/AP , you can simply obtain the key from there. Go to your router/AP and check the sides, rear, or bottom of the device. The default network security key should be there.
Some wireless router/AP manufacturers use the labels ‘WEP key’, ‘WPA key’, or ‘WPA2 key’, so look for those terms if you don’t find ‘wireless password’, ‘wireless passphrase’, or ‘network security key’.
Here’s what the default network security key looks like on my wireless router:
Note: Disregard the password (‘admin’ in this case) that’s adjacent to a username (also ‘admin’ in this case) shown below. That’s the factory default username and password for this device’s admin account. You’ll need those if you want to make changes to the router’s settings, not to access the Wi-Fi connection.

What if you already changed the default wireless password on your wireless router/AP? You can still find the network security key from a device that’s already connected to that router/AP. I’ll also show you how you can do that with any device connected to your Wi-Fi network.
On a Windows Device
Obtaining the network security key on a Windows device is easy.
- Go to the search box beside the Windows Start menu
- Type in network connections.
- Click the search result that says ‘View network connections’. That’ll take you to the Control Panel > Network and Internet > Network Connections window.

- Look for the icon representing the Wi-Fi network in question and then double-click it.

- Click the Wireless Properties button when the Wi-Fi Status window appears. That’ll bring up the current Wi-Fi network’s Wireless Network Properties window.
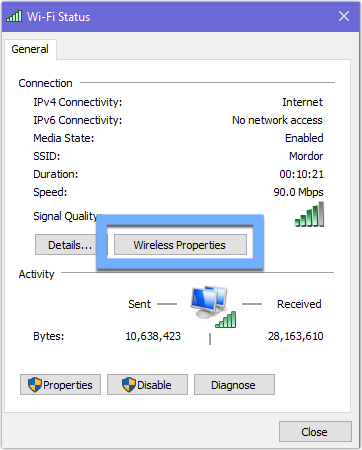
- Navigate to the Security tab
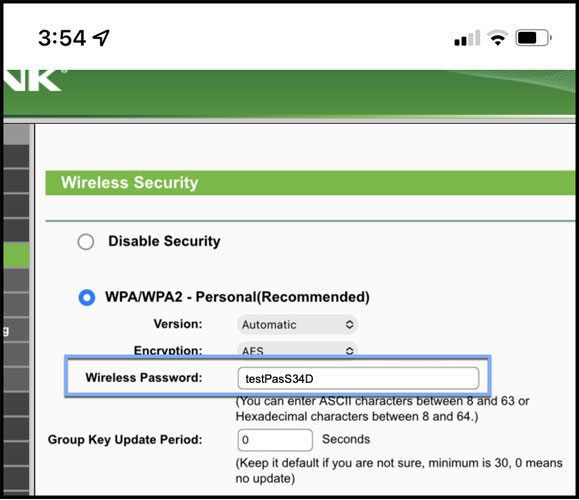
- Click the Show characters checkbox to display the network security key. In this example, the network security key is ‘testPasS34D’.
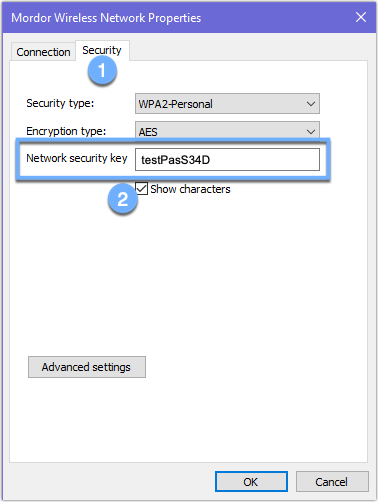
On a Mac
To obtain the network security key on your Mac device:
- Navigate to the upper-right corner of your screen
- Click the Spotlight icon.
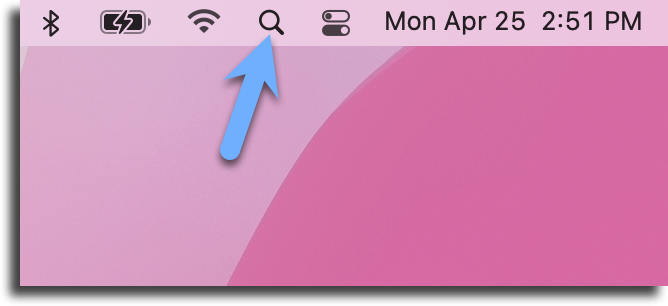
That should launch the Spotlight Search box.
- Enter ‘Keychain Access’ into the search box
- Click the entry with the keychain icon.
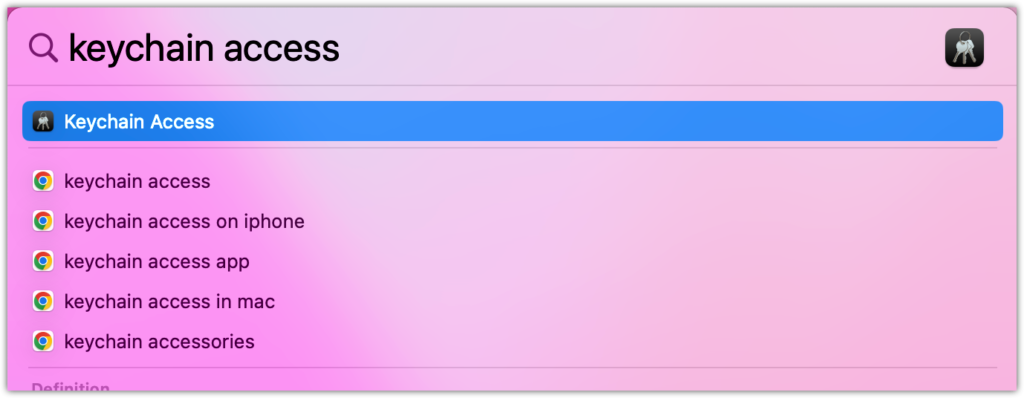
That should launch Keychain Access.
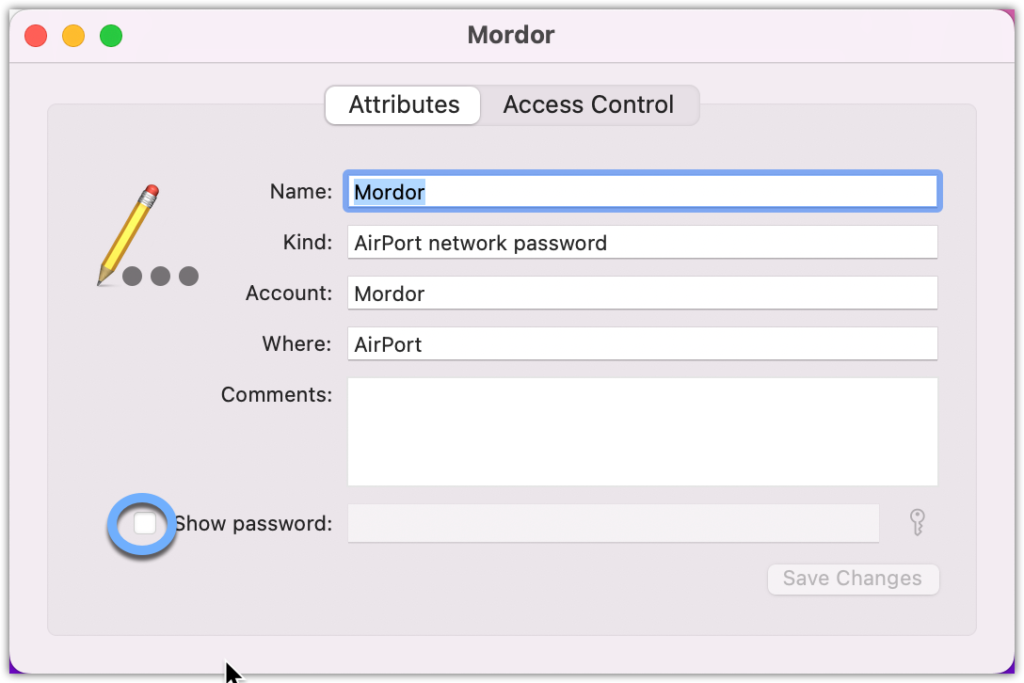
- Enter the name of your Wi-Fi network into the search box in the upper-right corner.
- Click the corresponding entry in the list shown in the lower half of that window.

That should launch the window for your Wi-Fi network. In my case, the name of the window is ‘Mordor’.
- Click the Show password checkbox.
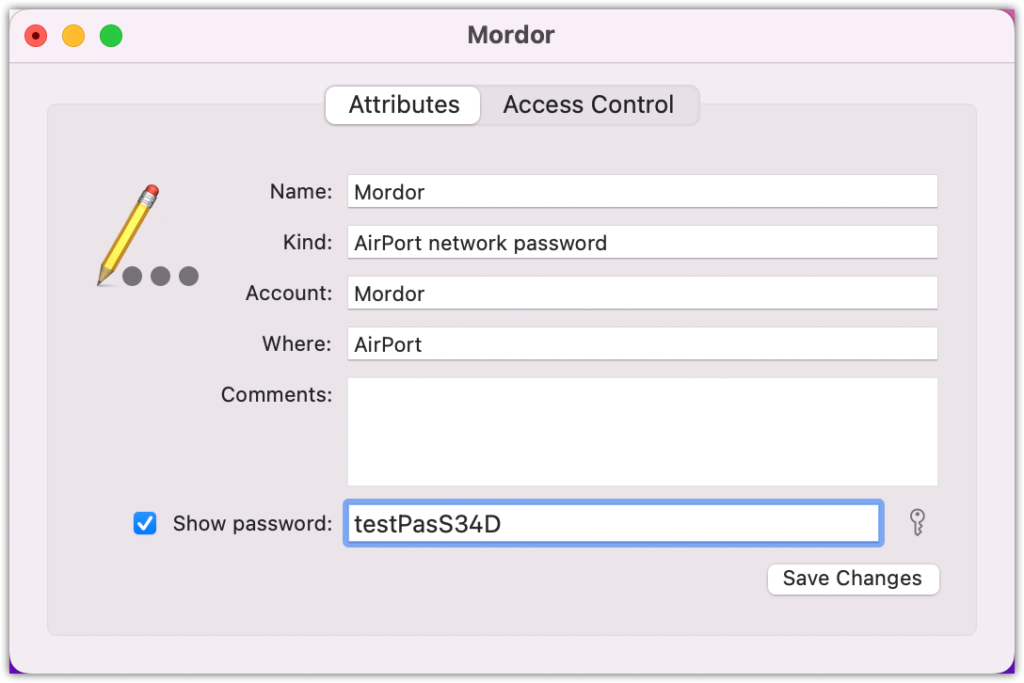
- Enter an administrator account username and password for your Mac device. Once you submit those credentials, you should then see the network security key in the Show password field. In this example, the network security key is ‘testPasS34D’.
On an Android Phone
To obtain the network security on your Android device:
- Launch the Settings application and
- Tap the Connections menu. Make sure you’re connected to the Wi-Fi network in question.
Note: These steps may slightly vary depending on your specific Android version and phone model.
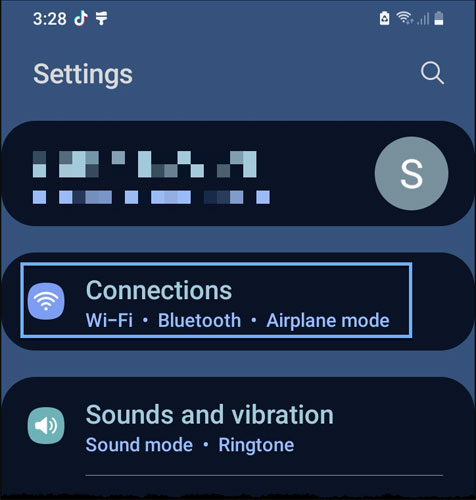
3. Tap the Wi-Fi submenu.

4. Click the gear icon beside the name of the Wi-Fi network you’re currently connected to.
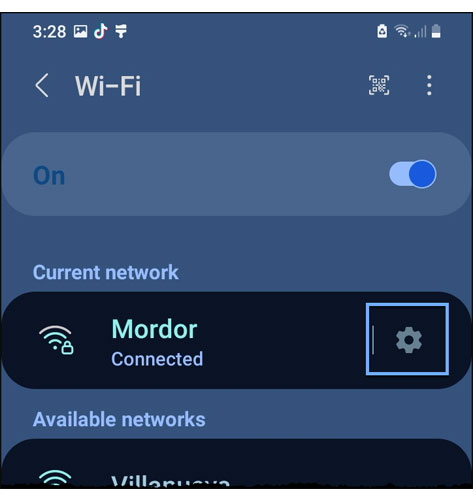
5. Tap the QR code icon near the bottom of the screen.
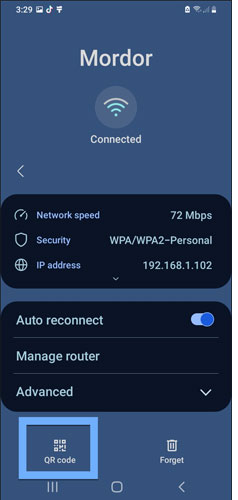
A QR code should now appear at the center of the screen. In some phone models, the Wi-Fi password will be right below that QR code. That’s not the case here. However, note that the QR code is all you need to share that Wi-Fi password with other devices and enable those devices to connect to your network.
You can either scan that QR code using the new device you want to connect, save it as an image for later, or share it by tapping the Share icon.

On an iPhone
Currently, iPhones don’t offer a straightforward method to obtain the security key, But, I have a workaround for you if you’re the Wi-Fi network admin.
- Go to the Settings application.
- Navigate to Wi-Fi.
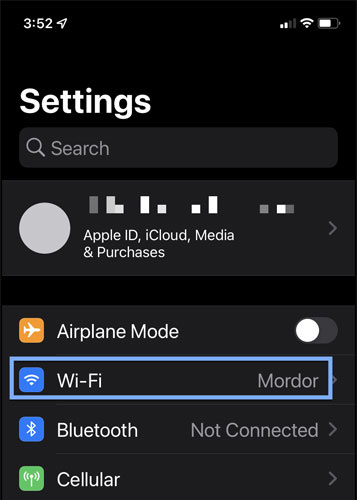
- Tap the Information icon beside the name of the Wi-Fi network associated with the network security key you want to obtain.
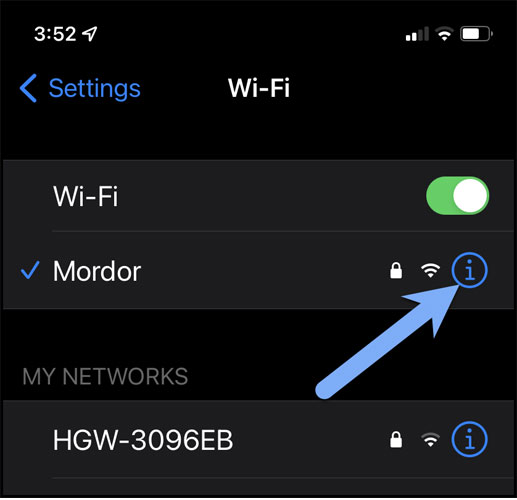
- Scroll down to the item labeled Router.
- Copy the corresponding IP address. In my case, that would be 192.168.1.1.
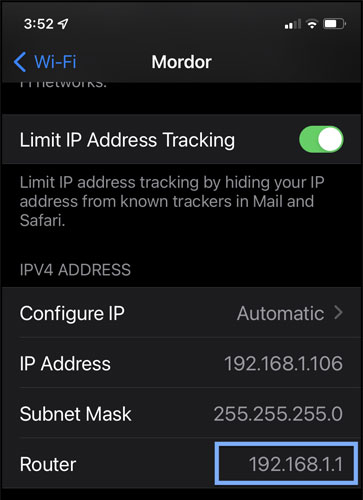
- Launch the Safari application and then paste the copied IP address into the URL box. This should load up the login screen of your router’s administrative web interface.
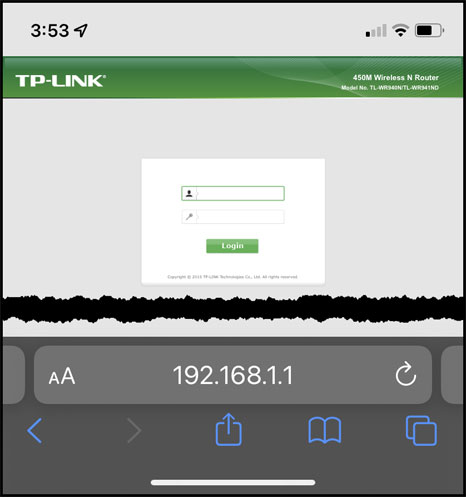
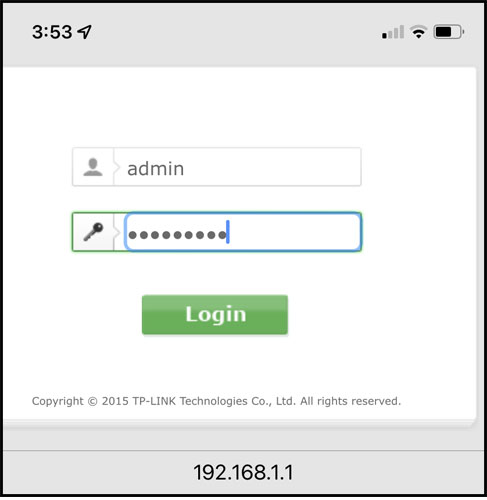
- Enter your administrator username and password.
If you haven’t changed the factory default values, they’re just the username and password printed on your wireless router/AP device. I showed this earlier, so you can scroll up and review that to see what I mean. Now, if you did change the default values but forgot what they were, you’ll need to do a factory reset to be able to use the factory default values again. Please consult your router’s user guide for instructions.
- Navigate to whichever section holds the settings for the wireless network security protocols. In my case, that would be the Wireless Security section.

- Look for the wireless network security protocol that’s enabled. You should see the network security key there.
Now that you know how to find your Wi-Fi network security key, it’s important to remember that you should only be sharing that key with authorized users. Read this next section to see what else you should keep in mind.
Network Security Key Best Practices
I’m now going to share with you 3 best practices that’ll make your password’s protection more effective.
1. Change Factory Default Passwords
Most wireless routers/APs have their factory default passwords/network security keys printed on the body of the device, usually at the bottom, rear, or sides. While you can use the default network security key during the initial setup, you should replace it as soon as you start configuring your router/AP.
That’s because the default password is the same for each unit of the model. That means cybercriminals may have already posted in hacking forums. In turn, your wireless router/AP could be at risk of getting hijacked.
The policy of changing factory default passwords should apply to network security keys. Still, you should also apply it to the default administrative user account of your router/AP. If you don’t change that, people who’ve already joined your network can simply log in to your router and alter settings, including your network security key!
2. Adhere to a Strong Password Policy
It’s not enough for you to simply change the default password. You must also follow password creation best practices to minimize the risk of a brute force attack. These practices involve using:
- Long passwords, ideally 10 characters or more
- A mix of alphanumeric characters and special characters (e.g., @, $, !)
- A mix of uppercase and lowercase letters
Follow these rules when changing your Wi-Fi password and the password of your wireless router/AP’s admin user account.
3. Remind Users Not to Share their Wi-Fi Password
You should only share your Wi-Fi network’s password with your network’s authorized users. Otherwise, you run the risk of a network overload or, worse, infiltration by a malicious individual. Implement security awareness training to remind your users not to share their password with outsiders
Does your password meet these standards? No? Then let me show you how you can change it. (Now’s your chance to follow these best practices above!)
How to Change Your Wi-Fi Password
Although your wireless router/AP comes with a factory default SSID and network security key, you shouldn’t be using those. All units of the same router/AP model will be using these exact values. That means anyone familiar with those default values can easily connect to your Wi-Fi network.
To change your Wi-Fi password, kindly follow these 5 steps below:
1. Obtain your Router’s IP Address
You can get your wireless router’s IP address from devices connected to that router. Earlier, I showed you how to do that on an iPhone. These steps will of course vary on different devices, so you need to find out how it’s done on your device. You can also refer to the list below, which contains some router brands and their common default IP addresses.
| Router Brand | Common Factory DefaultIP Addresses |
| 2Wire | 192.168.1.1, 192.168.0.1 |
| 3Com | 192.168.1.1, 192.168.10.1 |
| Apple | 10.0.1.1 |
| Asus | 192.168.1.1, 192.168.2.1 |
| 192.168.86.1, 192.168.0.1 | |
| Huawei | 192.168.1.1, 192.168.0.1 |
| Linksys | 192.168.1.1, 192.168.0.1 |
| Netgear | 192.168.0.1, 192.168.0.227 |
| TP-Link | 192.168.1.1, 192.168.0.1 |
| US Robotics | 192.168.1.1, 192.168.2.1 |
2. Enter the IP Address into your Web Browser
Once you’ve obtained the IP address in question, enter it into your device’s web browser. It’s probably going to be easier if you use a PC or laptop so you can work on a larger screen. Just make sure the device is connected to the Wi-Fi network in question.
3. Log into your Router’s Administrative Web Interface
Log in to your router’s administrative web interface, then look for the wireless security settings. It’s usually a page that contains settings for WEP or WPA/WPA2/WPA3.
4. Choose a Strong Wireless Security Protocol
Once you get to the wireless security settings page, select a strong wireless security protocol, preferably WPA2 or WPA3.
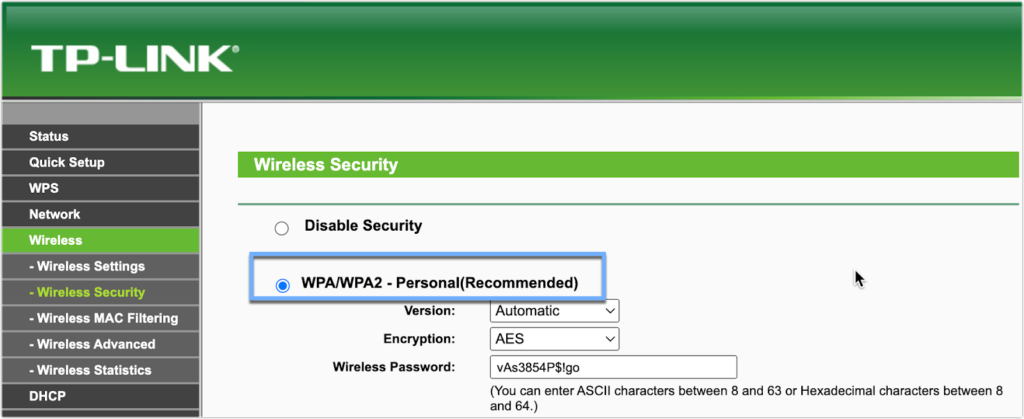
5. Change your Wi-Fi Password
Finally, look for the ‘Wireless Password’, ‘Wireless Passphrase’, or ‘Network security key’ field (again, this term may vary depending on the brand you’re using). Then, change it to your desired password/passphrase. Make sure you apply the strong password practices we shared earlier in this article. Once you’re done, you might have to click a Save or Apply button to apply those changes.
Final Words
Access control and data-in-motion encryption are two crucial elements of wireless network security. As you’ve learned in this article, your Wi-Fi network security key plays an important role in enforcing these security measures. Consequently, it’s important to adhere to best practices in coming up with a strong network security key. You should also ensure you’re giving those keys to legitimate users only.
Moreover, it’s also important to choose the right wireless network security protocol to maximize the full potential of that strong network security key. In this regard, you need to avoid WEP and shift to either WPA2 or WPA3.
In this article, I gave you tips to retrieve your network security key if you’ve forgotten it. That way, you can also onboard new users on your network even if you lost your Wi-Fi password. However, it’s also worth noting that malicious individuals can abuse these methods and gain unauthorized access to your wireless network.
As such, you need to constantly educate your users on the importance of securing their endpoint devices. Devices that can connect to your corporate network shouldn’t be shared with people who don’t have access privileges.
Have more questions about wireless network security? Check out the FAQ and Resources below!
FAQ
What is access control?
Access control is a security mechanism that allows you to restrict access to an IT environment to a certain group of users, devices, or applications. It’s a way of preventing threat actors and ordinary unauthorized entities from gaining access to resources protected by that access control. When you use it in the context of a wireless network (by using network security keys), you can prevent unauthorized access to your Wi-Fi network.
What is data-in-motion encryption?
Data-in-motion encryption, also known as data-in-transit encryption, is a security mechanism that leverages cryptographic technologies to preserve the confidentiality of data while it’s traversing a network. Data-in-motion encryption protects data traversing the wireless network. When you use network security keys, it implies you’ve enabled the encryption capabilities of your wireless router/AP.
What is a man-in-the-middle attack?
A man-in-the-middle (MITM) attack is an attack vector that involves intercepting data traversing a network—in this case, a wireless network. The usual targets of MITM attacks are usernames and passwords. Once they have that information, threat actors can use those login credentials to gain unauthorized access to the machine or application those credentials are associated with. You can mitigate the risk of a MITM by switching to strong wireless security protocols such as WPA2 or WPA3 and using strong network security keys.
Why is it important to secure endpoint devices?
Endpoint devices such as PCs, laptops, phones, and tablets may store sensitive data and metadata that threat actors can abuse to gain deeper access to your network. Besides, several other endpoint security issues can put your business at risk. By securing your endpoint devices, you can make it difficult for threat actors to obtain your sensitive data.
Why is it important to enforce a strict password policy?
Passwords are one of the weakest links in network security. They’re the keys to your kingdom, but they’re still easy to beat. Brute force attacks, dictionary attacks, credential stuffing, and even plain social engineering can put passwords into the wrong hands. Strict password policies can help you counter these threats. To be efficient, these policies should cover password creation, usage, management, and protection.
Resources
TechGenix: Newsletters
Subscribe to our newsletters for more quality content.
TechGenix: Article on SIEM Software
Explore the infosec policy-enforcement benefits of a SIEM in this article.
TechGenix: Article on Streamlining Zero Trust Network Access
Discover a better way of providing Zero Trust Network Access in this article.
TechGenix: Guide for Deploying a VPN on Windows
Learn how to deploy a VPN in a Windows environment in this article.
TechGenix: Article on Developing a DLP Strategy
Get in-depth knowledge of how to develop and assess a DLP strategy in this article.
TechGenix: Review on Kerio Control with VPN
Weigh the pros and cons of using Kerio Control in this article.




Hi there, this is more a question than comment. My dad & I bought a TP- link Dual-Band wi-fi router & are using it under the range extender mode. I’ve got the router at my place, picking up his signal from his house. He’s got a password & all on his wifi, now since I’m going off his wifi do it need to have a separate password for the new router or am I protected by his password since it’s his wifi I’m using ? Hope that’s not to confusing. Thank u