If you would like to read the other parts in this article series please go to:
- Office 2010 Security (Part 1) – Threat Mitigation
- Office 2010 Security (Part 2) – Threat Mitigation (Continued)
Introduction
In the first article of this series we described how security has been enhanced in Microsoft Office 2010 in two general ways: by the inclusion of new technologies for mitigating against threats, and by the addition of new features for controlling the flow of information. The first and second articles then described three new threat mitigation technologies found in Office 2010. These three threat mitigation technologies are Office File Validation (OFV), Protected View and Trusted Documents.
In this third and final article we’ll look how several Office 2010 features have been enhanced to enable enterprises to better control the flow of sensitive business information. The three information control features we’ll look at are:
- Crypto and digital signature improvements
- Document Inspector
- Domain-based password enforcement
Crypto and Digital Signature Improvements
Cryptography has been strengthened and enhanced in Office 2010 compared to previous versions of Office. Some of the key improvements in this area include the following:
- Support for CryptoAPI Next Generation (CNG) including support for the encryption algorithms AES, DES, DESX, 3DES, 3DES_112 and RC2, and support for the hashing algorithms MD2, MD4, MD5, RIPEMD-128, RIPEMD-160, SHA-1, SHA256, SHA384 and SHA512.
- Support for hash-based message authentication code (HMAC) to help safeguard the integrity of Office files.
- Use of 128-bit AES as the default encryption algorithm when password-protecting Office OpenXML files such as .docx and .xlsx files.
Note:
To help ensure backwards compatibility, Office 2010 still uses RC4 for encrypting legacy binary Office files such as .doc and .xls files.
The encryption and hashing algorithms supported by Office 2010 are also supported by Office 2007 SP2. This not only ensures interoperability but can also help ease migration from Office 2007 to Office 2010.
Digital signatures have also been enhanced in Office 2010 in several ways, including:
- Support for trusted time stamping to ensure signatures can remain valid even if the certificate used to sign the document has expired.
- The way users digitally sign documents has also been simplified as described in the next section below.
Note:
Documents signed using Office 2010 and Office 2007 cannot be verified using Office 2003.
End-User Experience for Crypto and Digital Signature Improvements
While cryptography works under the hood, signing a document is the task of the user. The steps for digitally signing a document using Word 2010 are basically like this. Begin with a .docx file you want to sign:

Figure 1: Step 1 of digitally signing a document using Word 2010.
Click the Signature Line control on the Text tab of the Insert ribbon:

Figure 2: Step 2 of digitally signing a document using Word 2010.
Type your name and other info in the Signature Setup dialog box:
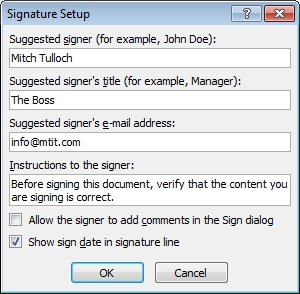
Figure 3: Step 3 of digitally signing a document using Word 2010.
After you click OK, your document will look like this:

Figure 4: Step 4 of digitally signing a document using Word 2010.
Now double-click on the signature line in the above figure. Doing this opens the Sign dialog box, and type your name as indicated:
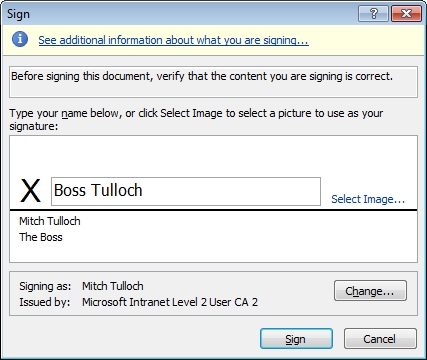
Figure 5: Step 5 of digitally signing a document using Word 2010.
Finally click Sign to digitally sign your document. The final result looks something like this:
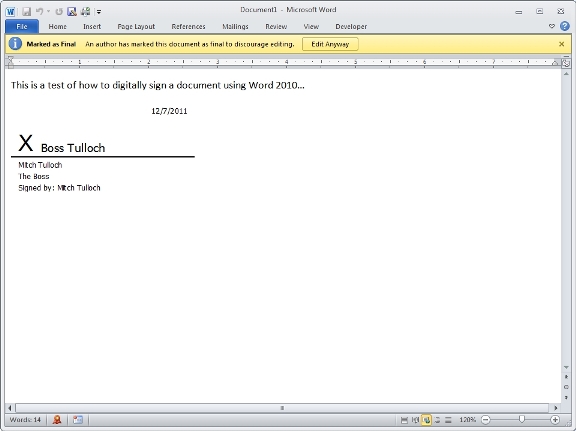
Figure 6: Step 6 of digitally signing a document using Word 2010.
Administrator Options for Configuring Crypto and Digital Signatures
As the administrator for your organization, you can use Group Policy to configure how encryption and digital signing works for end-users. As Figure 7 illustrates, Word 2010 for example has a number of different policy settings for encryption found under User Configuration\Administrative Templates\Microsoft Word 2010\Word Options\Security\Cryptography:
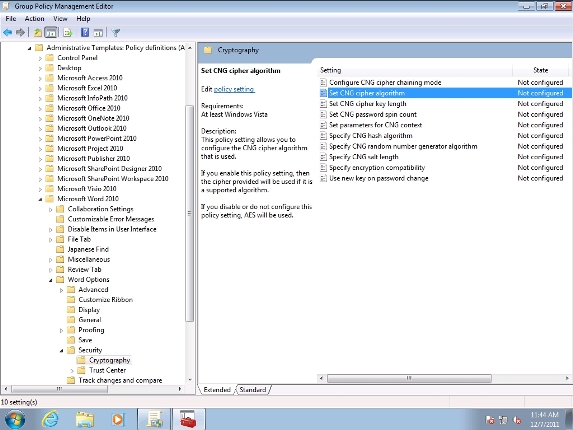
Figure 7: Group Policy settings for configuring encryption options for Word 2010.
For more information on these policy settings, see this link.
Document Inspector
Document Inspector was first introduced in Office 2007 and has been enhanced in several ways in Office 2010. For example, Document Inspector can check for additional types of hidden content in documents so users can ensure that no information leakage occurs when business documents are shared or published online. In an age of increasing concern over privacy and growing regulations over personally identifiable information (PII), these new capabilities are welcome news.
End-User Experience for Document Inspector
Document Inspector can be used by first opening Backstage view by selecting Info from the File ribbon:
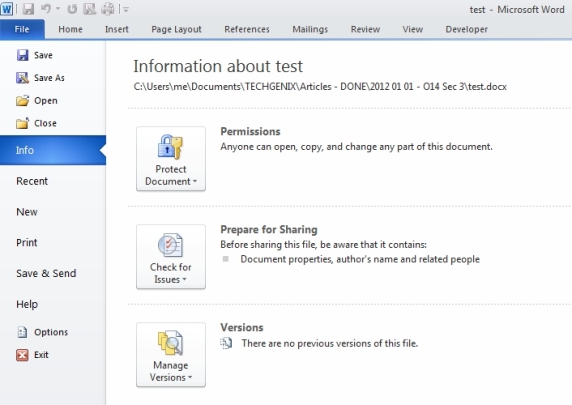
Figure 8: Backstage view indicates this Word document has information that should be removed.
In the above figure, to the right of the Check For Issues control, it says that this Word file contains document properties such as the author’s name. Before publishing such a document, most businesses will want the user to remove such personal information from the document. To do this, click the Check For Issues control:

Figure 9: Step 1 of using Document Inspector to clean up a Word document.
Now select Inspect Document to open the Document Inspector:

Figure 10: Step 2 of using Document Inspector to clean up a Word document.
Clicking the Inspect button to check for the selected types of content in the document indicates several types of personal information are present in the document:

Figure 11: Step 3 of using Document Inspector to clean up a Word document.
To remove the undesired information, click the Remove All button. The Document Inspector indicates that the document has been successfully cleaned:
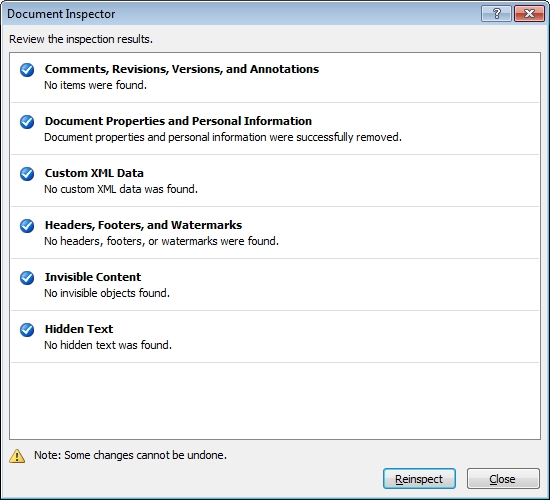
Figure 12: Document Inspector has been used to successfully clean the document.
Administrator Options for Configuring Document Inspector
There seems to be only one Group Policy setting for configuring Document Inspector for each of Word 2010, Excel 2010 and PowerPoint 2010. The Group Policy editor indicates that this policy setting is found under Computer Configuration\Microsoft Office 2010 (Machine)\Miscellaneous as shown below:
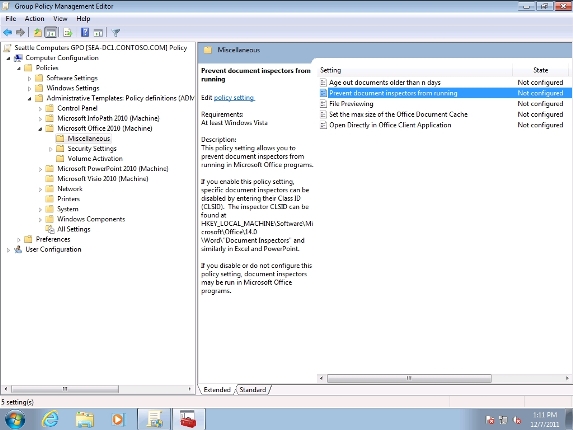
Figure 13: Group Policy setting for disabling Document Inspector functionality.
Domain-based Password Enforcement
Users who share documents and spreadsheets within or between organizations are used to the need of password-protecting these files to keep their contents private. In previous versions of Office 2007, the encryption key used to encrypt a password-protected document was generated from the password used, so the longer the password, the stronger the key, and if a user wanted to specify a single-character password there was nothing stopping them from doing so. New in Office 2010 is the ability for administrators to configure Office so that passwords used to protected documents must comply with the password policies for the Active Directory domain. In other words, if the user must use an 8-character password to log onto their PC, they will also need to specify an 8-character password when they try and password-protect their documents.
End-User Experience for Domain-based Password Enforcement
The end-user experience for password-protecting files has also been simplified in Office 2010. For example, to password-protect a Word document, open Backstage view and select the Protect Document control, then select Encrypt With Password:

Figure 14: Step 1 of password-protecting a document using Word 2010.
Type the password you want to use in the Encrypt Document box (must do this twice):
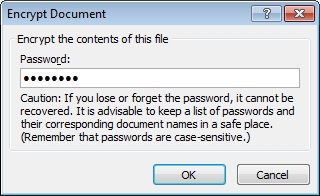
Figure 15: Step 2 of password-protecting a document using Word 2010.
The color change in Backstage view indicates that a password is now needed to open the document:

Figure 16: The document has been password-protected.
Administrator Options for Configuring Domain-based Password Enforcement
As the administrator for your organization, you can use Group Policy to enable domain-based password enforcement for Office 2010 users. The key policy setting for this is called Set Password Rules Level:
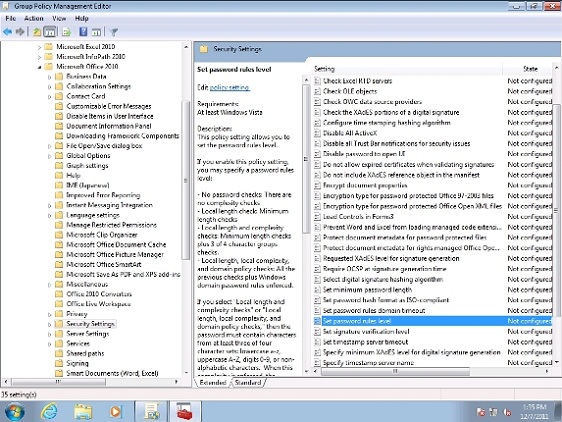
Figure 17: Policy setting for enabling domain-based password enforcement.
To enable domain-based password enforcement, open this policy setting and enable it and set it to “Local length, local complexity, and domain policy checks” as shown here:
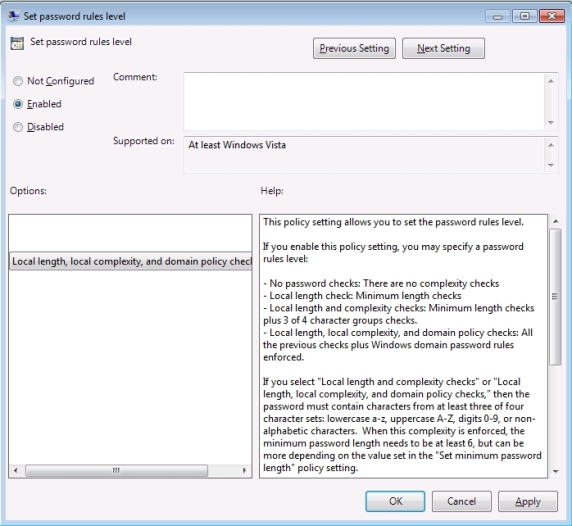
Figure 18: Policy setting for enabling domain-based password enforcement (details).
What happens now is that when a user tries to protect a document using a password, Office tries to contact a domain controller to enforce its password policy. But if no domain controller is available, Office simply reverts to using the local length and complexity settings specified using the other Group Policy settings indicated in the previous figure.
Conclusion
The three articles in this series have provided an overview of Office 2010 security and privacy enhancements, how to use them, and how to administer them using Group Policy. For more information on Office 2010 security and privacy enhancements, see the relevant articles in the TechNet Library.
If you would like to read the other parts in this article series please go to: