Introduction
The introduction of Microsoft Forefront Threat Management Gateway (TMG) 2010 brings us a number of exciting and compelling reasons to upgrade from previous versions of Microsoft ISA Server. Some of these are major new security features included in the product, such as URL filtering, web anti-virus and anti-malware inspection, forward SSL inspection, an all new intrusion detection and prevention system, and enhanced e-mail protection. There are also numerous small things that have changed that are sure to make TMG’s daily management much easier. In this article I will introduce you to some of my favorite new features and enhancements in the TMG management console.
New and Improved
Rule Base Search – This feature has been a long time coming! The new search functionality included in the TMG management console makes managing large and complex rule sets much simpler. Want to display any rule that uses the DNS protocol? Simply enter ‘DNS’ in the search box and click the magnifying glass icon to execute the search.

Figure 1
The main window displays any rule that includes the DNS protocol.
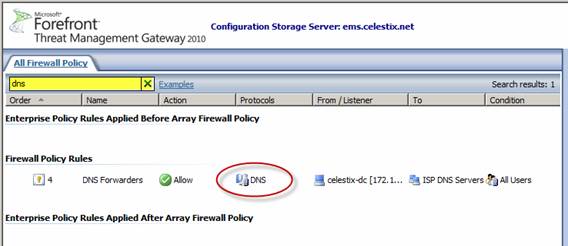
Figure 2
There are several ways to construct queries. You can choose free text, name:value pairs, and property:value pairs. For more information, click the Examples link next to the search box.
Web Access Policy – The new Web Access Policy node in the navigation tree displays a consolidated view of Web access rules configured in TMG.
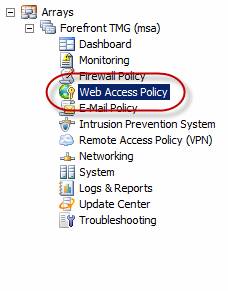
Figure 3
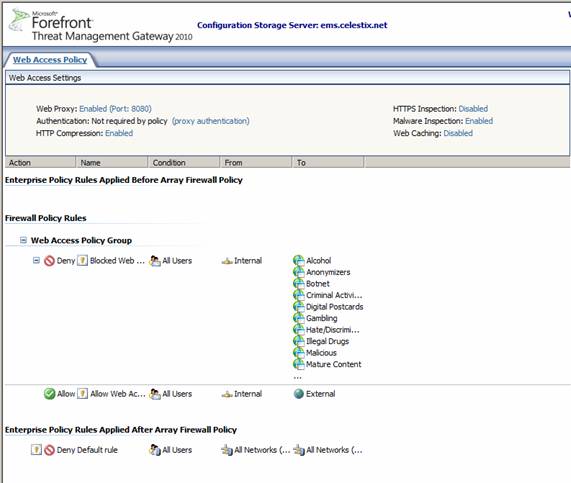
Figure 4
As with the rule base search functionality, this will significantly simplify administration for implementations with large and complex rule sets. A clear and concise view of web access rules reduces the chance of configuration error. Quick and easy access to common settings for enabling web access is also included in this view. These settings include web proxy configuration, authentication, compression, HTTPS inspection, malware inspection, and web caching.
Routing Configuration – Highlight the Networking node in the navigation tree and you will see a new tab called Routing.

Figure 5

Figure 6
Here you can create network topology routes (static routes). It is no longer necessary to connect to each TMG firewall individually and enter route commands from the command line. To add a static route, click on the Create Network Topology Route link in the task pane.
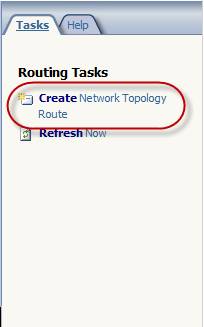
Figure 7
Enter the destination host or network, the appropriate subnet mask, and the next hop gateway address. You can also specify a metric if required.

Figure 8
This feature also allows you to view the routing configuration for each TMG firewall.
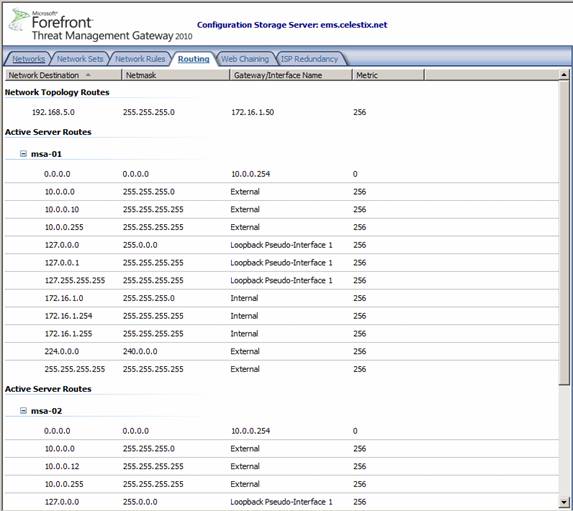
Figure 9
Network Interface Configuration – In addition to being able to configure static routes in the management console, you can also configure network interface properties. Highlight the Networking node in the navigation tree and select the Network Adapters tab.
Note:
This tab is only visible when running the management console on an array member. It is not displayed in the management console on the Enterprise Management Server.
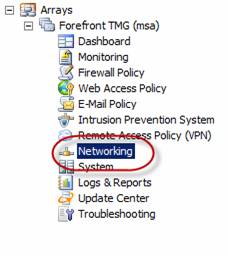
Figure 10

Figure 11
Right-click on a network interface and choose Properties. Here you can change IP addresses, subnet masks, default gateways, and configure DNS servers. Additionally you can enable or disable interfaces.

Figure 12

Figure 13
Getting Started Wizard – After TMG is installed, opening the management console for the first time will launch the Getting Started Wizard.

Figure 14
Here you are prompted to configure network and system settings and also define your deployment options. In the event you need to make significant configuration changes to your system or redefine deployment options post-installation, you can run the wizard again by highlighting the top node in the navigation tree then selecting the Tasks tab in the task pane and clicking on the Launch Getting Started Wizard link.
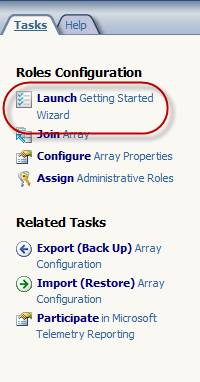
Figure 15
Please note that you cannot run the Getting Started Wizard when the TMG firewall is a member of an array. Attempting to launch the wizard will generate the following error:
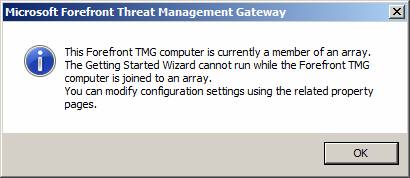
Figure 16
Network Load Balancing (NLB) Configuration – TMG now includes the ability to change the NLB operating node in the GUI.
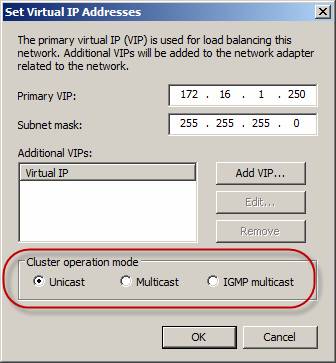
Figure 17
In the past, this change could only be made programmatically. This made confirming the settings difficult, requiring the administrator to drop down to the command line for verification.
Dashboard System Performance – The dashboard overview in the TMG management console now displays new counters for system performance. CPU Usage and Available Memory are included; this is much more useful to the average TMG administrator than the Allowed Packets/Sec and Dropped Packets/Sec that previous versions included.
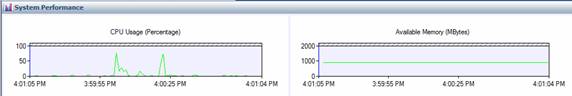
Figure 18
Connectivity Test – Highlighting the Troubleshooting node in the navigation tree shows a new Connectivity Test tab.

Figure 19
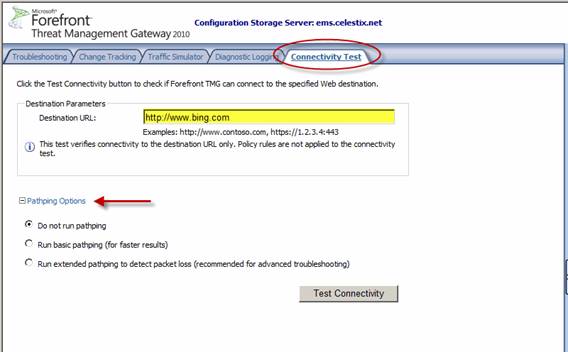
Figure 20
This new tool allows you to test basic web connectivity from the firewall in the management console. Complete the Destination URL: field and click the Test Connectivity button to perform the test. Optionally you can select to run a pathping during the test to gather additional information. Be aware that the destination URL cannot contain a path, so if you are in the habit of adding the trailing slash when entering URLs like I am, you will see the following error:

Figure 21
Firewall Policy Grouping – This is another feature administrators of large and complex rule sets will appreciate. To create a rule group select one or more rules, right-click on the selected rule(s) and choose Create Group.
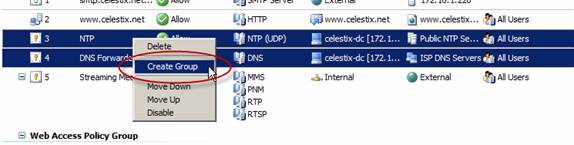
Figure 22
Give the policy group a descriptive name and choose Ok.
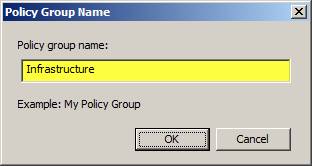
Figure 23
The rules you selected are now part of a group. By right-clicking on the group and choosing Properties you can enable, disable, or move the entire group. You can also rename the group or ungroup these rules.
Summary
Those are my favorite new features in the Forefront Threat Management Gateway 2010 management console. There are many more features that you will likely find useful, so I encourage you to begin exploring the new TMG management console today!



