If you missed the first part in this article series please read Packet fragmentation versus the Intrusion Detection System (IDS) Part 1.
Packet fragmentation versus the Intrusion Detection System (IDS) Part II
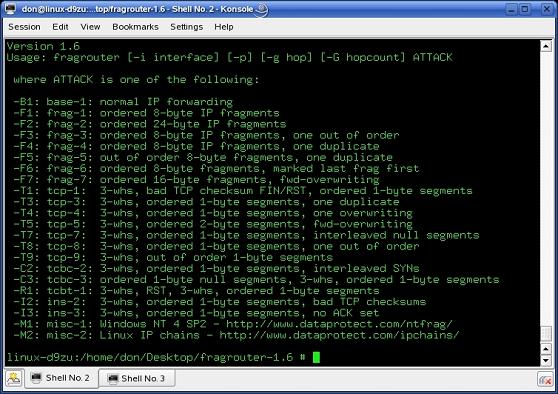
Over the course of part one, we saw how to set up the various computers in our VMware lab. The setup was simple, and even the installation and use of fragrouter fairly pain free. We ended off part one with an attempt at packet fragmentation via fragrouter in an effort to evade Snort. That first attempt failed for Snort did indeed pick up the attack. It had no problem in reassembling the fragmented packets and recognizing the attack for what it was; an RPC bind attempt via the MS03-026 exploit contained in the Metasploit Framework. Fragrouter has quite a few more tricks in its arsenal. If you enter the “./fragrouter -help” command as seen in the screenshot below, you will be shown all of the fragrouter options available to you.
Figure 1
What we now need to do is use a fragmentation attack that will likely be a bit more evasive. Seen in the screenshot above is one of interest. Specifically, the “-F3” one. This is much like the first attempt we made, but this time there will be one fragment out of order in the fragmented packet train. This also serves as an orderly incrementing of our attempted evasion attempts. We will now again have to ensure that Snort is running on the victim computer, as well as tcpdump.exe this time. It will allow us to log the incoming fragmented traffic and then view some sample packets. Also please ensure that you have invoked fragrouter before you initiate the attack via Metasploit Framework. In order to try and keep our results uniform we will again use the MS03-026 exploit via Metasploit. All set? Let’s get to it then.
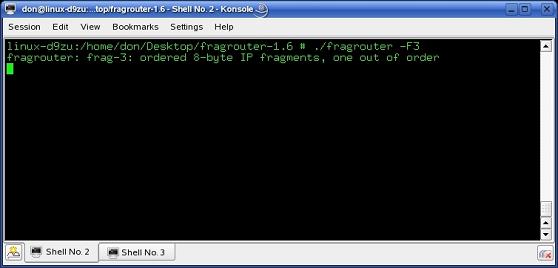
Figure 2
In the screenshot above I have invoked fragrouter with the “-F3” switches as discussed.
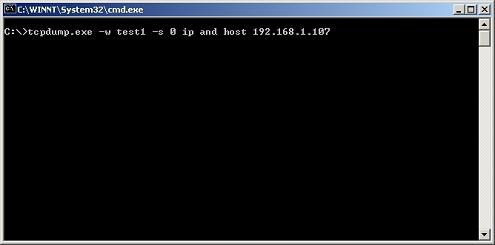
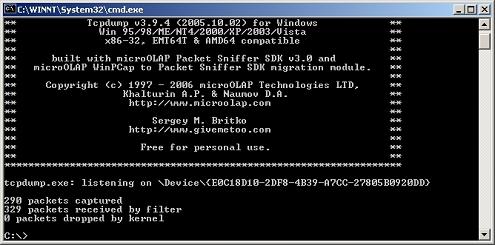
Figure 3
Now in the screenshot above I have invoked tcpdump.exe on the victim computer in order to log the fragmented packets as they arrive. This will allow us to take a look at them. Please note the “-w” switch as this will log the packets in binary format. You will later need to use “tcpdump -r test1 -nXvSs 0 | more” to view them.
Action!
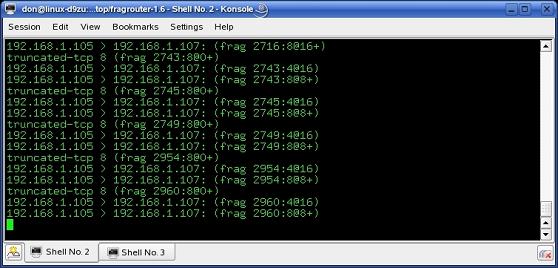
Now back to the fun stuff. On your attacking computer, bring Metasploit back up and enter the appropriate information in the web interface in order to attack the victim computer. Once ready, fire away as it were. As soon as you have obtained a shell on the computer, go and stop Snort on the victim computer. Then go back to the attacking computer and click on “session::break” to gracefully terminate the connection. In the screenshot below we can see that fragrouter does produce output when it is running. It will actually list the fragments as well as the offset in them as it is doing its fragmentation. That is a good list to have as a reference, should you want to go over your packet trace in detail.
Figure 4
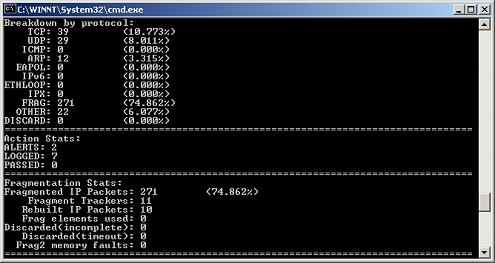
Seeing as we did not really increase the rate of fragmentation, the total amount of packets sent to the victim should be roughly the same. Let’s take a look at the screenshot below for it displays the statistics that tcpdump.exe collected.
Figure 5
There was a total of 290 packets received by tcpdump.exe which is roughly the same amount as previously recorded. That number can vary due to NetBIOS protocol broadcasts and the such. Of more interest is just what Snort did see this time.
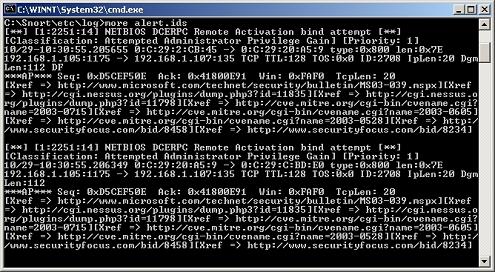
Figure 6
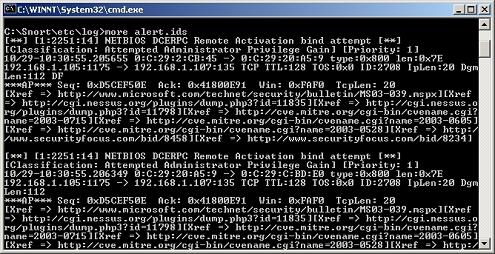
Well it would seem that Snort once again detected our attempts to evade it. To find out definitively, let’s take a look at the “alert.ids” file contained in the “log” directory.
Figure 7
Our most recent attempt at IDS evasion via packet fragmentation using fragrouter has once again failed miserably.
Bring on Metasploit
So far we have seen that generic attempts at packet fragmentation will not evade a modern IDS such as the latest version of Snort. There are many other options in fragrouter that may allow to bypass Snort if used creatively. Now that you have seen how to use fragrouter, I will leave that experimentation to you. What we shall now do is move on to another tool that will allow us to fragment attack traffic. That tool is the ever increasingly sophisticated Metasploit Framework. We have used it so far to generate attack traffic, but we will now also use its built in fragmentation capabilities as well.
To keep things simple we will recreate what we have already done before. To whit, we shall once again use MS03-026 but this time with fragmentation. Please see the screenshot below for the syntax used.
Figure 8
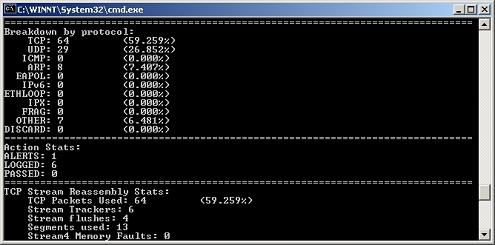
What Metasploit will now do is fragment the actual DCERPC fragment itself. It will not fragment all of the packets themselves, but only the DCERPC portion of it. Let’s go ahead and now try it, and see what Snort finds. Please see the screenshot below for what Snort saw.
Figure 9
Snort detected one alert within the traffic that was sent to it via Metasploit, but it detected no fragmented traffic, as only the DCERPC portion was fragmented. Now, the object of our interest, was the RPC bind attempt detected? Let’s take a look below.
Figure 10
Snort has once again foiled our attempts at being stealthy by using packet fragmentation. It detected three separate attempts at an RPC bind attempt. We could easily experiment further by continually decreasing the size of the fragment, but I will leave that up to you to do so. The key lesson to be learnt here is that IDS’s have indeed grown in sophistication and in their ability to deal with fragmented traffic.
Wrap Up
This article series dealt with the problem of a potential attacker deliberately fragmenting their attack traffic in order to evade IDS signatures. We attempted to recreate what such an aggressor may do in an attempt to obfuscate their attack. The slightly old but to some accounts still effective fragrouter was looked at. There was a good deal of options available to us via fragrouter, but some of the simpler ones were easily detected by Snort. That would leave the more sophisticated ones for use against a computer with an IDS running on it for further experimentation.
There were certainly quite a few more scenarios that we could have tried via fragrouter, but that would have entailed quite a few more article segments. The goal of this article series was to show you the existence of computer security tools such as fragrouter and Metasploit Framework. Neither of these tools is hidden away somewhere, rather they are out there for the taking. You would be wise to do just that, and learn how to use them. That in turn will lead you to a far more fundamental understanding of how fragmentation can affect an IDS. I know that it certainly worked for me. Prior to my having used these tools, the whole concept of fragmentation was really kind of murky. I always try to recreate any concept that I read about. The best way to learn is to actually do it. I sincerely hope this article was of use to you and as always welcome your feedback. Till next time.
If you missed the first part in this article series please read Packet fragmentation versus the Intrusion Detection System (IDS) Part 1.