Source: Unsplash
Between Dec. 6 and Dec. 8, 2022, cybercriminals compromised and harvested information from nearly 35,000 PayPal accounts in a credential stuffing attack, Paypal announced after an investigation into the incident. During the two-day window, the attackers gained access to highly sensitive information. This information included users’ names, dates of birth, postal addresses, social security numbers, and tax identification numbers. Plus, they might’ve gained access to transaction histories, connected credit/debit card details, and PayPal invoicing data.
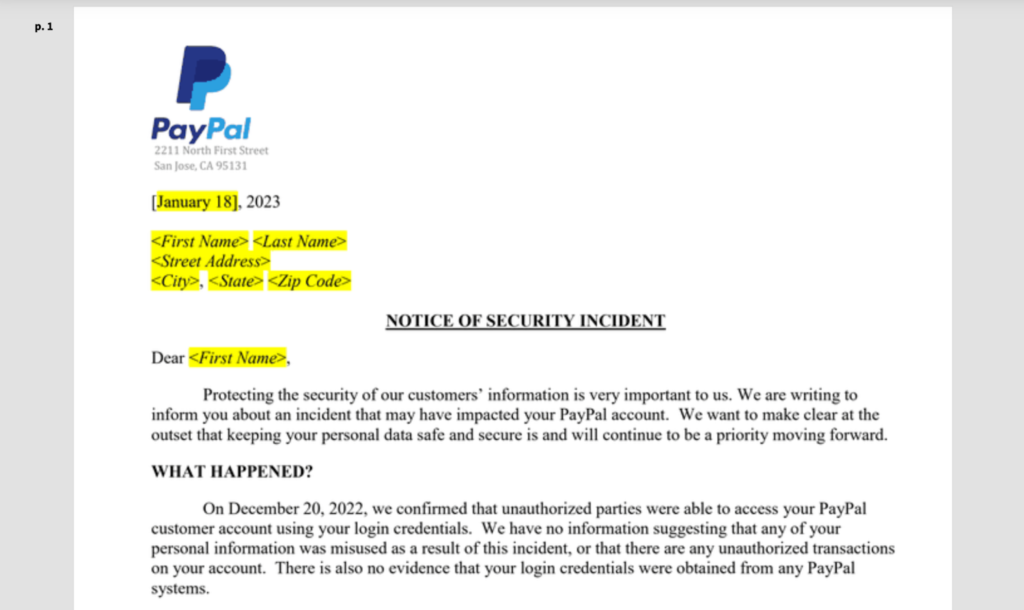
Starting Dec. 20., Paypal started notifying affected customers of the attack, the Notice of Security Incident statement read, which was sent out on Jan. 18. Aside from this customer notification, PayPal hasn’t publicly commented on the incident, as of the time of this writing.
The attackers didn’t compromise any of PayPal’s internal systems or employees in this credential stuffing attack. Instead, they simply logged in to the PayPal accounts through easily purchased username/password pairs. Since the accounts didn’t have two-factor authentication (2FA) enabled, cybercriminals were able to break into and easily compromise them.
PayPal Provides Recommendations but Delays Reporting the Incident
Source: Document Cloud
In response to the security incident, PayPal has reset the passwords of all affected accounts. In addition, it has offered free Experian identity monitoring services. Free identity monitoring is becoming a standard response in the event of identity fraud. In terms of identity restoration services, this package offers up to USD 1,000,000 of identity-theft insurance coverage, lost wallet assistance, automatic fraud alerts, web scan notifications, and access to major credit reporting agencies.
Ironically, these credit agencies have themselves suffered compromises in the past. In 2015, an Equifax leak led to the theft of the personal information of over 150 million American citizens. Eventually, Equifax reached a USD 700 million settlement for the breach. In Equifax’s case, it took the credit agency three months to update the public about the breach. In Paypal’s instance, it concluded its investigations on Dec. 20. and updated users on Jan. 18.
According to the GDPR rules for reporting personal data breaches, affected companies must report any breach within 72 hours. Fortunately for PayPal, it’s headquartered in the US. Here, reporting laws for such incidents differ from state to state and are not subject to GDPR. Often, these state laws don’t put any concrete time limit on reporting.
PayPal Credential Stuffing Attack Was Avoidable with the Right Security Measures

Source: Unsplash
As of yet, the attackers haven’t used the compromised data for any shady activities or transactions. Still, the data is likely to surface on some darknet forums sooner or later. PayPal has confirmed that none of its databases were breached.
As per the notification sent to affected account holders: “On December 20, 2022, we confirmed that unauthorized parties were able to access your PayPal customer account using your login credentials. We have no information suggesting that any of your personal information was misused as a result of this incident, or that there are any unauthorized transactions on your account. There is also no evidence that your login credentials were obtained from any PayPal systems.”
As recommendations to the affected account holders, PayPal suggested users change their passwords across platforms. The company further recommended that users ensure any new passwords are strong and complex. The online payments provider also recommends enabling 2FA across web services, particularly for financial transactions. Lastly, affected accounts should also take advantage of the identity monitoring services that PayPal offered post-incident and periodically check up on credit reports.
Credential stuffing and phishing attacks are on the rise. According to an F5 Labs Research report, credential stuffing and phishing attacks accounted for 50% of all publicly disclosed US data breaches between 2018 and 2019. The information cybercriminals steal from such attacks fuels the dark web economy. And malicious actors are always looking for stolen data to launch fresh attacks.
Credential Stuffing and Compromised Passwords

Source: Unsplash
Financial institutions have always been prime targets for cybercriminals. Stolen user credentials offer cybercriminals an easy entry route to instigate phishing campaigns or other nefarious activities. Massive lists of user/password pairs are readily available on darknet forums for low prices. Since users typically reuse the same basic passwords across various devices and services, they leave themselves open to threat actors with access to these lists.
That said, favorable security developments are underway, like passkeys replacing passwords. Passkeys could signal an end to an issue that has plagued business owners, government departments, and individuals—password management and authentication verification. In October 2022, PayPal became one of the first companies to make passkeys accessible to the public. However, this support is currently limited only to the US and iPhone, iPad, and Mac users.
Passkeys, as cryptographic pairs, can replace passwords completely, as they’re more secure and easy to use. The decryption key remains on the user’s device, barring threat actors from entry, even if a third-party service is compromised. With the introduction and widespread adoption of such a technology, username/password pairs leaked online will become a thing of the past.
As it stands now, password management is a resource-intensive process for business owners and network admins. Instead of making sure passwords are complex, changed regularly, and 2FA services enabled, passkeys forego such time-intensive considerations. This frees up network admins and business owners to give more attention to defending against the many other attack vectors deployed by cybercriminals.
The Severity of Authentication Fraud Operations
Despite best efforts, more firms are subject to data breaches through authentication fraud. It’s only a matter of time before the information cybercriminals harvested from these 35,000 PayPal accounts ends up for sale on the darknet forums, providing tinder with which to fuel more credential-stuffing operations.
The only viable solution here is the wide-scale and mandatory implementation of passkeys. Despite its simplicity, 2FA remains effective to a degree in thwarting such attacks.
Just last year, it was demonstrated how easy it is to employ publicly available username/passwords list in such attacks. A government watchdog used a software rig to crack passwords of accounts in a government department within 15 minutes. The username/password model is obsolete as a means of authentication security. Plus, password management is an annoyance for both businesses and individuals.
Credential stuffing operations on sites such as PayPal will continue to increase until businesses start to enforce effective solutions. While the transition to passkeys is underway, in the meantime, a well-implemented 2FA remains the best authentication procedure out there.



