If you would like to read about ScriptLogic’s product Desktop Authority please go to Product Review: Desktop Authority.
Product: ScriptLogic’s Active Administrator
Product Homepage/Request an Eval: click here

If you manage a Windows network, you know that Active Directory is at the same time one of the best and one of the most frustrating components Microsoft has ever given us. It’s a powerful and complex database that gives us incredible flexibility in managing users, computers and resources – but navigating its structure with the standard Microsoft tools and maintaining security on its objects can be time consuming and tedious, especially in the enterprise environment.
Managing Active Directory “out of the box” requires the use of several different administrative tools built into Windows 2000/2003 server operating systems. With the release of the Group Policy Management Console (GPMC), Microsoft took a step in the right direction toward centralized management, but there’s still a lot to be desired.
Luckily, there are third party tools that can make Active Directory administration easier. We installed the evaluation version of ScriptLogic’s Active Administrator, which is billed as an enterprise-level AD management and auditing solution, and gave it a try on our test network. Here are our impressions of the product.
Download and installation
The download was quick and relatively painless. You do have to create a download account, which means filling out a form with your name, company name, address, phone number, etc. Once that’s done, you log onto the ScriptLogic site and the software downloads as a 45.4 MB zip file that contains two setup files in .MSI format. The AAServerSetup file installs the Active Administrator program on the server, and the AAConsoleSetup file installs the management console for remotely administering the program.
ScriptLogic gives minimum system requirements as a Pentium 600MHz or faster processor, 256MB of memory, 50MB of disk space and screen resolution 1024×768 on Windows 2000 or later. We installed Active Administrator on a 3GHz system with 512MB of RAM, running Windows Server 2003.
You have the option of doing a complete or custom installation. Active Administrator can install MSDE 2000 or you can use an existing SQL server. MSDE is installed by default, so if you have a SQL server you want to use, and don’t want MSDE installed, you need to select the Custom option and deselect it, as shown in Figure 1. Note that if you use a SQL 2000 server, it needs to use mixed mode authentication.
Figure 1: Deselect MSDE if you want to use your existing SQL server
You can also change the installation directory if desired. Clicking the Space button will show you which volumes on your disk(s) have sufficient available space to install AA (144 MB is required). We liked this little feature, since it prevents you from going through the whole setup routine only to discover you don’t have enough space on the chosen partition. We also like that the AA installer can install MSDE for you. We’ve worked with other products that require you to go out and get it and install it yourself.
We experienced one quirk during the “Installing” portion of setup: although we could hear and see disk activity, no progress was shown on the Status bar for several minutes, making us wonder if there was a problem. Eventually, however, another dialog box popped up, informing us that MSDE was being installed and configured, and the installation proceeded swiftly after that. You’re asked to type a path to a shared folder where the AA data will be kept. You can create a new folder here by specifying a folder that doesn’t exist. By default, this share has permissions set to Full Control for Everyone, and you’ll probably want to change that, but we like that a security warning pops up to let you know this condition exists.
A database wizard helps you create the database, and then you configure the Group Policy History service, Active Template Auto-Repair service, and Backup service. For each, you must add domains and specify a user account to log on with. Note that you’ll need to specify the domain membership in the account name (e.g., mydomain.com\joeuser). We would have preferred a way to enter this info once if you want to use the same domain and account for all three. We did like that you can make a backup of the domain immediately, during this setup process, if you want.
Since there are many options to configure during the setup process, we recommend that you consult the Active Administrator Getting Started Guide (which you can find in the AA menu or on the web) to help guide you through the steps.
Once the installation is finished, you can install the Administrator console on workstations you’ll use to administer AA. We installed it on a Windows XP computer and, for kicks, decided to try installing it on a Windows Vista (Beta 2) workstation. Rather than the usual dialog box asking for administrative credentials when you install a program on Vista, we got a dialog box notifying that “the system administrator has set policies to prevent this installation.” The console installed on XP without a problem.
We were surprised that the console is not installed automatically on the server. You need to install it there too. Of course, many administrators prefer to manage AD from their workstations rather than the server console, so it makes sense to not clutter up the server with yet another program if you don’t need it.
Post-installation configuration
According to the Getting Started guide, the first thing you need to do after installation is to set up a security event database if you want to be notified of changes to Active Directory. The really cool thing about this feature is the way it works in conjunction with the Group Policy History service, to allow you to immediately find out about changes to GPOs and roll back to an earlier version of the GPO to undo those changes if you like.
To set up the security event database, you choose Create Auditing Database from the Active Administrator programs menu. The wizard that appears can be used to create a new database or remove, modify or manage an existing database. This is the same wizard encountered during installation. After you create the database, you have to edit the Default Domain Controller Policy. You can do this using either the Active Administrator console or the Active Directory Users and Computers MMC.
To configure the Event Monitoring service, you use yet another utility, the Event Configuration Utility. Every time you open it, you’ll have to go through the evaluation agreement process again if you’re using an eval version. The top tab shows a list of event definitions. There’s an “Enabled” checkbox to the left of each event name. Although it may not be clear at first glance, this box determines whether email notification is enabled for that particular event. You can enter different email addresses to be notified, depending on the event, as well as addresses to be notified of all events (global notifications).
With this utility, you can also find the domain controllers that have the monitoring service installed, and install it on those that don’t have it, which is a handy feature. Finally, you use the Event Configuration utility to configure collection options. This includes SMTP server information, limits for issuing alerts and parameters for collecting events. You can also select to create a log file to log information about collection (this is not enabled by default). You can start or stop the monitoring service from the “Install DC Agents” tab, but the buttons to do so are marked with the symbols for Start (or Play) and Stop that you’ll find on a DVD player or media player, as shown in Figure 2. Their functions might not be immediately obvious to every administrator. We’d have preferred more obvious text labels saying simply “Start” and “Stop.”
Figure 2: You stop or start the monitoring service using the “media player” buttons at the bottom
You also use this utility to view the status of collection monitors, and to load new event definitions files when they become available.
Using Active Administrator
On the server on which AA is installed (and on which you’ve also installed the console), you’ll find several selections in the Active Administrator menu (Start | All Programs | ScriptLogic | Active Administrator), as shown in Figure 3.
Figure 3: Several choices appear for Active Administrator in the Programs menu
When you open the console for the first time, you’ll be prompted to enter the path to your license file or indicate that you’re evaluating the software. The trial version works for 30 days. If you have a license file, it will have a .lic extension.
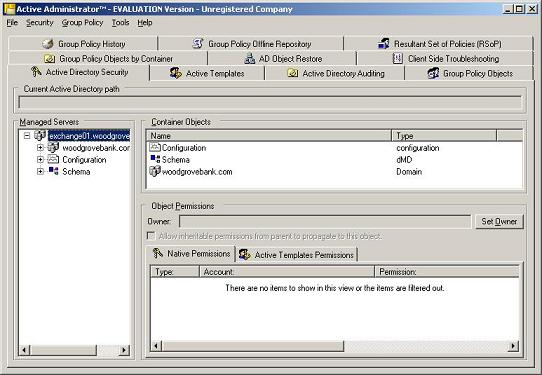
The AA console looks a little overwhelming at first. It contains several panes and many tabs, as shown in Figure 4.
Figure 4: The AA console strikes us as a little “busy”
If you thought you were finished configuring, think again. Before you can start using AA, you may need to configure the console to point it to the location of the Group History and the security event database. These configurations are done on the Group Policy History tab and the Active Directory Auditing tab, respectively.
Now, what do you do with all the rest of those tabs? Let’s take a look at them, one at a time.
- Active Directory Security: Here you see a list of managed servers and container objects. It’s very easy to determine what permissions each user or group has to AD objects, with tabs for both native permissions and Active Templates permissions.
- Active Templates: This is where you apply Active Templates to set permissions easily. You can create and edit templates as well.
- Active Directory Auditing: This lets you track and generate reports showing what’s being done to AD and by whom. You can filter the information by date range, user(s), event(s), server(s) and descriptions.
- Group Policy Objects: Through this interface, you can edit any of your GPOs from a centralized location, back them up and restore them, and add them to the off-line repository. You can get reports on GPO settings, GPO affected registry keys and a domain GPO summary. You can even create new GPOs here.
- Group Policy Objects by Container: Here you can view group policies by OU or site and see links.
- AD Object Restore: This is where you restore AD objects that have been backed up, without having to reboot into AD restore mode. You can also retrieve passwords or create new passwords when you restore.
- Client Side Troubleshooting: This is a very handy tool that lets you connect to client computers and make sure that policy changes have really been applied.
- Group Policy History: This “previous versions” feature lets you compare the current version of a Group Policy with the previous one and roll back if necessary.
- Group Policy Offline Repository: By adding GPOs to the offline repository, you can edit them without affecting your production network.
- Resultant Set of Policies (RSoP): You can use this tool to generate a calculation of how Group Policies will be affected when you make changes, applying it to the offline repository so that your production network isn’t changed.
Additional tools
Other tools included with Active Administrator include the Forest Prep Utility, which can be used to configure password recovery (you need to be running Windows Server 2003 SP1 or higher to restore passwords), the Object Level Backup/Restore Configuration tool, and the Active Template Repair Configuration utility. A 93-page User Guide in PDF format is also included, along with the Getting Started Guide we mentioned earlier. If you want to take a look at the User Guide prior to installing AA, you can view it on the web.
Summary
The Active Administrator package is a very comprehensive set of tools for managing the Windows Active Directory. Some may find it almost too comprehensive, at least until they become acquainted with it. Initial configuration is a somewhat daunting task, and requires the use of several different utilities. At first we wondered why all these tasks couldn’t be done from within a single utility. However, after working with AA for a while, we decided putting configuration tasks that are only performed one time (or infrequently) in individual utilities is probably preferable, as it keeps the main AA console interface from being even more jam-packed with options than it already is. Separating the functions also works well in an enterprise environment where different components of AA are installed on different servers.
There were some usability issues, such as buttons and fields whose purposes weren’t at all clear from the interface itself. We had to consult the documentation often. The Help menu option was less than helpful in some cases. For example, when you click Help in the Event Configuration Utility, the only choice you have is “About …” and if you make the mistake of clicking it, you’ll be nagged to apply a license file (or tell the software that you’re evaluating it) yet again. However, we were very impressed with the thoroughness of the Getting Started guide; it was a godsend as we navigated through the configuration process.
There are some very neat features that make this a worthwhile investment. We like the self-healing templates, and the email notification that goes with it. We also really like the ability to edit Group Policy offline; that takes a lot of the stress out of making changes to GPOs. The backup and restore function will be welcomed by any administrator who’s ever had to do an authoritative restore on a domain controller. We also really appreciated the fact that ScriptLogic lets you request additional time to evaluate the product if the 30 day trial period isn’t long enough.
Despite the little annoyances (and what software package doesn’t have a few of those?), we give AA a 4.25 rating on a scale of 1 to 5.
WindowSecurity.com Rating: 4.25 / 5
Get information about Active Administrator
If you would like to read about ScriptLogic’s product Desktop Authority please go to Product Review: Desktop Authority.