If you missed the other parts in this article series please read:
- Publishing Exchange Client Access with ISA 2006 – The Complete Solution (Part 1)
- Publishing Exchange Client Access with ISA 2006 – The Complete Solution (Part 2)
Create Web Listener
Before creating the Web publishing rule, we must first specify a Web listener to be used.
- In the console tree of ISA Server Management, click Firewall Policy. On the Toolbox tab, click Network Objects, click New, and then select Web Listener. Type a name for the Web listener. For example, type Exchange FBA.

Figure 1
- On the Client Connection Security screen, select Require SSL secured connections with clients.

Figure 2
- On the Web Listener IP Addresses, Listen for requests on these networks select Internal, since we have only one network interface.
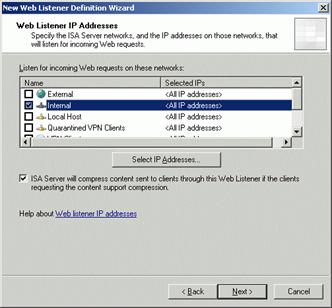
Figure 3
- Click Select Certificate and choose the certificate previously installed on the ISA Server. Click Next.

Figure 4

Figure 5
- Select HTML Form Authentication for forms-based authentication and select the appropriate method that ISA Server will use to validate the client’s credentials. We’ll use LDAP (Active Directory).

Figure 6
- Leave the default setting to enable SSO and type your DNS name.

Figure 7
- Review the selected settings, and click Finish to complete the wizard.
- Since we want our users to type in a simple URL without HTTPS (ISA will do the redirection), we must now modify the Web Listener just created, in order to provide access to HTTP. Right click the web listener and select Properties. Click Enable HTTP connections on port: 80 and then select Redirect all traffic from HTTP to HTTPS. This will allow our users to make the connection without explicitly typing the https portion of the URL.

Figure 8
ISA Server Rules
- To create an Exchange Web client access publishing rule, in the console tree of ISA Server Management, click Firewall Policy. On the Tasks tab, click Publish Exchange Web Client Access. Type a name for the rule. For example, type Exchange Web Client Publishing.

Figure 9
- Select the proper version of Exchange and select the desired Web client mail services. For Exchange 2003 you can choose all the methods in one rule; for Exchange 2007 you must create separate rules for each access method.

Figure 10

Figure 11
- Select Publish a single Web site or load balancer.

Figure 12
- Select Use SSL to connect to the published Web server or server farm.
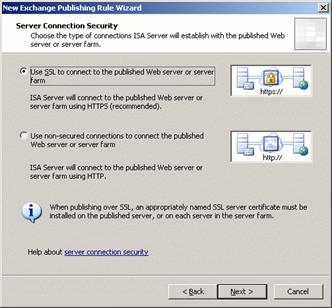
Figure 13
- Type the internal FQDN of the Exchange Client Access server. The internal site name must match the name of the server certificate that is installed on the internal Exchange Client Access server. If you cannot properly resolve the internal site name, you can select Use a computer name or IP address to connect to the published server, and then type the required IP address or name that is resolvable by the ISA Server computer. You can use whatever approach you like: use the same internal and external site name, or differentiate them. If you use different names, you’ll need 2 different certificates.

Figure 14
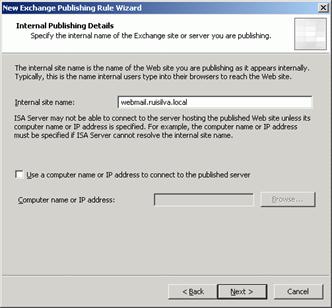
Figure 15
- Type the (external) domain name that you want ISA Server to accept the connection for. This must match the FQDN of the certificate selected when creating the Web listener.

Figure 16
- Select the Web listener you created previously.

Figure 17
- On the Authentication Delegation page, select Basic Authentication.

Figure 18
- Select the user set approved to access this rule (All Authenticated Users). If you later have problems with this rule, to troubleshoot it, start by modifying the User Set to All Users. If it works, it might indicate that there is an issue with LDAP authentication, which was set in the previous part of this article.

Figure 19
- Review the selected settings and click Finish to complete the wizard. Click the Apply button in the details pane to save the changes and update the configuration.
- If you are using different internal and external names, for RPC over HTTP(s) to work you must make a modification in the publishing rule. Right click the rule, select Properties, go to the To tab and deselect Forward the original host header instead of the actual one (specified in the Internal site name field).

Figure 20
Redirection
We already saw how to enable HTTP to HTTPS redirection in the Web Listener creation process. Now it’s time to drop the /Exchange or the /owa from the URL. If we were using ISA Server 2004, this would be done by including a special path mapping translating the root path “/” to the special Exchange path “/Exchange\”. Unfortunately, with ISA Server 2006 this is no longer possible because it generates the Event ID 21177.
You have two options to accomplish this:
- Include the root path “/” in the OWA web publishing rule and use HTML code on the front-end to do the redirection.
- Use a Deny Rule on the ISA Server that performs the redirection.
I prefer the former, so I’ll explain the steps involved.
- In the ISA Firewall console, click the Firewall Policy node in the left pane of the console. In the Task Pane, click Publish Web Sites. On the Welcome to the New Web Publishing Rule Wizard page, enter a name for the rule. In this example, we’ll name the rule OWA Folder Redirection and click Next.
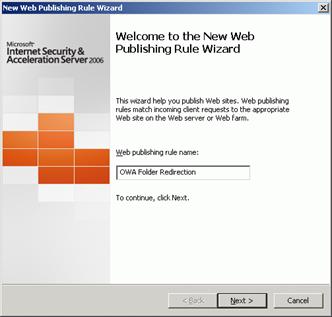
Figure 21
- On the Select Rule Action page, select the Deny option. All connections matching the parameters we set in this rule will be denied. Click Next.

Figure 22
- On the Publishing Type page, select the Publish a single Web site or load balancer and click Next.

Figure 23
- On the Server Connection Security page, select the Use SSL to connect to the published Web server or server farm. This option actually has no meaning in this scenario, since no connections will be forwarded by this Deny rule. Click Next.

Figure 24
- On the Internal Publishing Details page, enter the internal site name of the Exchange CAS/Front-End server. Click Next.
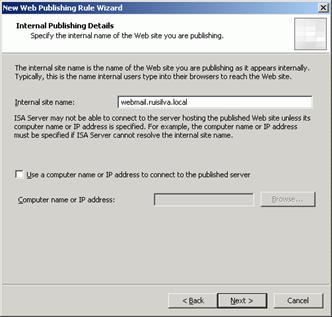
Figure 25
- On the Internal Publishing Details page click Next.
- On the Public Name Details page, enter the public name. Click Next.

Figure 26
- On the Select Web Listener page, click the down arrow on the Web listener drop down list and select the listener we use for the Exchange publishing rule. Click Next.

Figure 27
- On the Authentication Delegation page, accept the default entry, No delegation, and client cannot authenticate directly. There’s no need for the client to authenticate in this scenario, since we want the connection to be automatically redirected for everyone.

Figure 28
- On the User Sets page, remove the All Authenticated Users entry. Click the Add button. In the Add Users dialog box, double click the All Users entry and click Close. Click Next. You’ll see a warning that you can safely ignore.
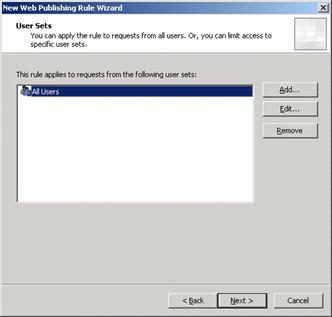
Figure 29

Figure 30
- Click Finish on the Completing the New Web Publishing Rule Wizard page.
- Double click the OWA Redirect rule we have just created. Go to the Action tab and put a checkmark in the Redirect HTTP requests to this Web page checkbox. Enter the complete URL of the Exchange OWA in the text box (https://webmail.ruisilva.org/exchange). Click OK.

Figure 31
- Make sure that the Deny rule is below the Exchange Web Client Publishing allow rule, as seen in the figure below. If it is not, use the up down arrow buttons in the MMC button bar to get the rules in the correct order.

Figure 32
- Click Apply to save the changes and update the firewall policy. Click OK in the Apply New Configuration dialog box.
Testing the Solution
In order to test the solution, use a computer outside the internal network, open a browser and at the address bar type the URL of the external Exchange public name (webmail.ruisilva.org).

Figure 33
If everything is working, you’ll be presented with the HTML form authentication, and after a successful logon, the Outlook Web Access page will appear, as illustrated in the pictures below.

Figure 34

Figure 35

Figure 36
To test RPC over HTTP(s) / Outlook Anywhere, make sure the Outlook profile is configured correctly to support this access method. Next, run Microsoft Outlook and verify that you can connect to your mailbox server. To confirm that you are using HTTPS, hold the CTRL key, right click the Outlook connection icon on the Taskbar and select Connection Status…

Figure 37

Figure 38
Conclusion
ISA Server 2006 introduced some new features and publishing wizards that can make the task of publishing Exchange much easier. Nevertheless, there are certain aspects and scenarios that are still difficult to find the right solution for.
The scenario I used in this series of articles is the most common I find with my customers. Hopefully it is the same in your case, so now you have a complete and detailed solution to publish Exchange 2003/2007 client access.
If you missed the other parts in this article series please read:
- Publishing Exchange Client Access with ISA 2006 – The Complete Solution (Part 1)
- Publishing Exchange Client Access with ISA 2006 – The Complete Solution (Part 2)
Related Links
Publishing Exchange Server 2003 with ISA Server 2006
Publishing Exchange Server 2007 with ISA Server 2006
Publishing Exchange 2007 OWA with ISA Server 2006
Outlook Anywhere 2007 with ISA Server 2006
ISA Firewall Publishing OWA and RPC/HTTP with a Single IP Address
Using ISA Server 2006 with Exchange 2007
ISA Server 2006: Installing ISA 2006 Enterprise Edition (beta) in a Unihomed Workgroup Configuration

