If would you like to read the first part in this article series please go to Publishing Microsoft SharePoint 2010 with Forefront TMG and different authentication options (Part 1).
Let’s begin
In the first article I gave an overview of the authentication options in Microsoft SharePoint Server 2010 and Microsoft Forefront TMG and how to set the different options. Then, we started publishing Microsoft SharePoint Server 2010 with the Standard publishing wizard of Forefront TMG and configured the SharePoint Server 2010 to listen on the HTTPS port. The second part of this article will explain how to change the authentication settings on the Forefront TMG Server to the following:
- KCD (Kerberos Constrained Delegation)
- SSL Client Certificate Authentication
- No Delegation / authentication at the TMG Server

Get your copy of the German language “Microsoft ISA Server 2006 – Das Handbuch”
Before we start with the different authentication options let us change the HTTPS-to-HTTP bridging of Forefront TMG to SharePoint HTTPS-to-HTTPS bridging. In the first article we requested a certificate from our internal Certification Authority for SharePoint so now we can change the Bridging on Forefront TMG as shown in the following screenshot.

Figure 1: Change HTTP to HTTPS redirection
Kerberos Constrained Delegation
Kerberos Constrained Delegation (KCD) is a primary functionality of the Kerberos protocol introduced in Windows Server 2000 domain environments for authenticating users, services and computers. If a published Web server like the SharePoint needs to authenticate a user that sends a request to it and if the Forefront TMG computer cannot delegate authentication to the published Web server by passing user credentials to the published Web server or impersonating the user, the published Web server will request the user to provide credentials for a second time. ISA Server 2006 introduced support for Kerberos constrained delegation to enable published Web servers to authenticate users by Kerberos, after their identity has been verified by the ISA Server using a non-Kerberos authentication method. When used in this way, Kerberos constrained delegation eliminates the need for requiring users to provide credentials twice. To get Kerberos Constrained Delegation to work, we must change the Authentication Delegation method to Kerberos Constrained Delegation in the Forefront TMG Management console for the SharePoint publishing rule. The Service Principal Name (SPN) is host/InternalDNSFQDN of the SharePoint Server.

Figure 2: Using KCD
Next, we must change the Client Authentication Method to HTTP-authentication with Integrated Authentication.

Figure 3: Integrated HTTP authentication
To get KCD (Kerberos Constrained Delegation) working, the Sharepoint Server must trust the Forefront TMG Server for Kerberos Delegation. Open the Active Directory User and Computers console, make sure that the “advanced Feature” view is activated, navigate to the Forefront TMG computer account, select the Delegation tab and specify the SharePoint Server for the Service type HOST.

Figure 4: The Sharepoint Server trusts Forefront TMG for delegation
SSL Client Certificate authentication
Now, we want to change the authentication between the Forefront TMG Server and the client to SSL Client Certificate Authentication. First, we need to change the allowed Client Authentication Method to SSL Client Certificate Authentication. If the client is not able to authenticate with the SSL client certificate, you can use different fallback authentication methods like Basic, Digest and Integrated.

Figure 5: SSL Client Certificate Authentication
Next, the client which must access the SharePoint Server from the Internet must have a user certificate installed into the local certificate store of the user account. There are some ways how to enroll the certificate to the client. If you have a large number of clients you can use the certificate auto enrollment with Active Directory and Group Policies, but if you only have few clients, then you are able to request the certificate manually. Start an empty MMC, add the certificate snap-in for the local current user account and request a user certificate based on the certificate templates provided by your internal Certification Authority (CA).

Figure 6: Request a certificate for SSL client certificate authentication
After the user account has received the correct certificate we are able to test the connection. Open the SharePoint website published by Forefront TMG and instead of entering the correct username and password, you now only have to select the issued certificate.
Note:
This is not two-factor authentication. Using certificate authentication on its own is a secure way only when giving access to known clients.

Figure 7: Test access to the Sharepoint Server with a client certificate
Enforce authentication only at the SharePoint Server
For some reasons it might be necessary to only let the SharePoint Server authenticate the client requests from the Internet. You can do this if you change the client Authentication method in the SharePoint Listener on Forefront TMG to “No Authentication”.

Figure 8: NO authentication at Forefront TMG
In addition we must change the Authentication Delegation to “No delegation, but client may authenticate directly” in the SharePoint publishing rule at the Forefront TMG console as shown in the following screenshot.
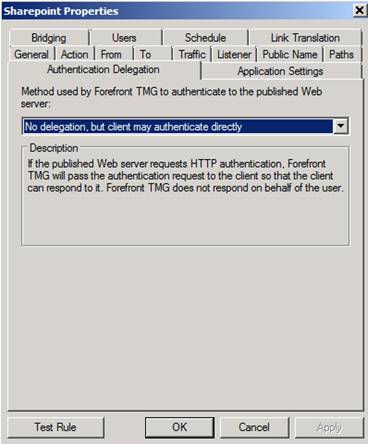
Figure 9: Let SharePoint Server 2010 do the authentication
Now, every authentication request will be forwarded to the Microsoft SharePoint Server 2010 without any pre authentication on the Forefront TMG Server.
Conclusion
In this second article about Microsoft SharePoint 2010 publishing, we configured the different authentication options in Microsoft Forefront TMG working together with Microsoft SharePoint Server 2010. We talked about other Forefront TMG publishing options for Microsoft SharePoint Server 2010 like Kerberos Constrained Delegation (KCD), SSL Client certificate authentication and redirecting the authentication directly to the Microsoft SharePoint Server.
Related links
- Kerberos Constrained Delegation in ISA Server 2006
- Plan authentication methods (SharePoint Server 2010)
- Using Kerberos for SharePoint Authentication
- Understanding SharePoint 2010 Claims Authentication
- Legacy – Configuring SharePoint publishing
- Choosing Between Forefront TMG or Forefront UAG for Publishing Scenarios
- What every SharePoint administrator needs to know about Alternate Access Mappings (Part 1 of 3)
If would you like to read the first part in this article series please go to Publishing Microsoft SharePoint 2010 with Forefront TMG and different authentication options (Part 1).



