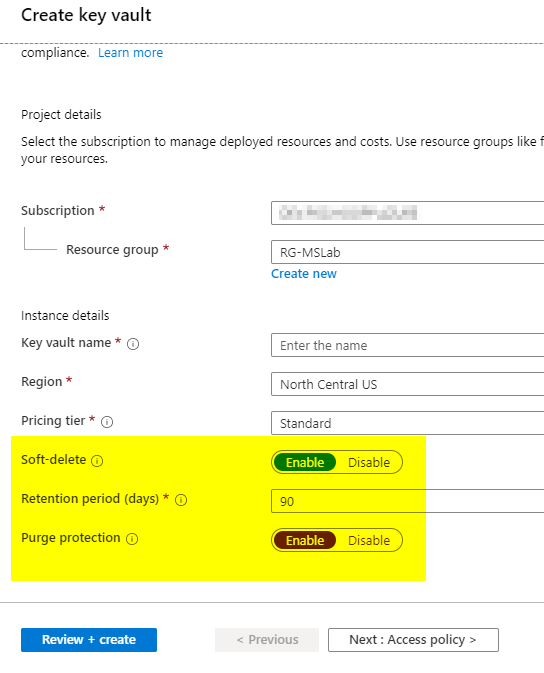
Azure Key Vault is vital for most organizations and the security controls around it must be tightened as much as possible. There are two features available during the creation of the resource that the cloud administrator should be aware of. They are purge protection and soft-delete. When we have those options configured, we cannot reuse Key Vault and Key Vault objects (secrets/keys and certificates) names before the period defined on the policy is reached.
The soft-delete allows the restore of entire vaults and vault objects for 90 days (maximum numbers of days).
The purge protection is not enabled by default, but it forces that any deleted object cannot be purged from Azure, and they will remain in that status for 90 days (maximum number of days).
The process to restore is done through PowerShell and there is no functionality at this time in the Azure Portal.



