If you would like to read the first part in this article series please go to:
- Rights Management Server and Exchange 2010 (Part 1)
- Rights Management Server and Exchange 2010 (Part 2)
- Rights Management Server and Exchange 2010 (Part 3)
- Rights Management Server and Exchange 2010 (Part 5)
- Rights Management Server and Exchange 2010 (Part 6)
- Rights Management Server and Exchange 2010 (Part 7)
- Rights Management Server and Exchange 2010 (Part 8)
Introduction
Welcome to the fourth part of this article series looking at the integration between Exchange 2010 and Rights Management Server (RMS). So far in parts one to three we have covered the necessary background work such as the installation pre-requisites and then gone on to install and configure RMS for Exchange integration. Let’s now continue the article by looking at our configuration testing options.
Configuring Testing
Having made all the required configuration changes that you saw in part three, how can we tell that the configuration is operating correctly other than trying the various RMS features in Exchange 2010? Fortunately, the Test-IRMConfiguration cmdlet can be used to do exactly this. The required parameter for this cmdlet is the Sender parameter, which we configure with the SMTP address of the sender that we would like to test. Since the administrator account has been configured with an SMTP address by default, let’s test our configuration using the administrator’s SMTP address with the following command:
Test-IRMConfiguration –Sender [email protected]
You can see the results of running this command in Figure 28. Note how the test process highlights the various configuration areas and how they pass the test; such configuration areas include the SCP configuration, the availability of the various certificates, the availability of the RMS templates, and so on.
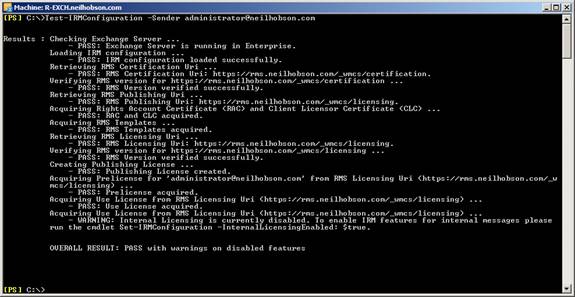
Figure 28: Results of the Test-IRMConfiguration Cmdlet
Right at the bottom of Figure 28 we can see that the overall result of the test is a pass, but warnings have been generated for some disabled features. Immediately above this information, we can see that a warning has been generated for the internal licensing component and we are advised that we must run the Set-IRMConfiguration cmdlet to enable IRM features for internal messages. The warning text gives us the full command to run:
Set-IRMConfiguration –InternalLicensingEnabled $true
This command enables the IRM features for messages that are sent to internal recipients. Without performing this additional configuration, my testing showed that it was not possible to see the RMS permission button in OWA. We will be covering the topic of OWA and RMS integration very soon but for the moment let’s take the time to re-run the Test-IRMConfiguration cmdlet to ensure that we have a full pass for each test. The results are shown in Figure 29.
As you can see the Test-IRMConfiguration cmdlet is extremely useful and I therefore advise you to use this to confirm that your configuration is correct.

Figure 29: All Tests Pass
Using OWA With Rights Management Server
Previously in part three of this article you have seen that we needed to perform some additional configuration steps in order to use the RMS features from within OWA. Let’s now take a look at OWA and check that things are working correctly. Without the extra configuration steps having taken place, here’s what the users will see when composing a new message within OWA.

Figure 30: New OWA Message Without RMS Integration
As you can see from Figure 30, this is a perfectly normal new message template within OWA; there is nothing exciting going on here. Compare this to Figure 31 which has been taken after the additional RMS configuration required to support integration within OWA.

Figure 31: New OWA Message With RMS Integration
You will notice the additional toolbar button at the top, which is known as the permissions button. Selecting this button gives you the option to place the Do Not Forward restriction on this message. If this option is selected, the message is protected with RMS and a banner appears at the top of the message to confirm this fact, as shown in Figure 32. Notice how the banner also advises the sender that the recipients of this protected message will not be able to print the message or copy the message contents in addition to not being able to forward the message.
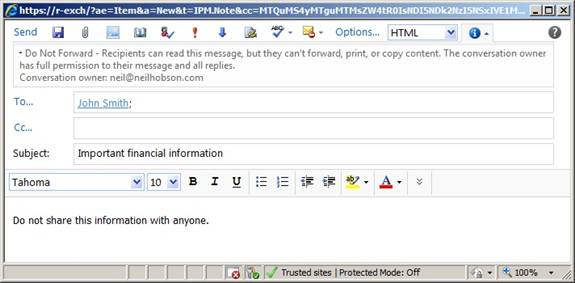
Figure 32: RMS Banner Information
At this stage, the message has not been sent. If the message is sent we expect that the RMS protection should remain in place and therefore the recipient will not be able to forward, print or copy this message. Let’s open the message and find out; the results are shown in Figure 33.

Figure 33: RMS Protected Message – Recipient View
Sure enough, the message has the Forward button greyed out, ensuring that the recipient cannot forward the message to someone else. Additionally, the printer button is also greyed and you should find that you cannot copy the text from the message, thus preventing you from pasting the text into another email or document. You will also notice that the message has a new icon when it is viewed in the inbox, as displayed in Figure 34. In actual fact, this icon will remain with the mail item and thus be viewable from all folders, such as Sent Items or other custom folders that you might create. The same principle of the restrictions icon applies to other message types, such as voicemails for example.

Figure 34: RMS Protected Message Icon
RMS Templates
You saw back in Figure 31 that a single RMS template is available to the end user and went on to see how this template gives the ability for the user to place restrictions on the message such that it cannot be forwarded. You might be wondering where this RMS template actually comes from. As it happens, Exchange 2010 ships with a single RMS template, namely the Do Not Forward template and it is this option that the users can select.
To obtain more details about this template, we can use the Get-RMSTemplate cmdlet as you can see from Figure 35.

Figure 35: Results of Get-RMSTemplate
As a result of using the Get-RMSTemplate cmdlet, you might assume that there is a corresponding New-RMSTemplate cmdlet but in actual fact there isn’t. RMS templates can be created but the process must be performed via the Active Directory Rights Management Services snap-in. We will be looking at this in a future part of this article.
Messages With Attachments
If a message includes one or more attachments, then those attachments are also protected in the same way that the message is. Furthermore, there has been an improvement made in Exchange 2010 Service Pack 1 that allows a user to view an IRM-protected attachment using Web-Ready Document Viewing. If you’re not familiar with Web-Ready Document Viewing, you can read more about the feature in an article of mine here; although this article was written for Exchange 2007 and not Exchange 2010, the principles are largely the same.
Consider Figure 36 where you can see that a user has used Web-Ready Document Viewing to examine the contents of a Microsoft Word document that has been attached to a message with the Do Not Forward RMS template applied.

Figure 36: Web-Ready Document Viewing and RMS Protection
Summary
Part four of this article has now been completed. In this article, we’ve focused on testing our RMS configuration and then gone on to look at how RMS integrates with OWA. In the next part, we’ll be taking a look at how we can enable or disable RMS integration and the various levels at which this can be performed. We will then cover Outlook protection rules.
If you would like to read the first part in this article series please go to:
- Rights Management Server and Exchange 2010 (Part 1)
- Rights Management Server and Exchange 2010 (Part 2)
- Rights Management Server and Exchange 2010 (Part 3)
- Rights Management Server and Exchange 2010 (Part 5)
- Rights Management Server and Exchange 2010 (Part 6)
- Rights Management Server and Exchange 2010 (Part 7)
- Rights Management Server and Exchange 2010 (Part 8)