Facebook’s data breach is a major roadblock on the road to the future, at least in terms of the idea of digitization of personal information. For the global marketing engine, the implications are massive. Here we were, rollicking along on the track to deeply engaging and personal knowledge of customers’ preferences. And here we are, staring at arguably one of the biggest business units ever facing years of litigation and reputation damage. It will be naïve of any organization to treat this event as mere news! The implications, lessons, and consequences will be as relevant and applicable for your startups, SMBs, and enterprises as it is for Facebook. The digitization of customer information, right from their consent forms to agree to your newsletters to their last order’s invoice, has been a major enabler of business productivity and efficiency. Also, this has enabled businesses to organize and analyze all the digitized information and bring out tremendous insights from the same. These insights help them to interact with the customer more effectively, improve the relationship, sell more, and in general, make the engagement more enjoyable for the customer. The result — more information, more documents, more data analysis, more insights, repeat. Of course, it all sounds like a win-win, until we decide to address the issue of customer data privacy and security. This is where management of customer documents becomes so important.
Customer documents management — What does it mean?
In the next sections of this guide, we’ll explore the strategic aspects of ensuring the privacy and security of customer documents.
End-to-end control over customer document security
Digitization of information, digital storage, and digital data transmission of data — these are the three stages of customer data management, and for all these, the responsibility of ensuring complete security rests squarely with the business.
- Envisioning the journey of information, from the point of creation to point of storage, is very important, and the first step you need to take.
- Next up, take stock of the existing information management systems in place, such as CRM tools, cloud-based data storage, and cloud-based Office and document management suites.
- Evaluate the range of data formats and monthly volume of customer document data, and choose a mix of platforms that can help you with the document management goals, without necessitating another purchase of a tool.
- You will need to think on lines of password complexity rules for document locking, encryption technologies for transmission of data, network security aspects, and access management and control across teams that use the customer documents.
Layer — The keyword to remember
In a world where a customer’s document is the equivalent of a bar of gold entrusted in your custody, it’s too risky to depend on a single layer of security to protect customer info assets. What you need is at least a dual-layer security cover (though higher the number of layers, better it is).
Consider how organizations from sensitive industries, such as finance, defense, medicine, and government, prefer to lock documents with passwords even while sharing them internally. The passwords can be dynamically generated from a database of customer information, using rules (such as, the first two digits of the recipient’s name, followed by the year of his/her birth, and then the first two digits of his/her mother’s maiden name). Then, these locked documents are sent over secured connections with encryption to make it triply certain that even if someone intercepts the data, they’ll not be able to make sense of it.
Invest in regular education and training of your customer support personnel
One of the most common causes of data breaches, particularly of customer information, is the lack of web security knowledge among customer support teams. To some extent, that’s because of the limited scope of process interaction of these users. No wonder users of this profile are the prime targets for hackers and information thieves.
These users are very close to the information databases holding the majority of customer documents, this is precisely where you need to focus your attention to deliver and enable education and training. The key areas of concern are — phishing, social engineering, clickbait, and fake calls. Running good simulations to expose your team to realistic scenarios can go a long way in preparing them to value customer documents, and to be ultra-cautious while dealing with potential spam and malicious messages.
Extend the security cover to the customer side
It’s human nature: Even if a customer’s documents are leaked because of carelessness on their own part, you might find yourself pulled into the storm. Also, any organization would rather invest 5 percent extra in its custom document security process efforts to ensure that the content remains secured than risk an unsavory situation around data leakage.
One of the proven effective methods to ensure that your organization remains covered against litigation risks related to customer document leakage because of an external factor is based on two factors:
Disclaimers
Clearly communicate that the customer must exercise caution in storing or sharing their documents, should delete them if not needed, or contact the organization’s service desk if they need assistance in handling their data.
Password protection
By default, add a password to every document, and explain to your customers why it is necessary and advisable. More on passwords in the next section.
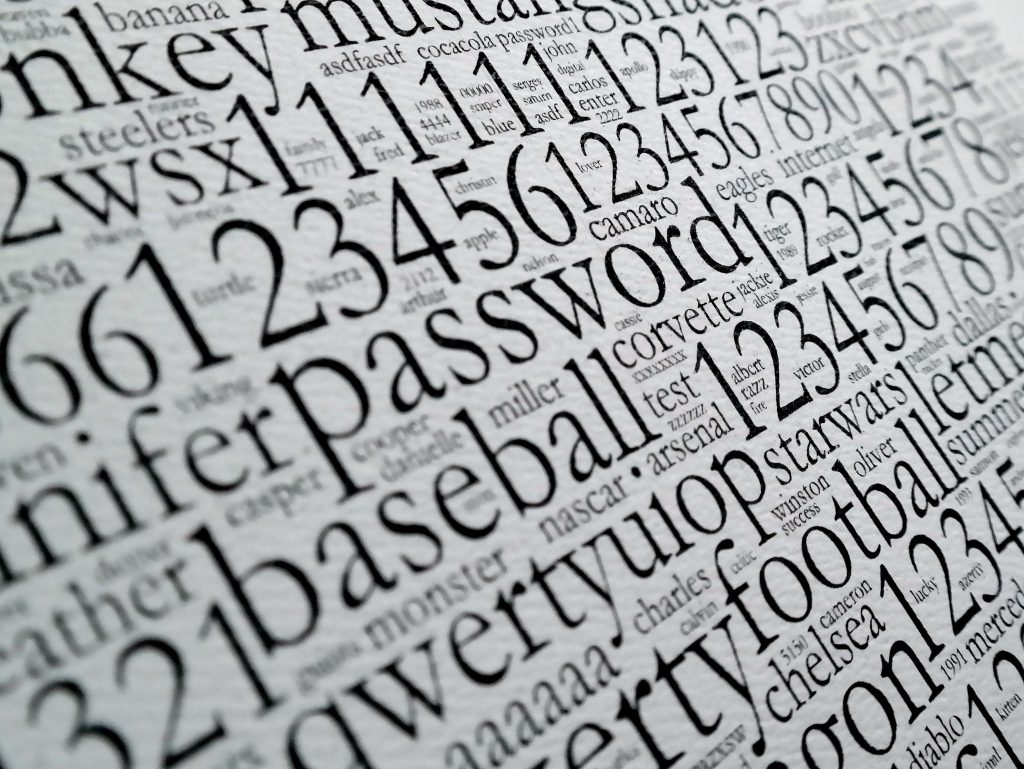
Implement strict password policies
Do you know — the kind of sophisticated password-cracking tools that cybercriminals possess can try out millions of possible combinations within seconds? Naive passwords such as name1234 (public information) and QWERTY (sequential keys) are cracked by the thousands every day. It’s only a matter of time before a weak password is cracked.
Unless, of course, if you can upgrade your password policy. For starters, ensure a minimum of eight characters, with a mix of alphanumeric and symbol characters, in both upper and lower cases. Next, ensure the passwords are updated every 90 days or sooner. Next, see to it that the password policy is implemented across all process that cuts through the customer document management ecosystem.
Apart from the five strategies discussed above, you could also embrace basic information management best practices for additional control and security. For instance, while sharing a document through your document collaboration software (such as Google Drive, OneDrive or Dropbox), ensure the info is shared via a link instead of sharing the actual document, share it only with as many people as really required, restrict actions such as edit and download, and put an expiration date on the validity of the link.
Safeguard these assets
Your customers’ data and documents are your responsibility; trust these five strategies to safeguard these assets.
Photo credit: Flickr / Blue Coat Photos



