The consensus among InfoSec professionals, especially those with cryptography expertise like Bruce Schneier, is that the SHA-1 hashing algorithm is obsolete. I have written numerous times on this issue for TechGenix, most notably in my article about modern cryptographic methods and their flaws. In that article I mention how a collision attack, “which capitalizes on two different hashes having the same output that deciphers the SHA-1 hash value,” is a major risk in SHA-1. In short, it can allow multiple malicious files to be accepted in place of legitimate ones, and this can theoretically be done on a broad scale with SHA-1.
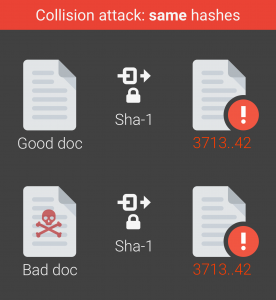
This was only theoretical until recently, as researchers in the Netherlands with Centrum Wiskunde & Informatica and also Google have officially, in their words, “broken SHA-1 in practice.” The method used involves PDF files, namely by creating a malicious SHA-1 digital signature on an illegitimate PDF file that can be accepted as a valid signature on a legitimate PDF file. In their extensive findings, the team provides a graphic (seen below), which shows how simple this collision attack is:
The team has named the attack, rather cleverly, “SHAttered,” and provided proof of the attack’s success in their findings. As Google stated in its blog post about the SHA-1 collision attack, “nine quintillion (9,223,372,036,854,775,808) SHA1 computations in total” were created to form SHAttered. While this seems rather large, any well-funded attacker can perform this attack even with these large computations, as Google estimates that it is “more than 100,000 times faster than a brute force attack.”
The SHAttered collision attack threatens numerous systems like HTTPS certificates, version control (Git), backup systems, software updates, and ISO checksums. The only way to protect against collision attacks, which are now truly possible by any well-trained attacker, is to move away from SHA-1. The researchers at CWI and Google recommend SHA-3 and SHA-256 as alternatives.
The main mission of the SHAttered project was to “cement that the protocol should no longer be considered secure.” While many tech companies like Google and Mozilla have taken considerable steps to phase out this hashing algorithm, others have not been so quick to move on this. If years of warning from cryptography experts have not been enough, let us hope this first truly applicable collision attack is enough.



