Cloud-based apps are a massive part of the modern enterprise’s IT infrastructure. With the move to the cloud, there is also a move to many clouds: enterprises typically employ several cloud providers. Of course, each cloud provider and app comes with its own login credentials. As every IT admin knows, end users don’t care to remember their passwords and keep on peppering and pestering service desks for account unlocks, new passwords, and similar access requests. Apart from hampering the smooth transition of workflow from one app to another, this also creates a nuisance for the service desk. Another direct negative outcome of this problem is the blatant sharing of passwords among end users, causing serious network vulnerabilities.

What’s the solution?
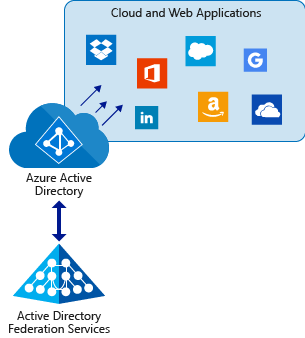
Single sign-on solutions (SSO) have come to the fore as a solution to this problem of logon management. It does so by empowering administrations to control authentication and access management at the back end. An SSO solution works by unifying all credentials for cloud apps, websites, and desktop applications into a single password for the end user, by syncing with an active directory. Single sign-on solutions help administrators control security policies, plug security gaps as they become visible, and achieve the perfect balance of productivity and security.
Let’s learn more about the best sign-on solutions for enterprises. Here are three that are ideal for enterprises looking to get rid of the problem of too many sign-on credentials for too many apps, for too many employees.
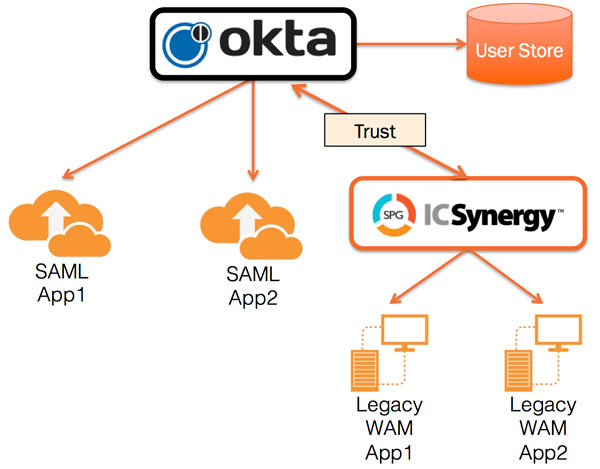
Okta Identity Management
Okta Identity Management offers highly effective SSO solutions. It integrates well with a large number of directory types, offers a user-friendly interface, and daily reporting. With a policy engine, it offers administrators complete control over the what, who, how, when, and where of access controls. Okta costs you about the same as most of its competitors, but scores well because of its amazing range of features. It works on all platforms and devices, offering complete remote access. Administrators can completely control the user-provisioning process using Okta. Multifactor authentication enables advanced security management, and you can set security policies to demand multifactor authentication under specific conditions.
EmpowerID
EmpowerID gives administrators full-fledged control over access management of all apps in a centralized and automated manner. Identity provisioning, termination, and management can be handled using EmpowerID’s neat and user-friendly interface. Consumer identity access management also helps you deliver your apps experience to customers. With EmpowerID, you can develop an enterprise-specific layer of authentication and user management for all your web apps and IoT technology interfaces. EmpowerID is mature enough to manage the complexity of technical implementations across industries such as finance, health care, and government.
Ping Identity
Following the market leaders closely is Ping Identity. It has Cisco, Boeing, and Comcast as its notable customers, along with close to 900 other enterprises. It differentiates itself from other SSOs by offering single sign-on for both on-premise and cloud-hosted apps, thus appealing to startups and fully grown enterprises equally. Ping Identity helps enterprises deliver seamless, fully secure access to all kind of apps (internal, as well as SaaS) across the enterprise, anywhere, and on any device. You can extend apps access to customers with limited privileges using this tool.
Apart from these sign-on solutions, let’s cover some more, with specific focus on cloud apps access over mobile devices. Before that, let’s understand why that’s necessary.
SSO for mobile
The modern enterprise is increasingly adopting mobile devices for application access. Mobile device-based app access is relevant for new technologies such as wearables, IoT, and smart TVs. This makes SSO for mobile apps a critical aspect of sign-on management for enterprises. Here’s a look at three mobile SSO solutions.
OAuth 2.0
Did you know that Facebook, Microsoft, and Twitter use OAuth 2.0? Here, the authentication is accomplished via a server that issues tokens from a known source. The token enables access to protected objects on HTTP servers. This methodology makes OAuth 2.0 perfect for public and cloud domain services. OAuth 2.0 originally emerged as an enabler of smooth resource authentication flow between PC and websites. One restriction is only one website can use OAuth effectively at a single time.
OpenID
OpenID overcomes the restrictions of OAuth 2.0 in terms of single-site application at a time. OpenID is also supported by Facebook, Google, Twitter, and Microsoft. With OpenID, users can use a single password for a basket of services, such as a single Google password for all Google apps. Enterprises can use OpenID along with OAuth to connect user accounts across desktop applications, web, and mobile apps, all using the same authentication. This also comprises APIs, third-party apps, off-shelf solutions, and custom apps.
OpenID with NAPPS
OpenID Connect and Native Application Profile (NAPPS) can be used to deliver seamless SSO for mobile apps. OpenID Connect is an extra layer that also comes with profile information over JSON packets. NAPPS is managed as an open-source project by OpenID.
How to choose the perfect SSO vendor
SSO options have been around for some years now. As you consider adopting one for your enterprise, make sure you confer with your IT stakeholders on these points:
- Do you retain sufficient control over core security policy settings and other core processes?
- Does the SSO support multifactor authentication?
- How well does the SSO integrate into existing directory types used by your enterprise IT?
- Is the user experience easy and intuitive?
- What’s the extent of tech support you can get without paying additionally from the vendor?
The market for single sign-on solutions is buzzing, with startups as well as mature SSO service providers looking to strengthen their client bases by offering flexible, secure, intuitive, and scalable solutions for enterprise customers. When you are ready for an SSO provider, negotiate well and map the best features and capabilities of the vendor with your organization’s access management and security requirements.
Photo credit: Pixabay




The single sign-on solution saves users time by allowing users to access all the services that are protected with the solution using one credential. You can also add single sign-on solution by LoginRadius of the list of SSO providers.