Product: Specops Password Policy
Product Homepage: click here
Free Trial: click here

Over the last few years, I have had a chance to review Specops Password Policy multiple times. Even so, the application continues to evolve, and so I decided to review it once again because I was curious about some of its new features. I am basing my review on version 7.2.
Installation process
I don’t want to spend a lot of time talking about the installation process, because I have covered it previously in some of the earlier reviews. Even so, I will tell you that I installed the client component and the administrative tools onto a Windows 10 VM that was running version 1903. I installed the Password Auditor and Blacklist Arbiter components onto a Windows Server 2016 VM and installed the Domain Controller Sentinel onto a domain controller.
As was previously the case, the installation process was simple and intuitive. The only extra component that I had to install was version 4.7 of the .NET Framework.
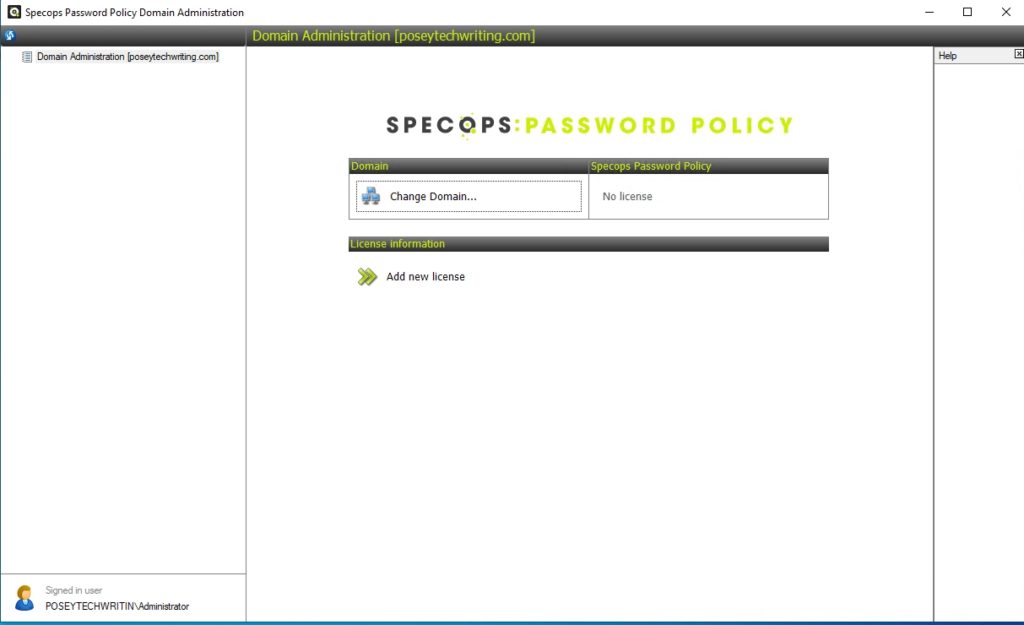
Once the installation process completes, there are a couple of simple tasks that must be performed to get Specops Password Policy ready to use. These tasks include specifying the domain and installing a license. You can see what this looks like in the screenshot below.
Specops password blacklist
With everything up and running, I decided to begin my evaluation by taking a look at the password blacklist features. The hosted blacklist existed in the previous version, but Specops has recently enhanced its functionality with the introduction of a downloadable version
In case you aren’t familiar with the blacklist, it is a tool that you can use to prevent users from using passwords that are known to have been leaked. The blacklist can be configured to check a user’s password whenever the user changes and/or resets it. If a user is found to be using one of the blacklisted passwords, they can be notified either by SMS text message or by email, as shown in the screenshot below.

As previously mentioned, one of the more significant enhancements that Specops has made to the blacklist feature in this version of Specops Password Policy is an option to download a list of passwords that are known to be vulnerable, as shown in the screenshot below. This list is essentially a subset of the hosted version. User’s passwords can be compared against this list to ensure that users are using secure passwords. The main difference between the downloadable list and the hosted version is that it allows new passwords to be checked at the time when they are changed, rather than after the password has already been changed.
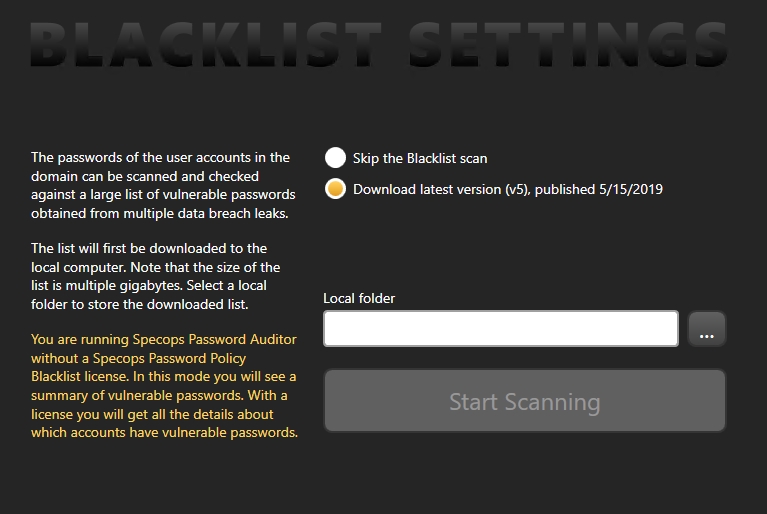
The most impressive things about the downloadable list is its sheer size and the fact that it allows for real-time evaluation of users’ passwords at the time of change. A password is typically only a few bytes in size. Even so, the list (which is divided into 257 separate files) is about 4.54GB in size, as shown in the next screenshot.

Length-based password aging
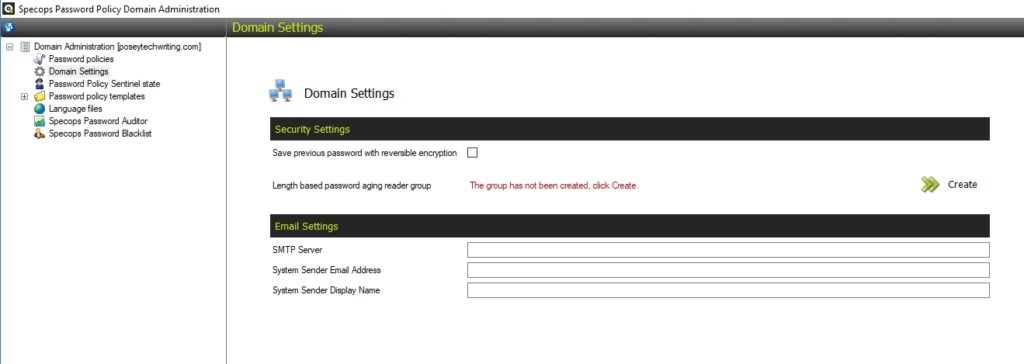
Another new feature that is definitely worth taking a look at is length-based password aging. The idea behind this feature is that administrators can encourage users to use longer passwords by rewarding them with less frequent password changes. Users who opt to use longer passwords won’t have to change their passwords as often. The setting used to enable length-based password aging is found on the Domain Settings screen. If you look at the screenshot below, you can see that there is an option to create a length-based password aging reader group. Clicking on this option causes the software to create a new Active Directory group named Specops Password Policy Custom Expiration Readers (the group is only required if you have a Specops Self-Service Password Reset solution).
The actual length-based password aging settings are found within the Password Policy Template, under the Password Expiration section. You can see the available settings in the next screenshot. When used in conjunction with Specops uReset, Specops’ password reset solution, users receive real-time feedback when a new password appears in the password blacklist. This removes user confusion when a password change fails.

When I created the screen capture shown above, I kept the default values, but you can change the settings to meet your own needs. In this case, the base expiration period is 180 days, and users can achieve 180-day password expirations by using passwords that are 20 to 21 characters in length. If, however, a user enters a 22- or 23-character password, the expiration period is extended to 210 days. If the user’s password is 24 or more characters in length, the password will be valid for 240 days.
You can customize the length-based aging by specifying the total number of levels that you wish to use, how many extra password characters are required for a user to reach the next level, and how many extra days a user gets when they go up a level. There is even an option to disable password expirations completely when a user reaches the highest level.
Finding accounts with leaked passwords
One more new feature that I want to talk about is a capability within the Specops Password Auditor that will allow you to figure out which accounts are using leaked passwords. This functionality works with the new downloadable password blacklist, and the auditor can help you to figure out if any of those passwords are currently being used within your organization.
Personally, I like the way that Specops decided to implement this new feature, because it doesn’t require you to jump through any new administrative hoops (although you will, of course, need domain admin permissions). when you run the Specops Password Auditor, it scans your Active Directory and then displays a series of reports outlining the auditor’s findings. The blacklisted passwords report is automatically displayed among the reports that already existed in the previous version of the auditor.
If you look at the next screenshot, you can see that the Specops Password Auditor includes reports outlining the use of blacklisted passwords, identical passwords, accounts with administrative privileges, accounts for which no password is required, accounts with expiring or expired passwords, password policies, password policy usage, and password policy compliance. All of these reports are clickable and can provide additional detail beyond what you see in the screenshot.

The verdict
Whenever I write a review for TechGenix, I conclude it by assigning the product a star rating. This rating ranges from 0 to 5 stars, with 5 stars being a perfect score. The last time that I reviewed Specops Password Policy, I gave it a score of 4.5 stars, which is a gold-star award.
Specops has made some nice improvements to Password Policy since the time that the previous review was written. I particularly like the idea of giving users more time between password changes as a way of rewarding those users for using longer passwords. As was the case before, I still found the installation and initial configuration process to be a little bit convoluted, but not overly difficult. I found myself having to consult the documentation several times while deploying and configuring the software but was always able to find what I needed within a reasonable amount of time.
So with all things considered, I have decided to give Specops Password Policy version 7.2 a score of 4.6, which is once again, a gold-star rating.
Rating 4.6/5


