 As the co-founder of Microsoft many years ago with my former colleague and friend Paul Allen, I’ve seen many developments in computer technology over the decades that followed. Some of the new technologies we developed have gone on to achieve success beyond our wildest dreams; others however have failed to grasp the imagination of the general public. As I’ve often said, however, it’s fine to celebrate success, but it is more important to heed the lessons of failure. And just as life is not fair (get used to it!), neither is business. And remember, technology is just a tool; in terms of getting the kids working together and motivating them, the teacher is the most important. That’s why I’ve created my new site for kids to look ahead into the next century and become leaders who empower others…
As the co-founder of Microsoft many years ago with my former colleague and friend Paul Allen, I’ve seen many developments in computer technology over the decades that followed. Some of the new technologies we developed have gone on to achieve success beyond our wildest dreams; others however have failed to grasp the imagination of the general public. As I’ve often said, however, it’s fine to celebrate success, but it is more important to heed the lessons of failure. And just as life is not fair (get used to it!), neither is business. And remember, technology is just a tool; in terms of getting the kids working together and motivating them, the teacher is the most important. That’s why I’ve created my new site for kids to look ahead into the next century and become leaders who empower others…
Hah, gotcha, didn’t I? I’m not Bill Gates, of course, and if you clicked on the above link you really weren’t hacked. But I think I did a pretty good impersonation of him, especially by weaving some real quotes by him into my text. And that’s what spoofing attacks are all about: masquerading as someone else via an email, a website, or some other attack vector with the goal of tricking you into installing some malware, stealing your data, or performing some other nasty action against you. Denial of service attacks also frequently use spoofing to disguise the source address of the IP packets they’re flooding your network or host with to prevent legitimate users from accessing the services your network or host provides. In the early days of the Internet, when everything was like the Wild, Wild West, spoofing attacks were an annoyance but were tolerated as a fun kind of challenge to try to prevent or overcome. Today, however, there’s nothing funny at all about an attack that could end up running up charges on your credit card, draining your bank account, or hijack your company’s website sending your customers running for the hills.
Erosion of trust
The biggest impact of spoofing and other forms of attacks, in my opinion, is what it is doing to our ability to trust others in our modern world. For example, I’ve written or been series editor of over 50 books on Windows Server, System Center, and other Microsoft products or solutions. I’ve also worked directly with insiders at Microsoft on various whitepapers and product documentation, and I’ve been honored with the Microsoft Most Valuable Professional (MVP) award a dozen times in a row. I think they’re an amazing company that has done a terrific job with their products, and I have huge respect for Microsoft based on my close involvement with them on various projects over the last 20 years. So you think I would trust an email I received from Microsoft, right?
Well, as My Online Security recently indicated, even an email message from a highly respected and trusted entity like the Microsoft Security Office may be suspect. Spoofed emails like this from a trusted entity not only lead to further erosion of your trust in society and the Order of Things in the World, they also, if you’re not careful, can end up causing you financial harm. It’s almost gotten to the point where we don’t open any attachments via email, including those from people we love and trust like our family and close friends.
Safe and secure
One of my favorite movies that I can watch again and again is “Knight and Day” starring Tom Cruise and Cameron Diaz. There’s a line in that movie where Tom is warning Cameron to watch out for anyone who tries to say reassuring words to her: “Words like ‘stabilized, secure, safe.’ If they say these words, particularly with repetition, it means they’re going to kill you.”
Websites that use SSL (Secure Sockets Layer) are safe to visit, right? After all, it ensures that any data passed between your web browser and the web server you’ve connected to is encrypted to safeguard the integrity of the data and your own privacy as a visitor. So SSL sites are safe, right? Not if they can be spoofed as this other recent article on My Online Security demonstrates. As the author of this article points out, many banks and other financial institutions only use SSL when the visitor wants to log on to access their account info; the public home page of the institution, however, is not protected by SSL and is thus trivial to impersonate. All it takes is a misdirected URL and you end up visiting a spoofed site instead of the real one, and before you can say, “Please hack my bank account,” you’ve entered your login credentials and your life savings are on the way to La La Land.
Wrong address
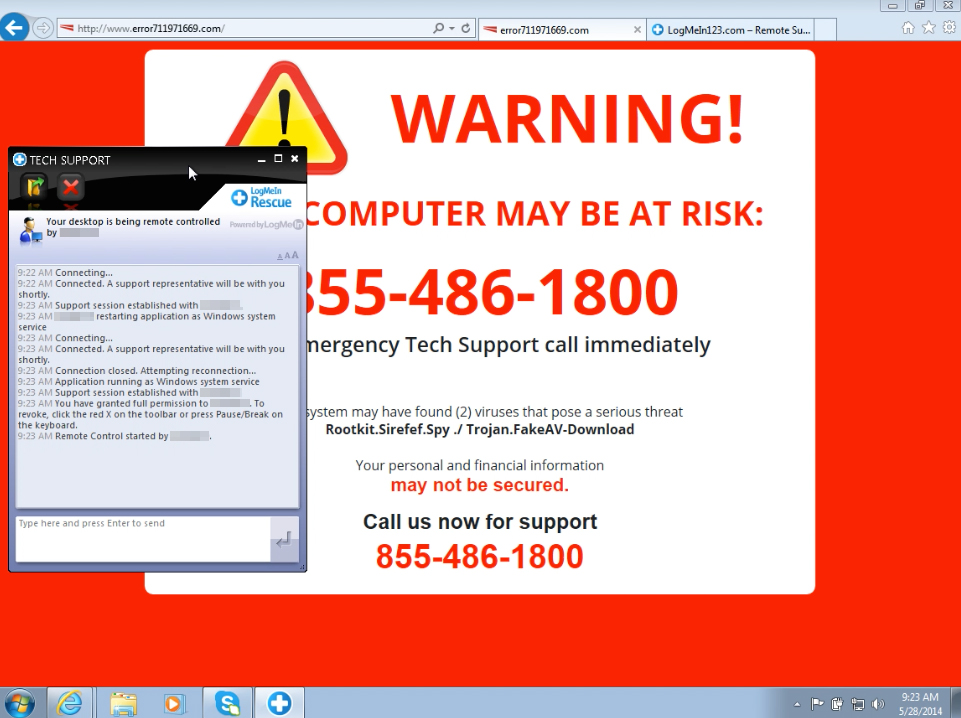
Scammers are getting more and more sophisticated with their attacks — much more sophisticated than the sites of the corporations and institutions they’re targeting. Take a look at this one for example: Open the site and click where it says “click here” and then on the next page click “Open and Spoof,” and you’ll see in the address bar of your browser that you’re now on the home page of Microsoft’s Bing search engine (www.bing.com). Or are you? Wait a couple of seconds and you’ll see that the address bar of your browser was spoofed and you’re actually on a site that redirects you to another site (which in this demonstration is harmless but in real life could be malicious). I’m hoping that the vulnerability this demo exploit is based on hasn’t been fixed by the time you’re reading this article (at the time of writing, it still works in Microsoft Edge, but appears to have been patched in Chrome and Internet Explorer). Even if it has been patched, read the article, because it goes into great detail explaining how address bar spoofing exploits work. For those of us who are not programmers or web developers, it’s enough to know you can’t even trust your eyes anymore because what you see in the address bar of your browser might not be the URL of the actual page you’ve opened.
The future looks grim
With biometrics poised to replace credit cards, it’s safe to say that the next big wave of innovation will be biometric spoofing attacks. As BetaNews says, it may soon be possible for “plastic finger tips, photographs that fool simple facial-recognition systems, and even highly technical voice recordings to manipulate [biometric] sensors. To thwart this threat, the industry will need to adapt by implementing measures such as behavioral biometrics, liveness checking, and multifactor authentication.” The irony here is almost cosmic in its dimensions: With the goal of biometrics being to simplify security by making it easier and more trustworthy, the result instead will be increasing complexity to defend against the increasing sophistication of threats that will be targeting biometric authentication systems. Isn’t that neat?
Photo credit: Wikimedia



