If you would like to read the other parts in this article series please go to:
- Test Lab Guide: Demonstrate Site to Site VPN with Threat Management Gateway 2010 (Part 2)
- Test Lab Guide: Demonstrate Site to Site VPN with Threat Management Gateway 2010 (Part 3)
- Test Lab Guide: Demonstrate Site to Site VPN with Threat Management Gateway 2010 (Part 4)
Introduction
It’s been a while since we’ve done a site to site VPN article here on ISAserver.org. Tom did a big series of VPN related articles several years ago with ISA 2000 and ISA 2004, and site to site VPN was a big deal back then, but it seems to be getting less attention these days. However, site to site VPN is still a great feature and it’s included with the TMG firewall. It’s worth delving into how it works, so that you can decide whether you want to deploy the TMG firewall as a site to site VPN server for your business.
Since this is a Test Lab Guide model, it builds on previous Test Lab Guides. If you have worked with test labs based on our Test Lab Guides, then you know that all Test Lab Guides start with the Base Configuration. If you have already gone through the Base Configuration setup and created your snapshot, then that’s great. You’re ready to go. If you haven’t, then you’ll need to download the Base Configuration guide and perform the steps to create your snapshot.
You can find the Base Configuration guide here.
The first step in this Test Lab Guide is to complete the steps in the Test Lab Guide: TMG Core Test Lab. You can find that Test Lab Guide by following this link. If you haven’t completed that Test Lab Guide yet, go ahead and perform the steps and then you’ll be ready to start on the steps in this Test Lab Guide. If you have already performed the steps in the TMG Core Test Lab Guide, then restore the TMG Core Lab snapshot and start all the virtual machines.
Create the site to site VPN connection
After starting all the virtual machines, log onto TMG1 as Administrator and open the TMG firewall console. In the left pane of the console, click Remote Access Policy (VPN), as seen in Figure 1 below.
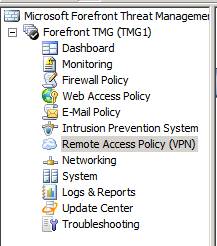
Figure 1
In the middle pane of the console, click the Remote Sites tab. Then in the Tasks Tab in the Task Pane, click Create Site to Site VPN Connection, as seen in Figure 2 below.

Figure 2
On the Welcome to the Create VPN Site-to-Site Connection Wizard page, click the VPN site-to-site networks link. This brings up the Configuring site-to-site VPN access help page that’s shown in Figure 3. Review this page to get a general idea of the steps required to create a site to site VPN connection using the TMG firewall.
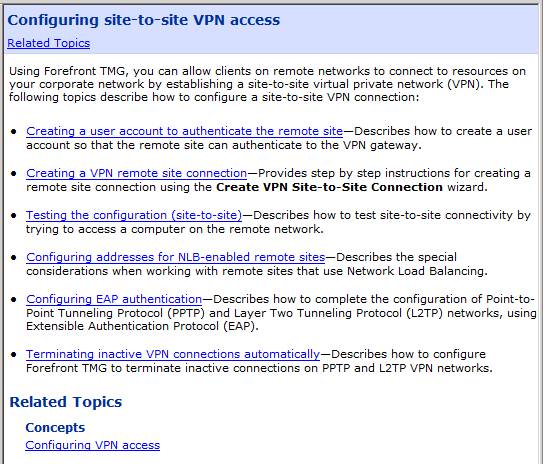
Figure 3
After reading the Help file page, close the window and then click Cancel on the Welcome to the Create VPN Site-to-Site Connection Wizard page.
Create the Account used by the Remote Site to Authenticate at the Local Site TMG Firewall
When the TMG firewalls communicate with each other to create the site to site connection, they need dedicated user accounts to log on to each other. The first step then iw to create an account on TMG1 that the remote site firewall (which we will call “Branch”) can use to authenticate when connecting to TMG1. This can be a local account on the firewall or it can be a domain account. In this example, we will create a local account on the TMG firewall.
Click Start and then right click on Computer and then click Manage, as shown in Figure 4.

Figure 4
In the Server Manager, shown in Figure 5, expand Local Users and Groups and then right click Users. Click New User.

Figure 5
In the New User dialog box that you see in Figure 6, enter Branch in the User name text box. Enter p@ssword1 in the Password and Confirm password text boxes. Uncheck User must change password at next logon. Put checkmarks in the User cannot change password and Password never expires checkboxes, then click Create.

Figure 6
Right click on the new Branch account and click Properties, as shown in Figure 7.

Figure 7
In the BranchProperties dialog box, click the Dial-in tab. On the Dial-in tab, select the Allow access option in the Network Access Permission section that’s shown in Figure 8.
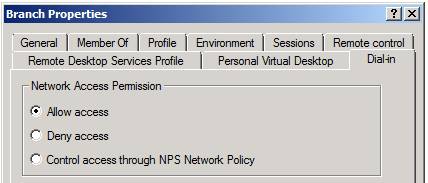
Figure 8
Create the Remote Site Connection
Now with that small bit of housekeeping out of the way, let’s get down to the task of creating the site to site VPN connection link. Click the Create VPN Site-to-Site Connection link again, as seen in Figure 9 below.

Figure 9
On the Welcome to the Create VPN Site-to-Site Connection Wizard page, enter Branch in the Site-to-Site network name dialog box as we’ve done in Figure 10. Click Next.

Figure 10
On the VPN Protocol page that you see in Figure 11, select Layer Two Tunneling Protocol (L2TP) over IPsec. This is the preferred option when connecting to TMG firewalls for a site to site VPN connection. If you wanted to connect the TMG firewall to a 3rd party VPN server, then you might want to use the IPsec tunnel mode option. However, if the other firewall supports L2TP/IPsec, then you should use that, as it’s more secure and performs better than IPsec tunnel mode. Click Next.

Figure 11
A dialog box liked the one shown in Figure 12 appears to remind you that you need to create a user account on TMG1 that the other side of the site to site VPN connection can use to authenticate to TMG1. We already know that and we’ve already created the account, so click OK to make the dialog box go away.

Figure 12
On the Local Network VPN Settings page, as shown in Figure 13, select the Dynamic Host Configuration Protocol (DHCP) option. This enables the TMG firewall to obtain addresses that can be assigned to the remote site to site VPN server from the DHCP server installed on DC1. Click Next.

Figure 13
On the Remote Site Gateway page that you can see in Figure 14, enter 131.107.0.4 in the Remote site VPN server text box. Click Next.
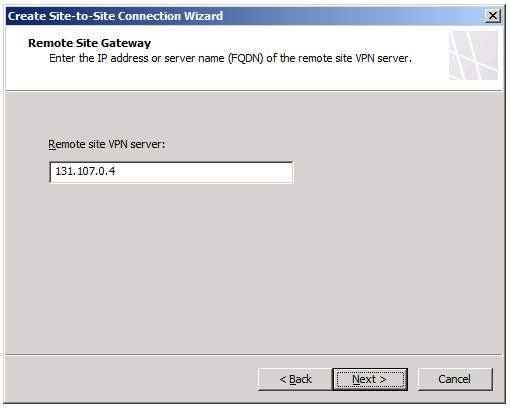
Figure 14
On the Remote Authentication page shown in Figure 15, put a checkmark in the Allow the local site to initiate connection to the remote site, using this user account checkbox. In the User name text box, enter Main. In the Domain text box, enter TMGBRANCH (this will be the name of the TMG firewall on the other side of the connection; you will create this TMG firewall in the second part of this Test Lab Guide). In the Password and Confirm password text boxes, enter p@ssword1. Click Next.

Figure 15
On the L2TP/IPsec Outgoing Authentication page that’s shown in Figure 16, select the Pre-shared key authentication option. We do this as a convenience for the test lab. In a production environment you should make sure you have a PKI in place so that certificate authentication can be used. Enter 123456789 in the Pre-shared key text box. Click Next.

Figure 16
On the Incoming L2TP/IPsec Authentication page that you see in Figure 17, select Allow pre-shared key authentication for incoming L2TP connection and then enter 123456789 in the Pre-shared key text box. Click Next.

Figure 17
On the Network Addresses page that’s shown in Figure 18, click the Add Range button. In the IP Address Range Properties dialog box, enter 10.0.1.0 in the Start addresses text box and then enter 10.0.1.255 in the End address text box. Click OK.
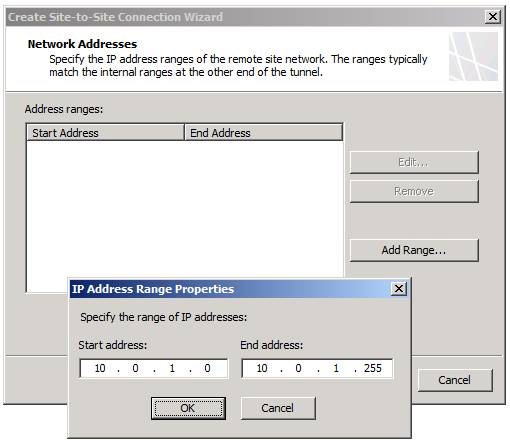
Figure 18
On the Network Addresses page that you see in Figure 19, click Next.
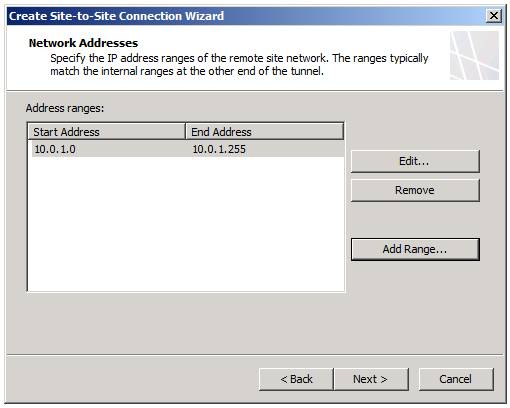
Figure 19
On the Remote NLB page shown in Figure 20, click Next.

Figure 20
On the Site-to-Site Network Rule page that’s shown in Figure 21, note the name of the Network Rule, which is Branch to Internal Network. Make sure that Create a network rule specifying a route relationship option is selected. Click Next.

Figure 21
On the Site-to-Site Network Access Rule page that you see in Figure 22, select the Create an allow access rule. This rule will allow traffic between the Internal network and the new site-to-site network for all users. In the Apply the rule to these protocols drop down list, select All outbound traffic. This rule will allow all traffic between the local and remote networks. If you decide later that you want to have a bit more granular access control between the networks, you can always go into the Firewall Policy node and delete this rule and create new ones.

Figure 22
Review your settings and click Finish on the Completing the New VPN Site-to-Site Network Wizard page that you see in Figure 23.
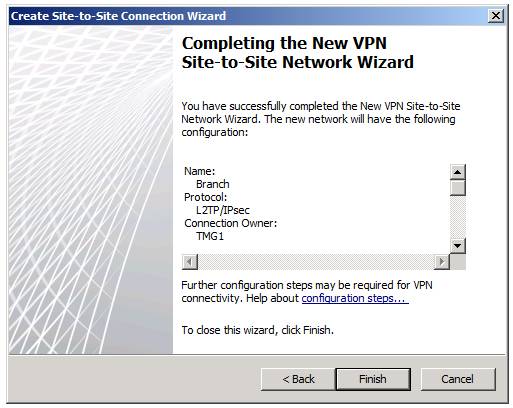
Figure 23
The Remaining VPN Site-to-Site Tasks dialog box that is shown in Figure 24 reminds you again that you need to create the user account. We’ve already done that, so click OK to make it go away.

Figure 24
You can see the new Remote Site on the Remote Sites tab that’s shown in Figure 25.

Figure 25
Click Apply to save the changes to Firewall Policy.
In the left pane of the TMG firewall console, click the Firewall Policy node. Notice the new Access Rule named Allow access between Branch and Internal in Figure 26.

Figure 26
Click on the Networking node in the left pane of the TMG firewall console. On the Networks tab, as shown in Figure 27, you can see the new Branch network.

Figure 27
Click on the Network Rules tab that you see in Figure 28. Here you can see the new Network Rule that connects the local Internal Network to the Branch network and vice versa (since it’s a Route relationship).

Figure 28
Summary
In this, part 1 of our two part Test Lab Guide on site to site VPN networking with the TMG firewall, we created the user account that the remote site will use to authenticate to the TMG1 firewall, and then created the Remote Site Network. In part 2, we will install a new TMG firewall that we will call TMGBRANCH. See you then! –Deb.
If you would like to read the other parts in this article series please go to:



