
Source: Created Using Canva
If you’re learning about VPNs, either for educational or buying purposes, it’s important to remember that you can choose between different types of VPNs. Some types of VPNs are already obsolete or no longer suited for business environments for security reasons. And although many materials on the web talk about those obsolete types, you’re better off focusing on the more current VPNs.
Some types of VPNs are also more suited for a particular use case than others. To ensure you’ll choose the right one for your business, you must be familiar with the different types of VPNs. So, in this article, I’ll explain how VPNs differ based on architecture and protocol, breaking these 2 classifications down in detail. Before doing that, let’s first review what a VPN is.
A Brief Review: What Is a VPN?
A virtual private network (VPN) enables you to extend your private network across a public network like the internet. At the same time, it keeps your connections safe from eavesdroppers. A robust VPN allows authorized users to send and retrieve files, messages, and other data without risks. In other words, a VPN upholds data confidentiality and integrity.
VPNs are currently in high demand with the rising adoption of remote and hybrid work. A recent report indicated that the global VPN market is expected to grow from USD38.56 billion in 2021 to USD45.89 billion this year (2022). The same report also predicts continued growth to USD91.20 billion in 2026 at a CAGR of 18.7%. As a result, it’s important to know more about VPNs. Continuing our discussion above, let’s dive into how VPNs work.
How Do VPNs Work?
Remote users employ tunneling technology to retrieve packets from your internal network through the internet. Tunneling encapsulates packets intended for a private network so they can traverse a public network. A VPN is one technology that uses tunneling.
In addition, a VPN secures your remote users’ connections through encryption, which renders data unreadable. Even if threat actors intercept your users’ connections, they can’t retrieve any useful information. Any intercepted data will be unreadable.
A business VPN will allow remote workers to securely access your internal servers, files, and printers. It’ll be as if they were inside your company network. That’s what we mean by saying, “a VPN extends your private network”.

Source: Created Using Canva
The scenario we just described depicts a specific VPN architecture known as remote access. In the next section, I’ll discuss the 3 main types of VPN architectures.
3 Types of VPNs, Based on Architecture
A VPN architecture refers to how a VPN environment is structured. Let’s talk about these 3 VPN architectures in more detail.
1. Remote Access VPN
Remote access refers to the VPN architecture that consists of external users and an internal network behind a VPN gateway or server. In this architecture, external users need a VPN client to connect to the VPN gateway on the network or “site”. For this reason, remote access VPN is also known as a client-to-site VPN or a client-based VPN. The client is normally a piece of software installed on the user’s device.
A remote access VPN is ideal for situations where you have remote users who need access to your internal network. Users can securely connect to your network at home, in a hotel, in an airport, or just about anywhere. Scroll back up to see what a typical remote access VPN looks like.
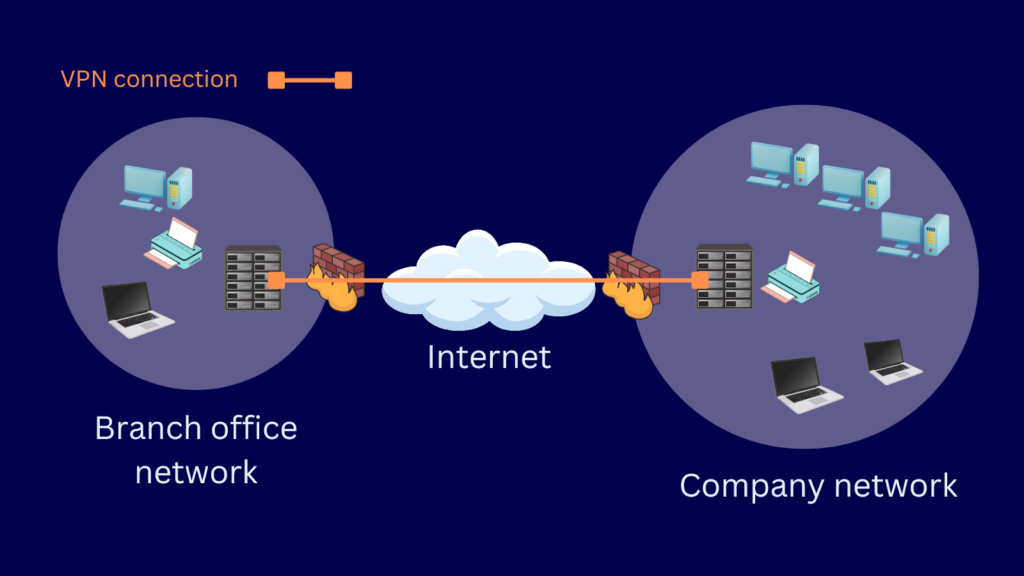
2. Site-to-Site VPN
A site-to-site VPN, or gateway-to-gateway VPN, is a VPN architecture that connects two separate networks. Implementing this architecture needs a VPN gateway or server on each network. Unlike remote access, this architecture doesn’t require installing any client software. Once you connect the two VPN gateways, users that reside in both networks can access resources in the other network.
You’ll want to use a site-to-site VPN to connect a branch office to your HQ network. You can also use these types of VPNs to connect a trading partner’s network with your network.
Source: Created Using Canva
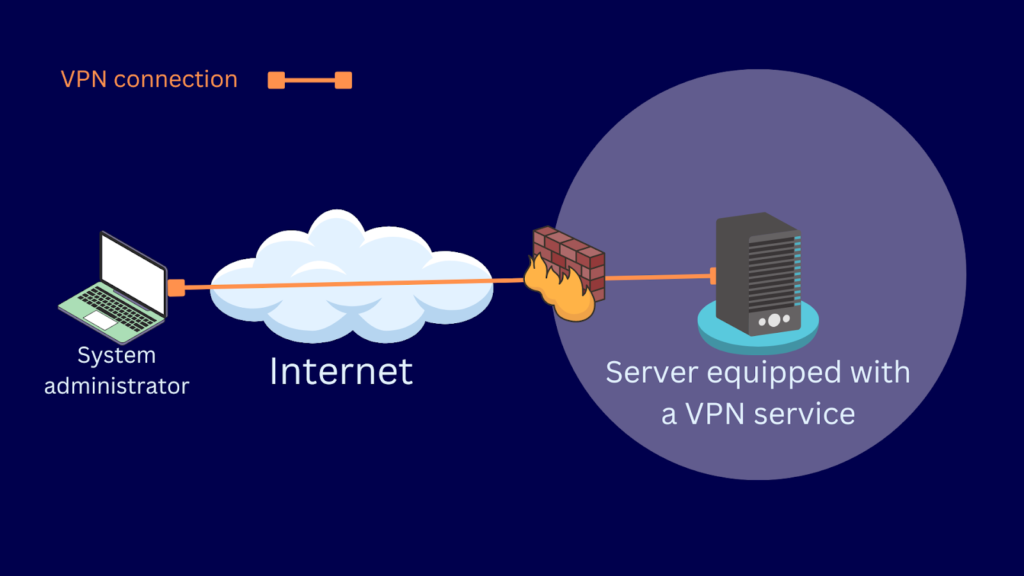
3. Host-to-Host VPN
A host-to-host VPN is similar to remote access VPN. This VPN architecture also requires a VPN client on one end. The main difference is that instead of using a VPN gateway, the other endpoint provides the VPN service itself. That “other endpoint” is usually a server with a VPN running on it.
You’ll use these types of VPNs if your system administrators need secure access to a highly-sensitive server. You can lock down that server and limit access through a host-to-host VPN. Thus, only authorized users who have VPN clients configured for that server’s VPN service can have access. In the diagram below, the system administrator’s laptop acts as one host, and the server on the other end acts as another host.
Source: Created Using Canva
Aside from architecture, VPNs also differ based on the protocol they use. Let’s now discuss the types of VPN protocols.
6 Types of VPNs, Based on Protocol
A protocol is a shared set of rules that devices or applications follow to communicate with one another. For example, if two VPN gateways or a VPN client and a VPN server need to establish a VPN connection, they need to support the same VPN protocol. In the following subsections, I’ll discuss the most commonly used VPN protocols today and in the past. I’ll also highlight their pros and cons.
1. IPSec VPN
Internet Protocol Security (IPSec) is the most widely used VPN protocol in business environments. If you want to be technical, IPSec isn’t just one protocol. Rather, it’s a suite of protocols that contribute to security functions like authentication, data integrity, encryption, etc. We discussed these protocols and IPSec as a whole in this comprehensive guide.
Here are a few pros and cons of IPSec.
Pros
- Well-established
- Great for site-to-site use cases due to interoperability reasons
Cons
- Complicated for remote access use cases
- Difficult to configure
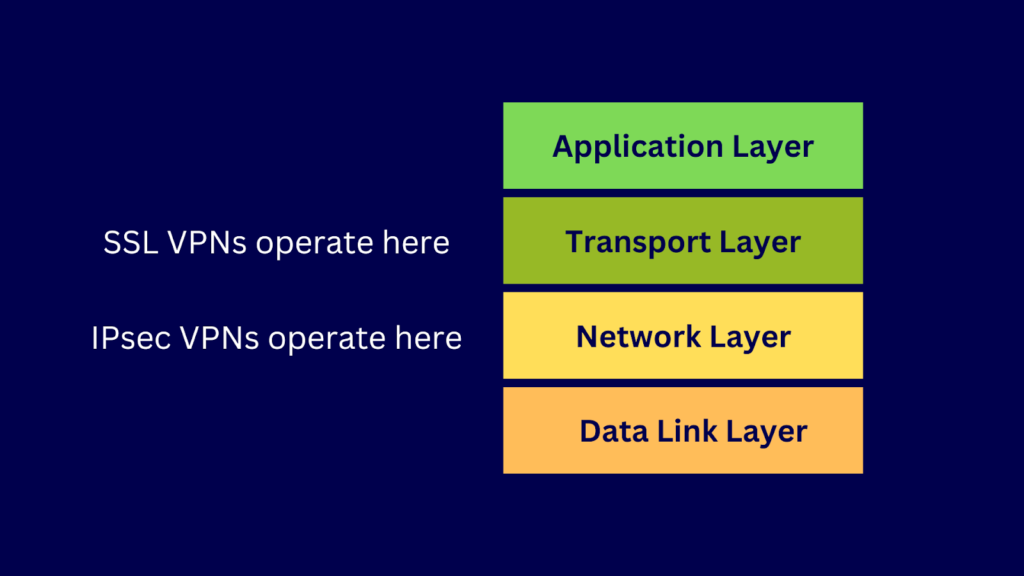
2. SSL VPN
SSL VPN is an overarching term that refers to types of VPNs that provide security at the transport layer of the TCP/IP model. For comparison, an IPSec VPN secures at the network layer. The Secure Sockets Layer (SSL) protocol has long been rendered obsolete due to its serious vulnerabilities. Examples of these vulnerabilities are weak cipher suites, POODLE exploits, etc. Thus, although they’re called SSL VPNs, most SSL VPN deployments no longer use SSL. Instead, they use SSL’s more secure successor, Transport Layer Security (TLS) protocol.
Source: Created Using Canva
Here are a few pros and cons of SSL VPN.
Pros
- Easy to implement for remote access use cases since users only need a web browser
Cons
- Rarely used in a site-to-site architecture, so you’re likely to encounter interoperability issues if you use it to connect with trading partners
3. OpenVPN
OpenVPN is arguably the most popular SSL VPN implementation — and it’s open source! This means an open community of developers and other contributors support it. OpenVPN comes in two editions: OpenVPN Community Edition and OpenVPN Access Server. The former is free, while the latter isn’t. You can leverage OpenVPN’s community to seek assistance, find examples, and even discover projects that extend OpenVPN.
Here are a few pros and cons of OpenVPN.
Pros
- More affordable if you already have people familiar with OpenVPN since it’s open source
- Highly customizable
- Suitable for site-to-site and remote access architectures
Cons
- Expensive if you choose to go the open-source route but lack the in-house talent to set up the required infrastructure
- Costly since it requires hiring a third party or new staff to deploy, administer, and maintain your OpenVPN infrastructure
- Difficult to set up since it isn’t built to any OS
4. SSTP VPN
Secure Socket Tunneling Protocol VPN (SSTP VPN) is an SSL VPN developed by Microsoft. It was Microsoft’s response to the growing popularity of SSL VPNs in the mid-2000s. SSTP only supports remote access architecture, which Microsoft calls “point-to-site”. If you need to do site-to-site, you’ll need to look for another protocol. SSTP also uses port 443, which is the same port used by HTTPS.
Here are a few pros and cons of SSTP.
Pros
- Easy to deploy and readily available since it comes with a Windows installation
- Immune to most firewall-related issues since it uses port 443
Cons
- Incapable of supporting site-to-site use cases
5. PPTP VPN
Point-to-Point Tunneling Protocol (PPTP) is an older VPN protocol also developed by Microsoft. Like SSTP, it ships with Windows, which explains why PPTP was so popular in the past. Some businesses still use it nowadays, but I don’t recommend it. The main protocol PPTP uses for authentication, MCHAP, is found to have serious vulnerabilities. Similarly, the RC4 keys, used for encryption and decryption, can be easily obtained through a man-in-the-middle attack.
Here are a few pros and cons of PPTP.
Pros
- Easy to deploy and readily available since it comes with a Windows installation
- Immune to most firewall-related issues since it uses pot 443
Cons
- Plagued with serious vulnerabilities that make it unusable in production environments, especially those where data is transmitted through the internet
- Unsuitable for production environments
6. L2TP VPN
Layer 2 Tunneling Protocol (L2TP) is yet another tunneling protocol for implementing a VPN. L2TP was supposed to replace PPTP and, like PPTP, shipped with leading operating systems. LT2P alone doesn’t have security mechanisms. Rather, it’s usually paired with IPsec to acquire encryption and data integrity capabilities. Thus, technically speaking, L2TP VPNs are L2TP/IPSec VPNs.
In its Special Publication 800-77 Rev.1, the US National Institute of Standards and Technology (NIST) considered L2TP and PPTP as “obsoleted and deprecated VPN protocols”.
Here are a few pros and cons of L2TP.
Pros
- Common and old, making it useful for interoperability purposes
Cons
- Plagued with serious vulnerabilities that make it unusable in production environments, especially those where data is transmitted through the internet
Now that you know the common types of VPNs, let’s put that knowledge to practical use.
3 Best Practices When Choosing the Right VPN for Your Company
Familiarity with the different types of VPNs can come in handy when choosing a VPN for your business. Here are some steps you can follow to pick the right VPN.
1. Identify Your Specific Needs
How do you intend to use your VPN? Is it supposed to provide secure network access for remote workers? Or do you want to establish a secure connection between a branch office and your HQ network? If your intention is for the former, you’ll need a remote access VPN. If it’s the latter, you’ll need a site-to-site VPN. Knowing your specific need can already narrow down your options. For instance, if you need a site-to-site VPN, IPSec and OpenVPN will be your top choices. You can’t use the other VPNs for this architecture.
2. Identify Your Risk Appetite
How many risks are you willing to take when sending traffic over a public network? You can’t afford to use an obsolete VPN protocol — especially if you’ll transmit highly-sensitive data over the network. If you provide remote access to highly-sensitive servers, a VPN with serious vulnerabilities shouldn’t be an option. That means PPTP and L2TP are out. Identifying the risks will allow you to determine which type is the right choice based on the architecture you’ve set up.
3. Identify Your Administrative Capabilities
Do you have the in-house talent to deploy, manage, and maintain a highly complex VPN infrastructure? If not, IPSec might not be a good choice. Is your IT team comfortable with open-source solutions? Would they prefer something already built into the Windows OS? You might have to remove OpenVPN from your shortlist if the answer is the latter.
Once you’ve ironed out these key criteria, you can start considering less critical factors. These factors include cost, interoperability, technical support, ease of use, etc. I believe we’ve covered a lot already. Let’s wrap things up.
Final Words
Businesses need VPNs to provide secure remote access to their internal networks. VPNs have different types, first in terms of architectures and then in terms of protocols. For VPN architectures, some types are remote access, site-to-site, and host-to-host. Meanwhile, for VPN protocols, I discussed IPSec, SSL VPN, OpenVPN, SSTP, PPTP, and L2TP.
Lastly, I suggested some tips to help you choose between the different types of VPNs. In a nutshell, you need to identify your specific needs, risk appetite, and administrative capabilities when choosing a VPN. Some popular VPNs are already plagued with serious vulnerabilities, so it’s best to avoid those. In addition, consider factors like interoperability, ease of use, and cost.
Do you have any questions? Check out the FAQ and Resources sections below.
FAQ
What is a VPN service?
A VPN service is a VPN infrastructure that a third-party service provider manages. Some VPN services are free, but the more advanced and capable ones charge a monthly or annual fee. A VPN service is ideal if you wish to avoid the capital outlay of owning a VPN infrastructure.
What is a No-Log VPN?
A No-Log VPN is a VPN that doesn’t store traffic logs. This practice serves privacy purposes. Some countries, like Switzerland, have laws that don’t allow servers to store log traffic. A No-Log VPN also helps VPN-equipped businesses meet that mandate.
WARP vs VPN — which is better for online security?
WARP is a cloud-based service that the web performance and security company Cloudflare offers. Like a VPN, WARP protects your privacy. That said, it’s not as secure as a full-fledged VPN. WARP focuses more on speed rather than privacy. Our article on WARP vs VPN has more details on the topic.
Why should I use a VPN if I’m working remotely?
A VPN can keep you safe when you connect to public Wi-Fi. It gives you secure remote access to files, applications, and other resources in your corporate network. You can get more details on the topic in our article about remote workers and using a VPN.
What VPN services should I use for small businesses?
You can find several good VPN services for small businesses. Some of the best options include KerioControl, VyprVPN, CyberGhost VPN, ExpressVPN, and NordVPN. We’ve discussed all these VPN services in detail in our article about VPN services for small businesses.
Resources
TechGenix: Article on L2TP VPN
Dive into the basic concepts of Layer 2 Tunneling Protocol (L2TP).
TechGenix: Article on Remote Access
Understand the various options for implementing remote network access.
TechGenix: Review on Kerio Control VPN
Weigh the different pros and cons of using KerioControl.
TechGenix: Article on Self-hosted VPN vs VPN-as-a-Service
Compare between self-hosted VPN and VPN-as-a-Service.
TechGenix: Article on Tor vs VPN
Learn when to use Tor vs VPN and vice versa.



