If you would like to read the other parts in this article series please go to
- Understanding Man-in-the-Middle Attacks – ARP Cache Poisoning (Part 1)
- Understanding Man-In-The-Middle Attacks – Part2: DNS Spoofing
- Understanding Man-In-The-Middle Attacks – Part 4: SSL Hijacking
Introduction
In the first two articles of this series on man-in-the-middle attacks we examined ARP cache poisoning and DNS spoofing. As we have demonstrated with those examples, MITM attacks are incredibly effective and increasingly hard to detect. In the third part of this article we will examine session hijacking, which is no different. As with the previous two articles I will describe the theory behind session hijacking, demonstrate the technique in practice, and discuss detection and prevention tips.
Session Hijacking
The term session hijacking is thrown around frequently and encompasses a variety of different attacks. In general, any attack that involves the exploitation of a session between devices is session hijacking. When we refer to a session, we are talking about a connection between devices in which there is state. That is, there is an established dialogue in which a connection has been formally set up, the connection is maintained, and a defined process must be used to terminate the connection. When we talk about sessions theoretically it’s a bit confusing, so it may help to think of a session in a more practical sense.
In this article we will be talking about session hijacking through cookie stealing, which involves HTTP sessions. If you think about some of the common websites you visit that require login credentials, those are great examples of session-oriented connections. You must be authenticated by the website with your username and password to formally set up the session, the website maintains some form of session tracking to ensure you are still logged in and are allowed to access resources (often done with a cookie), and when the session is ending the credentials are cleared and the session ends. This is a very specific example of a session and even though we do not always realize it, sessions are occurring constantly and most communications rely on some form of session or state-based activity.

Figure 1: A normal session
As we have seen in previous attacks, nothing that goes across the network is safe and session data is no different. The principle behind most forms of session hijacking is that if you can intercept certain portions of the session establishment, you can use that data to impersonate one of the parties involved in the communication so that you may access session information. In the case of our earlier example, this means that if we were to capture the cookie that is used to maintain the session state between your browser and the website you are logging into, we could present that cookie to the web server and impersonate your connection. If that sounds too good to be true from an attackers standpoint, well….it is.

Figure 2: Session Hijacking
Now that we have a little bit of theory in the books, let us delve into a practical example.
Stealing Cookies with Hamster and Ferret
In our practical scenario we will be performing a session hijacking attack by intercepting the communication of a user logging into his Gmail account. Using this intercepted communication we will impersonate that user and access the account from our attacking machine.
In order to perform this attack we will be using two tools straight out of the pet store, named Hamster and Ferret. Both tools can be downloaded from here. These are both command-line tools so the hamster folder can be extracted to an easy to get to location.
Alternatively, you can download and use Backtrack 4. BT4 is a Linux live-CD distribution designed specifically for hacking and penetration testing that comes with a myriad of preinstalled and precompiled tools, with Hamster/Ferret being two of them. You can download BT4 from here. You will then find Hamster in the /pentest/sniffers/hamster folder. The screenshot examples used in the rest of this tutorial are taken from BT4.
The first step involved in this form of session hijacking is to capture the traffic of the victim user as he browses Facebook. This traffic can actually be captured using any packet sniffing application such as TCPDump or Wireshark, but in order to capture the right packets you will need to employ a technique such as ARP cache poisoning (discussed in the first article in this series).

Figure 3: Capturing traffic of the user browsing to Gmail
Once you have captured the traffic of the victim user browsing to Gmail you will need to save the captured file into the Hamster directory. For the purposes of this example, we have named our file victim_gmail.pcap. When that file is in place, we will use Ferret to process the file. This is done by browsing to the Hamster folder and running the command, ferret -r victim_gmail.pcap. Ferret will process the file and create a hamster.txt file that may be used by Hamster for the actual hijacking of the session.
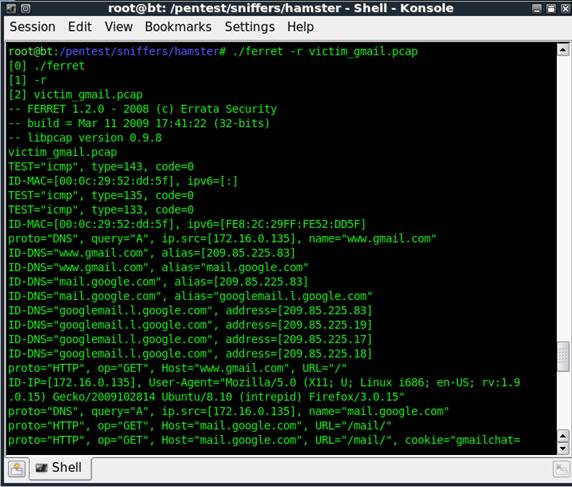
Figure 4: Processing the capture file with Ferret
With our HTTP data intercepted and prepared for use, we can use Hamster to actually execute the attack. Hamster itself actually runs as a proxy that provides an interface for browsing and using stolen session cookies. In order to start the Hamster proxy you can simply execute Hamster with no command line options.

Figure 5: Starting Hamster
Once executed, you will need to open your browser and configure its proxy settings to match those provided to you by the Hamster output. By default, this means that you would configure your proxy settings to use the local loopback address 127.0.0.1 on port 1234. You can access these settings in Internet Explorer by selecting Tools, Internet Options, Connections, LAN Settings, and placing a checkbox in the Use a proxy server for your LAN box.

Figure 6: Configuring proxy settings for use with Hamster
Now that the proxy settings have been applied you can access the Hamster console in your browser by browsing to http://hamster. Hamster will use the file created by Ferret to produce a list of IP addresses for whom session information has be intercepted and display those IP address in the right pane of the browser. Our file we’ve created only contains a single IP address of the victim, so if we click that the left pane will be populated with the sessions available for hijacking.
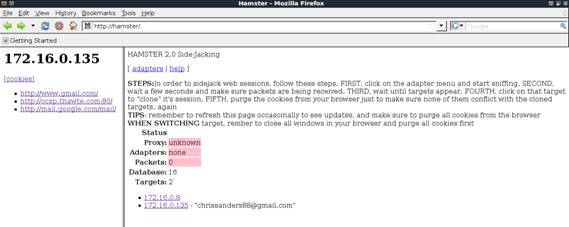
Figure 7: The Hamster GUI
We see that facebook.com is listed, and if you click that link you will be pleased to be presented with a new window that has you logged in to the victims Facebook account!

Figure 8: Successfully hijacked Gmail account!
Defending Against Session Hijacking
There are many different forms of session hijacking so the defenses for them can vary. Just like the other MITM attacks we’ve evaluated, session hijacking is difficult to detect and even more difficult to defend against because it’s a mostly passive attack. Unless the malicious user performs some type of obvious action when he accesses the session being hijacked, you may never know that they were there. Here are a few things you can do to better defend against session hijacking:
- Save Online Banking for Home – The chance of somebody intercepting your traffic on your home network is much less than on your work network. This isn’t because your home computer is more secure (let’s face it, its probably less secure), but the simple matter of fact is that if you only have one or two computers at home, the most you have to worry about in terms of session hijacking is if your 14 year old son starts watching hacking videos on YouTube. On a corporate network you don’t know what is going on down the hall or in the branch office 200 miles away, so the potential attack sources multiply. One of the biggest targets for session hijacking is online banking, but this principal applies to anything.
- Be Cognizant – Smart attackers will not leave any evidence that they have been in one of your secure accounts but even the most seasoned hackers make mistakes. Being aware when you are logged into session-based services can help you determine if somebody else is walking in your shadow. Keep an eye out for things that seem out of place, and pay attention to “Last Logon Time” fields to ensure everything matches up.
- Secure your internal machines – Once again, attacks like these are most commonly executed from inside the network. If your network devices are secure then there is less of a chance of those compromised hosts being used to launch a session hijacking attack.
Wrap Up
We have now covered three very lethal MITM attack types which could all have very grave consequences if successfully carried out against a victim. Using session hijacking someone with malicious intentions could access a user’s online banking, e-mail, or even a sensitive intranet application. In the next article in this series we will look at another lethal MITM attack, SSL spoofing.
If you would like to read the other parts in this article series please go to



