Introduction
The “feature complete” public beta of Windows 7 was released on January 9th, and the industry is abuzz with commentary about changes to the interface, but what is going on under the hood? What changes have been made that will affect OS and network security? In this article, we will take a first look at Windows 7 security features and whether, from a purely security standpoint, it is worth the upgrade. We will be focusing specifically on changes to the security management interface, changes to User Account Control, enhancements to BitLocker, the introduction of AppLocker, and the new Biometric Framework.
The Trouble with Vista Security
In response to complaints that Windows was not secure, Microsoft focused heavily on security when they built Windows Vista. BitLocker drive encryption, parental controls, built-in anti-malware (Windows Defender), improvements to the Windows firewall, Data Prevention Execution (DEP), protected mode IE, service hardening , new digital rights management features, an update to the Crypto API, Network Access Protection (NAP) client, and improvements to the Encrypting File System (EFS), software restriction policies and numerous other security enhancements were introduced in Vista. Service Pack 1 added more security-related improvements, including multifactor authentication for BitLocker, a redesigned Random Number Generator (RNG), signing of Remote Desktop Protocol (RDP) files, and more.
However, the security feature that users noticed (and hated) most was User Account Control (UAC), by which all user accounts, including administrative accounts, run in standard user mode by default and request elevation if higher privileges are needed. The “in your face” nature of UAC , along with the Secure Desktop feature that prevents malware from accessing the desktop during the prompt for administrative rights, but also annoyingly dims the display, was one of the chief complaints about Vista.
The challenge for the Windows 7 team was to make the OS as secure (or more secure) than Vista, while keeping the security more transparent to users.
So Long to the Security Center, Hello to the Action Center
The Security Center, accessed through Control Panel and intended to provide a centralized location for managing security-related settings, was introduced in Windows XP SP2 and carried over into Vista. With Windows 7, there is even more centralization. The Security Center is gone and a new Action Center takes its place. Here you will find alerts not only related to security but also regarding Windows Update, Diagnostics, NAP, Backup and Restore and troubleshooting issues, as shown in Figure 1.

Figure 1: The Action Center centralizes many administrative tasks, including security
More Flexible UAC settings
In Vista, you could disable UAC through Group Policy, but that was not a good solution as it left you vulnerable to attack. Alternatively, you could set UAC to elevate without prompting, which is a better idea. However, the Home versions of Vista do not include the Group Policy editor, so you had to edit the registry to accomplish this. Microsoft has made it easier for users to control UAC’s behavior in Windows 7.
Note:
IT admins will be relieved to know that users would not be able change UAC settings unless they have administrative privileges.
In the Action Center’s left pane, there is an option labeled User Account Control Settings. UAC’s prompt behavior is adjusted via a slider bar that gives you a choice of four positions:
-
Always Notify: You will get the UAC prompt when you install software or make system changes
-
Notify Only When Programs Try to Make Changes: You will get the prompt if I program requests elevated privileges, but not when you make changes to Windows settings (this is the default)
-
Notify Only When Programs Try to Make Changes (Do Not Dim the Desktop): same as the default except that Secure Desktop is disabled during the prompt
-
Never Notify: You would not get the prompt when you make changes to Windows settings nor when you install software (not recommended)
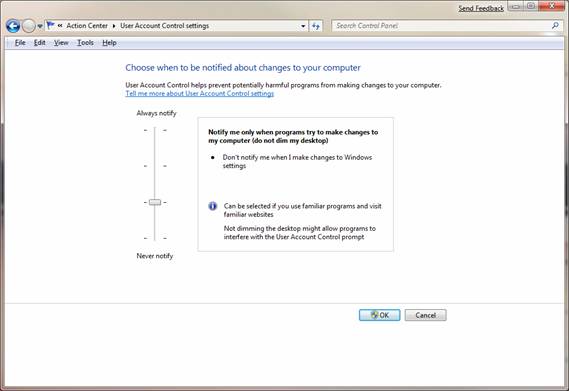
Figure 2: A slider bar allows you to more precisely control how the UAC prompt works in Windows 7
BitLocker enhancement
BitLocker, included in Vista Enterprise and Ultimate editions, allows you to encrypt entire volumes using AES, either utilizing the Trusted Platform Module (TPM) chip that comes in some computers, or using a USB key. This prevents booting into the operating system or accessing the data on the encrypted volume without authorization (for example, by installing a different instance of the OS and booting into that). It is especially useful for portable systems that may be lost or stolen.
In Vista, BitLocker originally could only be used to encrypt the volume on which the operating system was installed. Service Pack 1 added the ability to encrypt multiple fixed disks, but you could not use it to encrypt removable disks. In Windows 7, BitLocker has been enhanced to support encryption of portable hard disks and flash memory devices. This is being called “BitLocker to Go.” This is a feature that many companies have been wanting, since storage of sensitive data on USB keys has become popular.
Note:
You can also apply a policy that will require removable drives to have BitLocker protection before users can write data to them.
BitLocker is managed via a Control Panel applet, shown in Figure 3.
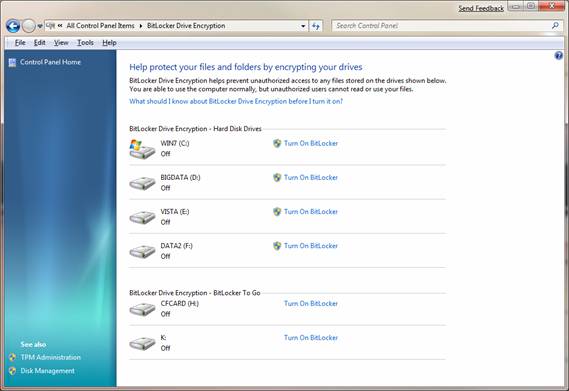
Figure 3: In Windows 7, you get the option to use BitLocker encryption on removable drives as well as fixed disks
You can choose to use a passphrase to unlock the disk or you can use a smart card and PIN, as shown in Figure 4.

Figure 4: When you encrypt a disk with BitLocker, you can use a passphrase or smart card to unlock it
You can also set up a recovery key so that you can unlock your device if you forget your passphrase. The recovery key can be saved to file or printed and stored in a safe place (or both). It may take a while, depending on the size of the drive. Encrypting a 2 GB USB key took a little over 9 minutes on my system. A progress bar will keep you informed during the process, as shown in Figure 5.

Figure 5: A progress bar keeps you informed during the encryption process
For more information about BitLocker and BitLocker to Go in Windows 7, see the screencast here.
AppLocker
Windows 7 gets another “locker”: AppLocker, which is a new feature of Group Policy. It lets admins control the versions of applications that users can install and use. This makes it possible to prevent users from installing and running older versions of applications that may have security holes.
Earlier versions of Windows used Software Restriction Policies control which programs users could run. AppLocker improves on that with easier configurability via three types of rules: Path, File Hash and Publisher. Publisher Rules replace the Certificate Rules in SRP, and give you more flexibility and options. They are also harder to circumvent.
For more information about AppLocker, see the screencast here.
Biometric Framework
In Vista, if you wanted to use fingerprint logon, you had to use software provided by the fingerprint sensor vendor. A new security feature in Windows 7 is the Biometric Framework, which provides native support for fingerprint devices and makes it easier for developers to put biometric security into their applications. You will find a new Control Panel applet called Biometric Devices that’s used for managing fingerprint, as shown in Figure 6.

Figure 6: You can manage biometric devices through the Control Panel applet
Settings can be adjusted to allow users to log on to Windows and/or to the domain using biometrics, and you can set different fingers per user.
Note:
At the time of this writing, fingerprint sensors are the only biometric devices that are supported by the Windows Biometric Framework.
The Windows Biometric Service (WBS) is the part of the framework that manages fingerprint readers and acts as an I/O proxy between client applications and the biometric device, so that applications can not directly access the biometric data. This protects user confidentiality.
For more “under the hood” information about the WBS, see the white paper here.
Summary
With Windows 7, Microsoft has continued their efforts to provide a more secure operating system while listening to user input about how security should work behind the scenes instead of getting in your face. At the same time, they have improved some of the security features from previous operating systems from the perspective of the user experience, the admin experience and the level of security achieved. For most business users and network administrators, the security enhancements in Windows 7 are likely to make it well worth the upgrade.



