If you would like to read the other parts in this article series please go to:
Introduction
In the first two articles in this series, I exposed the reality of Windows’ password policy and how it is controlled in an Active Directory environment. I went over where to find the password policy and the associated settings which are stored for Active Directory. If you recall, these will be found in the Default Domain Policy by default. I also reviewed which technologies used to break into a Windows password, describing what the limitations were with each attack. Now, I want to cover how a Windows password could be made secure, solving all of the issues that I covered in the first two installations of this topic. We will cover what the possibilities are with Windows’ default installation of Windows 2000/2003/2008 Active Directory, as well as some other technologies that are available to increase the overall security of the password.
First Things First, Just Use a Phrase
It is now nearly three years that I have been spreading the word to individuals and organizations that if passwords are looked at from a fresh perspective, they are easier to remember, easier to type, and much easier to obtain a longer password. A typical password that a user might use would be:
Am3r1c@
This particular password would meet complexity requirements, but is hard to remember and certainly not easy to type. Therefore, users will write this down, place it on their monitor, stick it under their keyboard, etc. Instead of something archaic like this password, try using a password…err, I mean pass-phrase, like this:
I am a Group Policy MVP.
Or
I went to Germany on my last vacation.
Note:
Read each of the above three passwords and pass-phrases, then try to type each one quickly. You will see that the pass-phrases are much easier to type and even remember!
Since the pass-phrases all beat LM, dictionary attacks, and Rainbow tables, you can now allow your users to keep their passwords longer, even up to a full year!
In this final article, we will discuss what a good password policy should look like, how to ensure it is implemented, how to ensure it is the same on all PCs (including the local SAM), and what other technologies (fine-grained passwords and specops password policy) can be used to get a good password implemented.
Ensuring Password Policies are Consistent for Domain and Local User Accounts
The built-in configuration of Active Directory ensures that all user accounts (those stored in Active Directory and those stored in the local SAM on each desktop and server) all have the same password policy. However, this can be altered by linking and configuring a GPO down at the organizational unit (OU) level, where the OU has computer accounts stored in them. In this case, desktops and servers (not domain controllers) can have the local SAM of the user accounts adhere to a different password policy than that of domain user accounts.
In order to keep a consistent password policy for all users, you can “enforce” the GPO that houses your password policy settings for domain user accounts. Again, by default, this is the Default Domain Policy. To enforce a GPO, right-click on the GPO and select the Enforce Menu option. Figure 1 illustrates how this would look once it is configured.
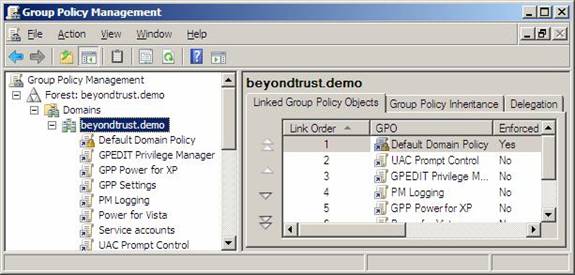
Figure 1: Enforcing the Default Domain Policy will ensure that all user accounts in local SAMs use a consistent password policy
Multiple Password Policies per Domain Using Microsoft Technology
Microsoft has risen to the occasion and delivered the ability to have multiple password policies in a single Active Directory domain. This is not exactly breaking news, but it is a breath of fresh air non-the-less. This technology is only available in a Windows Server 2008 domain, where all domain controllers run Windows Server 2008. Also, the domain must be running at Windows Server 2008 functional level. The technology is referred to as fine-grained password policies.
If this situation arises, you can configure multiple password policies. This means that you can have the following:
- IT users must use a 25 character password
- HR users must use a 20 character password
- All other users must use a 17 character password
The negative to this is that this is not configured in Group Policy. Instead, you must create additional Active Directory objects under the Password Settings Container. One too you can use to view and configure these new objects is ADSIEDIT.MSC, which is illustrated in Figure 2.
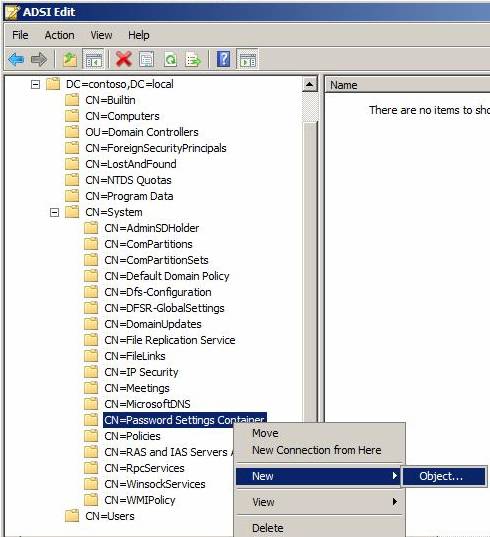
Figure 2: ADSIEDIT.MSC can be used to create additional fine-grained password policies in Windows Server 2008 domains
To create the additional objects, you have to right-click on the Password Settings Container, then select New, then Object. The wizard will walk you through what needs to be configured. There are many details that need to be worked out, which are all described here in other Windows Security articles;
- Configuring Granular Password Settings in Windows Server 2008 – Part 1
- Configuring Granular Password Settings in Windows Server 2008 – Part 2
- Configuring Granular Password Settings in Windows Server 2008 – Part 3
Taking Password Policies To The Next Level
Microsoft has provided us with years of password policy controls, and now, with Windows Server 2008 fine-grained password policies, we have even more control. However, if you want to take your Windows domain password policy settings to a level that gives you ultimate control over your passwords, you need to get a tool like Password Policy from Special Operations Software. This tool works seamlessly in Active Directory and plugs into Group Policy, like you would want the fine-grained password policies to work!
With this tool, you can configure the following:
- Set any combination of password restrictions: lower case, upper case, numeric, and special characters
- Different password expiration rules, commonly called password age, on each policy
- Disallow consecutive characters in password
- Dissallow incremental passwords
- Automatically send password expiration e-mail
- Additional password policy requirements; Regular expressions; Disallow backward words in wordlist; Disallow digit as last character
Figure 3 illustrates what the interface for Password Policy looks like.

Figure 3: Specops Password Policy is a granular password policy tool for Windows domains
Summary
Windows passwords are always under attack. There are many tools and reasons why an attacker would go after a Windows password. Many of the attacks are valid and quite easy. So, you must protect your own password and the passwords of users on the network you manage. The defaults within a Windows environment need to be altered, specifically those around LanManager authentication. You need to instruct your users to not document or post their passwords, as this is far too easy to discover. Education on how to create a good, solid, complex, long password… I mean pass-phrase, is key! Moving to a tool that provides multiple passwords in the same domain and even forcing more complex and restrictive passwords can go a long way in protecting and making your passwords more secure. If the default password policies are kept in place and an attacker gets a hold of a hash or SAM, chances are you will not be protected! Protect and secure your passwords better today!
If you would like to read the other parts in this article series please go to:




